红队live-展期
日期:9月3日晚19:20
MITRE ATT&CK
TTPS
Tactics, Techniques and Procedures
整个靶场技术战术和操作(TTPS)同样重要。
Techniques 技术
技术是攻击面的知识点、是计算机基础的知识点、是代码能力、是漏洞原理。
Tactics 策略;战术
战术是思维框架,是我怎么想到的问题,是优先级的排定,是攻击思路的对抗。
Procedures 程序
操作是对kali的熟悉,各类shell命令、工具集tooling的熟悉。
本周环境
OSINT
nmap高级
服务扫描
OSINT
公开信息搜集
Open source intelligence 开源情报 (OSINT) 是对从开源(公开来源和公开信息)收集的数据的收集和分析,以生成可操作的情报。OSINT 主要用于国家安全、执法和商业情报职能,对于使用非敏感情报来回答先前情报学科中的机密、非机密或专有情报要求的分析师来说很有价值。
Media, print newspapers, magazines, radio, and television from across and between countries.
来自各国和国家之间的媒体、印刷报纸、杂志、广播和电视。Internet, online publications, blogs, discussion groups, citizen media (i.e. – cell phone videos, and user created content), YouTube, and other social media websites (i.e. – Facebook, Twitter, Instagram, etc.). This source also outpaces a variety of other sources due to its timeliness and ease of access.
互联网、在线出版物、博客、讨论组、公民媒体(即 – 手机视频和用户创建的内容)、YouTube 和其他社交媒体网站(即 – Facebook、Twitter、Instagram 等)。由于其及时性和易于访问性,该来源也超过了其他各种来源。Public government data, public government reports, budgets, hearings, telephone directories, press conferences, websites, and speeches. Although this source comes from an official source they are publicly accessible and may be used openly and freely.
公共政府数据、公共政府报告、预算、听证会、电话簿、新闻发布会、网站和演讲。尽管此来源来自官方来源,但它们是公开访问的,并且可以公开自由地使用。Professional and academic publications, information acquired from journals, conferences, symposia, academic papers, dissertations, and theses.
专业和学术出版物,从期刊、会议、研讨会、学术论文、学位论文和学位论文中获得的信息。Commercial data, commercial imagery, financial and industrial assessments, and databases.
商业数据、商业图像、财务和行业评估以及数据库。Grey literature, technical reports, preprints, patents, working papers, business documents, unpublished works, and newsletters.
灰色文献、技术报告、预印本、专利、工作论文、商业文件、未发表的作品和新闻通讯。
在初期最重要的就是信息收集
而且是贯穿全流程的
APTLabs simulates a targeted attack by an external threat agent against an MSP (Managed Service Provider). The lab requires prerequisite knowledge of attacking Active Directory networks. APTLabs consists of fully patched servers, prevalent enterprise technologies, a simulated WAN network, and much more!
Your goal is to compromise all client networks and reach Domain Admin wherever possible. On completion of this lab you will be familiar with long-lasting TTPs, how to abuse enterprise technology, and be a true google-ninja.
This is an extremely challenging Red Team Operator Level III lab, that will push you to the limit, and put your skills to the test in the following areas:
Active Directory enumeration and exploitation
Bypassing security features such as 2FA, JEA and WDAC
Exploiting interactive users
Kerberos attacks
Lateral movement between multiple forests
Reaching your goals without using any CVEs
APTLabs 模拟外部威胁代理对 MSP(托管服务提供商)的针对性攻击。本实验需要具备攻击 Active Directory 网络的必备知识。APTLabs 由完全修补的服务器、流行的企业技术、模拟的 WAN 网络等等组成!
您的目标是破坏所有客户端网络,并尽可能使用 Domain Admin。完成本实验后,您将熟悉持久的 TTP、如何滥用企业技术,并成为真正的 google-ninja。
这是一个极具挑战性的红队操作员 III 级实验室,它将把您推向极限,并在以下领域测试您的技能:
Active Directory 枚举和利用
绕过 2FA、JEA 和 WDAC 等安全功能
利用交互式用户
Kerberos 攻击
在多个林之间横向移动
在不使用任何 CVE 的情况下实现您的目标
Google Hack
.....
网络博物馆
可以查网站历史

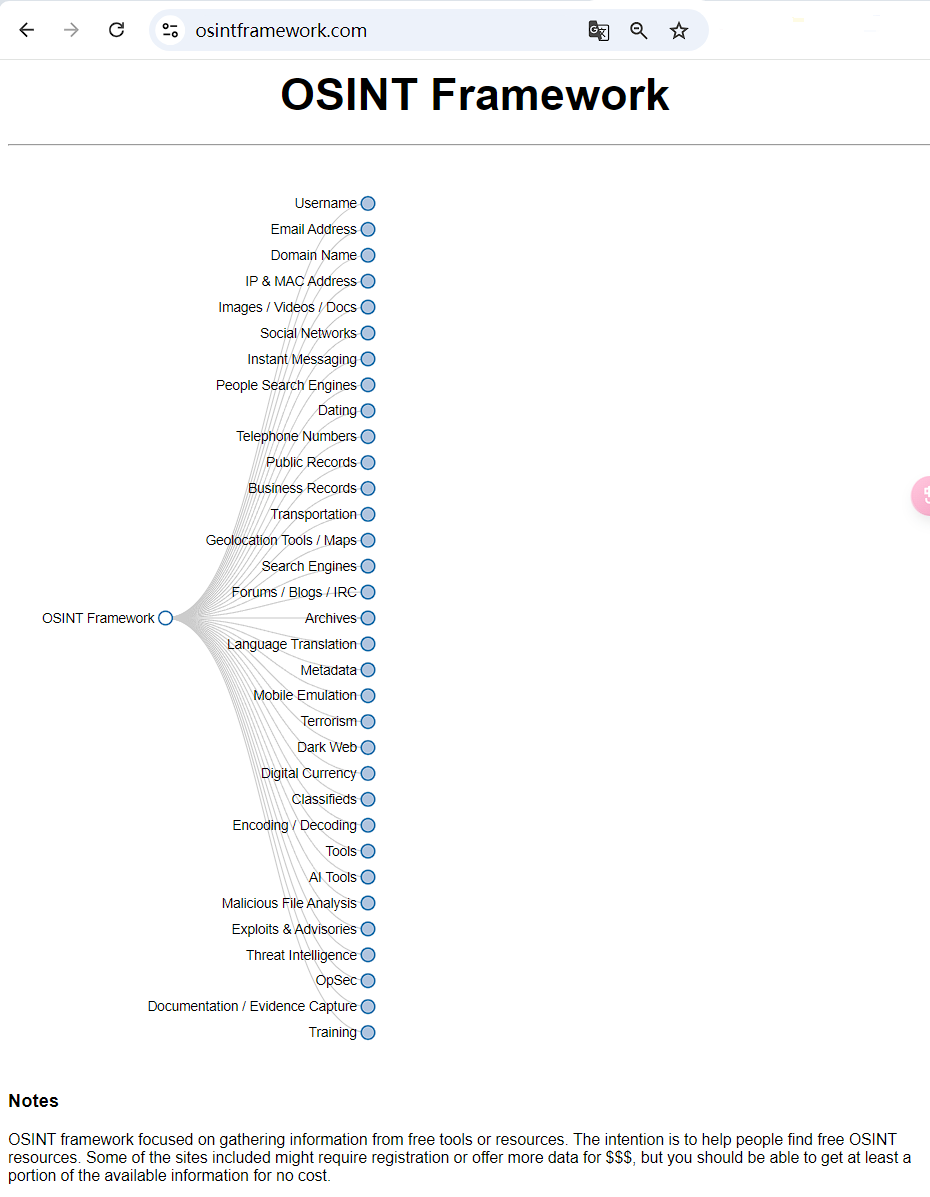
osint framework
Tmux 和 ZSH
Tmux 和 Zsh 是两个不同领域的工具,它们的功能和用途各不相同。下面详细解释它们的原理以及区别:
1. Tmux(Terminal Multiplexer)
Tmux 是一个 终端复用器,其主要作用是在一个单一的终端会话中管理多个终端窗口。它允许你在一个终端窗口中开启多个子窗口,甚至可以在不同的会话中共享同一个终端会话。Tmux 可以让你将会话分离(detach)和重新附加(reattach),即使关闭了原始的终端窗口,你也可以在之后恢复之前的工作状态。
Tmux 的主要功能和原理:
会话管理:Tmux 允许你创建和管理多个会话,每个会话可以包含多个窗口,每个窗口又可以包含多个面板(pane)。
面板分割:在一个窗口中可以水平或垂直分割成多个面板,分别运行不同的命令或进程。
持久性:Tmux 的会话可以在断开连接时保持活跃,当你重新连接时可以恢复到上次的状态。这对于远程登录的用户尤为有用,避免因为网络断开导致工作的丢失。
共享会话:Tmux 允许多个用户同时连接到同一个会话,以便协同工作。
快捷键:Tmux 提供了强大的键盘快捷键来操作各种窗口和面板。
适用场景:
在单个终端中处理多个任务,比如在一个窗口中运行编辑器,另一个窗口中运行编译程序。
远程服务器管理,保持会话的持久性,避免因网络断开导致会话丢失。
2. Zsh(Z Shell)
Zsh 是一种功能强大的 Unix Shell,它是一个命令行解释器,用户可以通过它输入命令并与操作系统交互。Zsh 是 Bash 的增强版本,提供了许多高级的功能,例如更好的自动补全、更强的脚本编写能力、插件和主题支持。
Zsh 的主要功能和原理:
命令补全:Zsh 提供了非常强大的命令自动补全功能,支持文件路径、命令选项、Git 分支等补全。
历史记录管理:Zsh 允许你轻松地搜索和管理历史命令,支持多种历史搜索模式。
别名和函数:Zsh 支持复杂的命令别名和函数定义,使得用户可以简化日常工作流程。
扩展性:Zsh 支持插件系统(如 Oh My Zsh),通过插件和主题可以轻松扩展 Zsh 的功能,比如 Git 集成、语法高亮等。
强大的脚本能力:Zsh 拥有强大的编程语言功能,能够编写复杂的 Shell 脚本,支持条件判断、循环、数组等。
适用场景:
需要高效、灵活的命令行操作和脚本编写。
希望通过插件系统扩展 Shell 的功能和定制化外观(如 Oh My Zsh)。
希望有更强的命令自动补全和快捷键功能,尤其适合开发人员和系统管理员。
Tmux 和 Zsh 的区别:
领域不同:
Tmux 主要用于 终端复用,管理多个终端会话、窗口和面板,适合需要同时操作多个任务的场景。
Zsh 是一个 命令行 Shell,用于解析和执行用户的命令,它是 Bash 的替代品,提供了更强大的命令行交互和脚本编写功能。
工作原理不同:
Tmux 提供的是一个虚拟终端环境,帮助你在单个终端窗口中运行多个终端任务。
Zsh 提供的是一个命令解释器,它帮助你解析命令并与操作系统进行交互。
功能侧重点不同:
Tmux 的侧重点是 会话管理 和 终端窗口管理,特别是远程会话的保持和恢复。
Zsh 的侧重点是 命令行体验的增强,提供更强大的自动补全、命令历史、别名和函数支持,适合复杂的命令行操作和脚本处理。
使用方式不同:
Tmux 是一个独立的终端复用器工具,通常在已经登录的终端中启动。
Zsh 是一个 Shell,可以作为系统的默认命令解释器,与 Bash 等其他 Shell 替换。
总结:
Tmux 主要解决的是如何高效管理多个终端会话,提供持久性和灵活的窗口管理功能。
Zsh 主要解决的是如何让命令行操作更高效、更智能,特别是在命令补全、历史记录管理和自定义功能方面具有显著优势。
入口
🆗我们开始吧,入口已经给了
10.10.110.0/24

上nmap
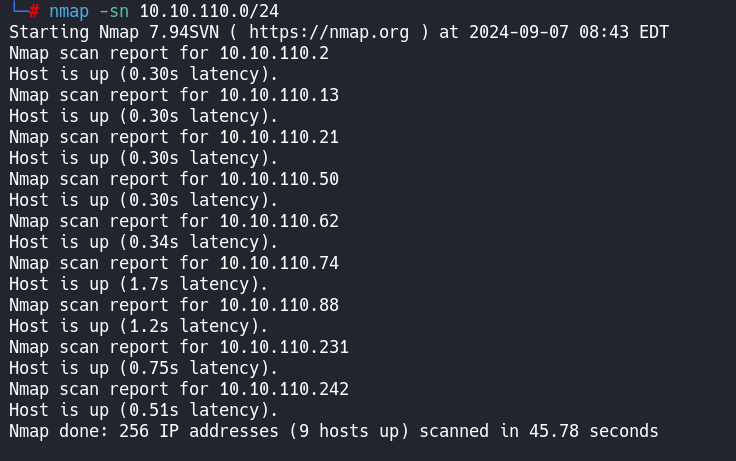
将存活ip保存到hosts文件
10.10.110.2
10.10.110.13
10.10.110.21
10.10.110.50
10.10.110.62
10.10.110.74
10.10.110.88
10.10.110.231
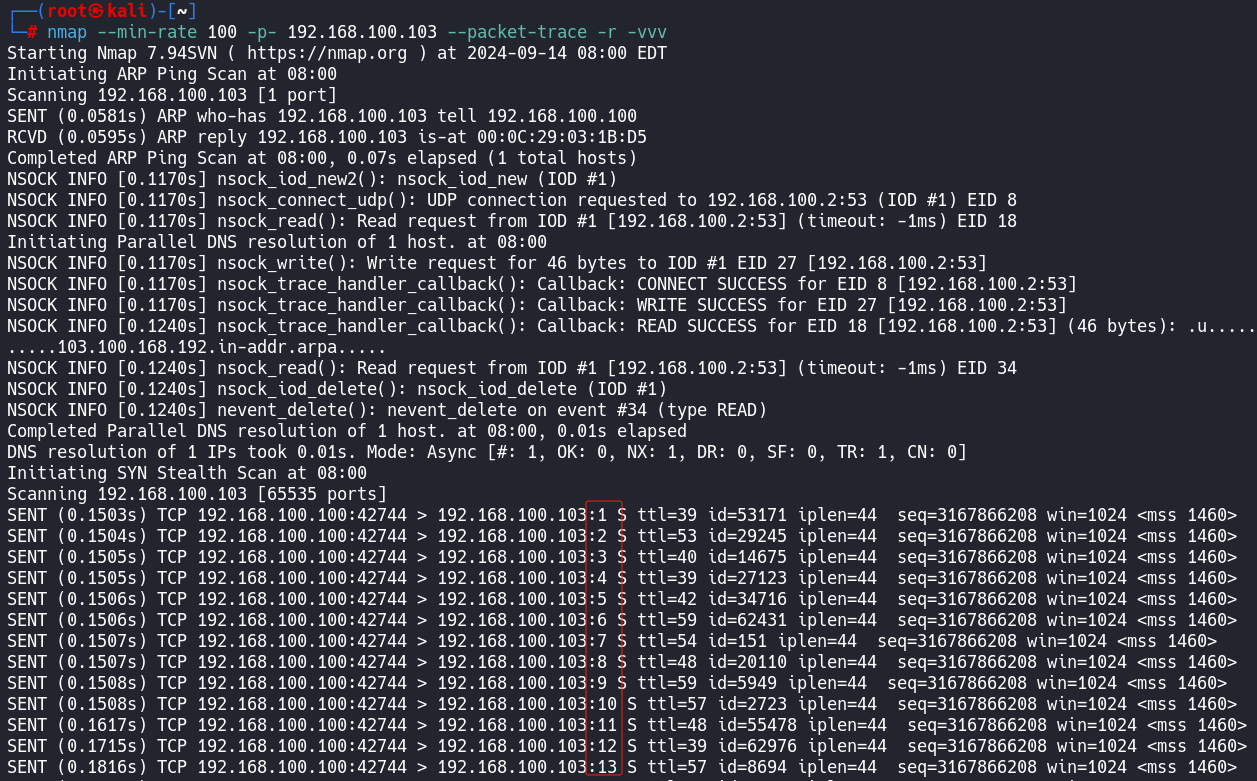
10.10.110.242nmap --min-rate 10000 -p- 192.168.100.103 --packet-trace -r -vvv
开始扫描
┌──(root㉿kali-linux-2022-2)-[~/Desktop/RedTeam-Live]
└─# nmap -sT 10.10.110.0/24 --stats-every 5s
Nmap scan report for 10.10.110.13
Host is up (0.47s latency).
PORT STATE SERVICE
53/tcp open domain
443/tcp open https
Nmap scan report for 10.10.110.21
Host is up (0.61s latency).
All 1000 scanned ports on 10.10.110.21 are in ignored states.
Nmap scan report for 10.10.110.50
Host is up (0.38s latency).
All 1000 scanned ports on 10.10.110.50 are in ignored states.
Nmap scan report for 10.10.110.62
Host is up (0.47s latency).
PORT STATE SERVICE
8080/tcp open http-proxy
Nmap scan report for 10.10.110.74
Host is up (0.47s latency).
PORT STATE SERVICE
22/tcp open ssh
25/tcp open smtp
Nmap scan report for 10.10.110.88
Host is up (0.45s latency).
PORT STATE SERVICE
80/tcp open http
Nmap scan report for 10.10.110.231
Host is up (0.66s latency).
PORT STATE SERVICE
443/tcp open https
Nmap scan report for 10.10.110.242
Host is up (0.47s latency).
PORT STATE SERVICE
80/tcp open http
Nmap done: 256 IP addresses (9 hosts up) scanned in 945.83 seconds10.10.110.2
10.10.110.13
┌──(root㉿kali-linux-2022-2)-[~/Desktop/RedTeam-Live]
└─# nmap -sT -sC -sV -O -p53,443 10.10.110.13
Starting Nmap 7.92 ( https://nmap.org ) at 2024-09-20 08:46 CST
Nmap scan report for 10.10.110.13
Host is up (0.81s latency).
PORT STATE SERVICE VERSION
53/tcp open domain PowerDNS Authoritative Server 4.1.11
| dns-nsid:
| NSID: powergslb (706f77657267736c62)
| id.server: powergslb
|_ bind.version: PowerDNS Authoritative Server 4.1.11
443/tcp open ssl/caldav Radicale calendar and contacts server (Python BaseHTTPServer)
|_http-title: Error response
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Not valid before: 2020-01-09T12:45:01
|_Not valid after: 2021-01-08T12:45:01
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
No OS matches for host
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 128.42 seconds
┌──(root㉿kali)-[~/Desktop/Redteam-live]
└─# nmap --script=vuln -p53,443 10.10.110.13
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-24 07:20 EDT
Nmap scan report for 10.10.110.13
Host is up (0.29s latency).
PORT STATE SERVICE
53/tcp open domain
443/tcp open https
|_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug)
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
| http-enum:
| /admin/: Possible admin folder
| /admin/index.html: Possible admin folder
|_ /admin/backup/: Possible backup (401 Unauthorized)
|_http-dombased-xss: Couldn't find any DOM based XSS.
Nmap done: 1 IP address (1 host up) scanned in 2895.45 secondss扫一下目录
┌──(root㉿kali-linux-2022-2)-[~/Desktop/RedTeam-Live]
└─# ffuf -w /usr/share/wordlists/dirb/big.txt:FUZZ -u https://10.10.110.13/FUZZ
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.5.0 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : https://10.10.110.13/FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/dirb/big.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405,500
________________________________________________
admin [Status: 401, Size: 206, Words: 16, Lines: 10, Duration: 714ms]
https://10.10.110.13/admin/
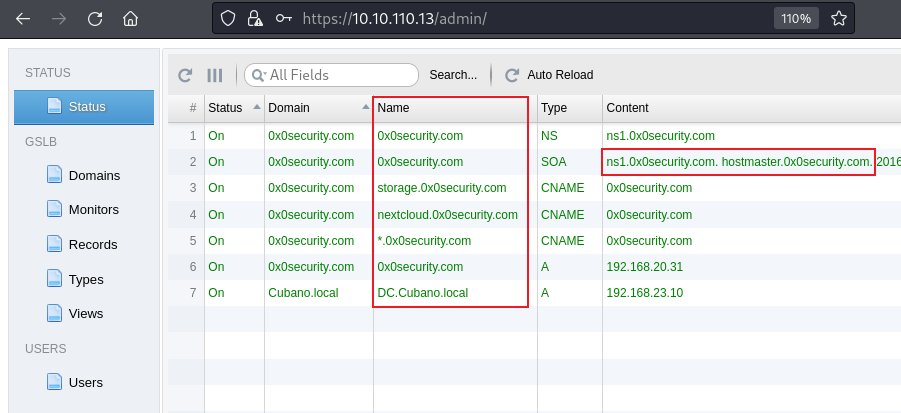
这里的nmap的报告中对服务的识别是有问题的
PowerDNS Authoritative Server 4.1.11
这个是不对的
经过多种搜索得出powergslb才是对的
他是
"GSLB" 是"Global Server Load Balancing"的缩写,
PowerGSLB 是一种基于 DNS 的简单全球服务器负载平衡 (GSLB) 解决方案。
广域服务器负载均衡(GSLB),有运维经验的,甚至只要搭建过网站的都应该听说过或实施过,一种用于在全球范围内分发流量技术,通常基于地理位置、服务器健康状况、响应时间或其他因素。
https://github.com/acudovs/powergslbMain features 主要特点
Quick installation and setup
快速安装和设置
Written in Python 2.7 用 Python 2.7 编写
Built as PowerDNS Authoritative Server Remote Backend
构建为 PowerDNS 权威服务器远程后端
Web based administration interface using w2ui
使用 w2ui 的基于 Web 的管理界面
HTTPS support for the web server
Web 服务器的 HTTPS 支持
DNS GSLB configuration stored in a MySQL / MariaDB database
存储在 MySQL/MariaDB 数据库中的 DNS GSLB 配置
Master-Slave DNS GSLB using native MySQL / MariaDB replication
使用本机 MySQL/MariaDB 复制的主从DNS GSLB
Multi-Master DNS GSLB using native MySQL / MariaDB Galera Cluster
使用本机 MySQL / MariaDB Galera 集群的多主 DNS GSLB
Modular architecture 模块化架构
Multithreaded architecture
多线程架构
Systemd status and watchdog support
systemd 状态和看门狗支持
Extendable health checks:
可扩展的运行状况检查:
ICMP ping ICMP 标记
TCP connect TCP 连接
HTTP request HTTP 请求
Arbitrary command execution
任意命令执行
Fallback if all the checks failed
如果所有检查都失败,则回退
Weighted (priority) records
加权 (优先级) 记录
Per record client IP / subnet persistence
每条记录的客户端 IP/子网持久性
DNS GSLB views support DNS GSLB 视图支持
All-in-one Docker image 一体化 Docker 镜像并且在github中找到了管理地址和默认账号密码
Web based administration interface
Open URL https://SERVER/admin/.
Default username: admin
Default password: admin
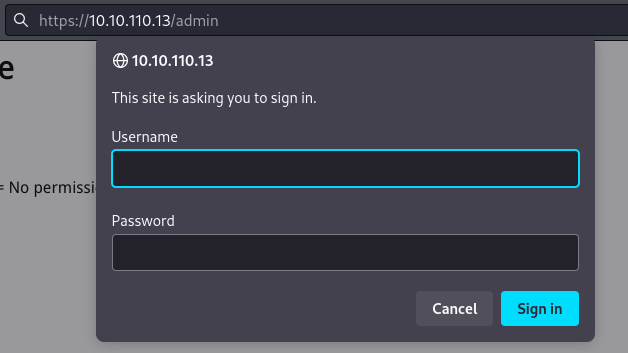
试一下admin/admin
!!!成功登录!!!
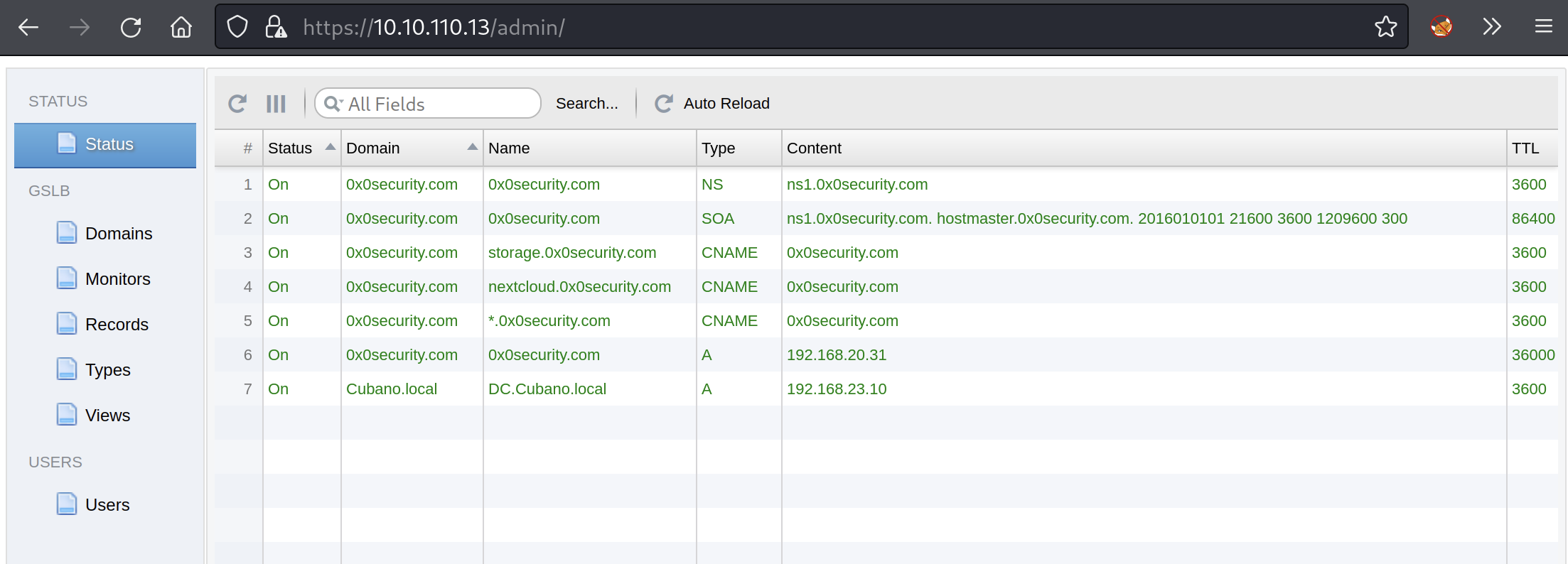
第一个flag。。。
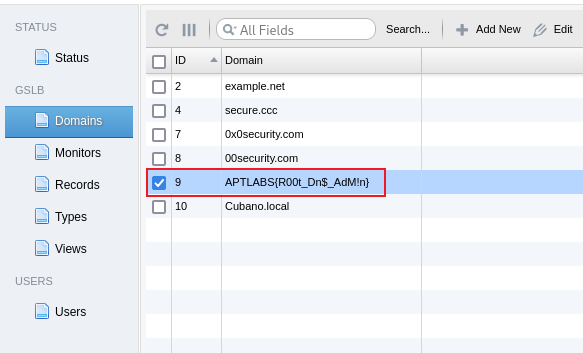
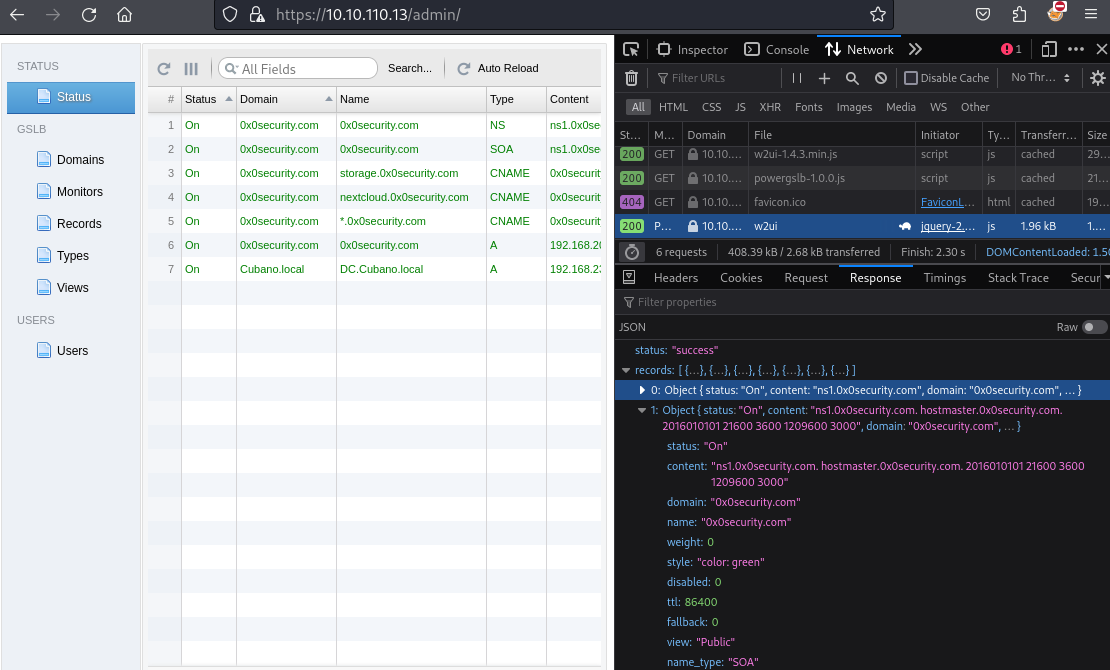
然后这里的信息也是有价值的,也需要下载下来
然后就是接着扫描开启web服务的主机
这里使用师傅自己写的脚本
open_hosts_firefox.sh
使用firefox遍历hosts中的内容
#!/bin/bash
# 检查hosts.txt⽂件是否存在
if [ ! -f "hosts" ]; then
echo "hosts ⽂件不存在,请确认⽂件路径。"
exit 1
fi
# 初始化⼀个变量,⽤于存储所有待打开的URL
urls=""
# 循环读取hosts中的每个IP地址
while IFS= read -r ip; do
echo "正在准备打开 $ip:80 和 $ip:443"
# 将每个IP地址的80和443端⼝URL添加到urls变量中
urls="$urls http://$ip:80 https://$ip:443"
done < "hosts"
# 检查 Firefox 是否已经在运⾏
if pgrep firefox > /dev/null
then
echo "Firefox 正在运⾏,在现有的窗⼝中打开标签。"
firefox --new-tab $urls &
else
echo "Firefox 未运⾏,启动新窗⼝并打开标签。"
firefox $urls &
fi
echo "所有IP地址已在同⼀浏览器窗⼝中打开。"
执行
┌──(root㉿kali)-[~/Desktop/Redteam-live]
└─# ./open_hosts_firefox.sh
正在准备打开 10.10.110.2:80 和 10.10.110.2:443
正在准备打开 10.10.110.13:80 和 10.10.110.13:443
正在准备打开 10.10.110.21:80 和 10.10.110.21:443
正在准备打开 10.10.110.50:80 和 10.10.110.50:443
正在准备打开 10.10.110.62:80 和 10.10.110.62:443
正在准备打开 10.10.110.74:80 和 10.10.110.74:443
正在准备打开 10.10.110.88:80 和 10.10.110.88:443
正在准备打开 10.10.110.231:80 和 10.10.110.231:443
正在准备打开 10.10.110.242:80 和 10.10.110.242:443
Firefox 正在运⾏,在现有的窗⼝中打开标签。
所有IP地址已在同⼀浏览器窗⼝中打开。使用curl遍历访问hosts
open_hosts_curl.sh
if [ ! -f "hosts" ]; then
echo "hosts ⽂件不存在,请确认⽂件路径。"
exit 1
fi
# 循环读取hosts中的每个IP地址
while IFS= read -r ip; do
echo "正在访问 $ip:80 和 $ip:443"
# 访问80端⼝,⽆需-k,因为是http
curl -I --connect-timeout 5 --max-time 10 "http://$ip:80"
# 访问443端⼝,添加-k以忽略⾃签名或不可信证书
curl -I --connect-timeout 5 --max-time 10 -k "https://$ip:443"
echo ""
done < "hosts"
echo "所有IP地址的访问已完成。"
┌──(root㉿kali)-[~/Desktop/Redteam-live]
└─# ./open_hosts_curl.sh
正在访问 10.10.110.2:80 和 10.10.110.2:443
curl: (28) Failed to connect to 10.10.110.2 port 80 after 5002 ms: Timeout was reached
curl: (28) Failed to connect to 10.10.110.2 port 443 after 5002 ms: Timeout was reached
正在访问 10.10.110.13:80 和 10.10.110.13:443
curl: (28) Failed to connect to 10.10.110.13 port 80 after 5002 ms: Timeout was reached
HTTP/1.1 200 OK
Server: PowerGSLB/1.7.3 Python/2.7.5
Date: Tue, 24 Sep 2024 12:09:17 GMT
Content-type: text/html; charset=UTF-8
Content-Length: 210
正在访问 10.10.110.21:80 和 10.10.110.21:443
curl: (28) Failed to connect to 10.10.110.21 port 80 after 5002 ms: Timeout was reached
curl: (28) Failed to connect to 10.10.110.21 port 443 after 5002 ms: Timeout was reached
正在访问 10.10.110.50:80 和 10.10.110.50:443
curl: (28) Failed to connect to 10.10.110.50 port 80 after 5001 ms: Timeout was reached
curl: (28) Failed to connect to 10.10.110.50 port 443 after 5002 ms: Timeout was reached
正在访问 10.10.110.62:80 和 10.10.110.62:443
curl: (28) Failed to connect to 10.10.110.62 port 80 after 5001 ms: Timeout was reached
curl: (28) Failed to connect to 10.10.110.62 port 443 after 5002 ms: Timeout was reached
正在访问 10.10.110.74:80 和 10.10.110.74:443
curl: (28) Failed to connect to 10.10.110.74 port 80 after 5002 ms: Timeout was reached
curl: (28) Failed to connect to 10.10.110.74 port 443 after 5002 ms: Timeout was reached
正在访问 10.10.110.88:80 和 10.10.110.88:443
HTTP/1.1 200 OK
Date: Tue, 24 Sep 2024 12:09:58 GMT
Server: Apache/2.4.29 (Ubuntu)
Set-Cookie: PHPSESSID=ousaoilrghdejmcd3ktluvos6j; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate
Pragma: no-cache
Content-Type: text/html; charset=UTF-8
curl: (28) Failed to connect to 10.10.110.88 port 443 after 5002 ms: Timeout was reached
正在访问 10.10.110.231:80 和 10.10.110.231:443
curl: (28) Failed to connect to 10.10.110.231 port 80 after 5002 ms: Timeout was reached
HTTP/1.1 200 OK
Date: Tue, 24 Sep 2024 12:10:09 GMT
Server: Apache/2.4.52 (Ubuntu)
Last-Modified: Sat, 07 Mar 2020 18:16:43 GMT
ETag: "2b63-5a047c5b32072"
Accept-Ranges: bytes
Content-Length: 11107
Vary: Accept-Encoding
Content-Type: text/html
正在访问 10.10.110.242:80 和 10.10.110.242:443
HTTP/1.1 200 OK
Date: Tue, 24 Sep 2024 12:10:11 GMT
Server: Apache/2.4.41 (Unix)
Last-Modified: Mon, 23 Dec 2019 09:29:26 GMT
ETag: "3a1f-59a5ba9dba980"
Accept-Ranges: bytes
Content-Length: 14879
Content-Type: text/html
curl: (28) Failed to connect to 10.10.110.242 port 443 after 5002 ms: Timeout was reached
所有IP地址的访问已完成。┌──(root㉿kali-linux-2022-2)-[~/Desktop/RedTeam-Live]
└─# nmap -sT 10.10.110.0/24 --stats-every 5s
Nmap scan report for 10.10.110.13
Host is up (0.47s latency).
PORT STATE SERVICE
53/tcp open domain
443/tcp open https
Nmap scan report for 10.10.110.21
Host is up (0.61s latency).
Nmap scan report for 10.10.110.50
Host is up (0.38s latency).
Nmap scan report for 10.10.110.62
Host is up (0.47s latency).
PORT STATE SERVICE
8080/tcp open http-proxy
Nmap scan report for 10.10.110.74
Host is up (0.47s latency)
PORT STATE SERVICE
22/tcp open ssh
25/tcp open smtp
Nmap scan report for 10.10.110.88
Host is up (0.45s latency).
PORT STATE SERVICE
80/tcp open http
Nmap scan report for 10.10.110.231
Host is up (0.66s latency).
PORT STATE SERVICE
443/tcp open https
Nmap scan report for 10.10.110.242
Host is up (0.47s latency).
PORT STATE SERVICE
80/tcp open http
Nmap done: 256 IP addresses (9 hosts up) scanned in 945.83 seconds┌──(root㉿kali)-[~/Desktop/Redteam-live]
└─# gobuster dir -u http://10.10.110.62:8080 -w /usr/share/seclists/Discovery/Web-Content/raft-large-directories.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.110.62:8080
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/Web-Content/raft-large-directories.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/admin (Status: 301) [Size: 0] [--> /admin/]
10.10.110.21
无开放端口
Nmap scan report for 10.10.110.21
Host is up (0.61s latency).10.10.110.50
无开放端口
Nmap scan report for 10.10.110.50
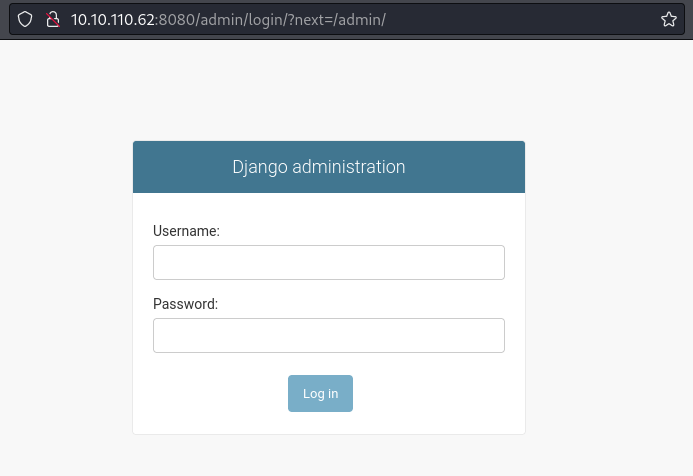
Host is up (0.38s latency).10.10.110.62
Nmap scan report for 10.10.110.62
Host is up (0.47s latency).
PORT STATE SERVICE
8080/tcp open http-proxy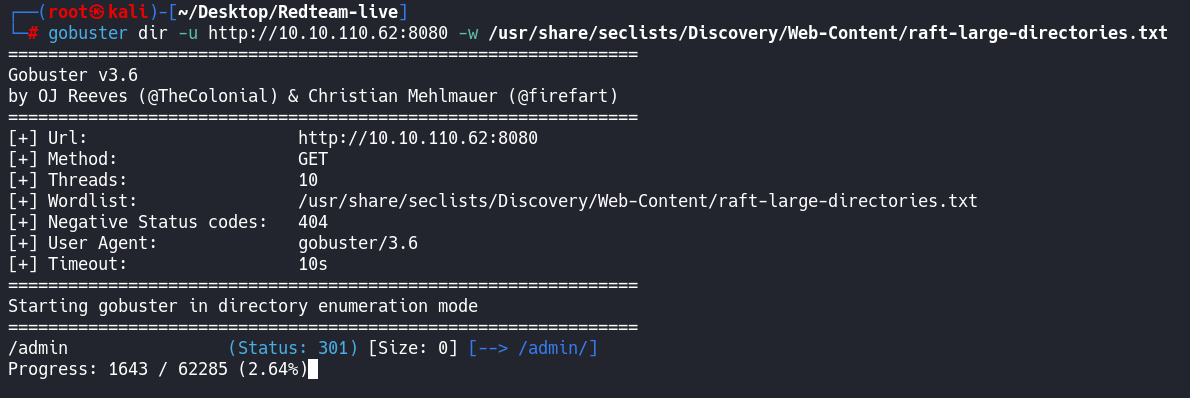
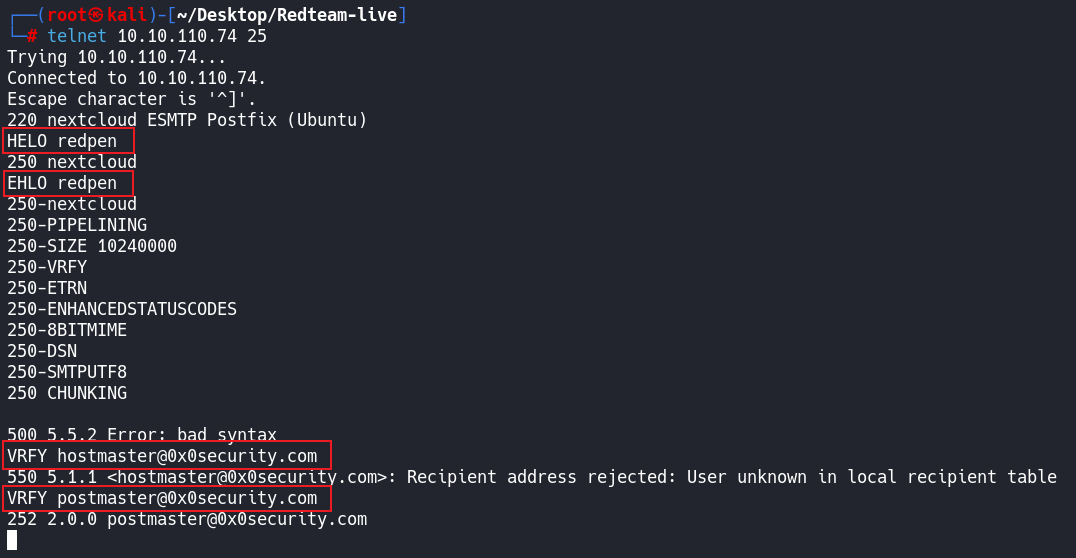
10.10.110.74
Nmap scan report for 10.10.110.74
Host is up (0.47s latency).
PORT STATE SERVICE
22/tcp open ssh
25/tcp open smtp对比nmap如何查看版本
其实原理就是
┌──(root㉿kali)-[~/Desktop/Redteam-live]
└─# nc -nv 10.10.110.74 22
(UNKNOWN) [10.10.110.74] 22 (ssh) open
SSH-2.0-OpenSSH_8.9p1 Ubuntu-3ubuntu0.10就是这样
┌──(root㉿kali)-[~/Desktop/Redteam-live]
└─# telnet 10.10.110.74 25
Trying 10.10.110.74...
Connected to 10.10.110.74.
Escape character is '^]'.
220 nextcloud ESMTP Postfix (Ubuntu)
HELO redpen
250 nextcloud
EHLO redpen
250-nextcloud
250-PIPELINING
250-SIZE 10240000
250-VRFY
250-ETRN
250-ENHANCEDSTATUSCODES
250-8BITMIME
250-DSN
250-SMTPUTF8
250 CHUNKING
hostmaster@0x0security.com
postmaster@0x0security.com
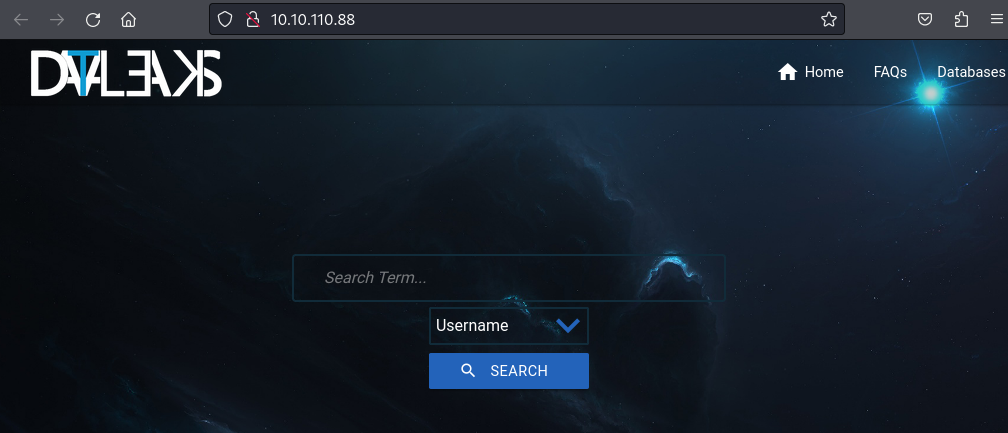
10.10.110.88
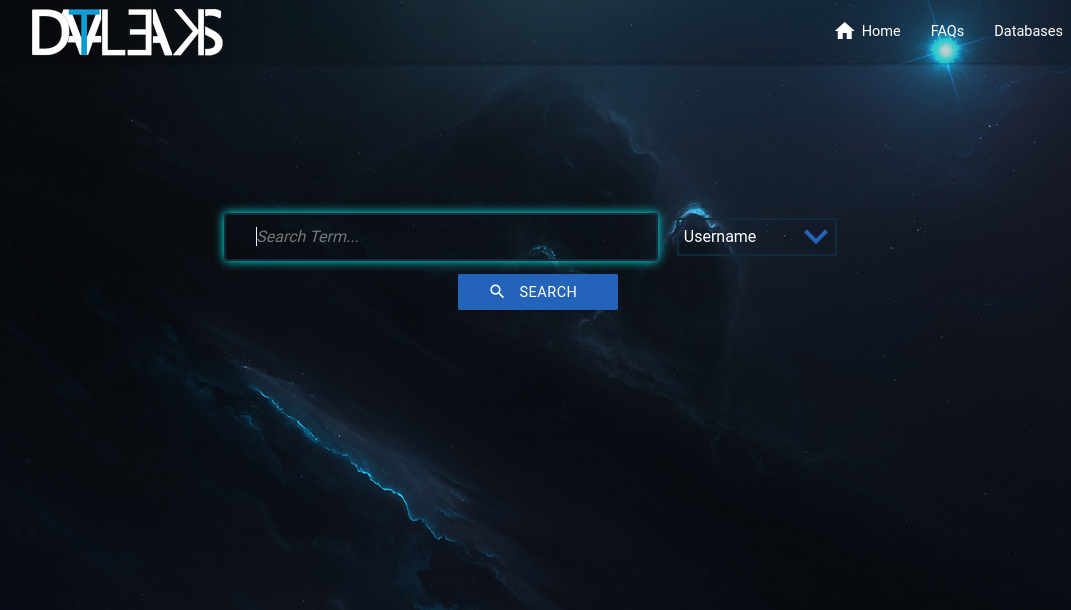
这是一个数据泄露检索的数据库
用来查看你们的数据库数据有没有泄露过
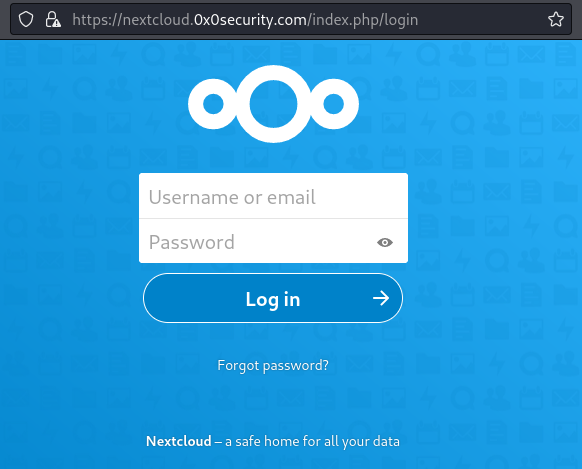
10.10.110.231
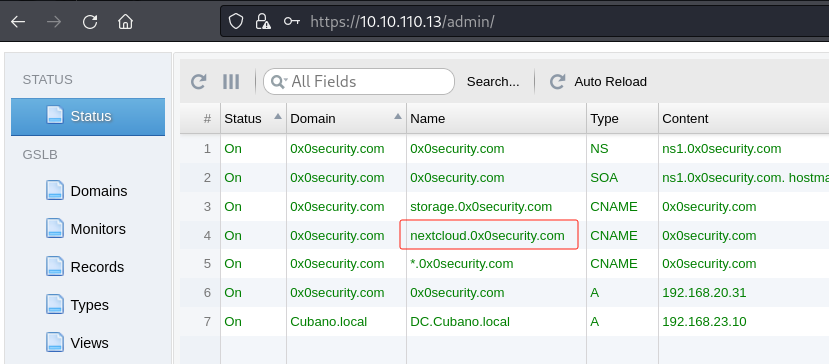
这里跟之前那台110.13里面的域名解析配置有关系
因为最开始使用ip访问是这个站

那我们把hosts添加进去
┌──(root㉿kali)-[~/Desktop/Redteam-live]
└─# cat /etc/hosts
10.10.110.231 hostmaster.0x0security.com
10.10.110.231 storage.0x0security.com
10.10.110.231 nextcloud.0x0security.com
10.10.110.231 0x0security.com
127.0.0.1 localhost
127.0.0.1 localhost.com
127.0.1.1 kali
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters这里为什么把域名解析绑定到10.10.110.231呢
因为你看这俩个站https://10.10.110.231和https://hostmaster.0x0security.com/
页面是一样的
https://hostmaster.0x0security.com/

10.10.110.242
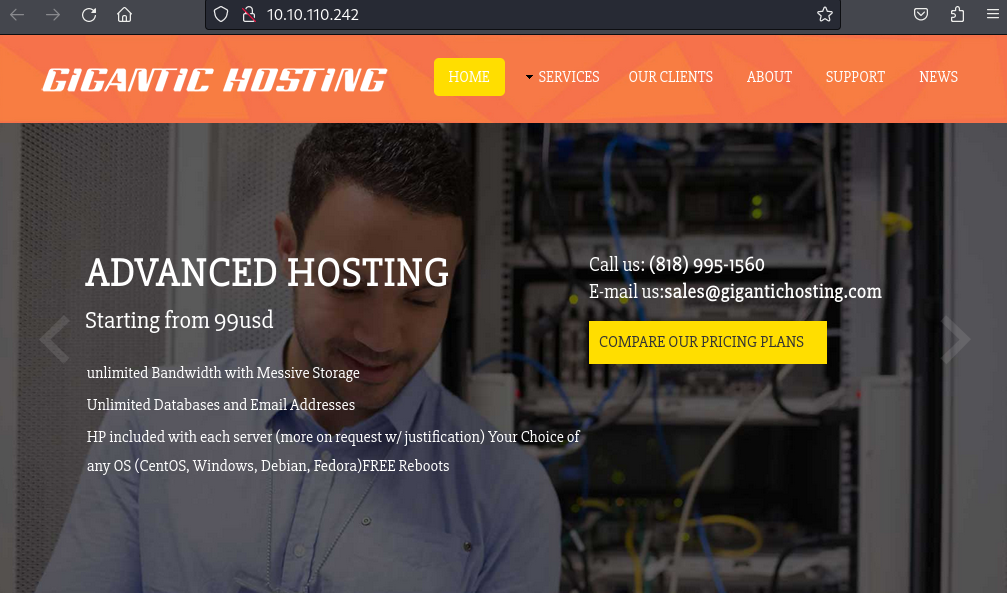
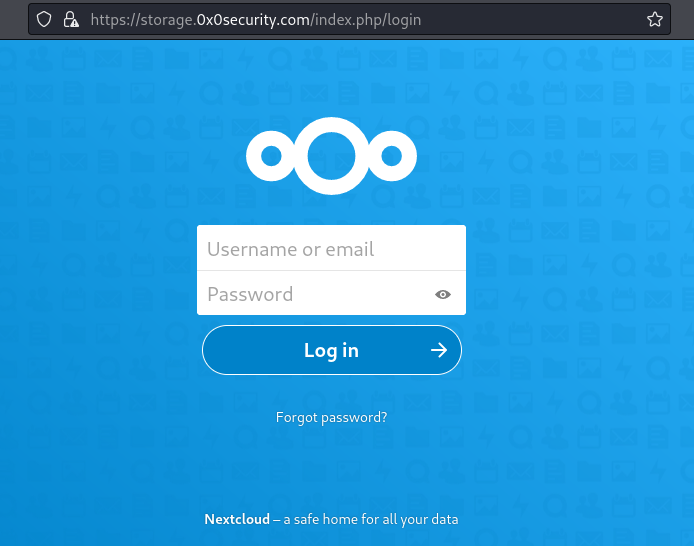
https://nextcloud.0x0security.com
这个域名和另一个https://storage.0x0security.com是一样的,其实都是一个,
因为老外喜欢把一些东西改名称叫下一代云,下一代技术等名称
-.-


评论区